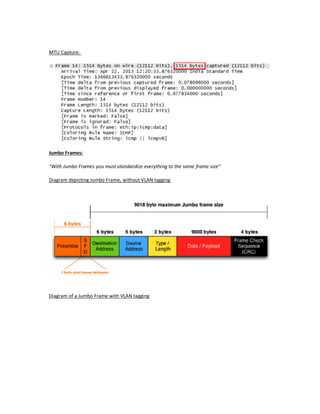
An Ethernet frame contains 6 segments: the preamble, destination and source addresses, type/length field, data/payload, and frame check sequence. It can carry higher-level network protocols like IP packets. The frame always refers to the physical transmission medium, while a packet can be transmitted over different mediums. Jumbo frames are larger than the standard 1500 byte frame size and introduce VLAN tagging to identify specific VLANs and prioritize traffic between interconnected devices.