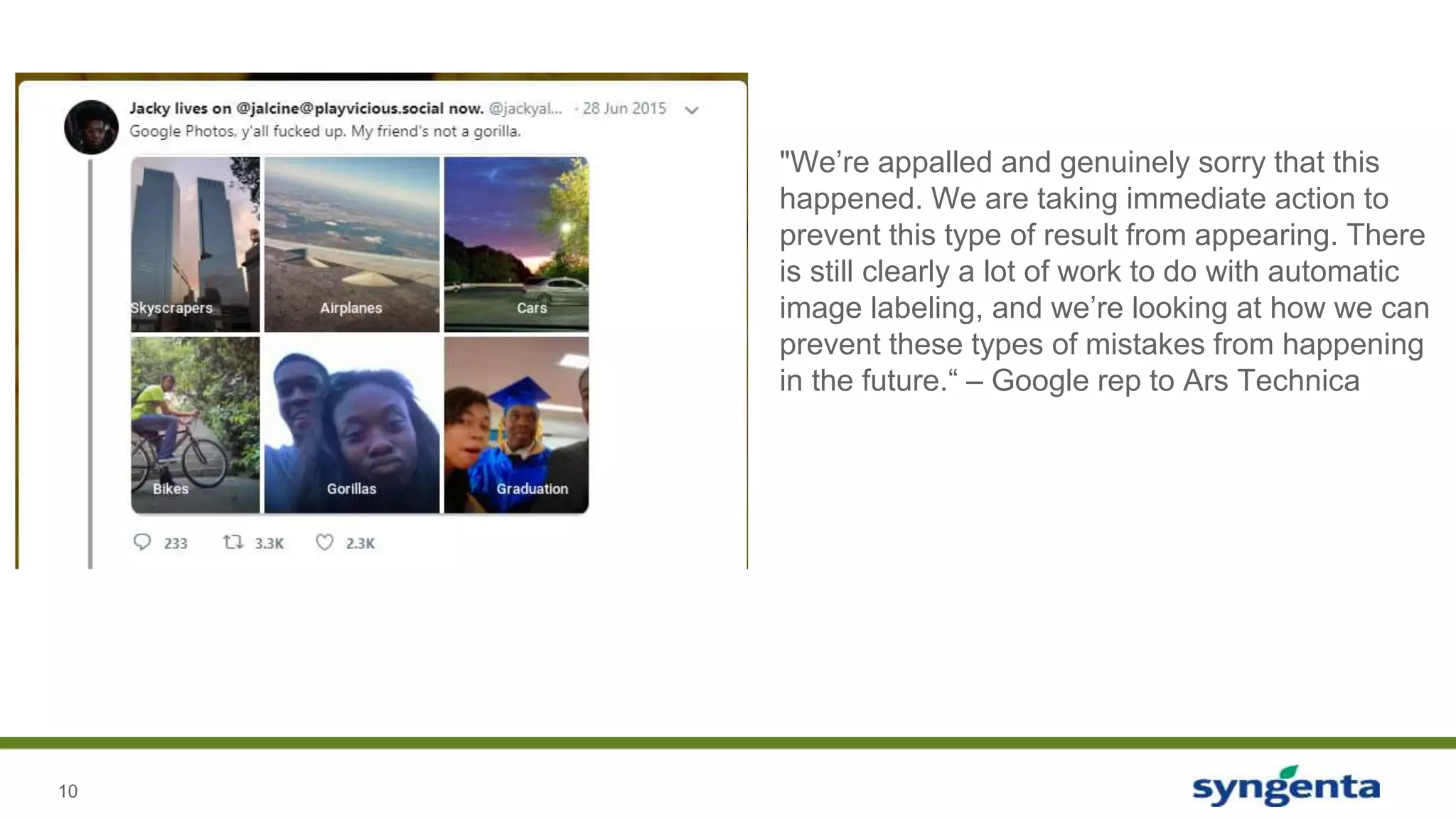
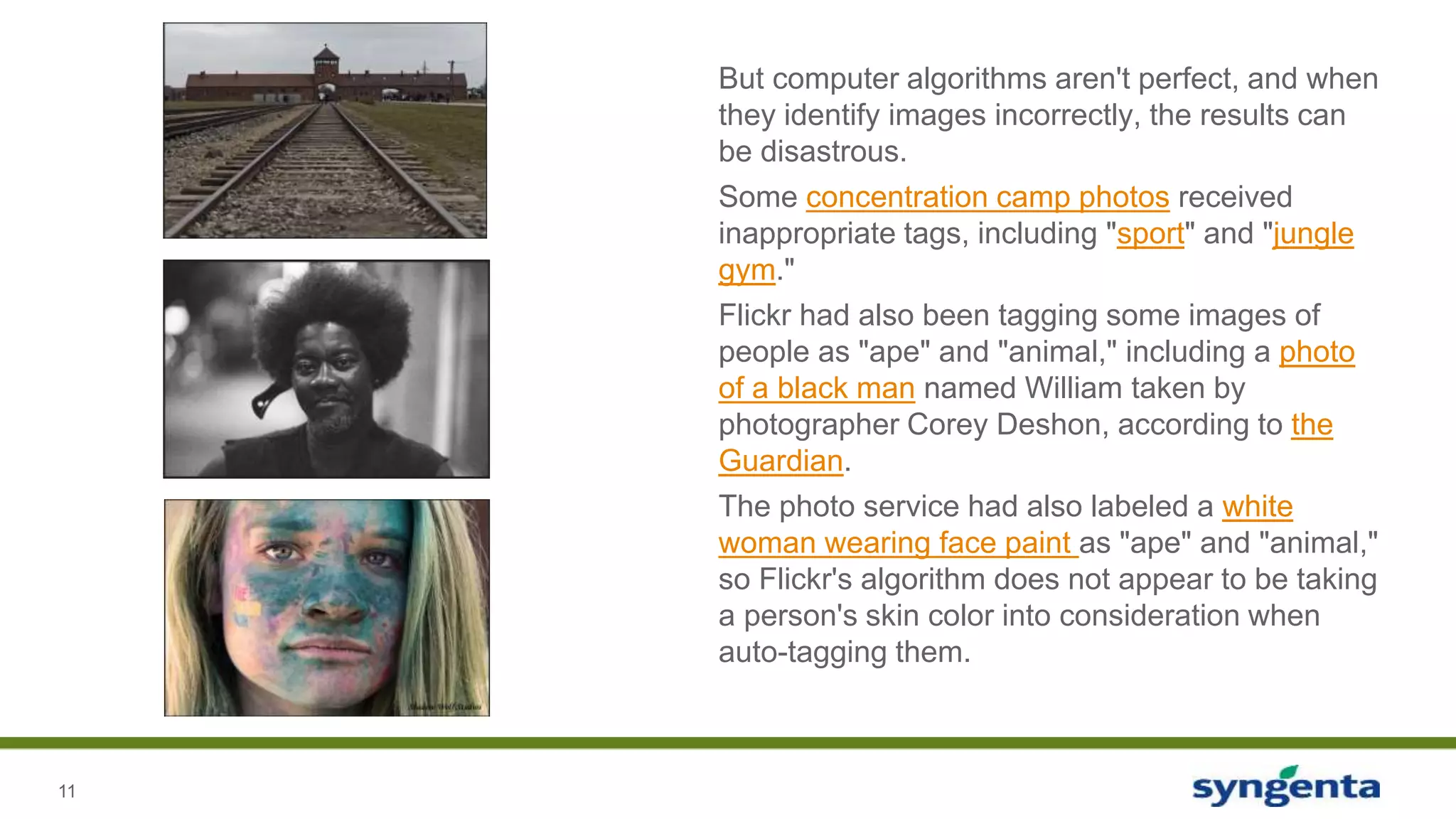
The document discusses the challenges of ethics in data-driven marketing, highlighting how companies use customer data to target demographics, particularly expectant parents. It addresses issues with algorithmic biases in image tagging and the legal implications of using genealogy databases like gedmatch for criminal investigations. Additionally, it touches on the controversy of drug pricing and how fitness tracking data influences insurance discounts.

