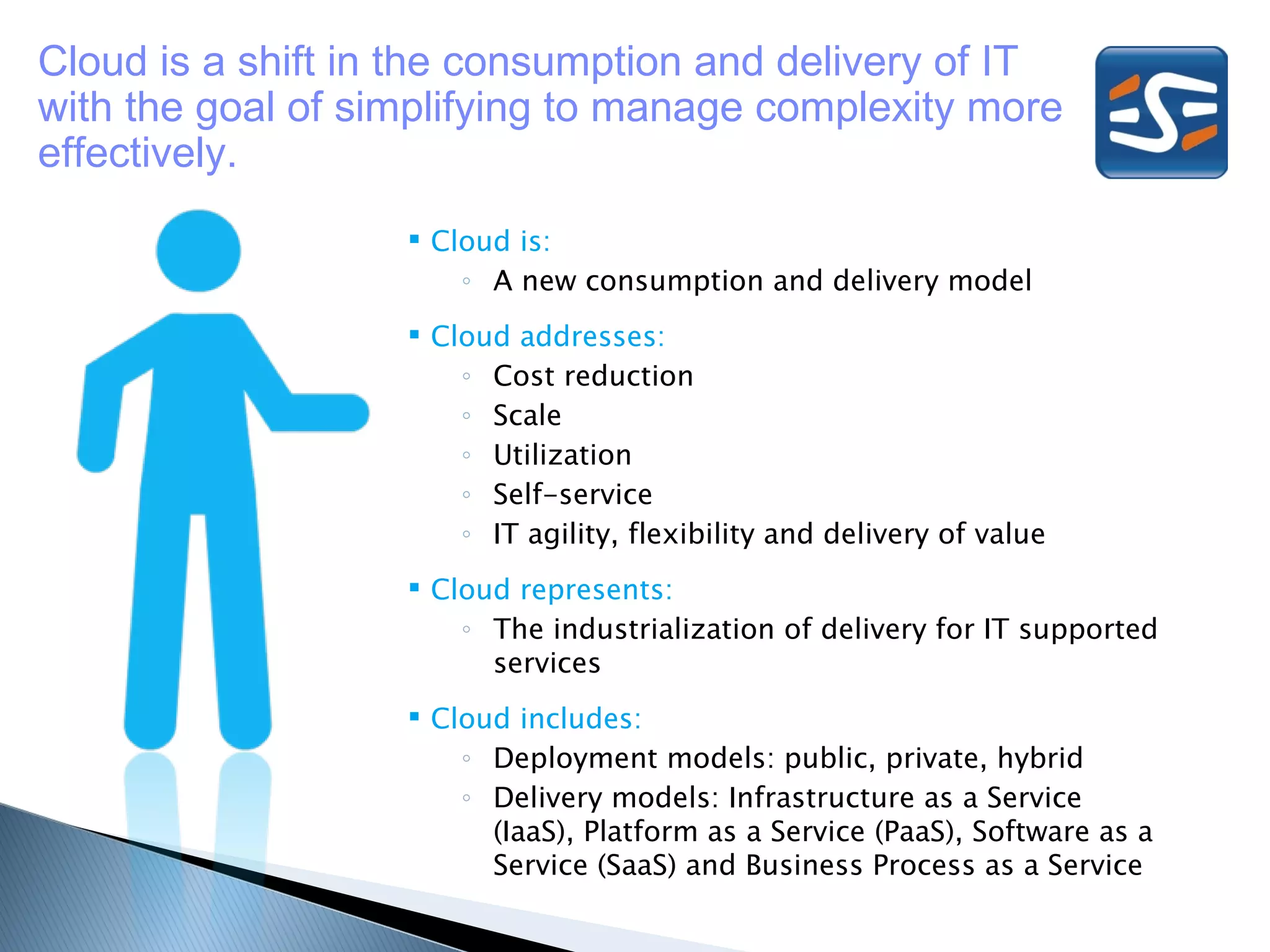
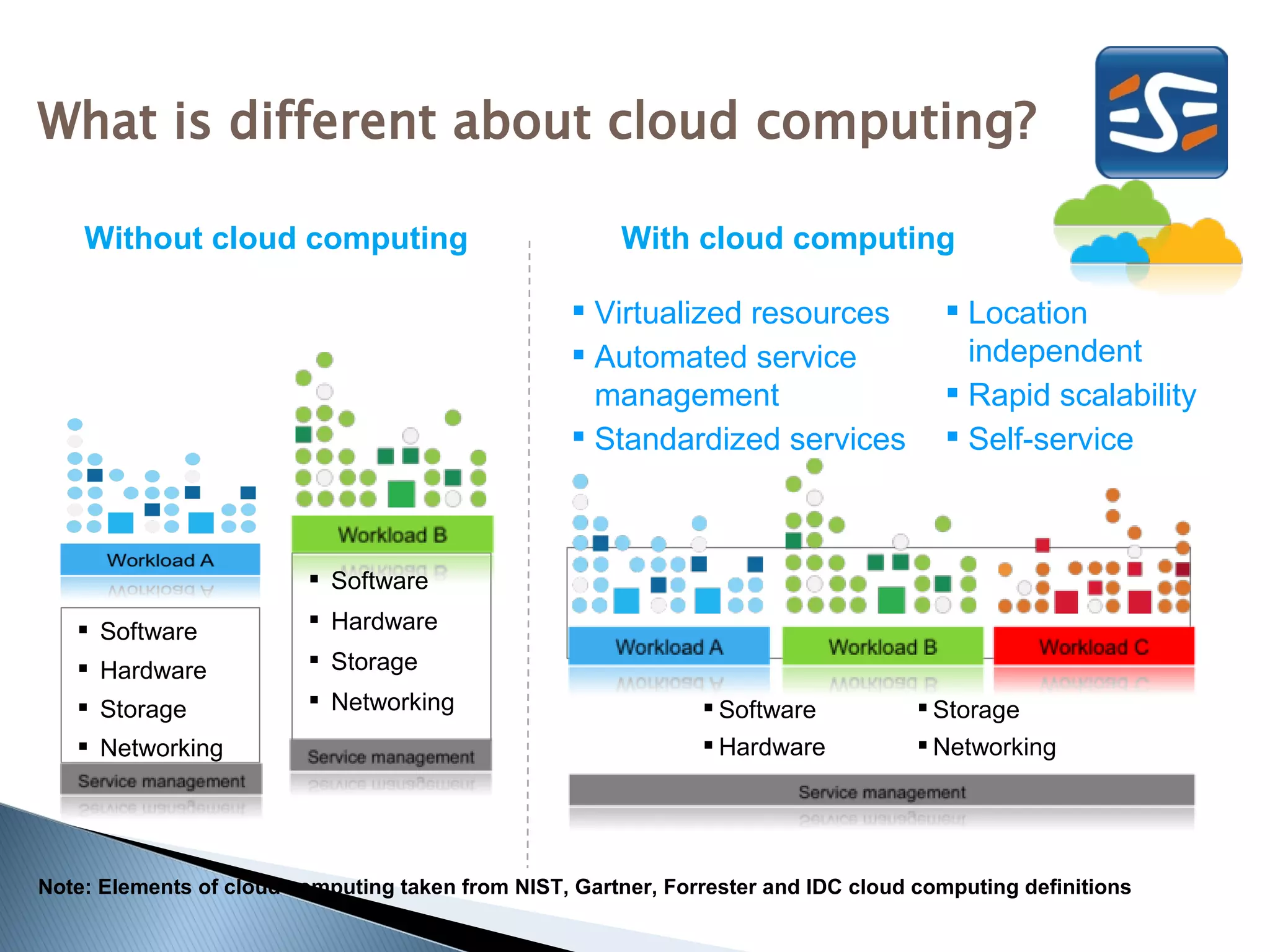
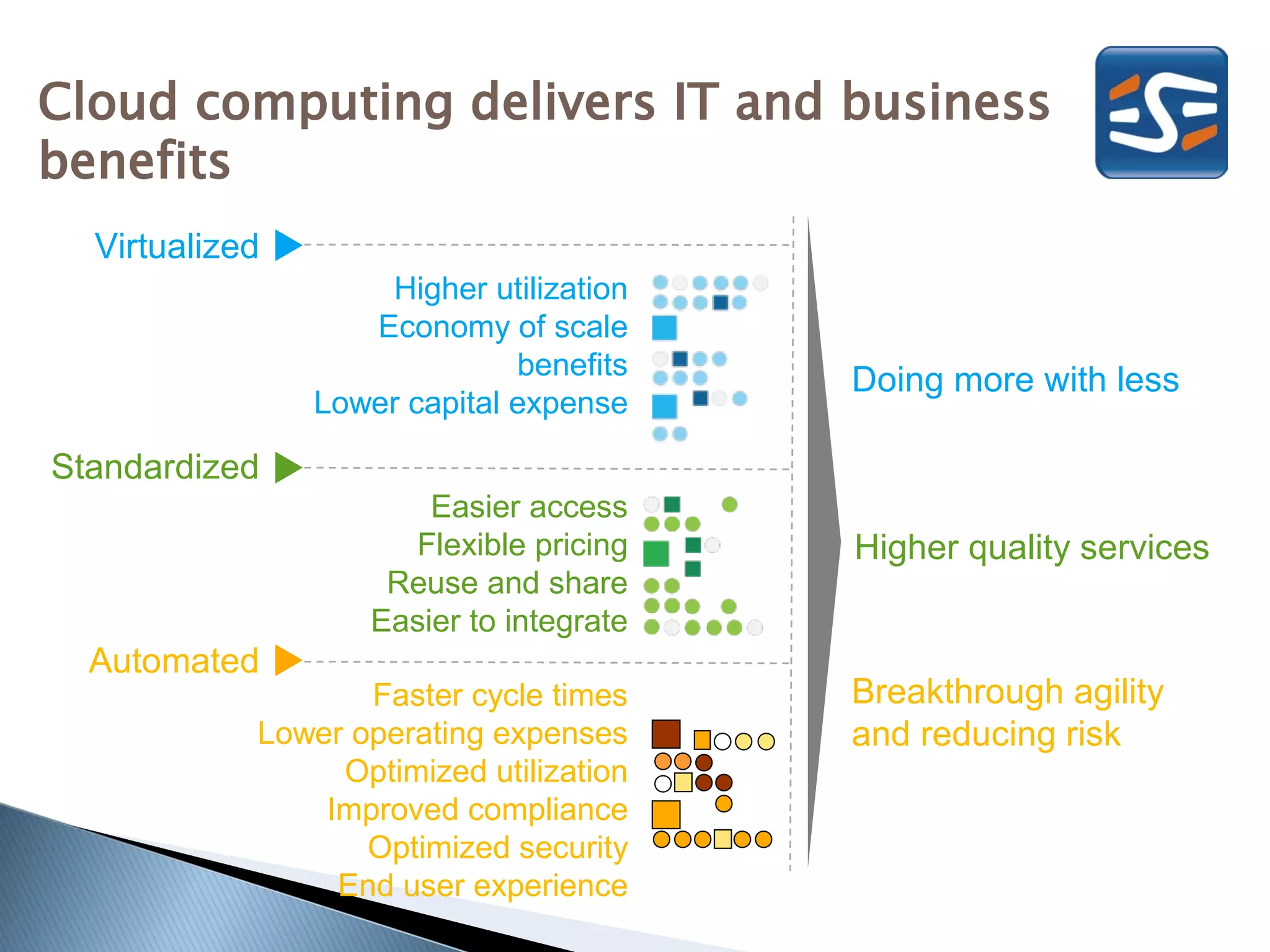
