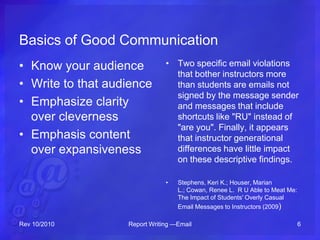
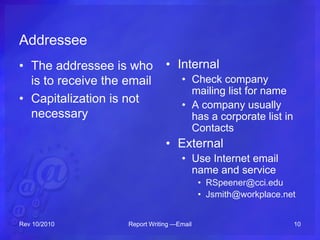
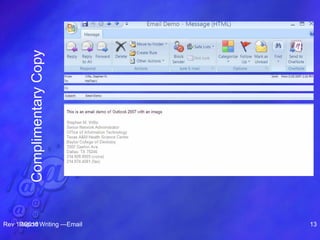
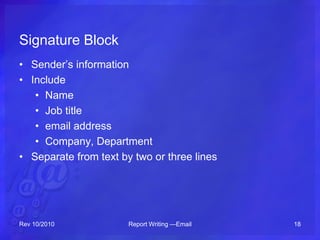
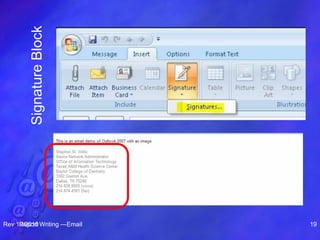
This document provides an overview of email including its definition, parts of an email, etiquette, security risks, and how to write effective emails. It discusses the key components of an email like the addressee, subject line, text, signature, and attachments. It emphasizes the importance of clarity, brevity, and knowing your audience when writing emails. It also outlines best practices for email security including using antivirus software and being cautious of emails from unknown senders.