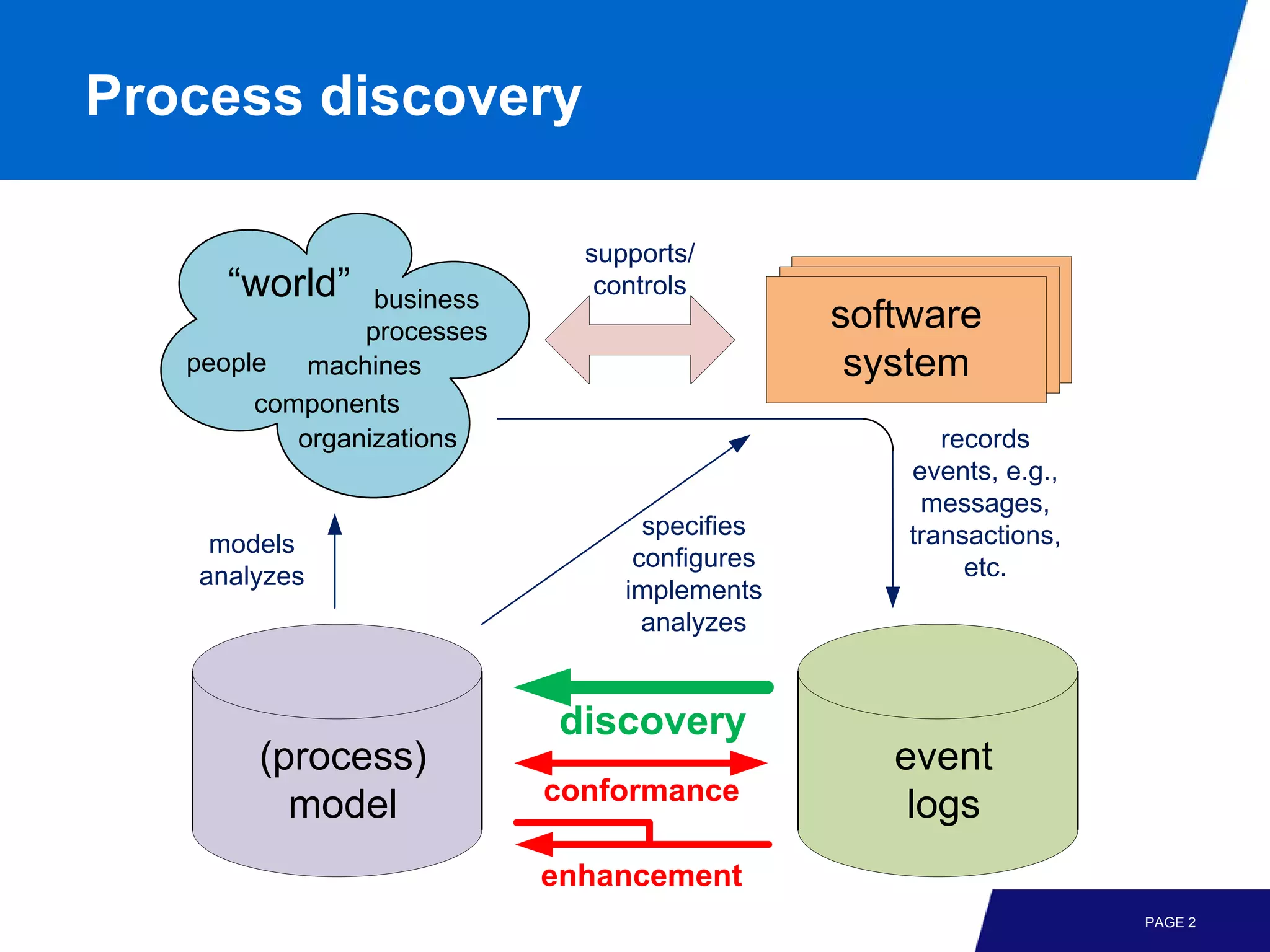
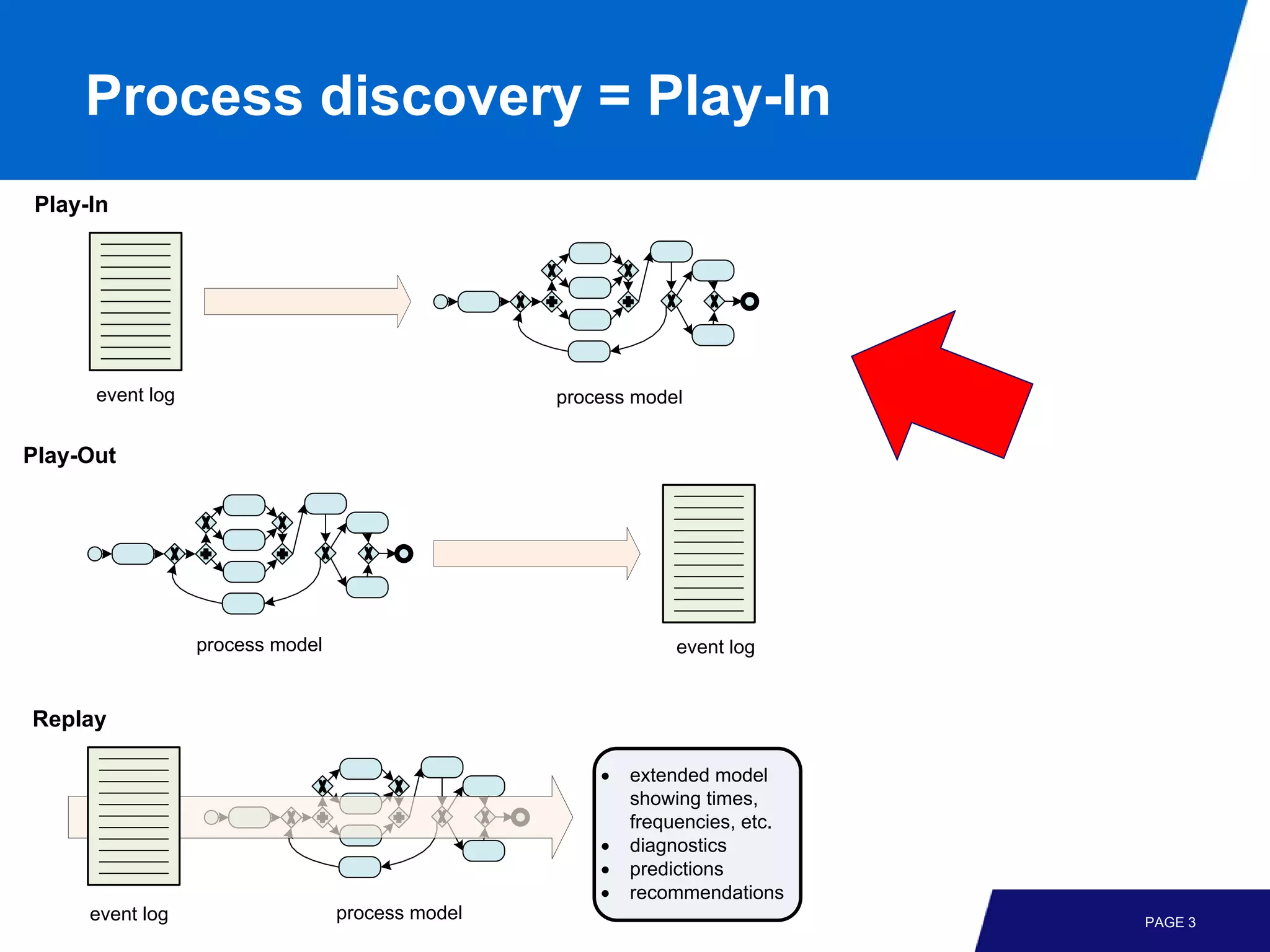
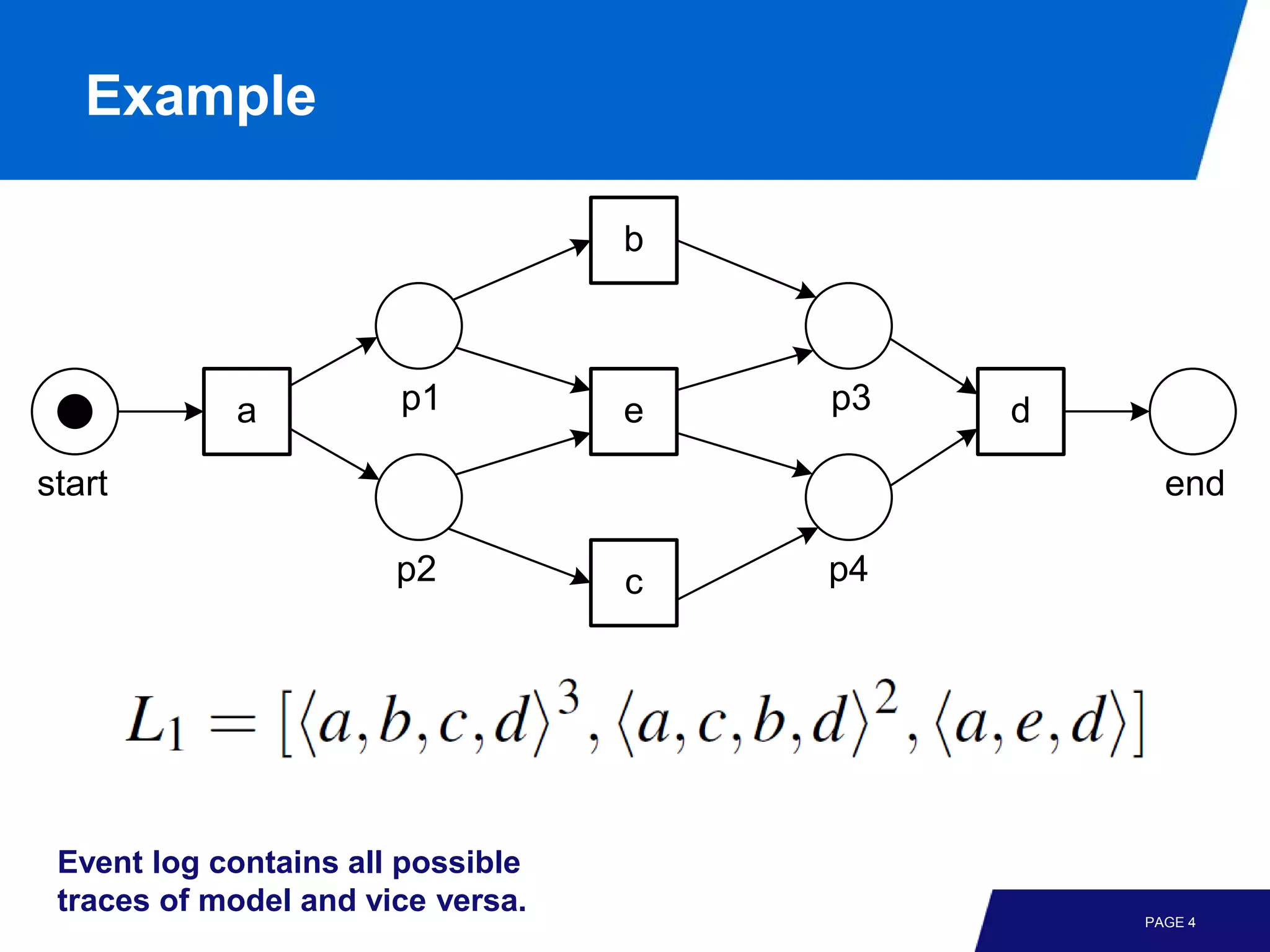