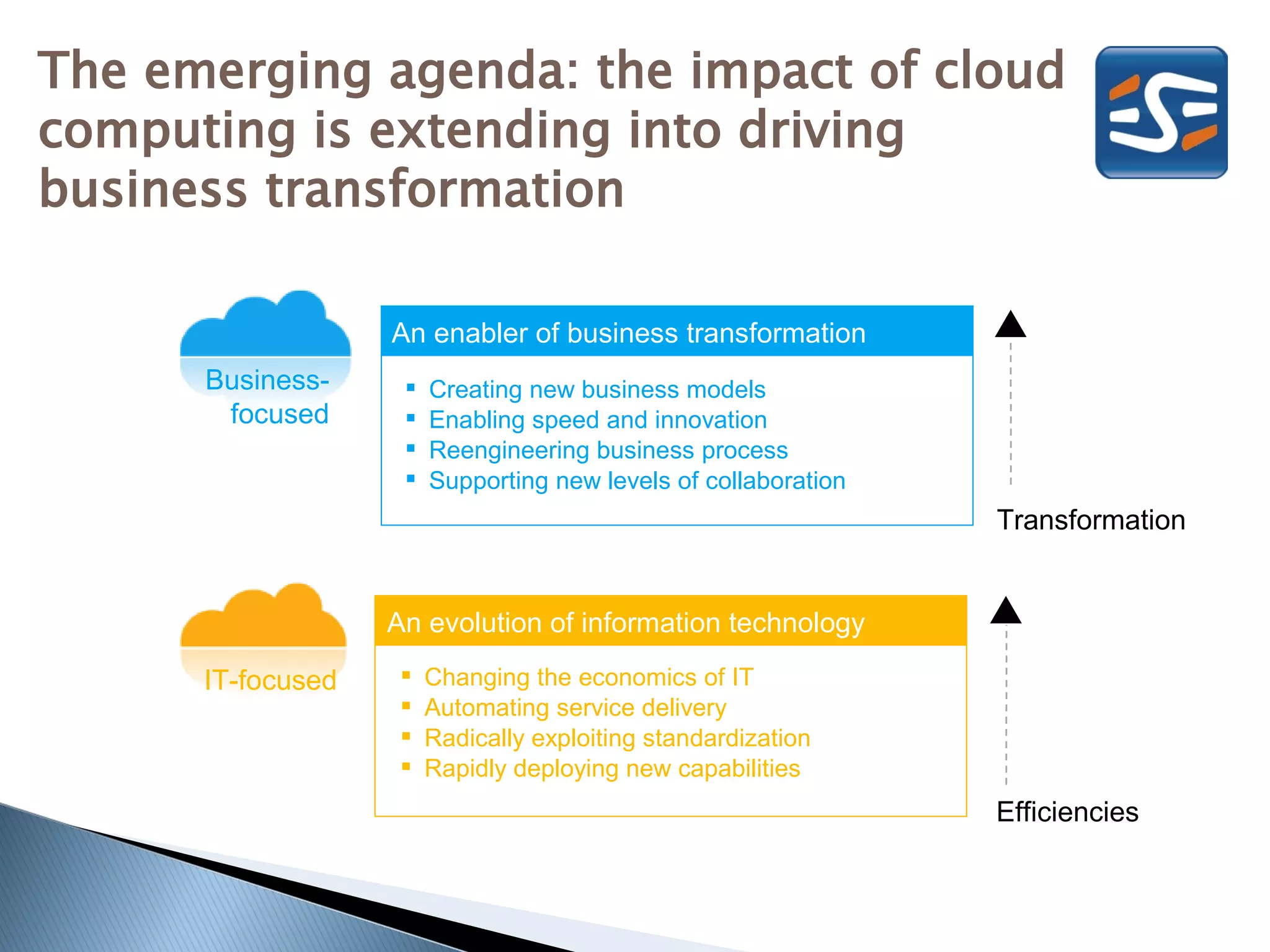
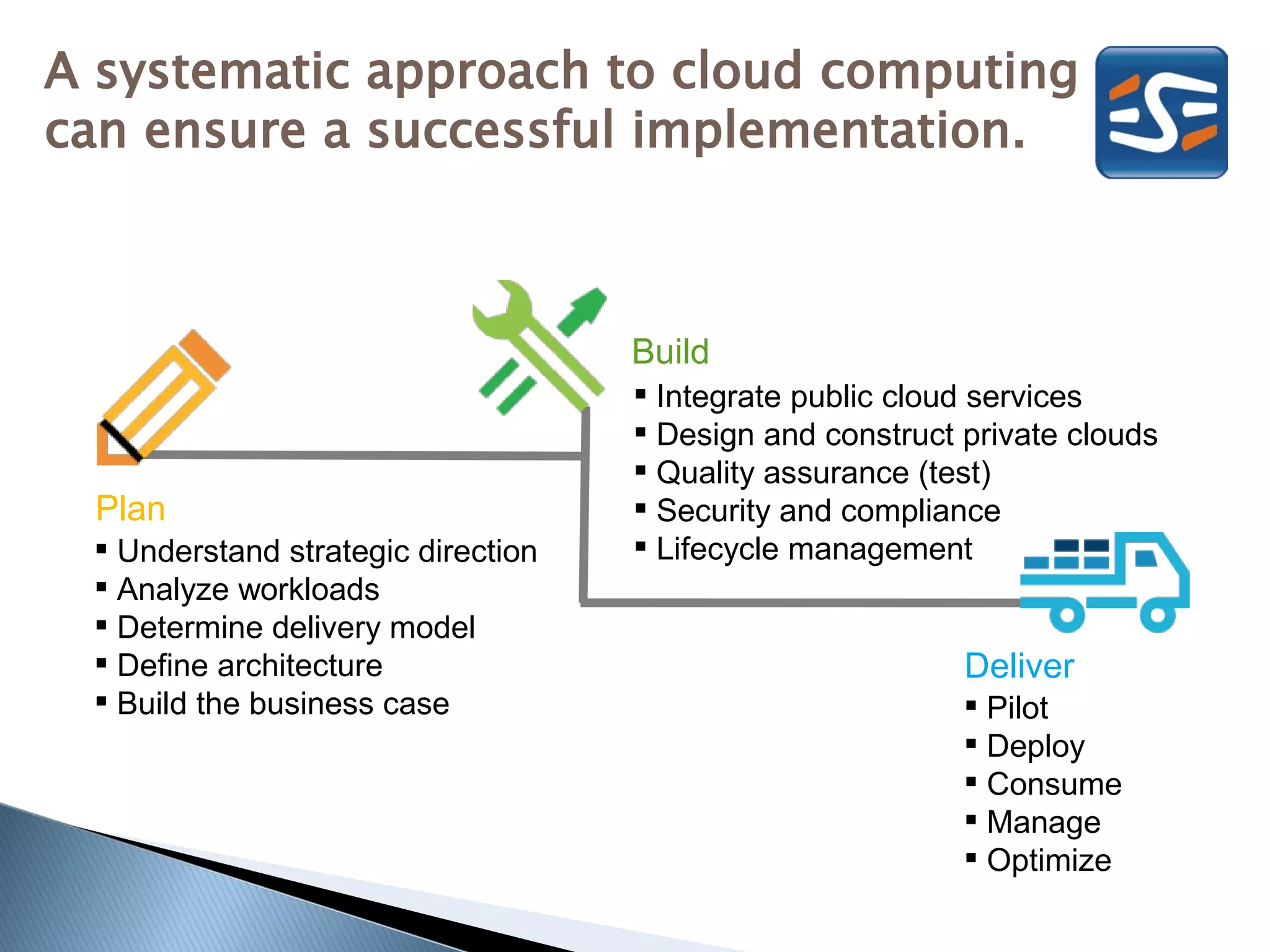
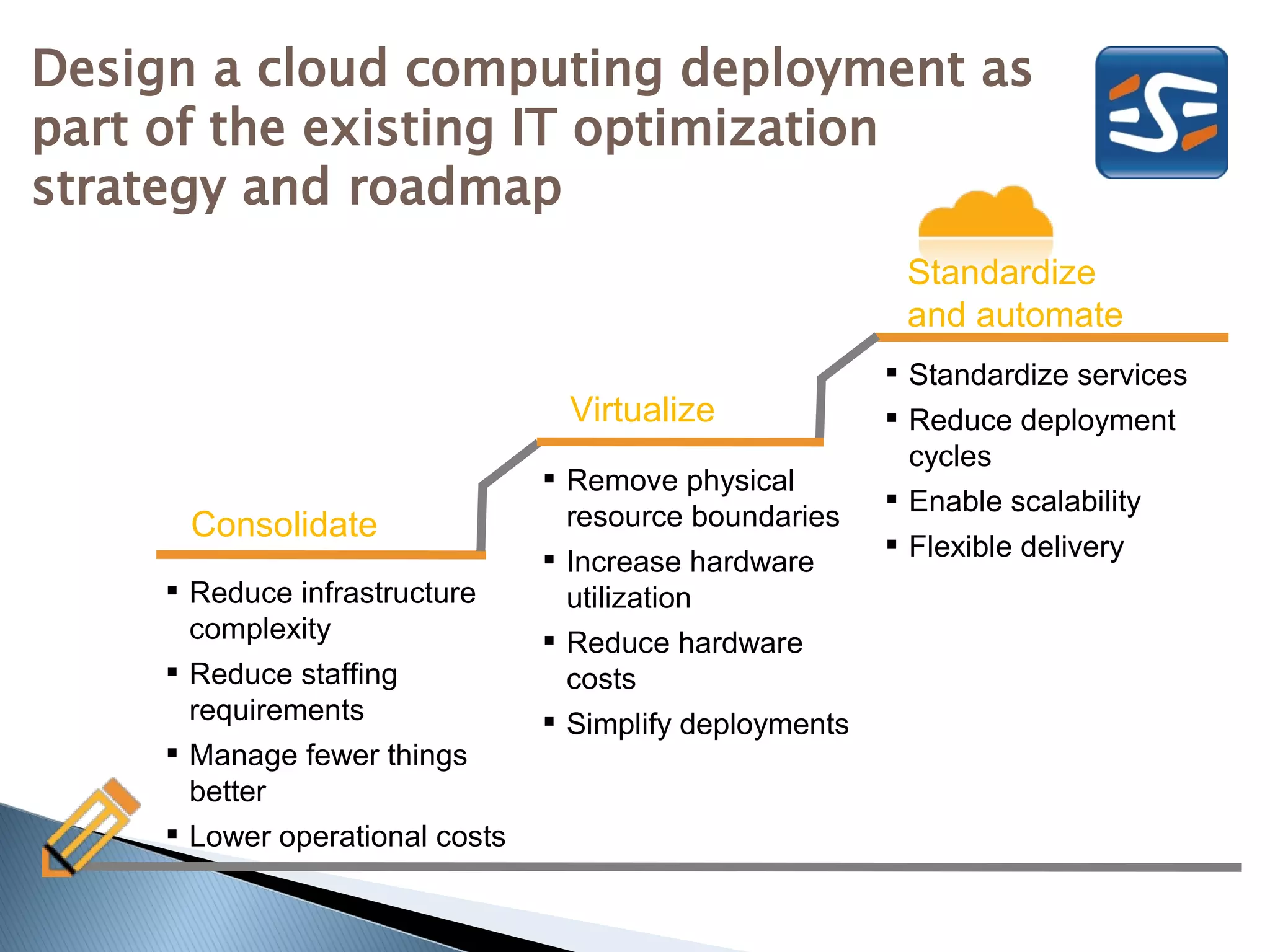
