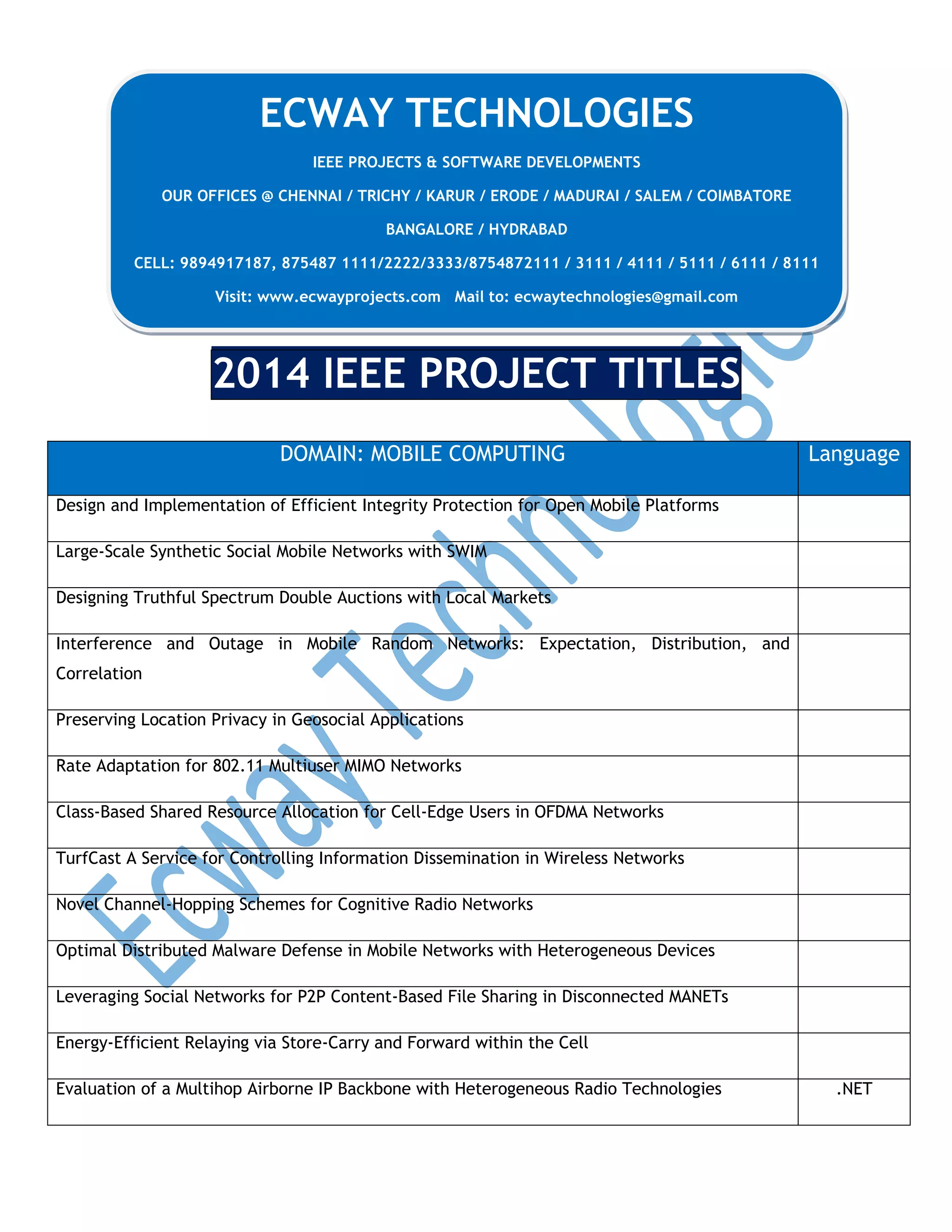
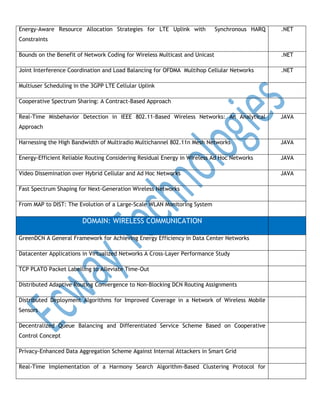
This document provides a summary of IEEE projects and software developments from ECWAY Technologies, an Indian technology company with offices in multiple cities. It lists project titles from 2014 in several domains, including mobile computing, wireless communication, network security, data mining, neural networks, cloud computing, parallel and distributed computing, software engineering, and image processing. The document provides contact information for ECWAY Technologies and a high level overview of the types of projects they undertake without providing many details about the projects themselves.