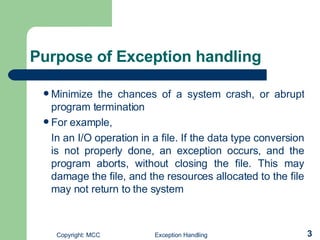
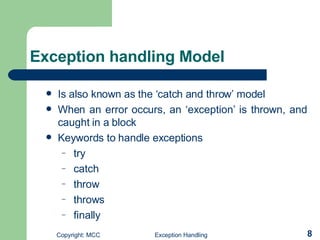
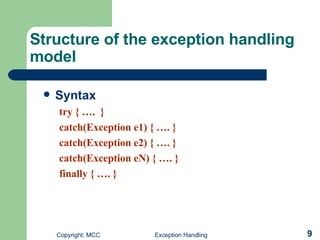
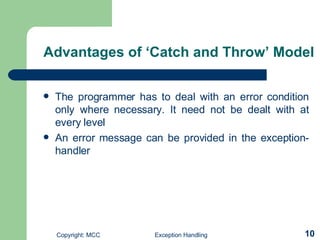
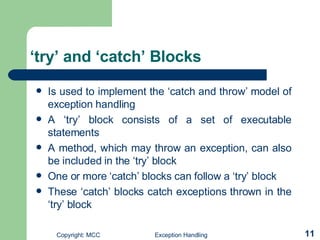
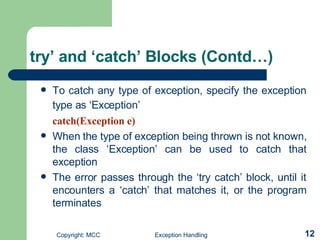
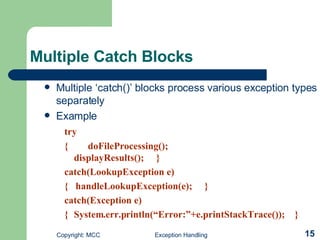
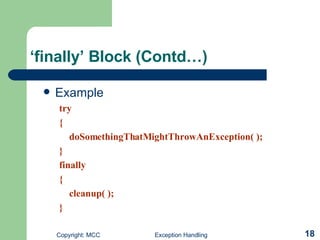
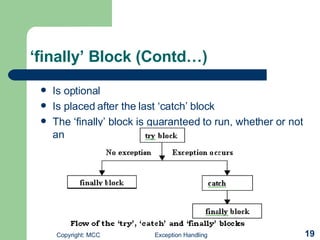
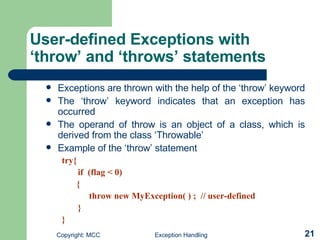
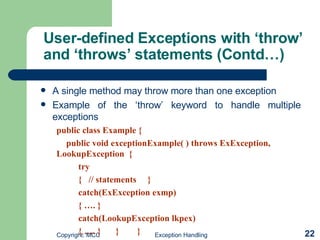
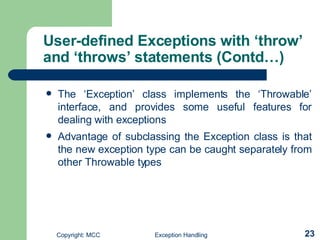
Exception handling in Java involves using try, catch, and finally blocks to gracefully handle errors and unexpected conditions at runtime. The try block contains code that might throw exceptions, catch blocks specify how to handle specific exceptions, and finally ensures cleanup code runs regardless of exceptions. User-defined exceptions can be created by subclassing the Exception class and using throw to raise the exception which catch blocks can then handle.


![How exception work? //to show exception class UNO{ public static void main(String args[]){ int num=Integer.parseInt(args[0]); System.out.println("Here is "+num); } }](https://image.slidesharecdn.com/exception-handling-1197644384672497-5/85/Exception-Handling-7-320.jpg)
![Example of catch and throw model //Number Format Exception Example class Try_Example{ public static void main(String args[]){ try{ int n=Integer.parseInt(args[0]); System.out.println("N is "+n); } catch(Exception e){ System.out.println("E is "+e); } } }](https://image.slidesharecdn.com/exception-handling-1197644384672497-5/85/Exception-Handling-13-320.jpg)
![Example(cont) //Arithemetic Exception Example class Try_Example{ public static void main(String args[]){ int demo=0; try{ System.out.println(20/demo); } catch(Exception e){ System.out.println("E is "+e); } } }](https://image.slidesharecdn.com/exception-handling-1197644384672497-5/85/Exception-Handling-14-320.jpg)
![Example of Finally Block //Finally Block Example class Finally_Example{ public static void main(String args[]){ int demo=0; try{ System.out.println(20/demo); } catch(Exception e){ System.out.println("E is "+e); } finally{ System.out.println("Finally Executed"); } } }](https://image.slidesharecdn.com/exception-handling-1197644384672497-5/85/Exception-Handling-20-320.jpg)
![User Defined Exception Example public class ExTest{ public static void main(String args[]){ int num=Integer.parseInt(args[0]); try{ if(num<0) throw new MyExceptionTest(); } catch(MyExceptionTest e) { System.out.println(e); } } } public class MyExceptionTest extends ArithmeticException{ MyExceptionTest(){ super("You have passed Illegal Operation"); } }](https://image.slidesharecdn.com/exception-handling-1197644384672497-5/85/Exception-Handling-24-320.jpg)
![Multi catch example public class Pre { public static void main (String argv[]) { try { double d = Double.valueOf(argv[0]).doubleValue(); System.out.println (d); } catch (ArrayIndexOutOfBoundsException e) { System.out.println ("An argument is required."); return; } catch (NumberFormatException e) { System.out.println ("The argument must be a real number."); return; } } }](https://image.slidesharecdn.com/exception-handling-1197644384672497-5/85/Exception-Handling-25-320.jpg)