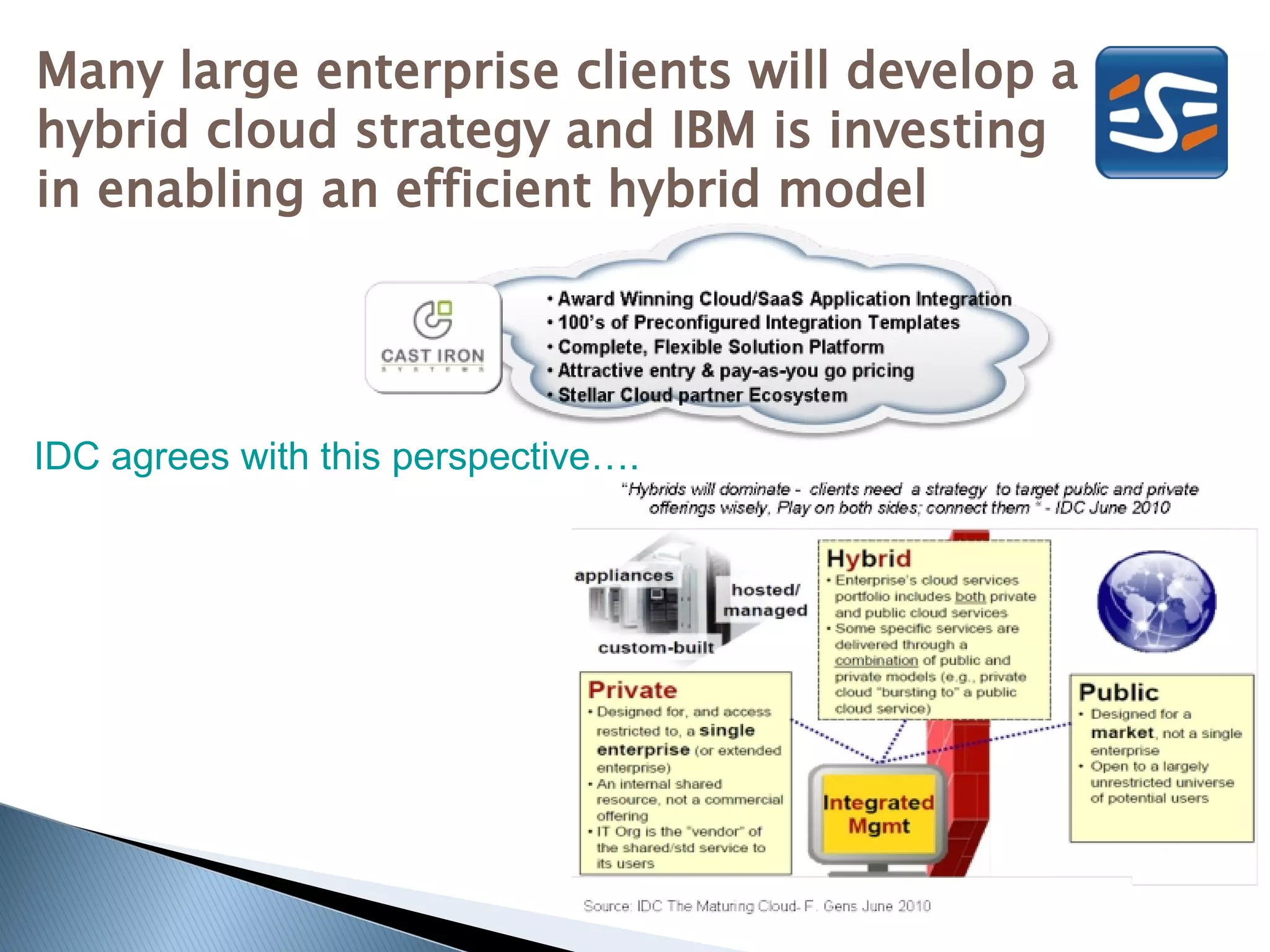
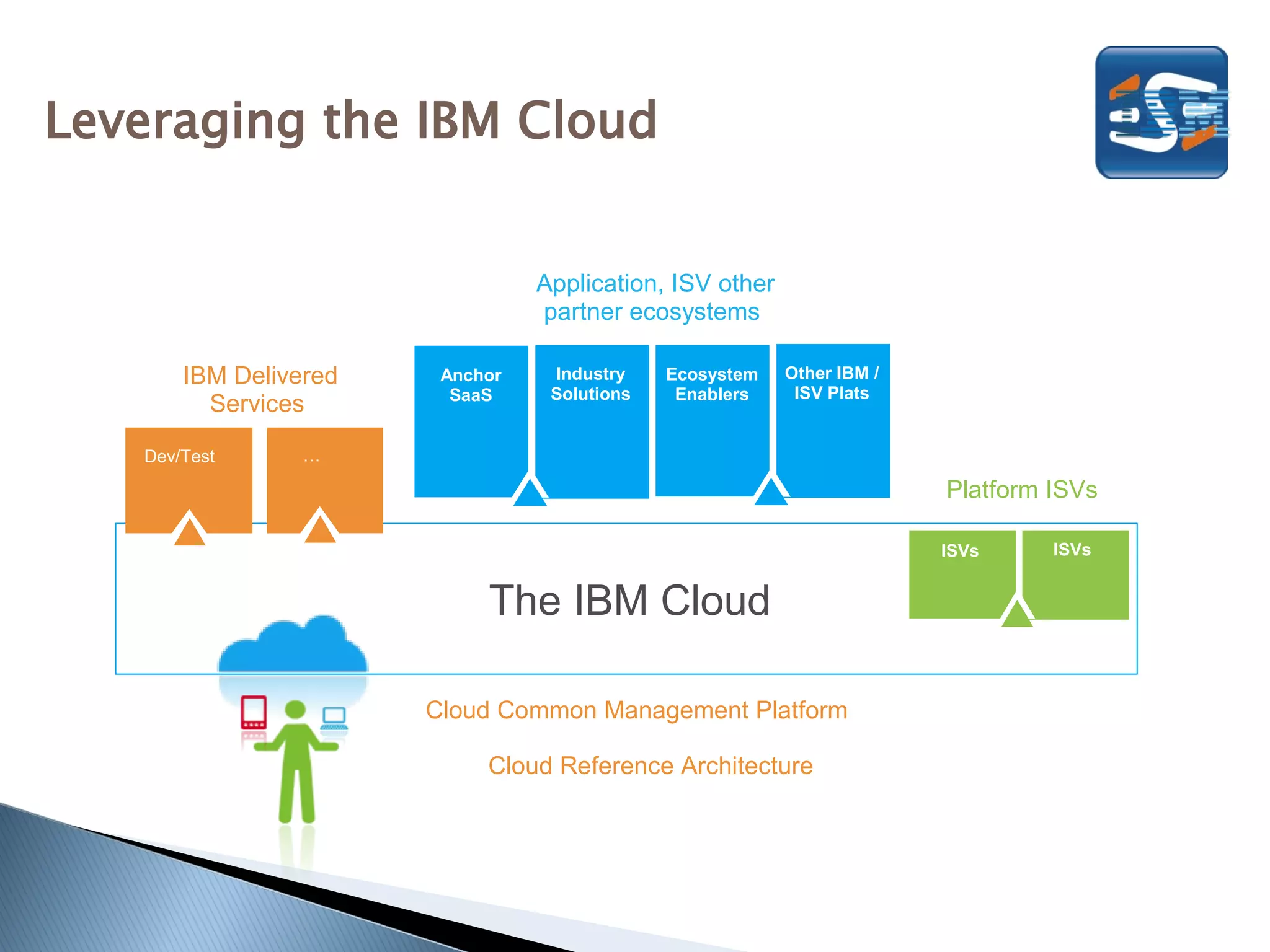
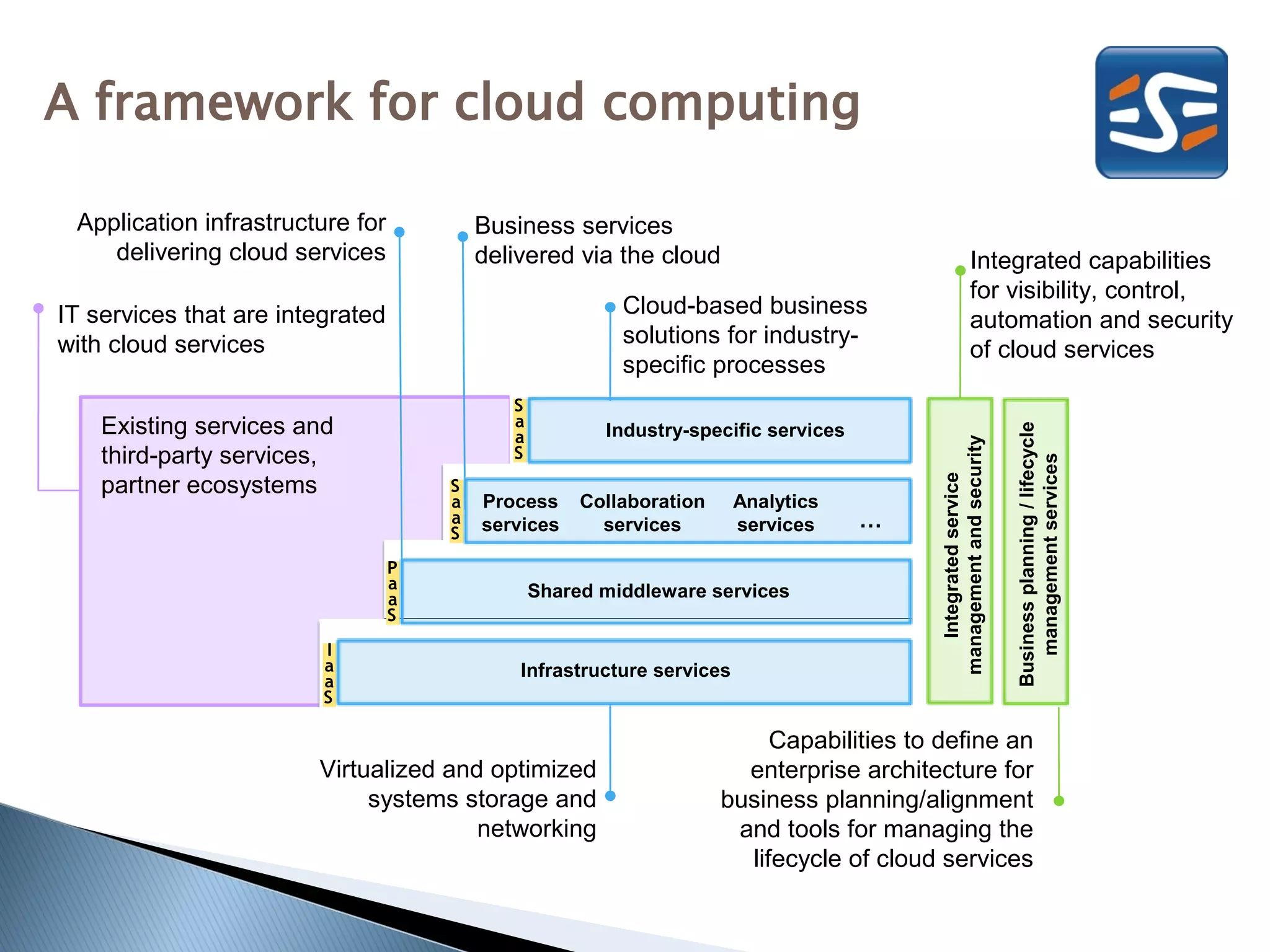
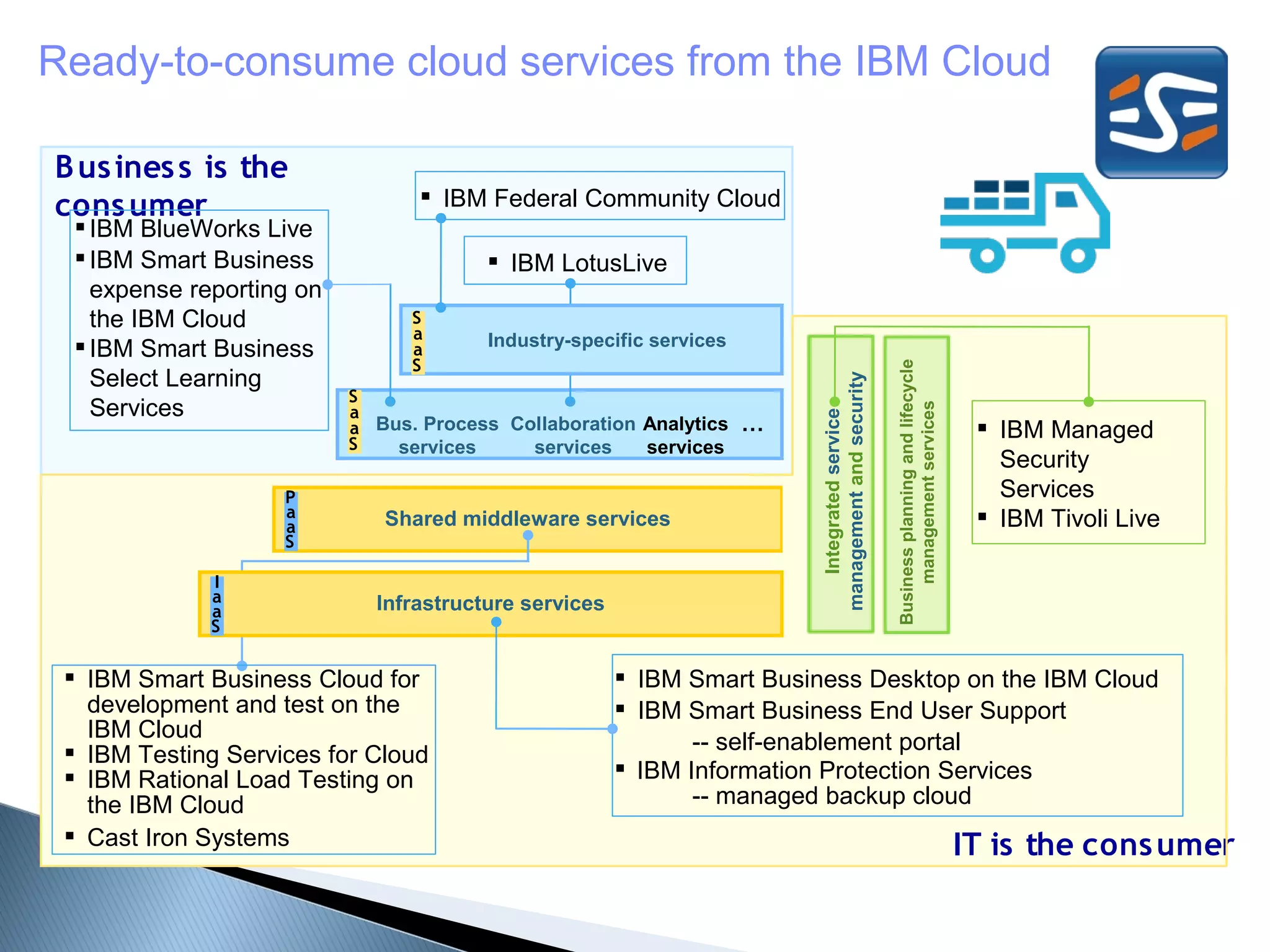