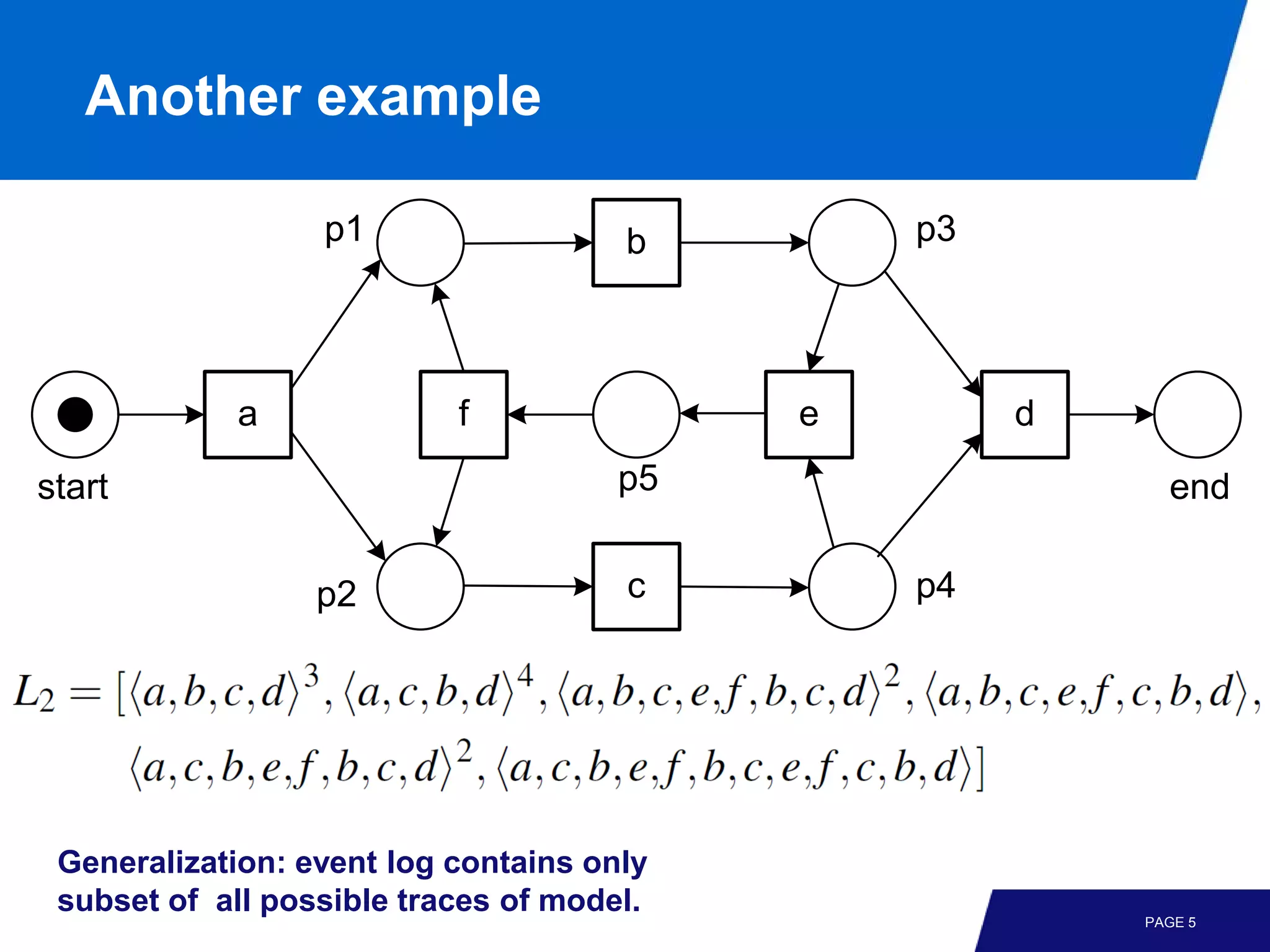
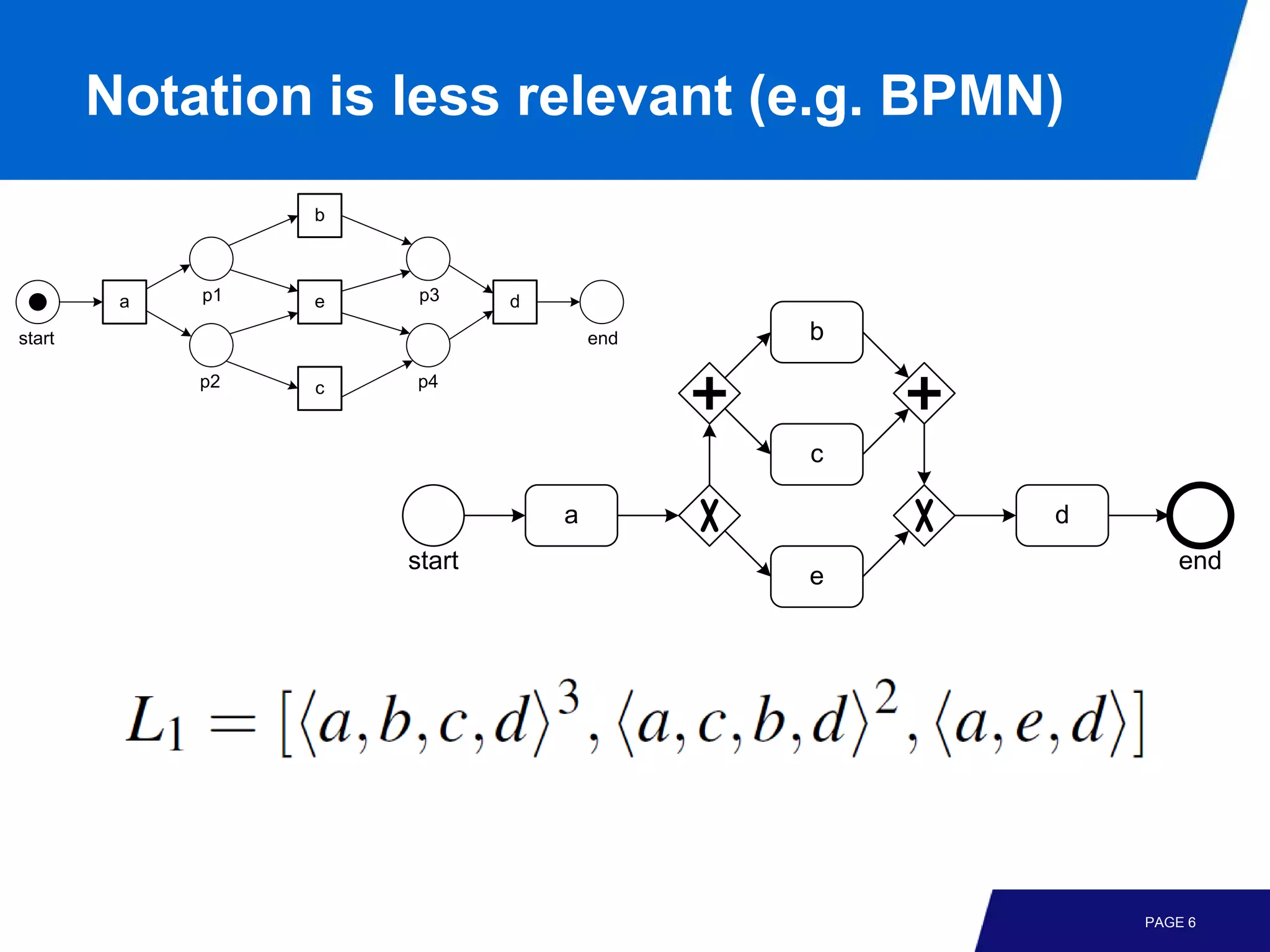
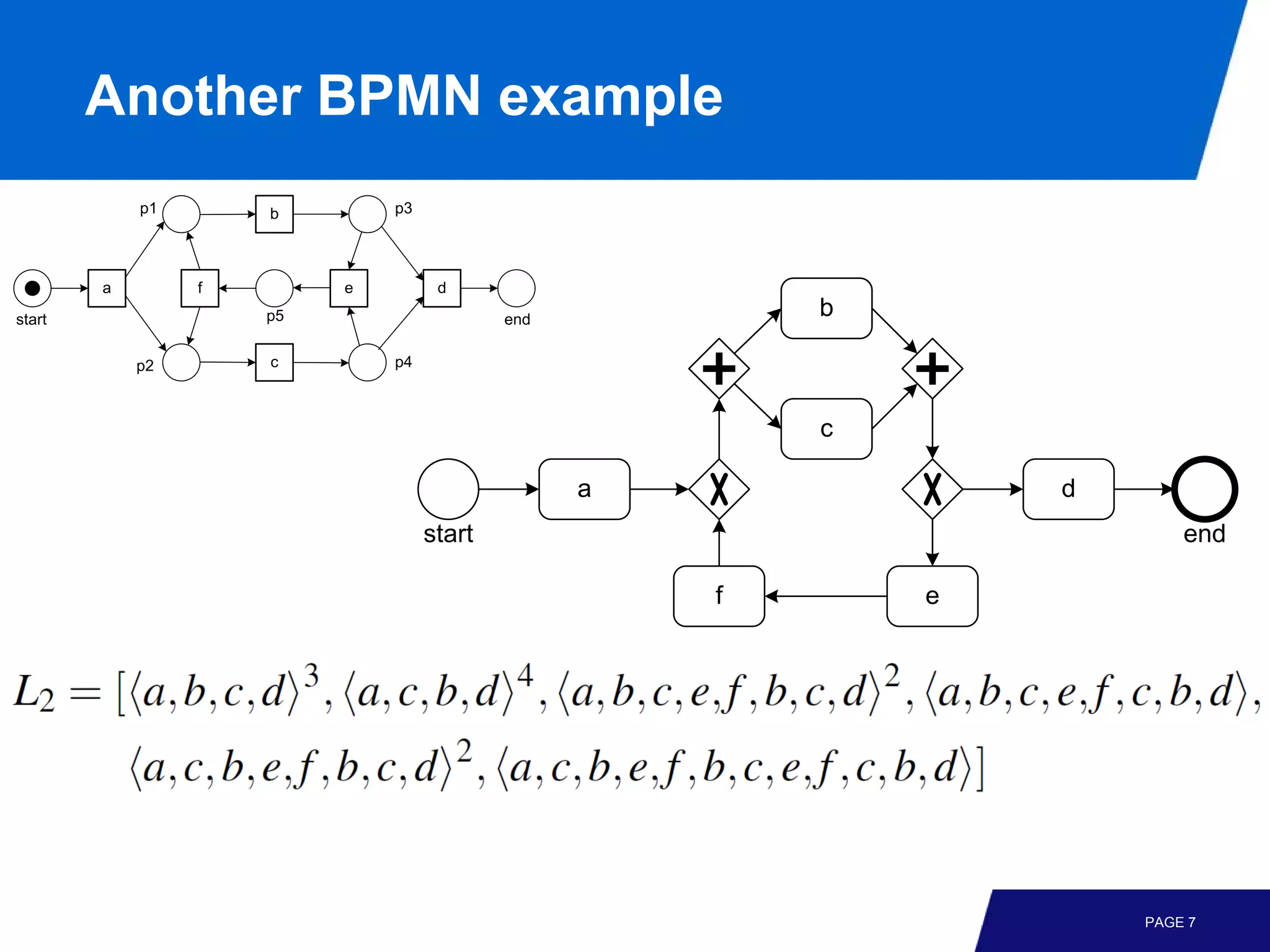
