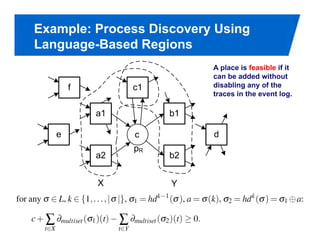
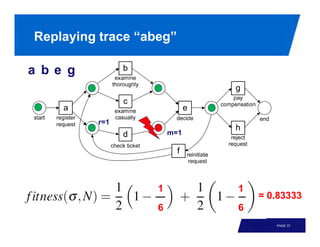
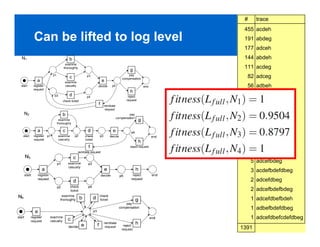
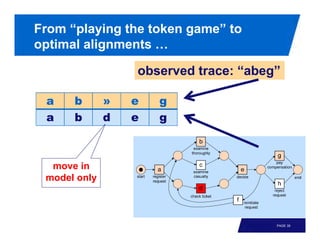
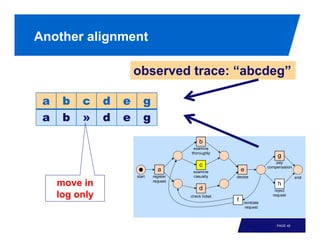
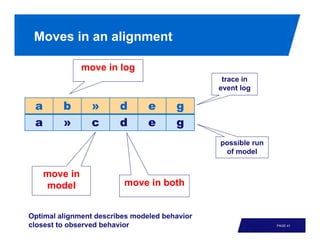
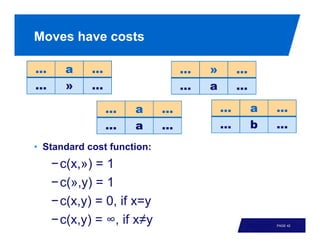
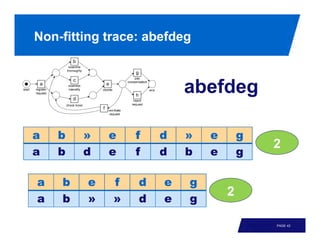
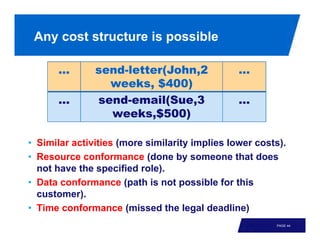
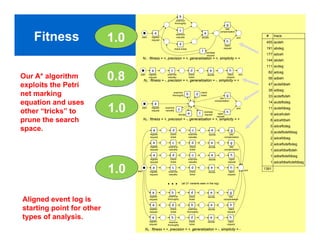
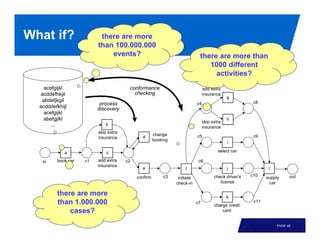
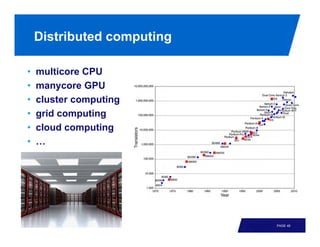
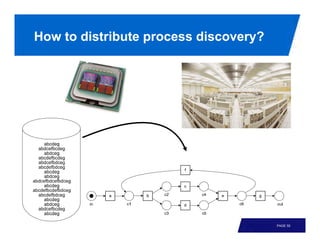
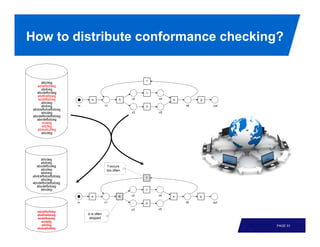
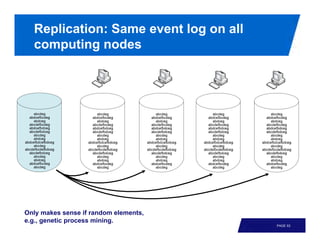
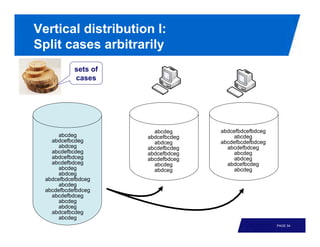
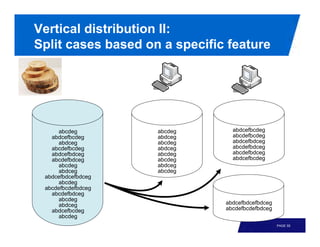
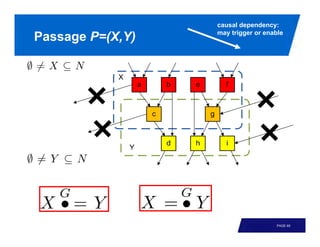
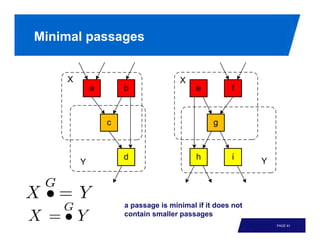
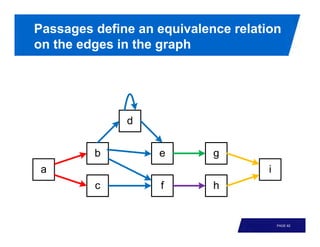
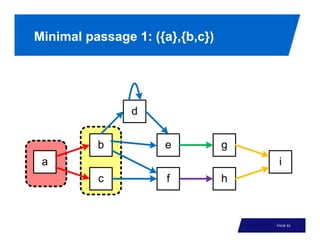
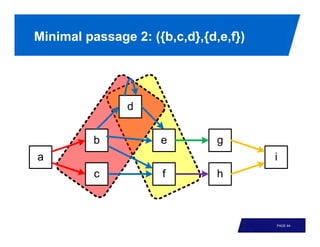
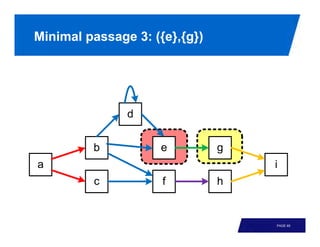
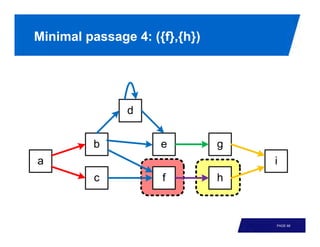
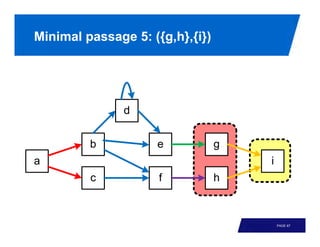
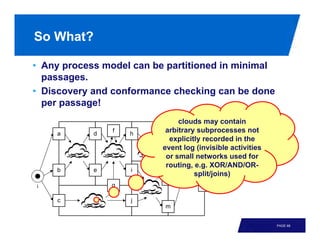