![5
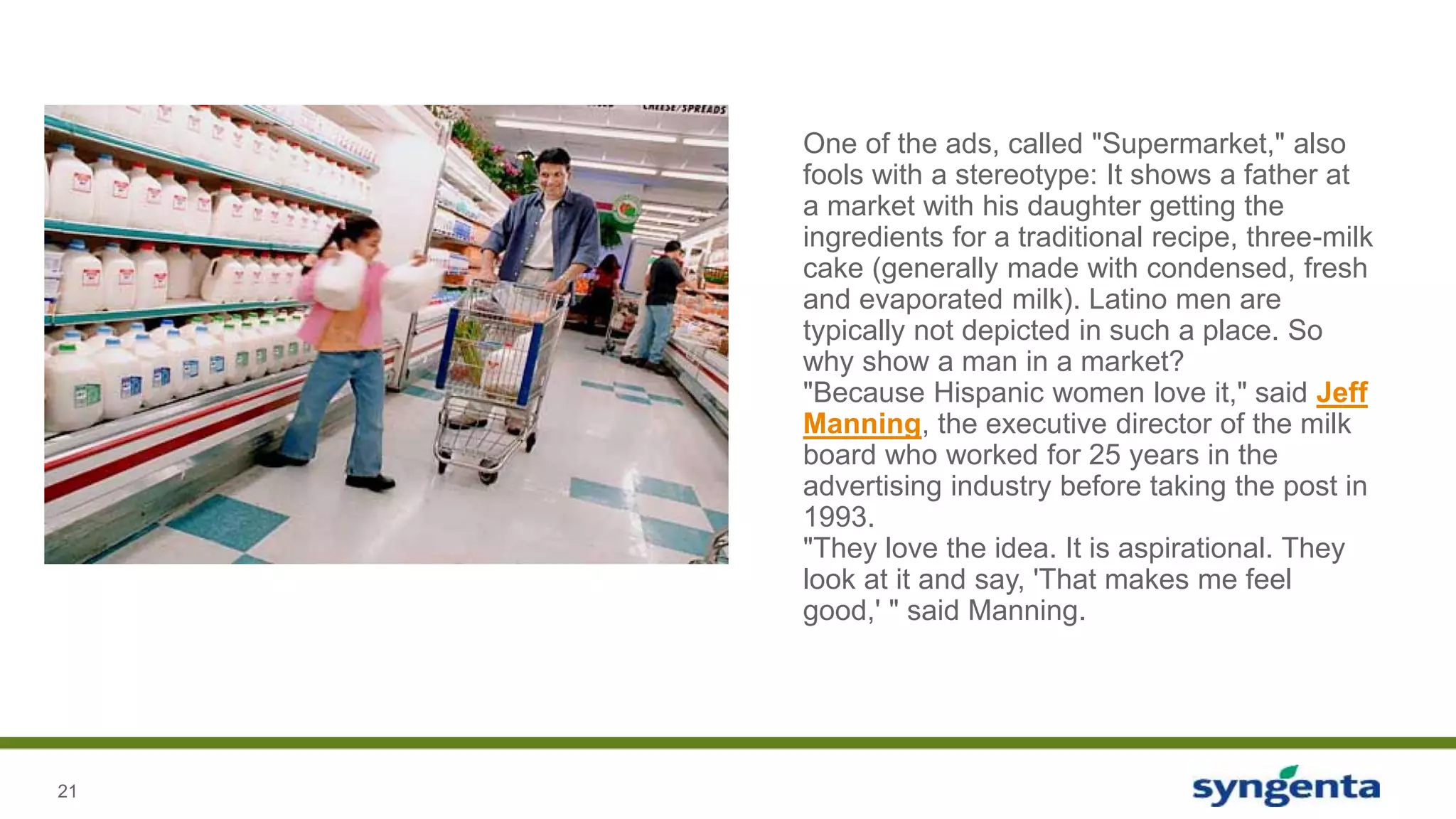
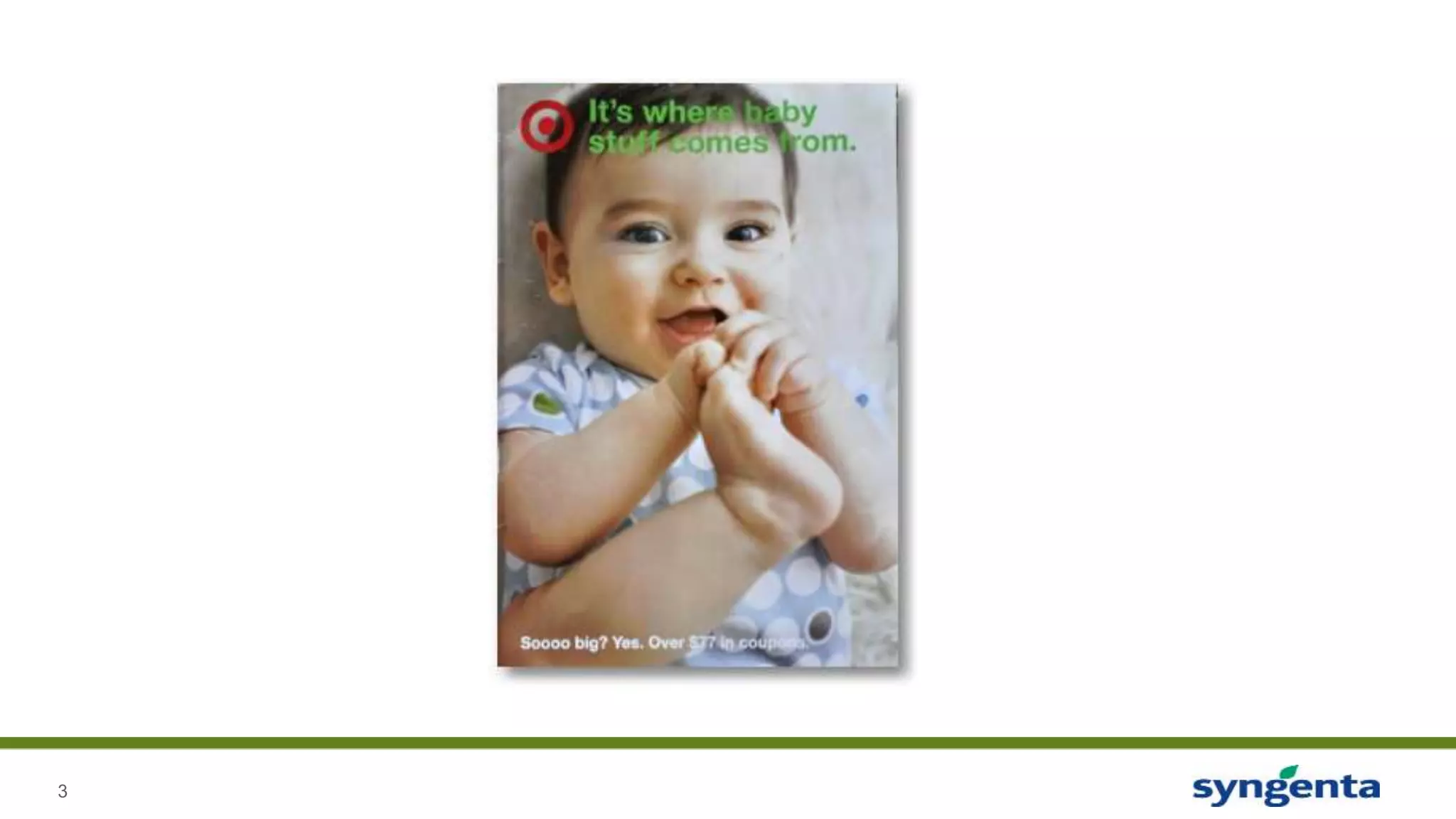
“[Pole] ran test after test, analyzing the data, and before
long some useful patterns emerged. Lotions, for
example. Lots of people buy lotion, but one of Pole’s
colleagues noticed that women on the baby registry
were buying larger quantities of unscented lotion
around the beginning of their second trimester.