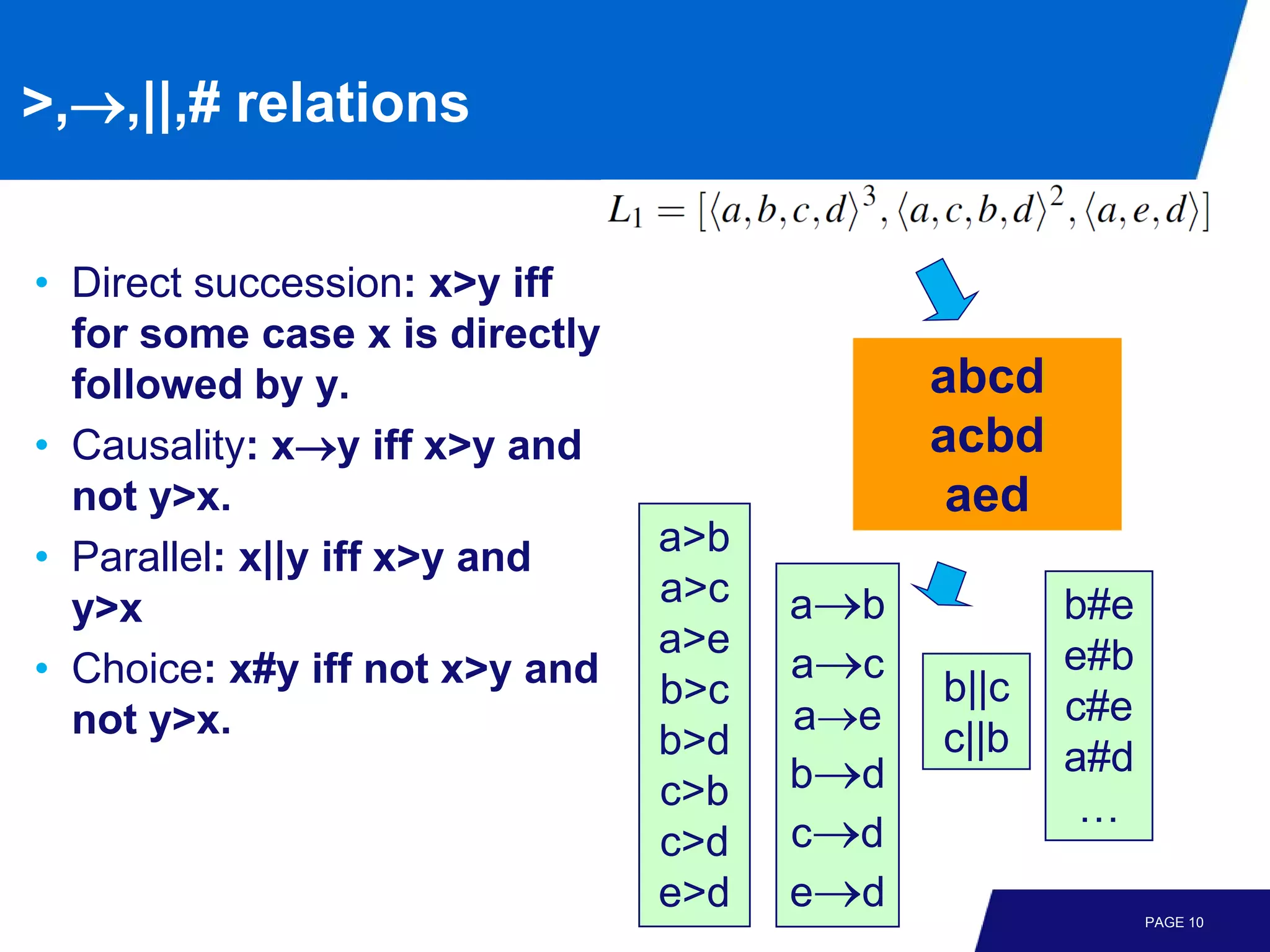
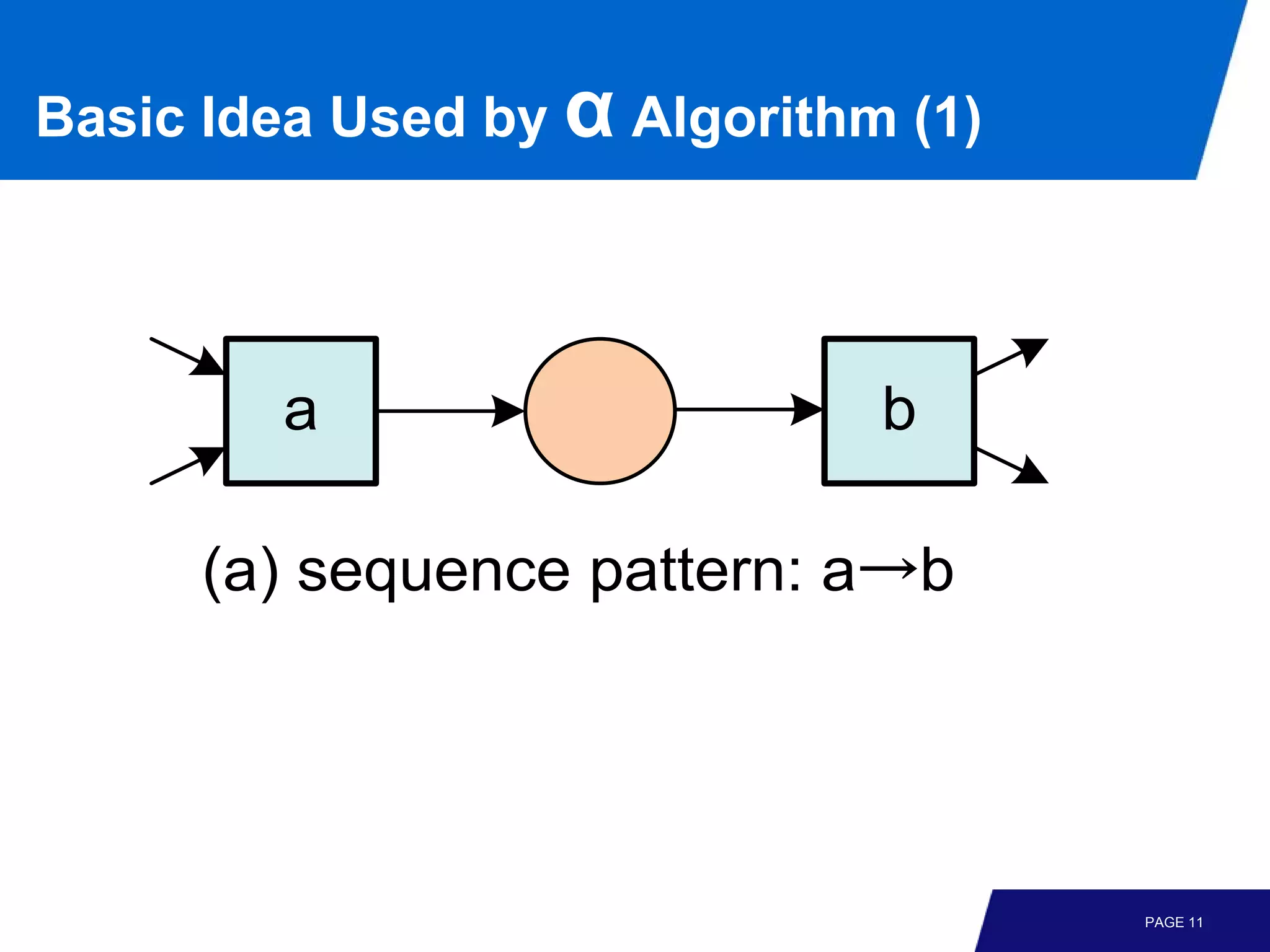
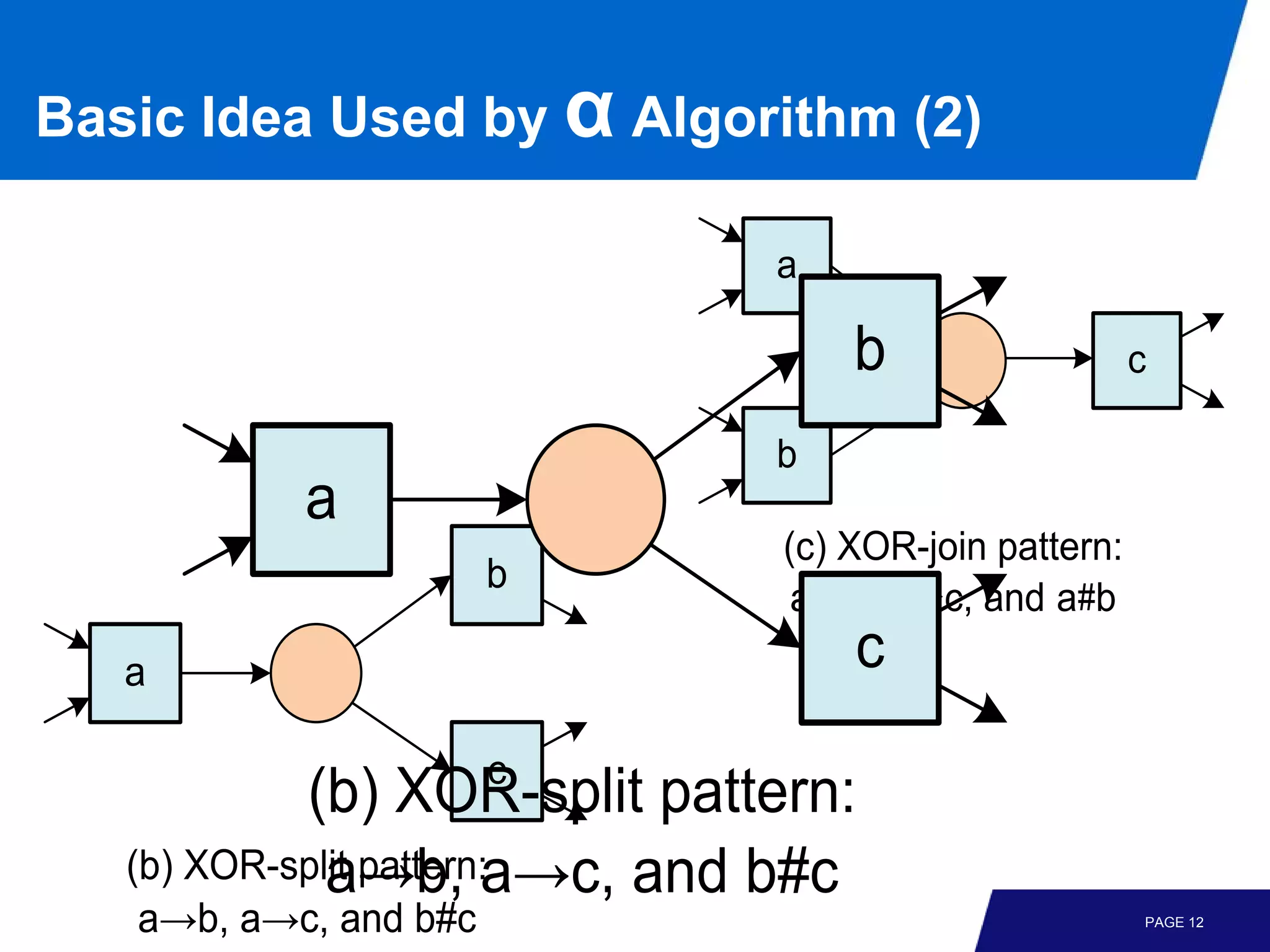
