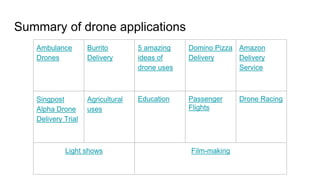
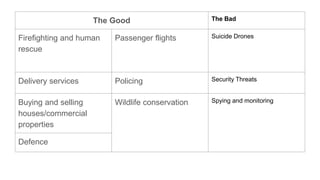
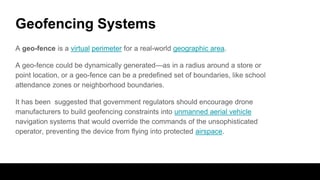
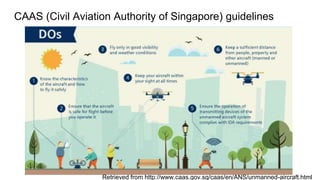
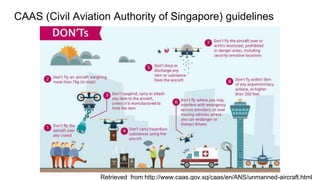
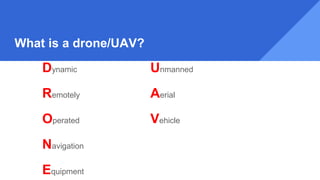
The document outlines various aspects of drones and unmanned aerial vehicles (UAVs), including their definitions, types of users, and diverse applications across sectors like agriculture, delivery, and entertainment. It emphasizes the growing prevalence of civilian drones and discusses the importance of geofencing systems for safety. Additionally, it touches on regulatory guidelines from the Civil Aviation Authority of Singapore pertaining to drone operations.

![What is a drone/UAV?
- It is an aircraft without a human pilot aboard.
- Originated mostly in military applications, although their use is expanding in
commercial, scientific, recreational, agricultural, and other applications,[3]
such as policing and surveillance, aerial photography, agriculture and drone
racing
- Civilian drones now vastly outnumber military drones, with estimates of over
a million sold by 2015.
- Read the History of UAVs here.](https://image.slidesharecdn.com/dronesinformation-170110150856/85/Drones-101-4-320.jpg)