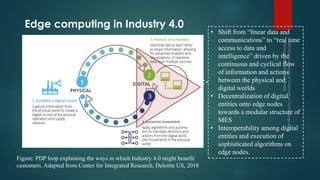
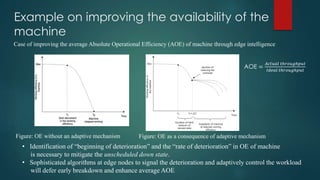
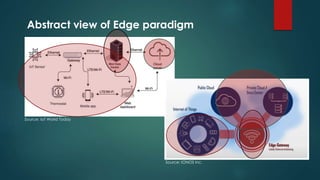
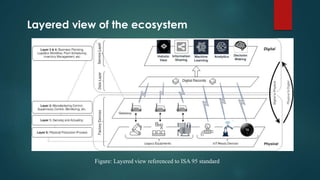
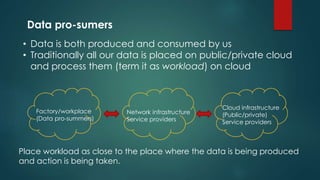
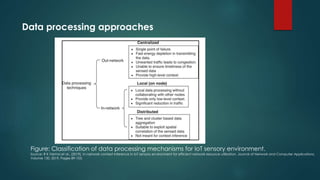
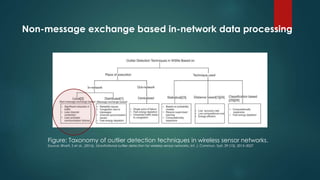
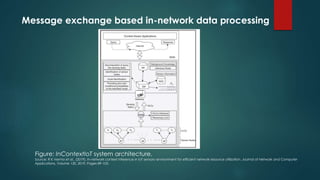
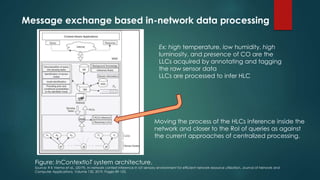
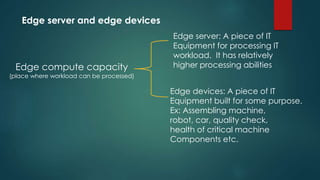
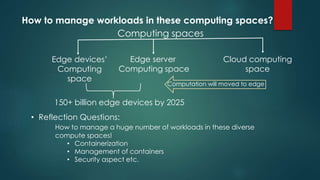
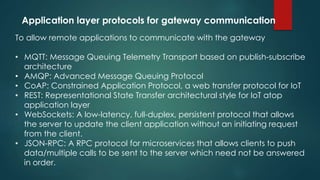
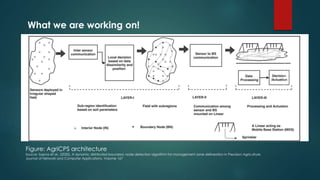
The document discusses the role of edge computing in the architecture of the Internet of Things (IoT), emphasizing its benefits for enhancing operational efficiency and real-time data processing while reducing costs. It outlines various use cases across industries, highlights the importance of decentralized data processing, and presents the technological innovations needed to support edge computing. Key focus areas include predictive maintenance, equipment effectiveness monitoring, and the integration of sophisticated algorithms for improved system performance.