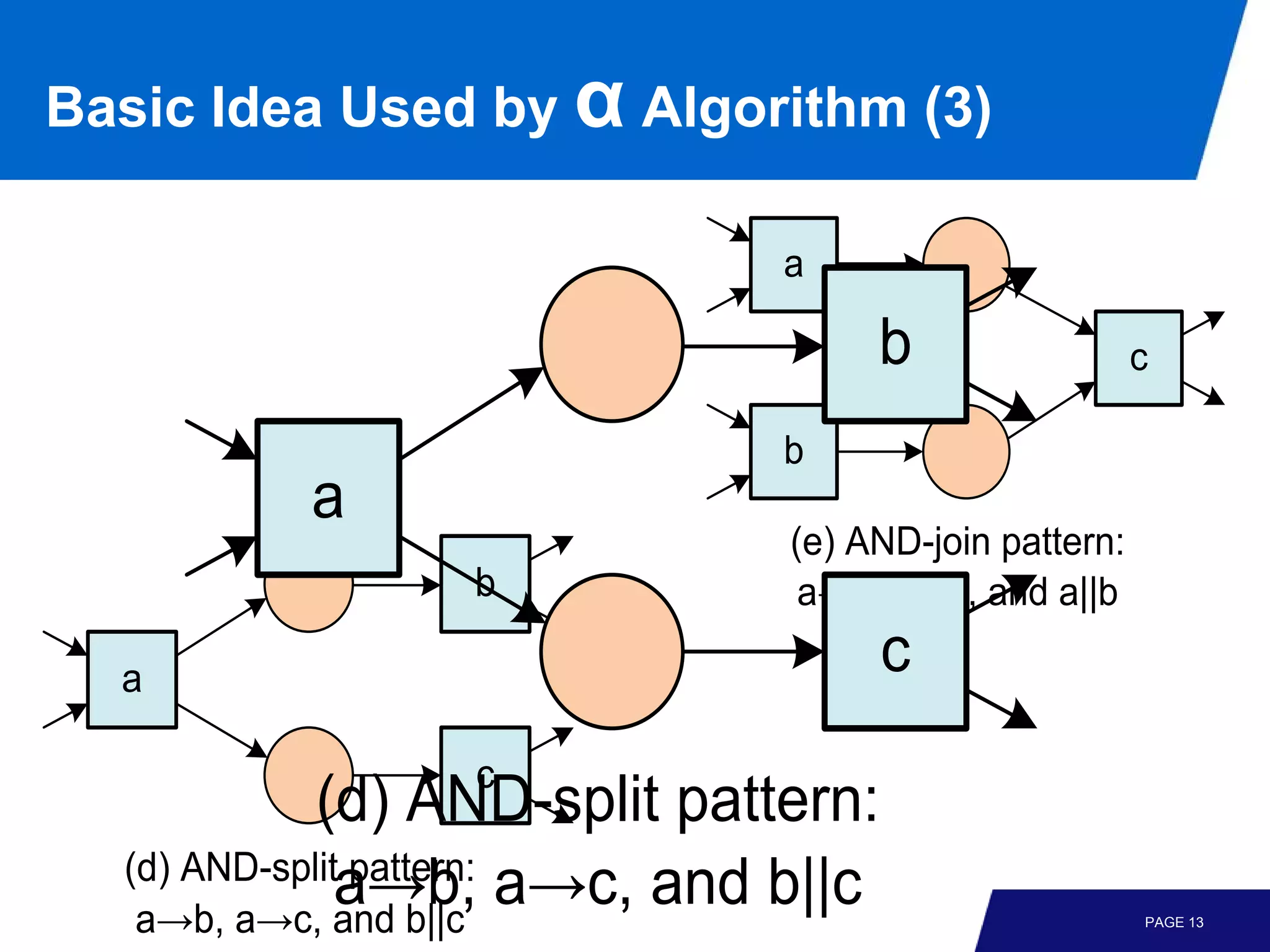
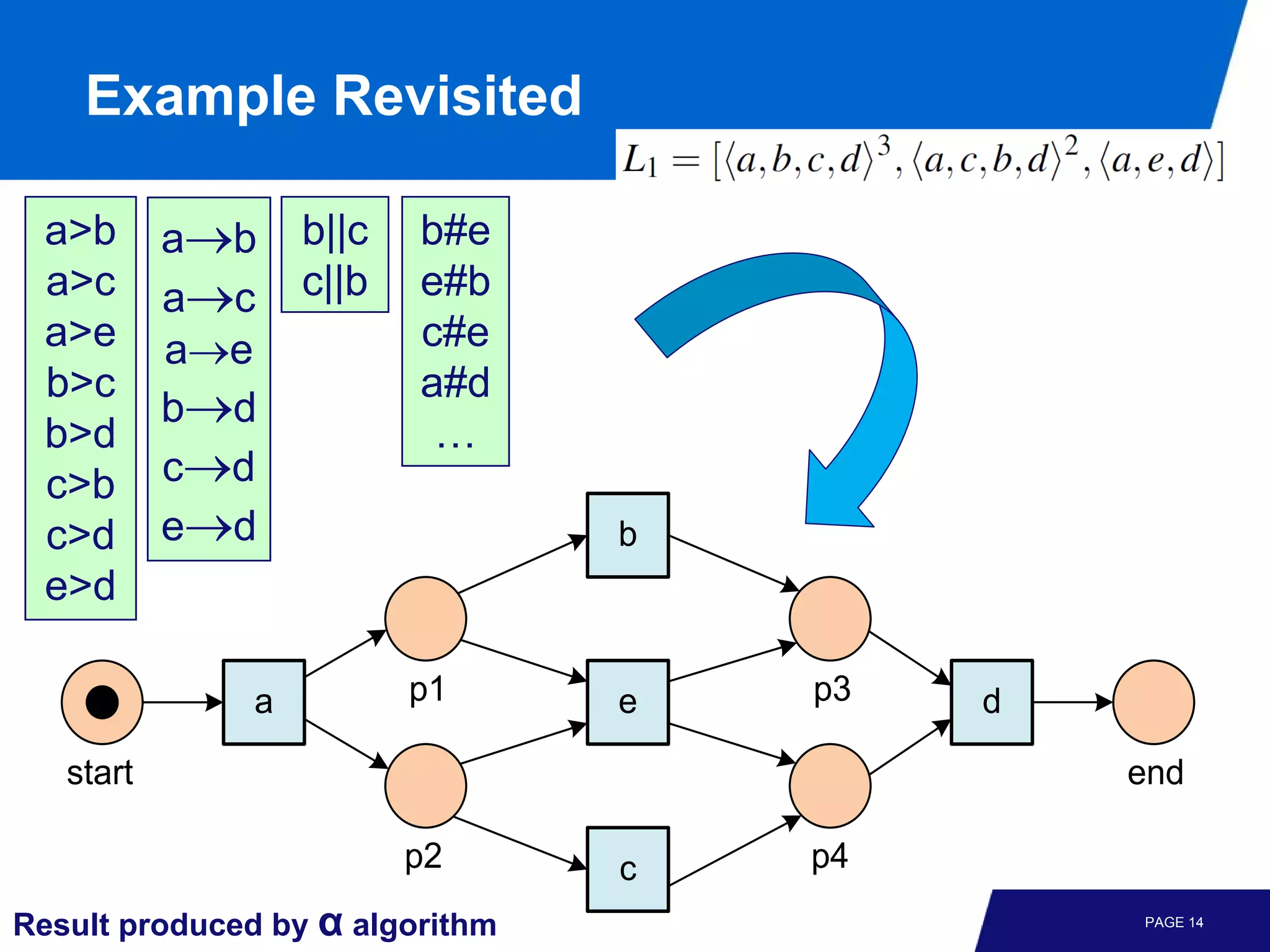
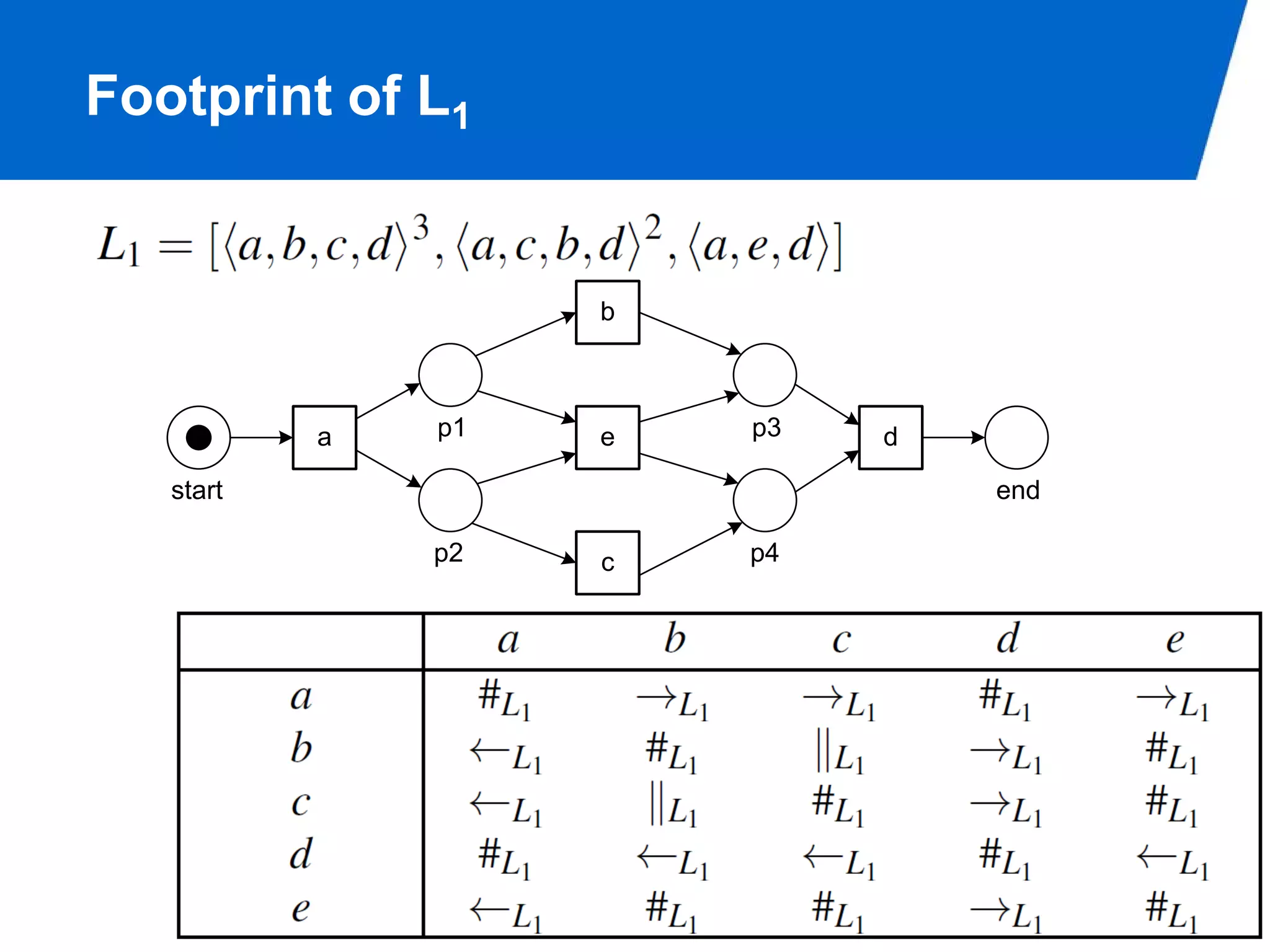
