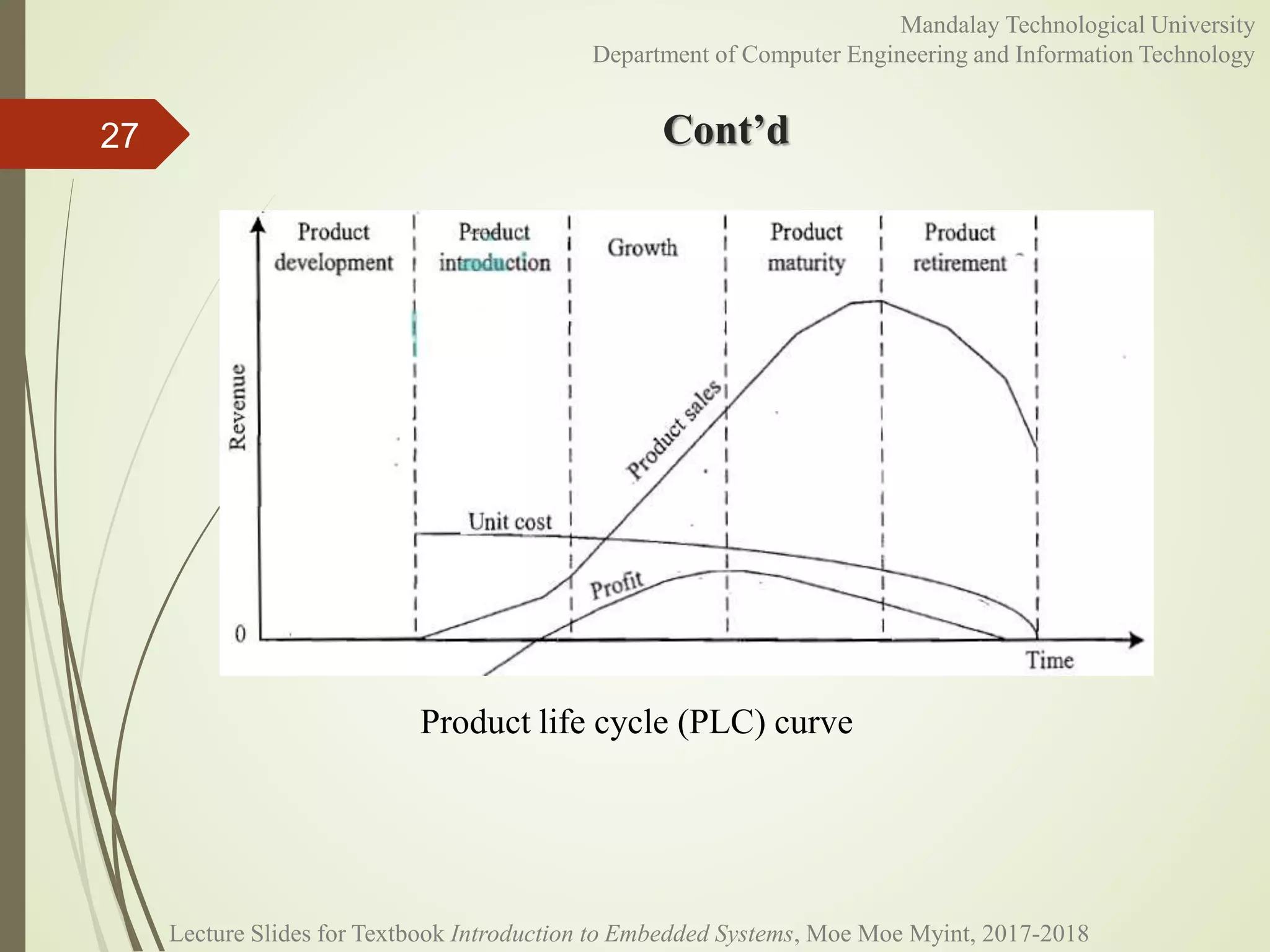
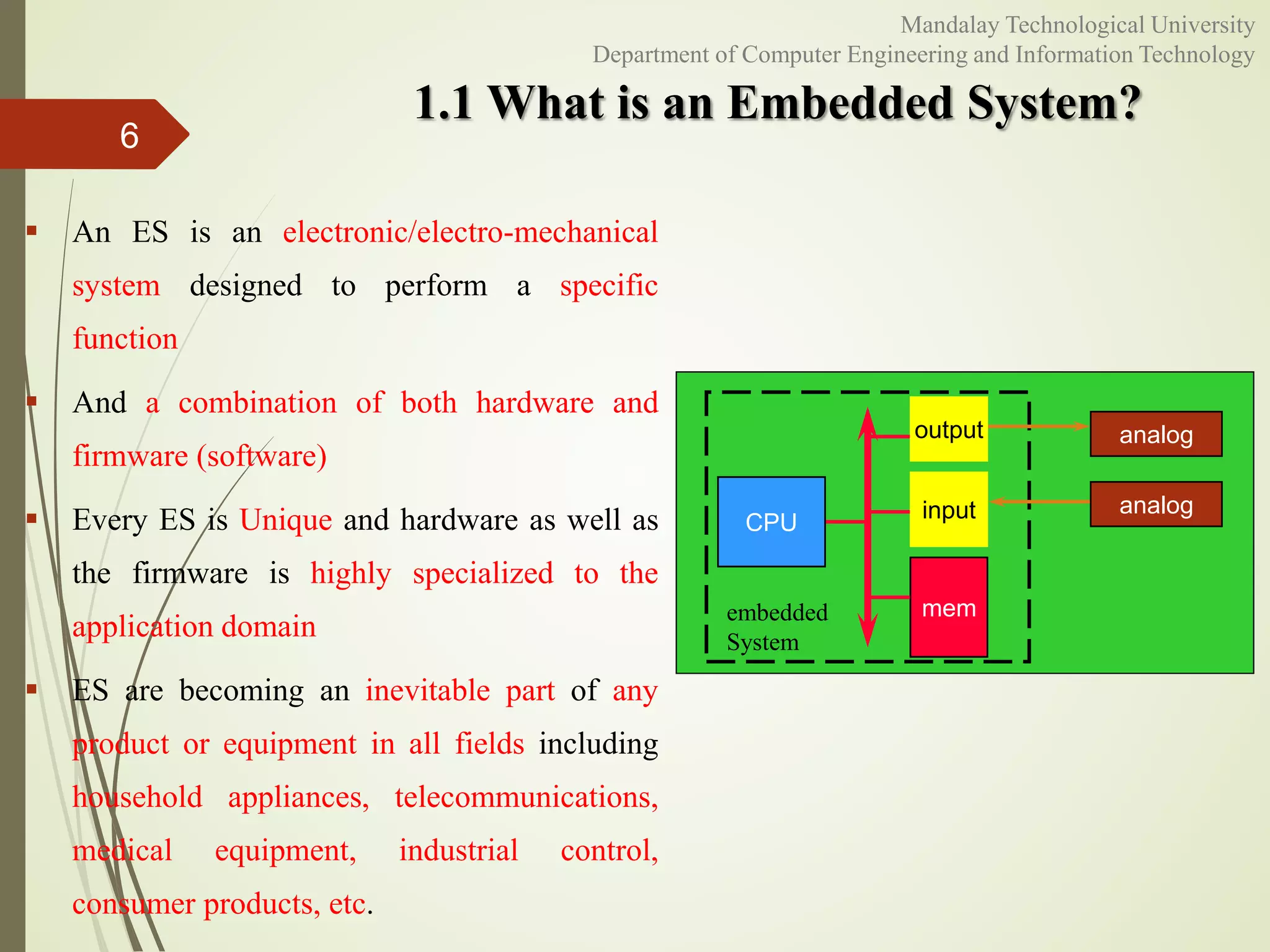
The document discusses the characteristics and quality attributes of embedded systems. It begins by defining embedded systems and noting they are application specific, reactive and operate in real-time, harsh environments, are distributed, and have concerns over size, weight and power. Quality attributes are then categorized into operational and non-operational. Operational attributes include response, throughput, reliability, maintainability, security and safety. Non-operational attributes include testability, evolvability, portability, time to market, and cost. Specific examples are provided to illustrate each attribute.