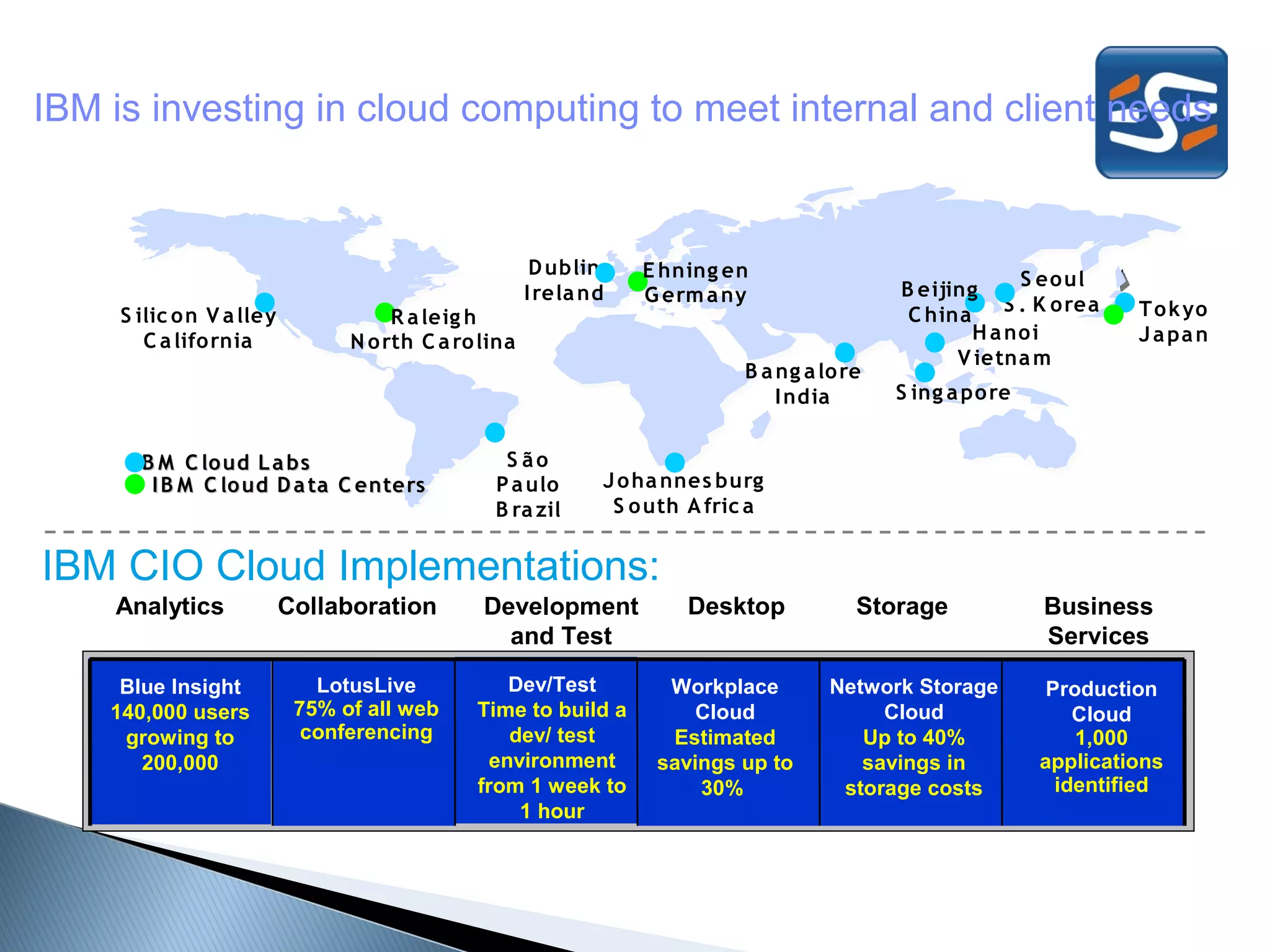
Leon Cruywagen discusses how cloud computing can help businesses address challenges through reduced costs, improved security and resiliency, and increased agility. Cloud computing offers a new consumption and delivery model for IT resources on-demand via the internet. IBM is investing in cloud computing to meet internal and client needs through data centers globally and a portfolio of cloud services across planning, building, and delivering clouds. Working with partners, IBM aims to help businesses optimize their cloud journey and take advantage of the opportunities cloud provides.