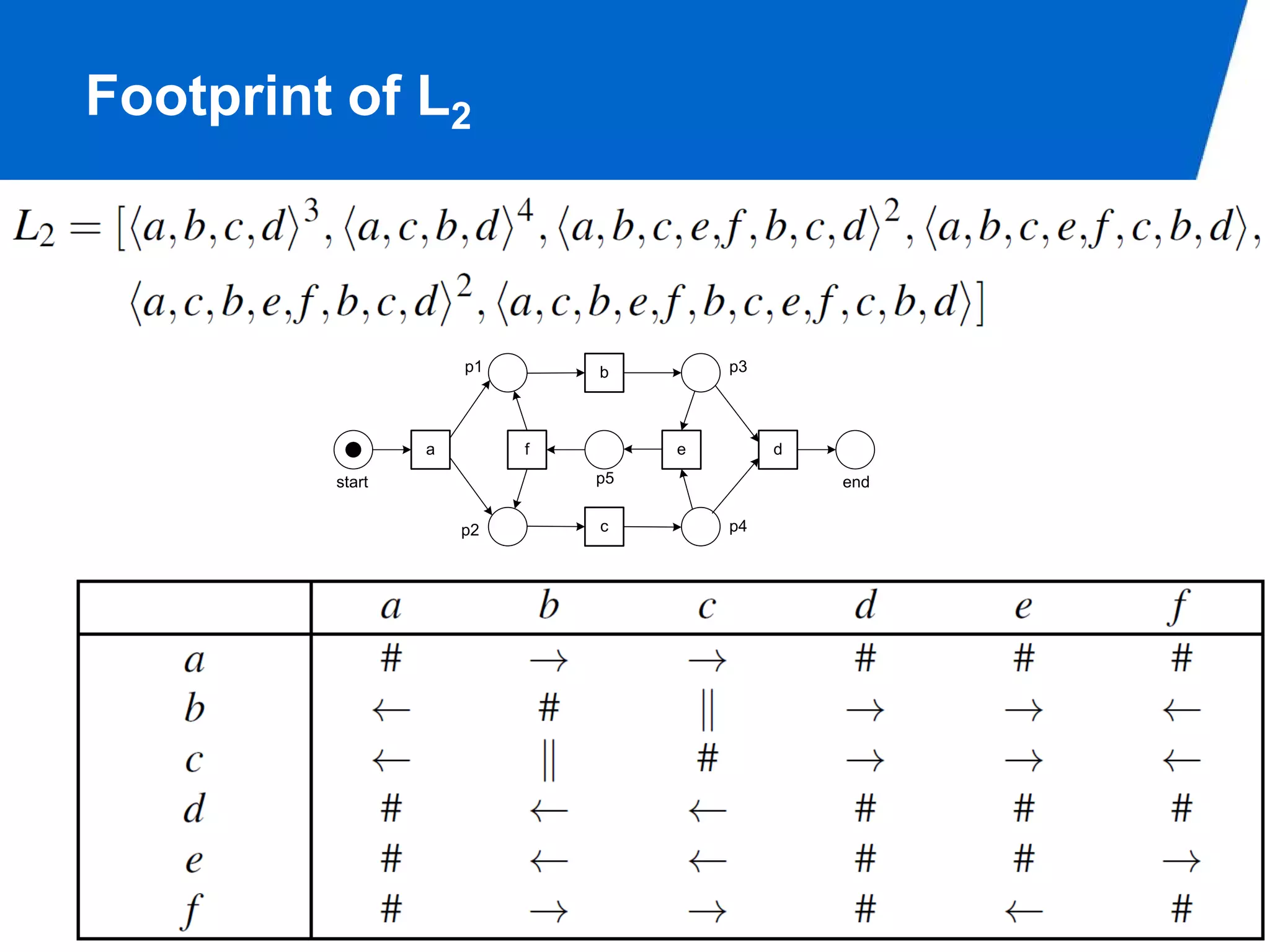
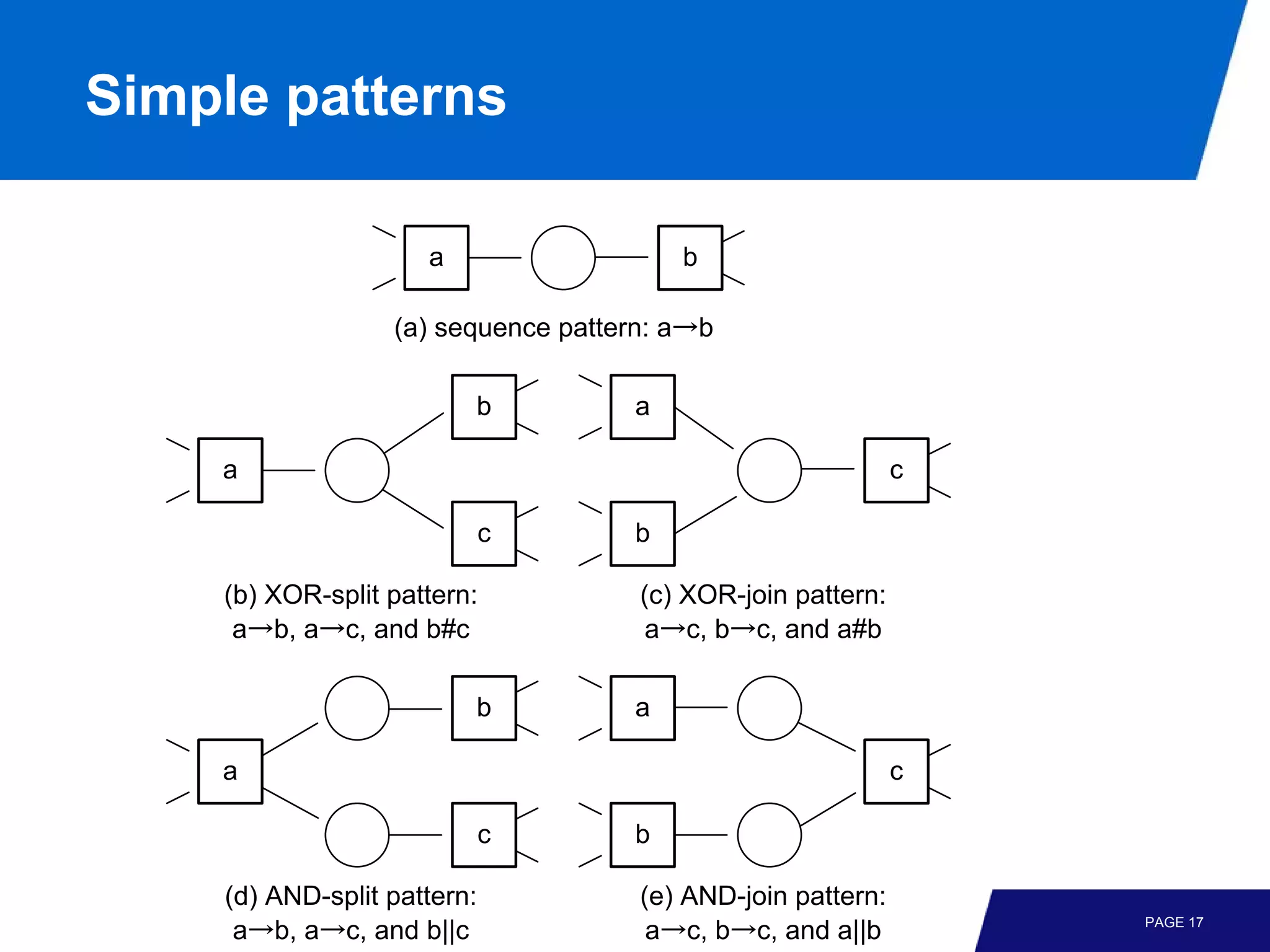
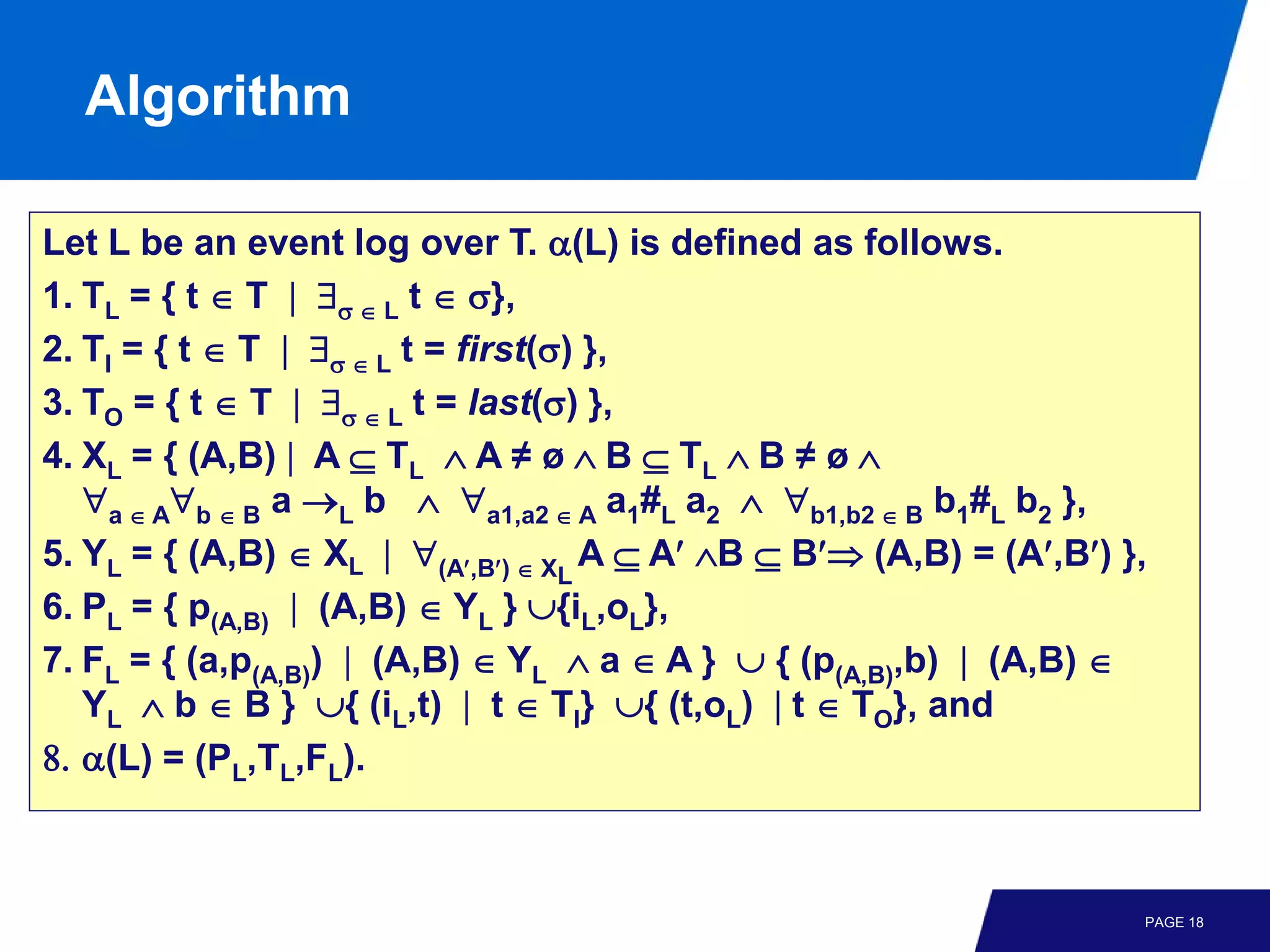
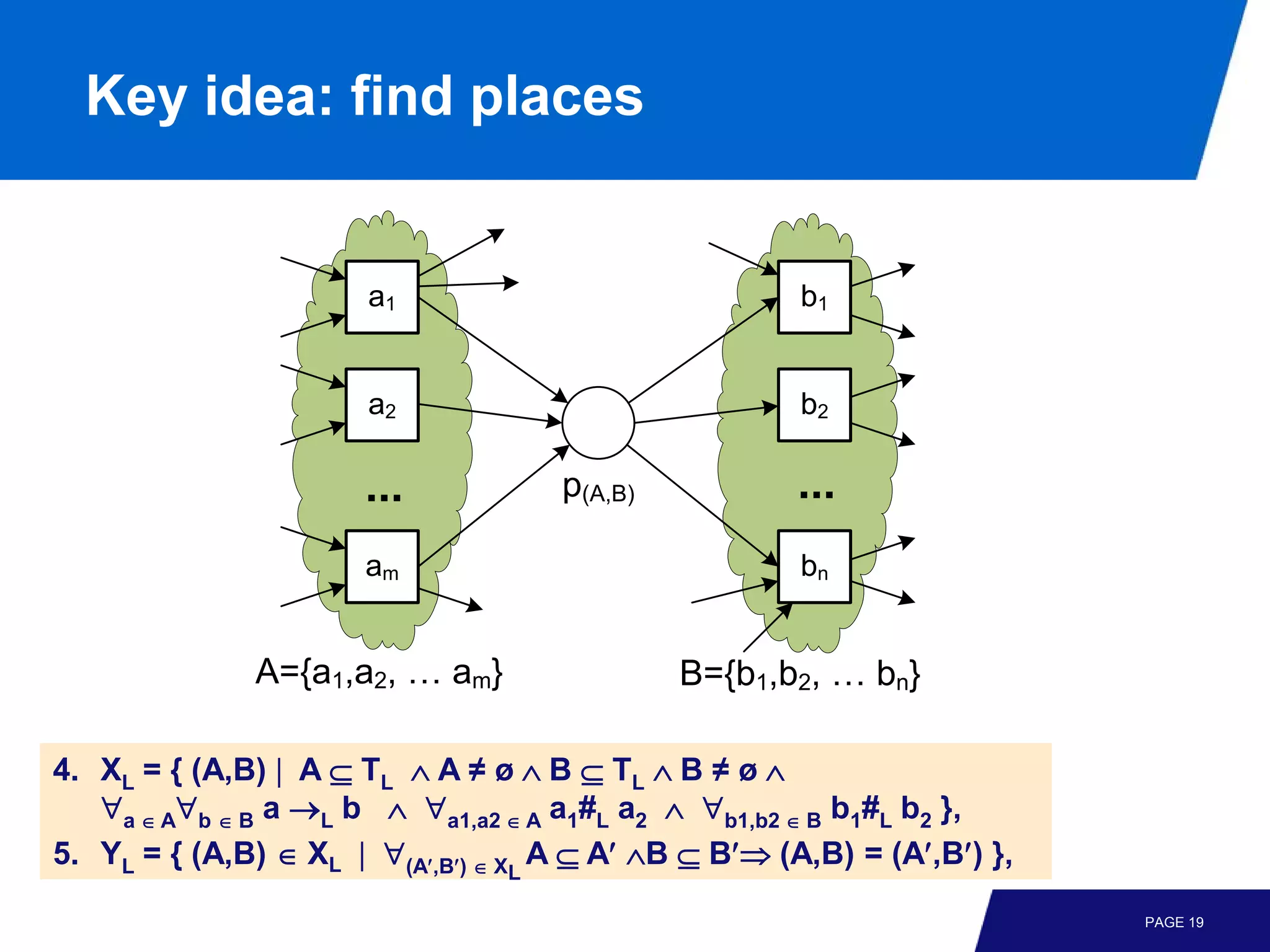
