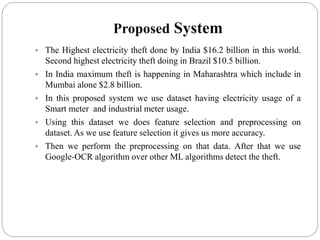
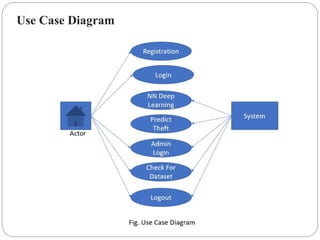
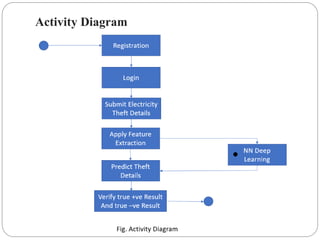
This document presents a project report on detecting electricity theft using machine learning algorithms. The project aims to reduce financial losses to electric utilities caused by electricity theft. It uses a supervised machine learning model trained on meter data to identify abnormal usage patterns indicative of theft. The proposed system applies optical character recognition to meter images to extract consumption data, then performs preprocessing, feature selection, and anomaly detection using algorithms like boosting to accurately detect theft. Key advantages include reduced manual inspection efforts, increased automation, and lower time complexity compared to existing systems.



















![References
Tripathi, Bhasker (26 March 2018). "Now, India is the third largest
electricity producer ahead of Russia, Japan". Business Standard India.
Retrieved 27 September 2019.
"One Nation-One Grid". Power Grid Corporation of India. Retrieved 2
December 2016.
P. Jokar, N. Arianpoo, and V. C. M. Leung, “Electricity theft detection
in AMI using customers’ consumption patterns,” IEEE Trans. Smart
Grid, vol. 7, no. 1, pp. 216-226, Jan. 2016
M. Buzau, J. Aguilera, P. Romero, and A. Expósito, “Detection of Non-
Technical Losses Using Smart Meter Data and Supervised Learning,”
IEEE Trans. Smart Grid, Feb. 2018. [DOI:
10.1109/TSG.2018.2807925]
P. Jokar, N. Arianpoo, and V. C. M. Leung, IEEE Trans. Smart Grid,
vol. 7. (Jan. 2016)
P. J. Rousseeuw, A. M. Leroy, Robust Regression and Outlier
Detection. (Wiley- IEEE, 2003)](https://image.slidesharecdn.com/electricitytheftdetectionusingimageprocessing-201125111736/85/Electricity-theft-detection-using-image-processing-28-320.jpg)
