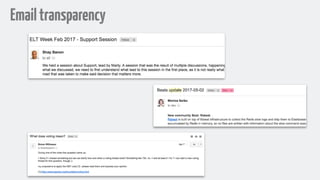
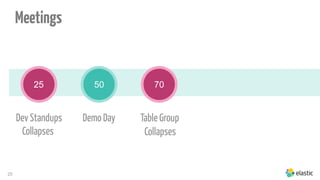
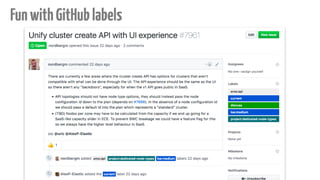
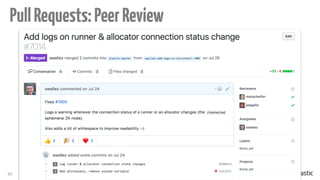
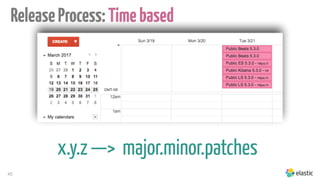
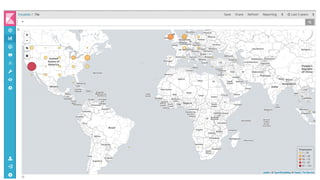
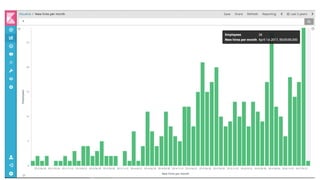
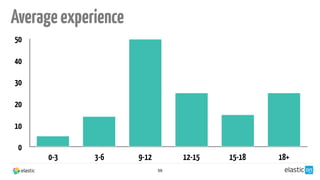
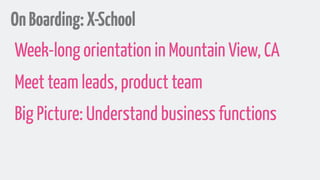
The document details a presentation by Sylvain Wallez at DevFest Toulouse 2017, focusing on scaling a distributed engineering team at Elastic, a company with 600 employees across 32 countries. Additionally, it highlights their communication strategies, meeting structures, and the importance of transparency, autonomy, and trust within their organization. Key takeaways stress the need for open processes and adaptability as the team grows.