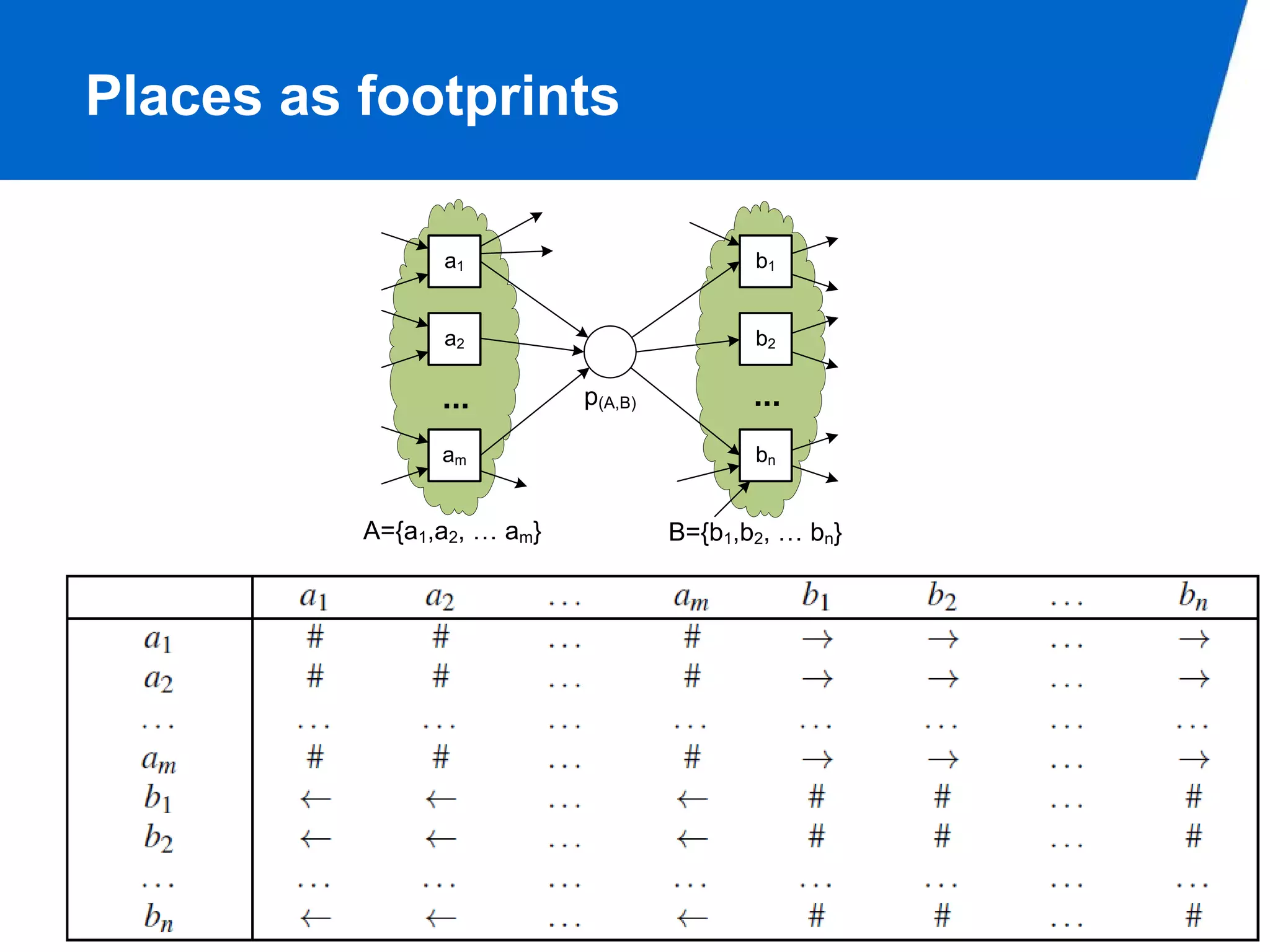
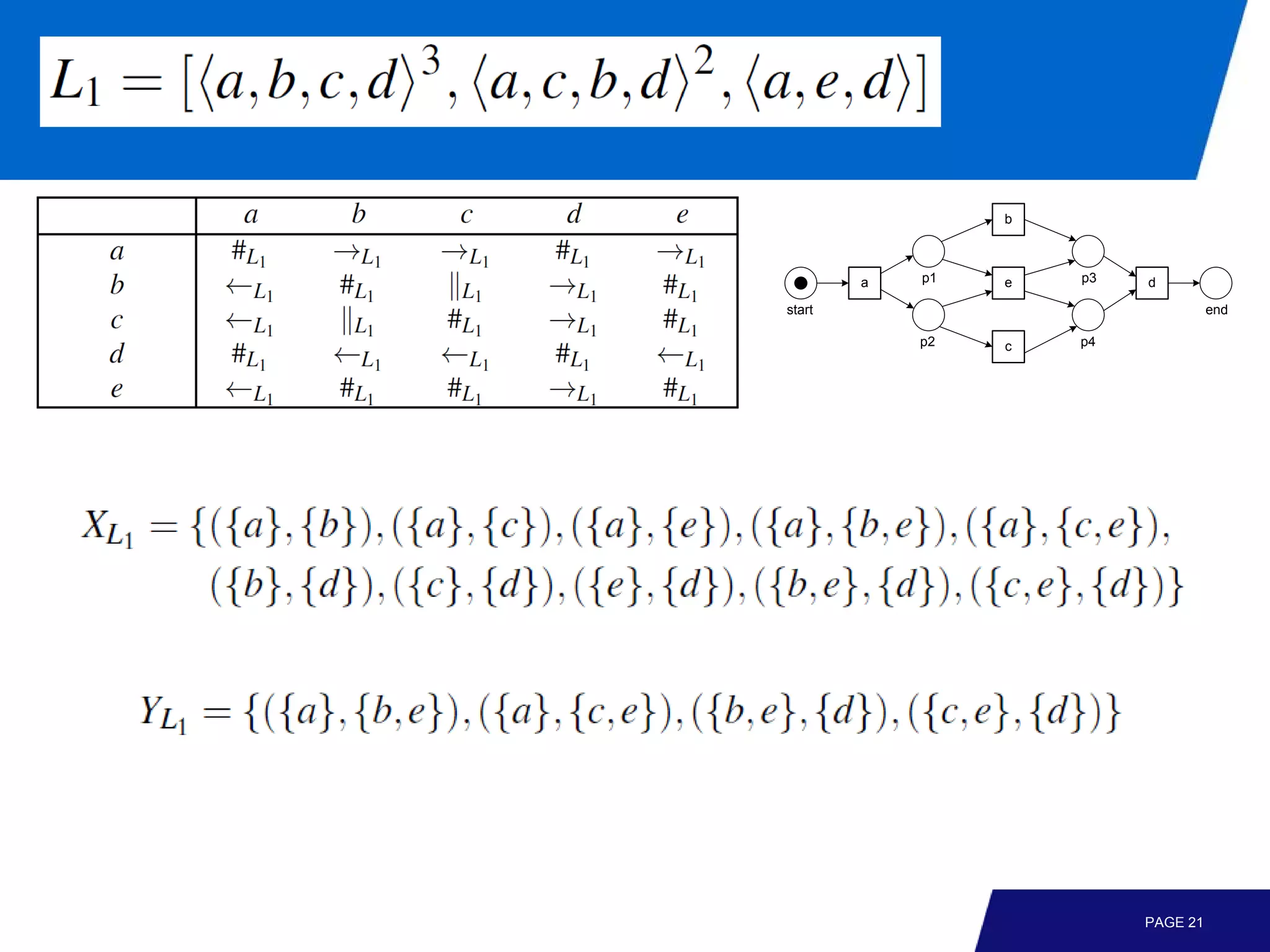
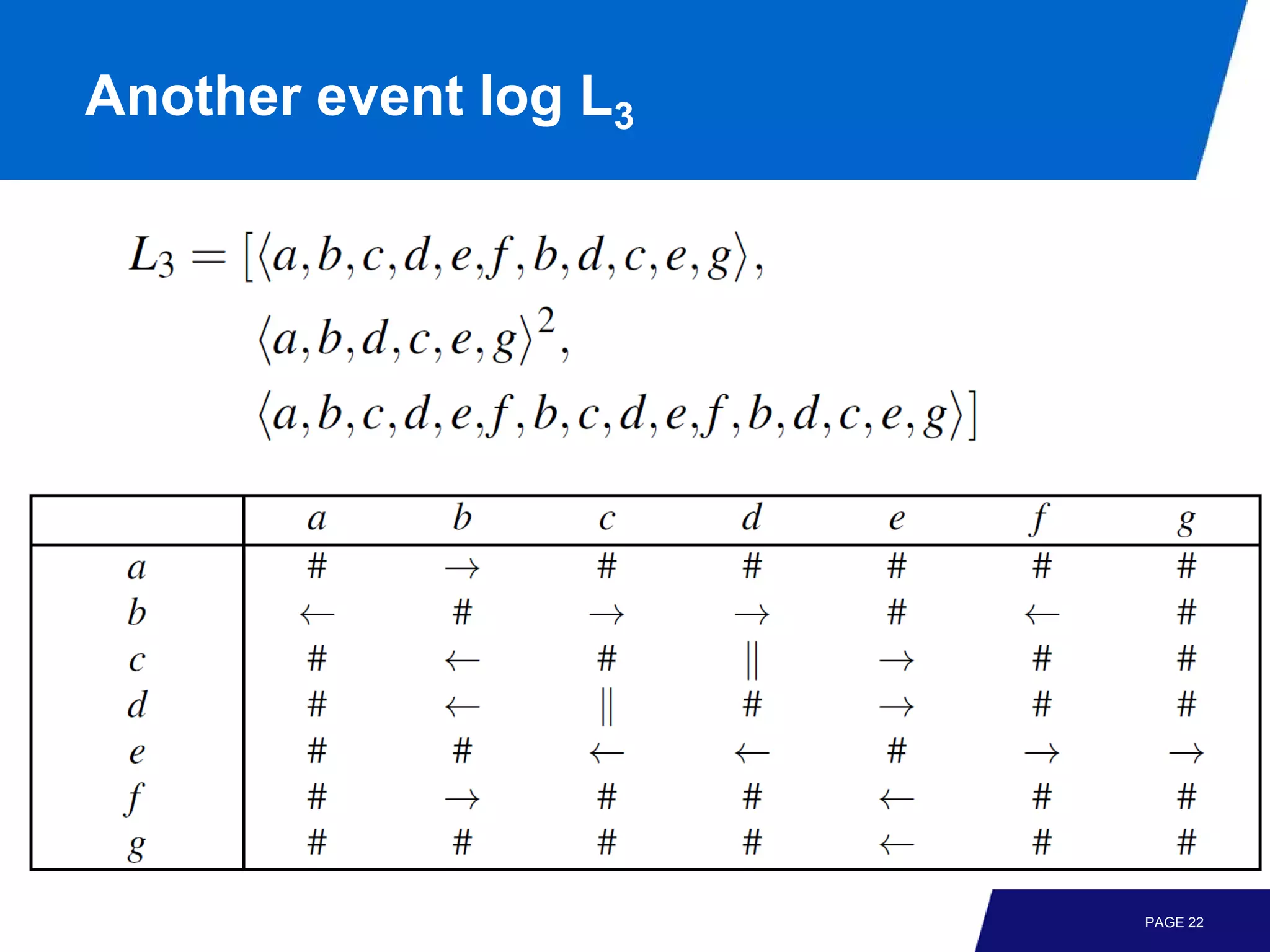