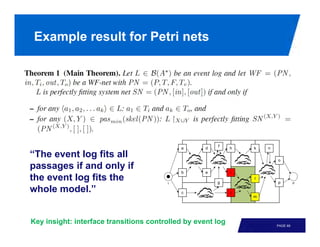
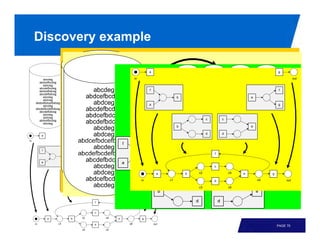
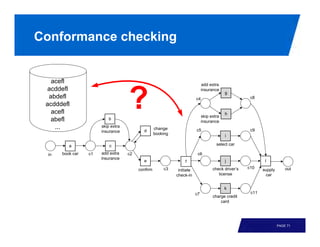
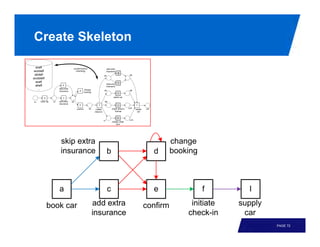
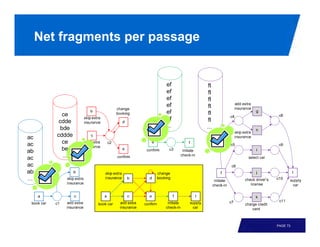
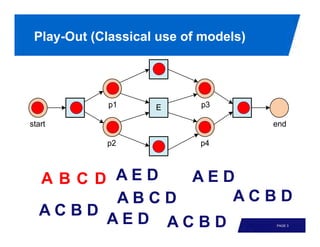
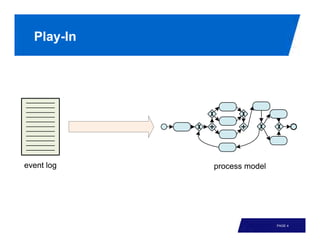
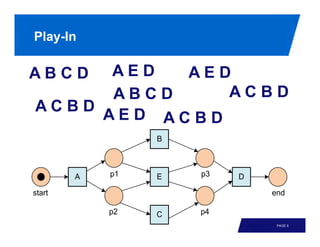
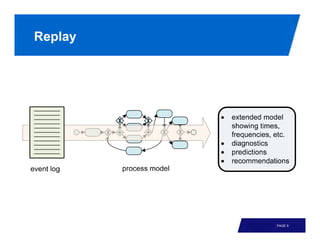
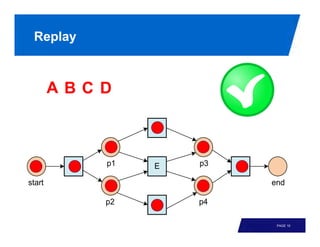
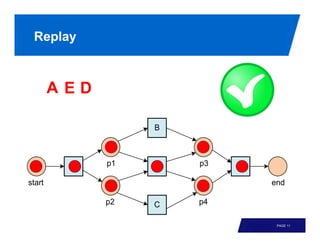
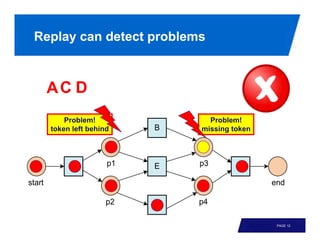
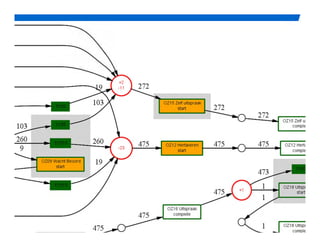
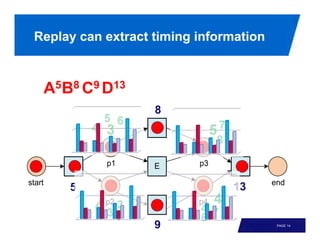
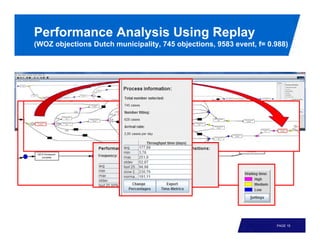
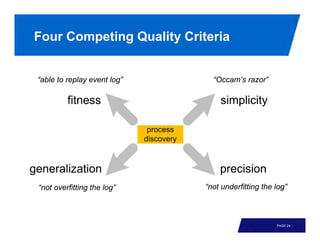
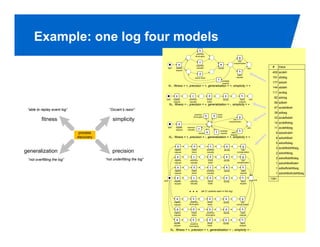
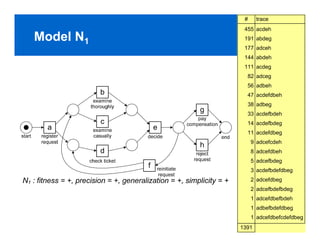
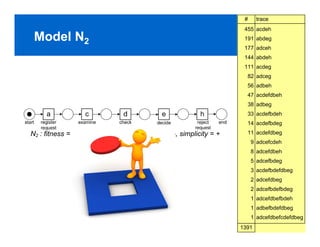
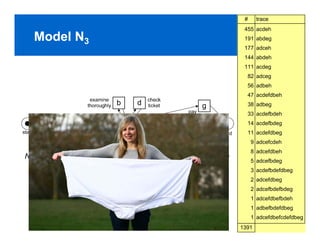
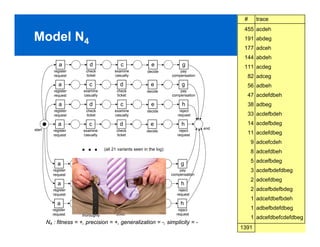
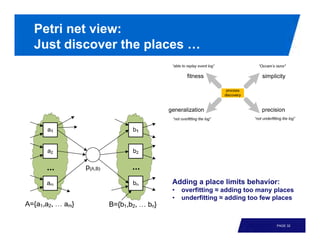
The document discusses process discovery and conformance checking. It begins with an introduction to different roles of process models and examples of process discovery