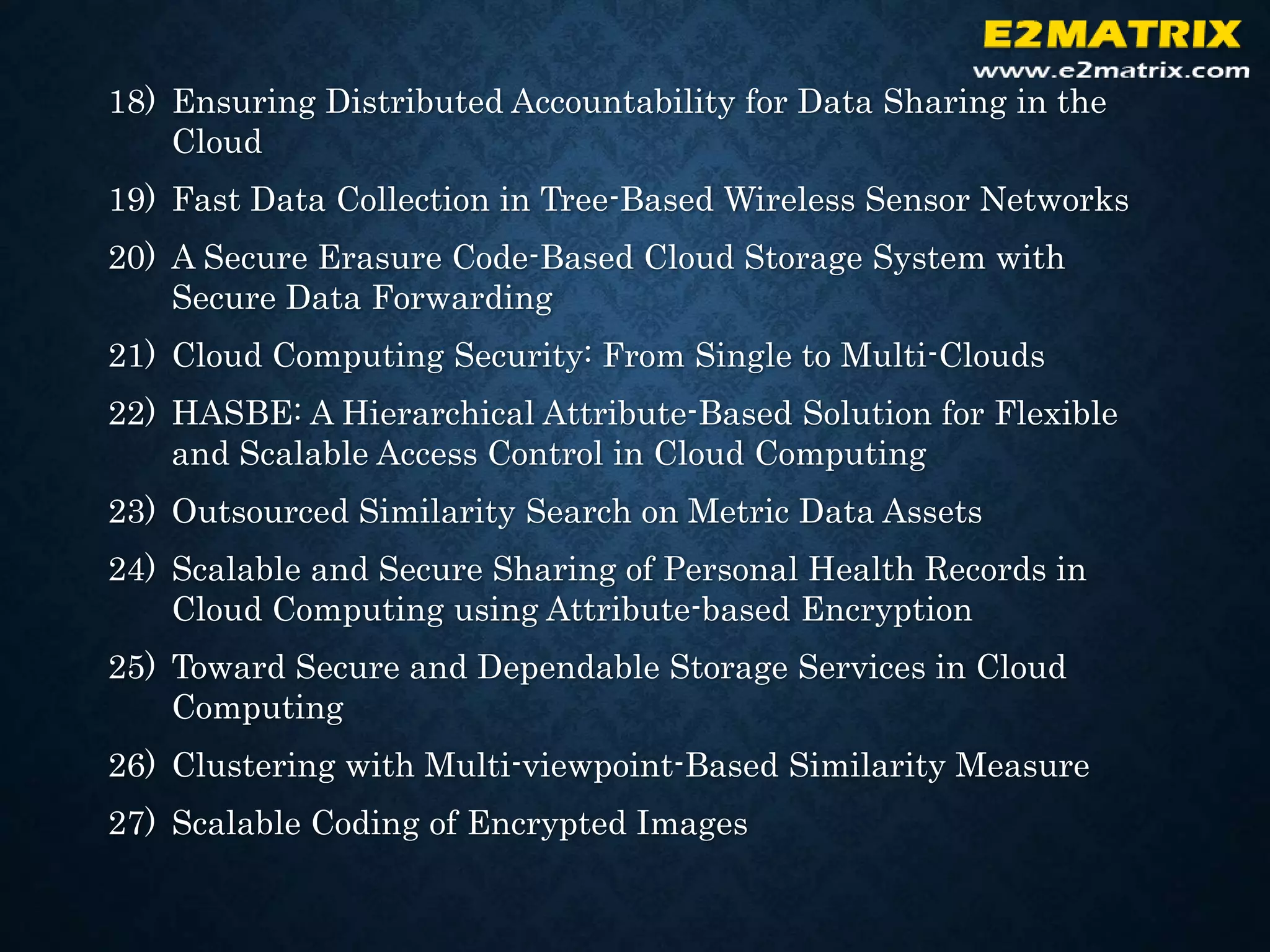
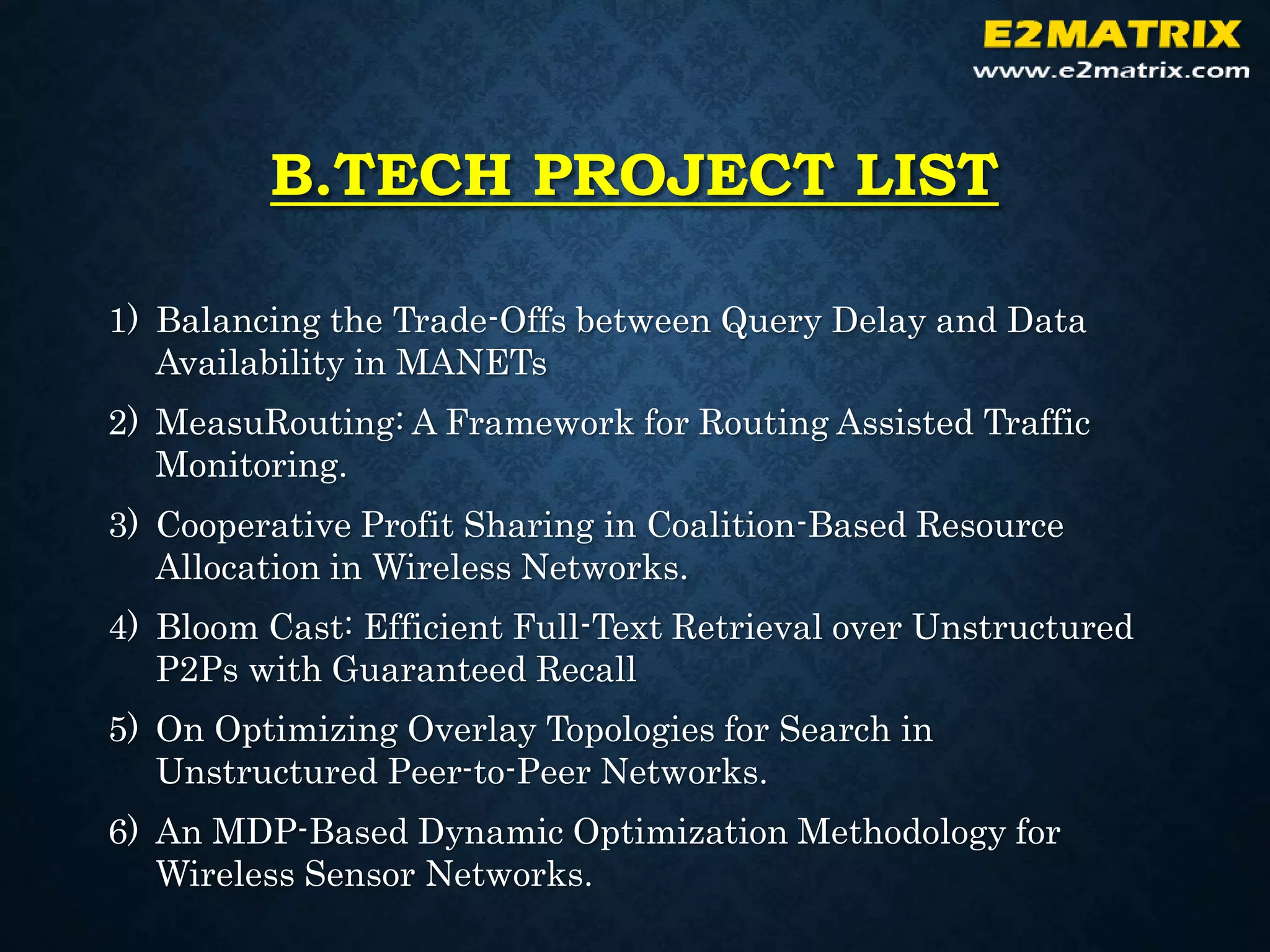
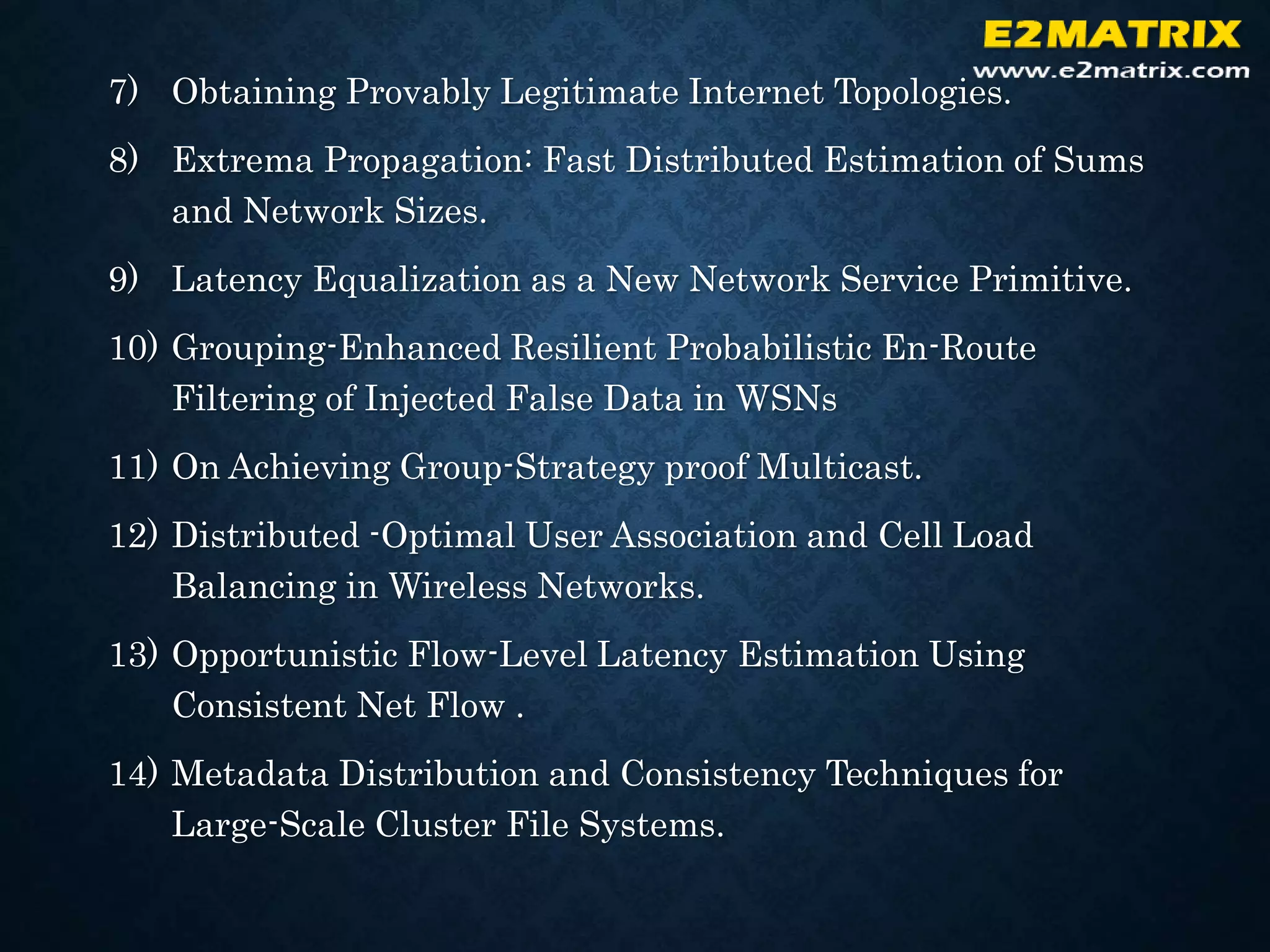
E2MATRIX is an industrial training and project development company that provides services including readymade projects, project guidance, and software development for students in various technology fields such as M.Tech, B.Tech, BE, B.Sc, and MCA. They have experienced trainers and developers who use technologies like MATLAB, Embedded Systems, PLC, VLSI, and more to deliver authenticated project work on time. Their areas of expertise include VLSI, antenna design, optical communication, and wireless technologies. They provide full documentation and support including source code, screenshots, databases, and training.