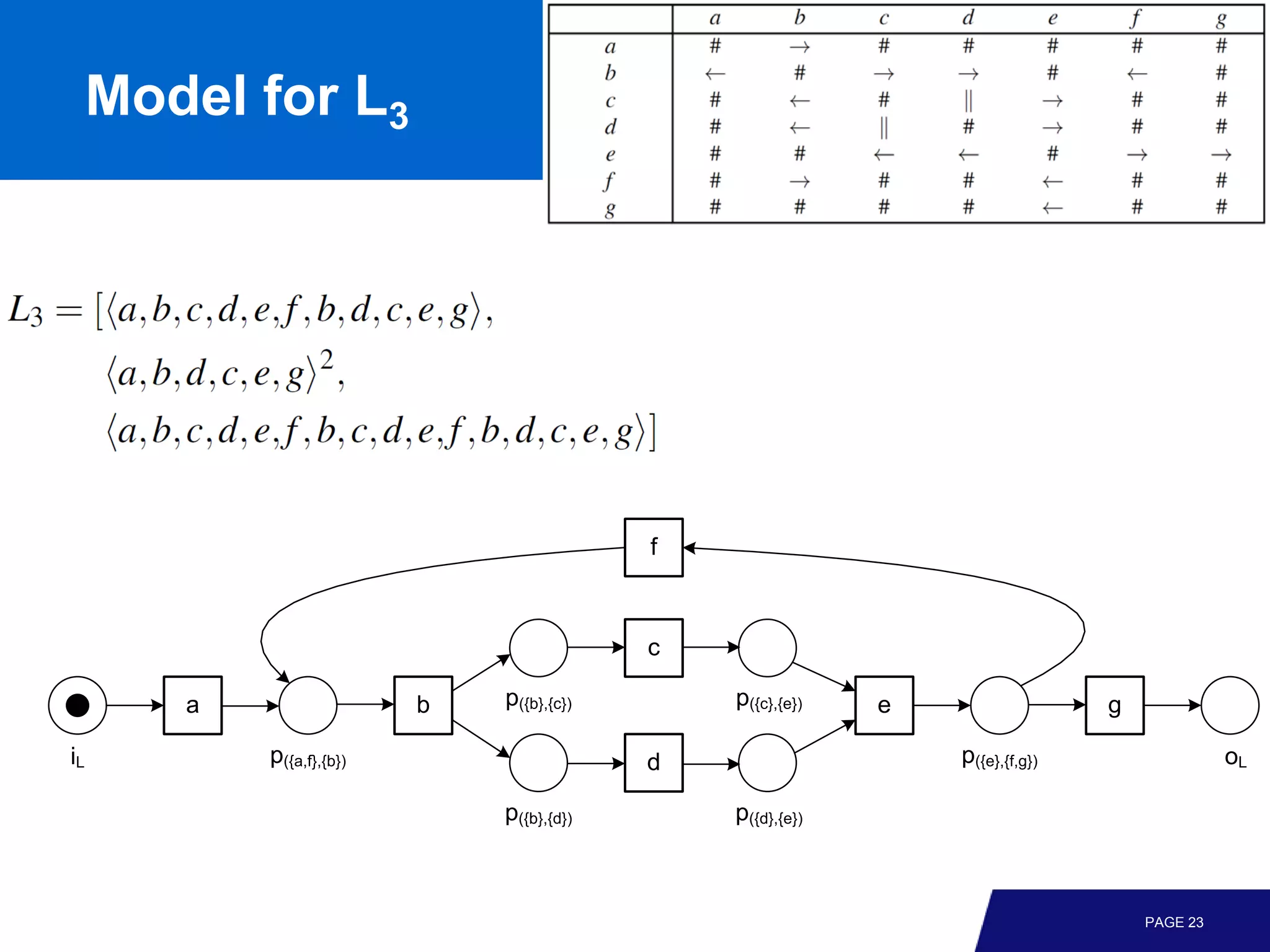
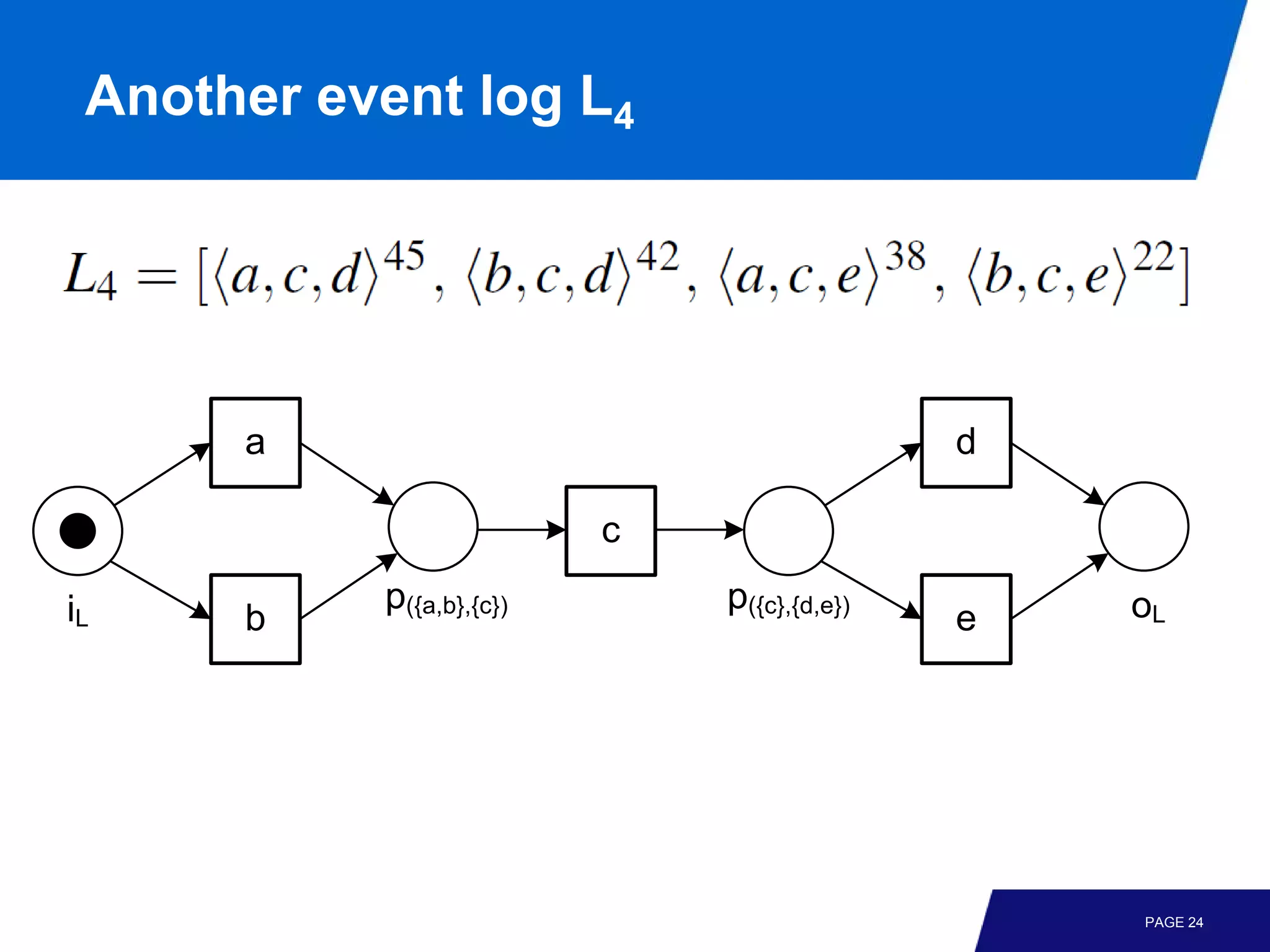
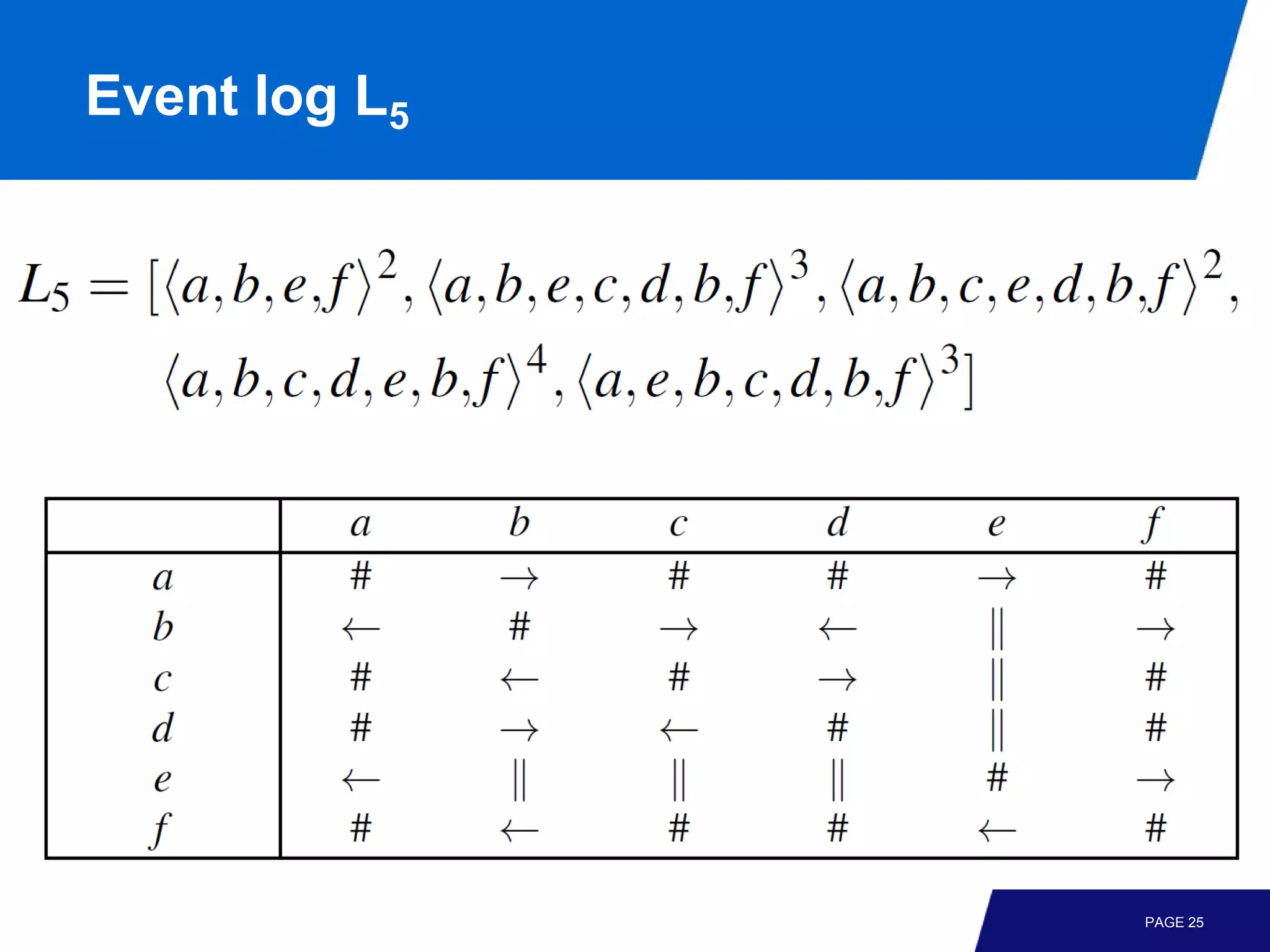