on real event logs. It then covers topics like replay, conformance checking, and analyzing models based on criteria like fitness and simplicity. Process discovery algorithms discussed include state-based regions and language-based regions approaches. The document explains how conformance checking involves replaying traces and calculating alignments between event logs and models.

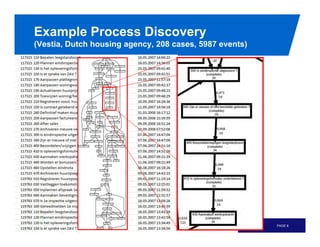




![Example: Process Discovery Using
State-Based Regions
d
e
[a,e] [a,d,e]
[ a,b]
a b
[] [a] c
c
b d
[a,c] [a,b,c] [a,b,c,d]
b
a p1 e p3 d
start end
p2 c p4
PAGE 33](https://image.slidesharecdn.com/fase-2012-invited-talk-wvda-120327090511-phpapp01/85/Distributed-Process-Discovery-and-Conformance-Checking-34-320.jpg)
![Example of Region
d
e
[a,e] [a,d,e]
[ a,b]
a b
[] [a] c
c
b d
[a,c] [a,b,c] [a,b,c,d]
enter: b,e
leave: d
do-not-cross: a,c
b
a p1 e p3 d
start end
p2 c p4
PAGE 34](https://image.slidesharecdn.com/fase-2012-invited-talk-wvda-120327090511-phpapp01/85/Distributed-Process-Discovery-and-Conformance-Checking-35-320.jpg)