Another analyst noted that sometime in the first 20
weeks, pregnant women loaded up on supplements
like calcium, magnesium and zinc. Many shoppers
purchase soap and cotton balls, but when someone
suddenly starts buying lots of scent-free soap and
extra-big bags of cotton balls, in addition to hand
sanitizers and washcloths, it signals they could be
getting close to their delivery date.”](https://image.slidesharecdn.com/ethicsinadatadrivenworld-181212151728/75/Ethics-In-A-Data-Driven-World-5-2048.jpg)


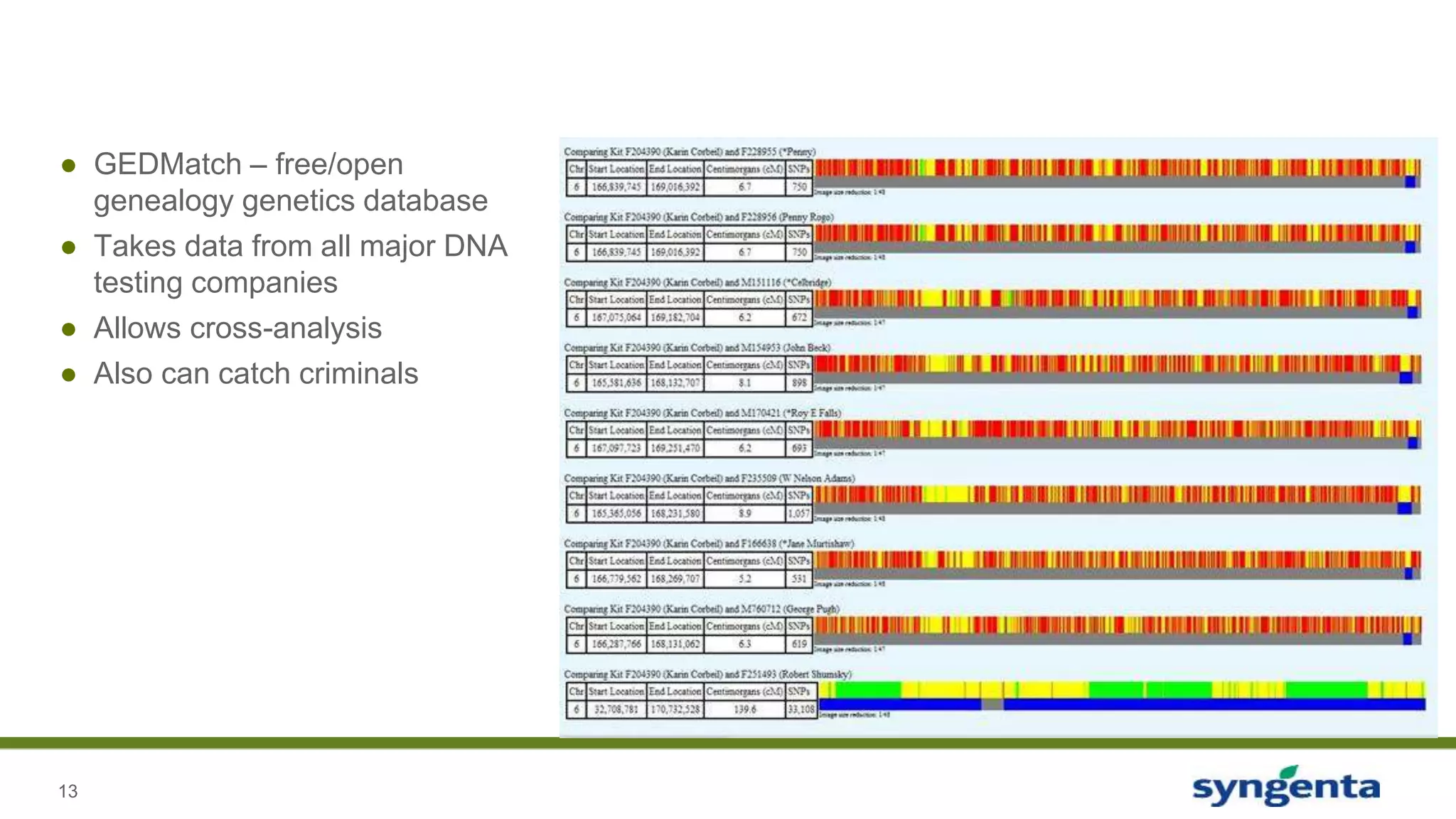
![14
● DNA from over 100 crime scenes uploaded
● Police create fake profiles, upload suspect data and triangulate
● Forced GEDMatch to change their Terms of Service to allow for criminal investigation
● Users have mixed reactions
- A few deleted their data
- Others were thankful
• [GEDMatch’s co-creator] says a woman wrote that her father was a serial killer, and she
wanted her data out there to give the families of his victim’s closure.
● Police also have CODIS – the government criminal DNA database
- Only looks at small snippets of DNA – 20 locations in human genome
- DNA Tests/GEDMatch contains full DNA sequences – 600,000 locations in human genome](https://image.slidesharecdn.com/ethicsinadatadrivenworld-181212151728/75/Ethics-In-A-Data-Driven-World-14-2048.jpg)