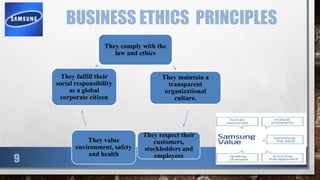
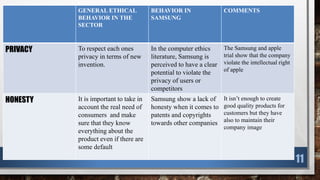
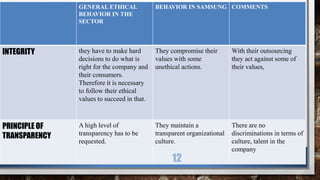
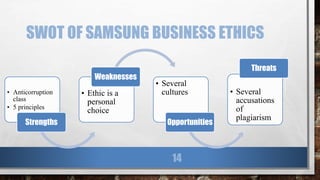
This document presents an ethical evaluation of Samsung electronics. It begins with an introduction on business ethics and principles. It then provides an overview of Samsung as a company, focusing on its core markets. The document evaluates Samsung's behavior in areas like privacy, honesty, and integrity against general ethical standards in the IT industry. It identifies both strengths and weaknesses in Samsung's business ethics through a SWOT analysis. The document concludes with recommendations for Samsung to improve its ethical practices and uphold high standards.