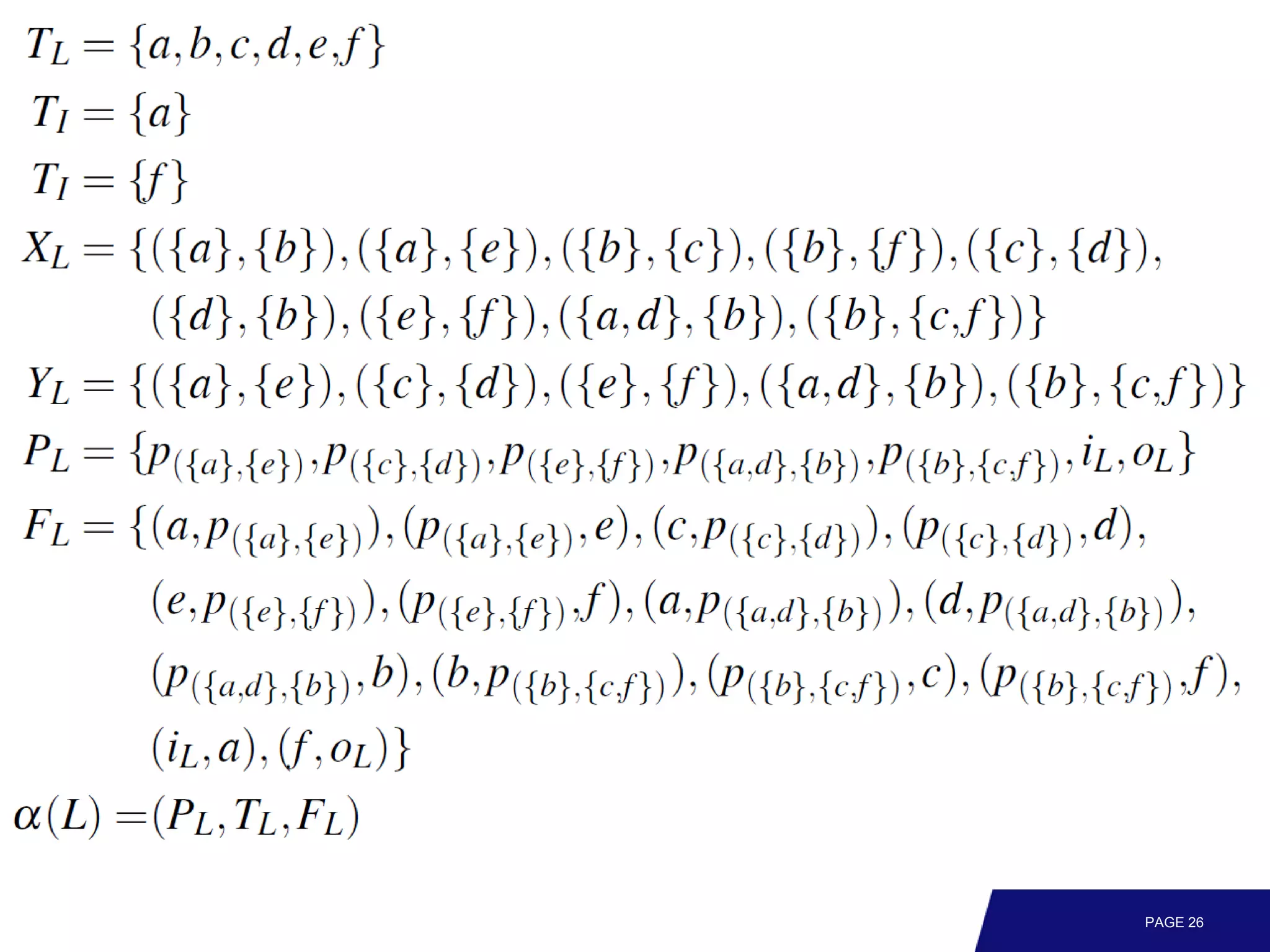
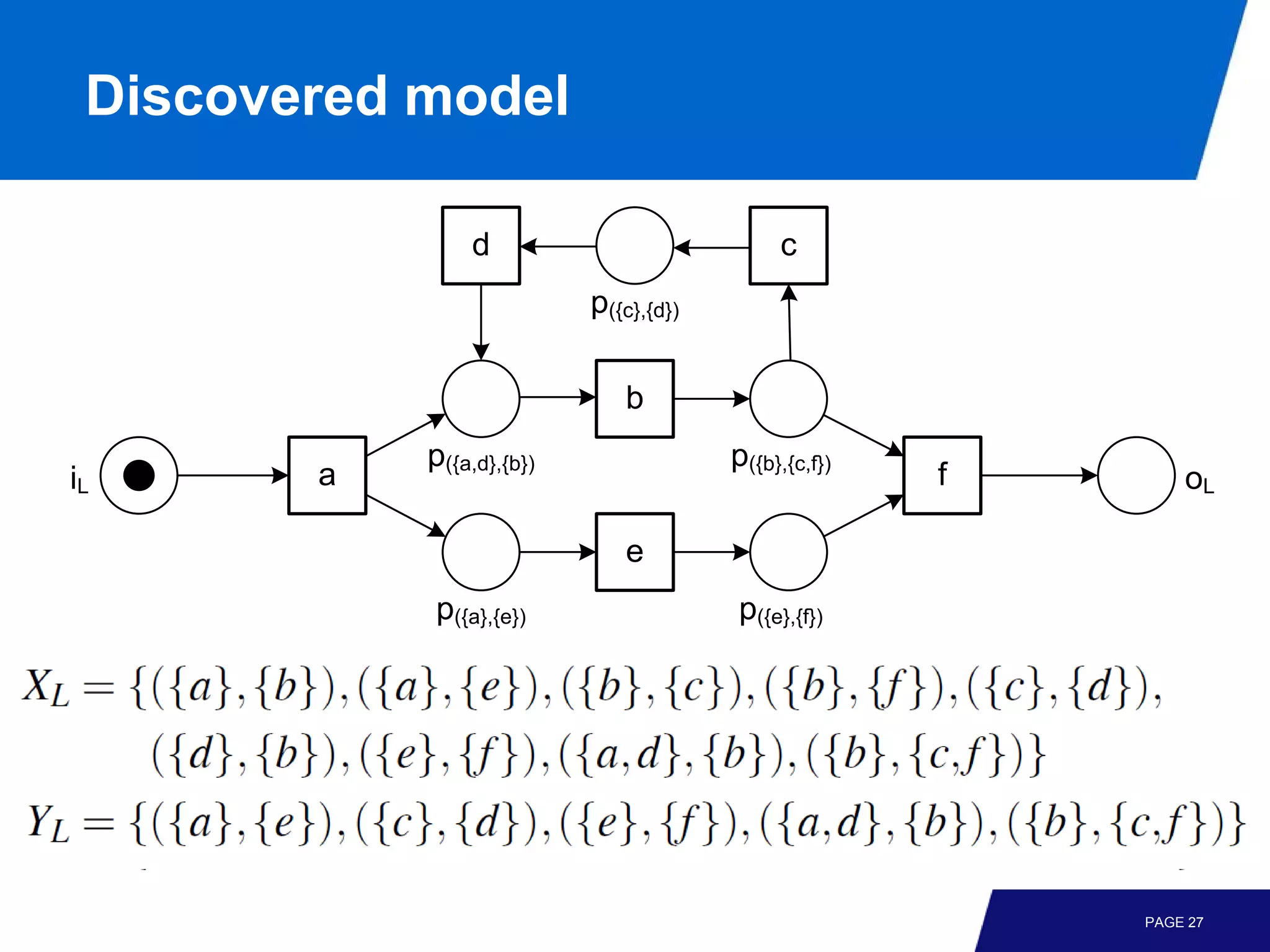
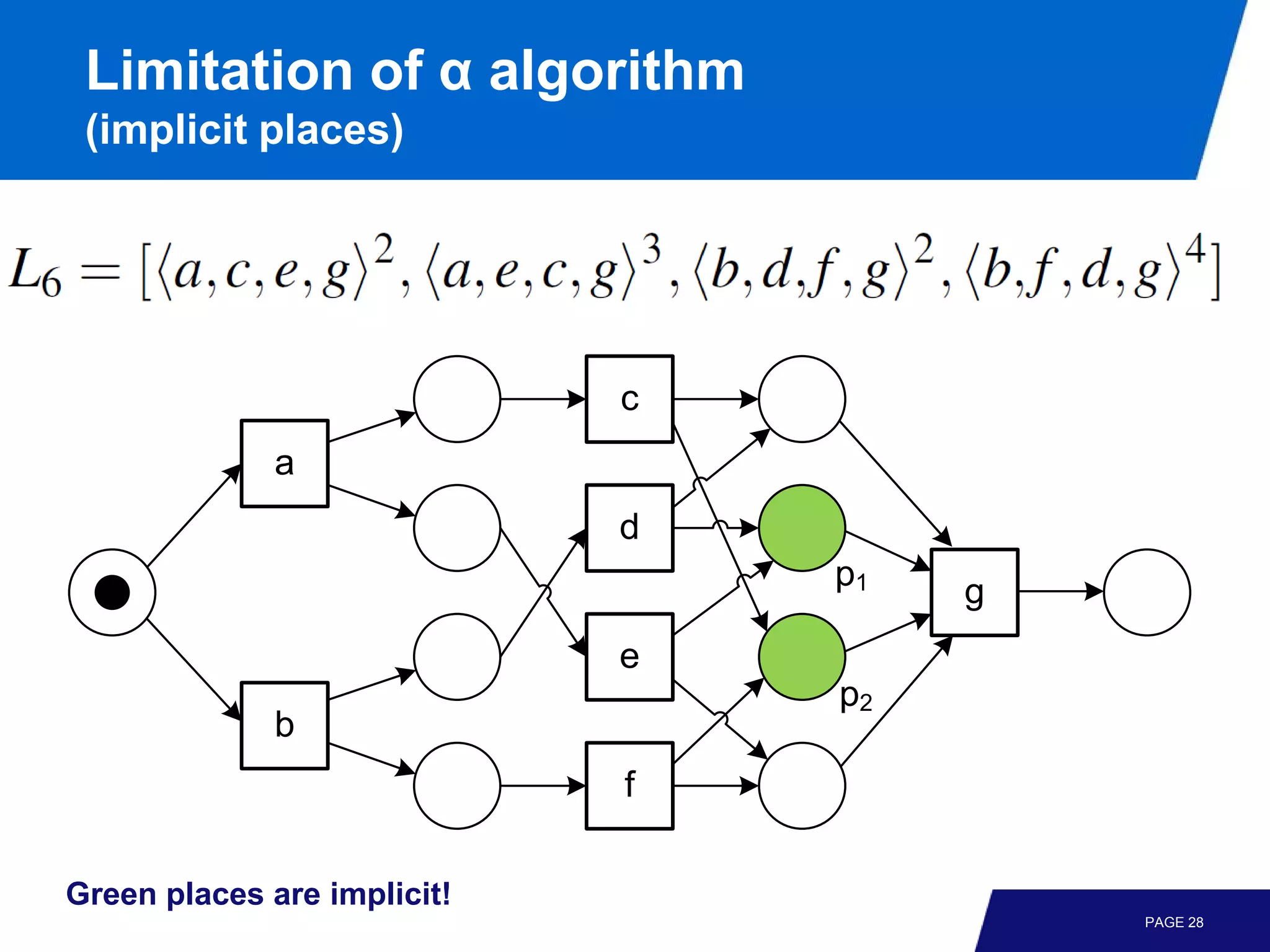
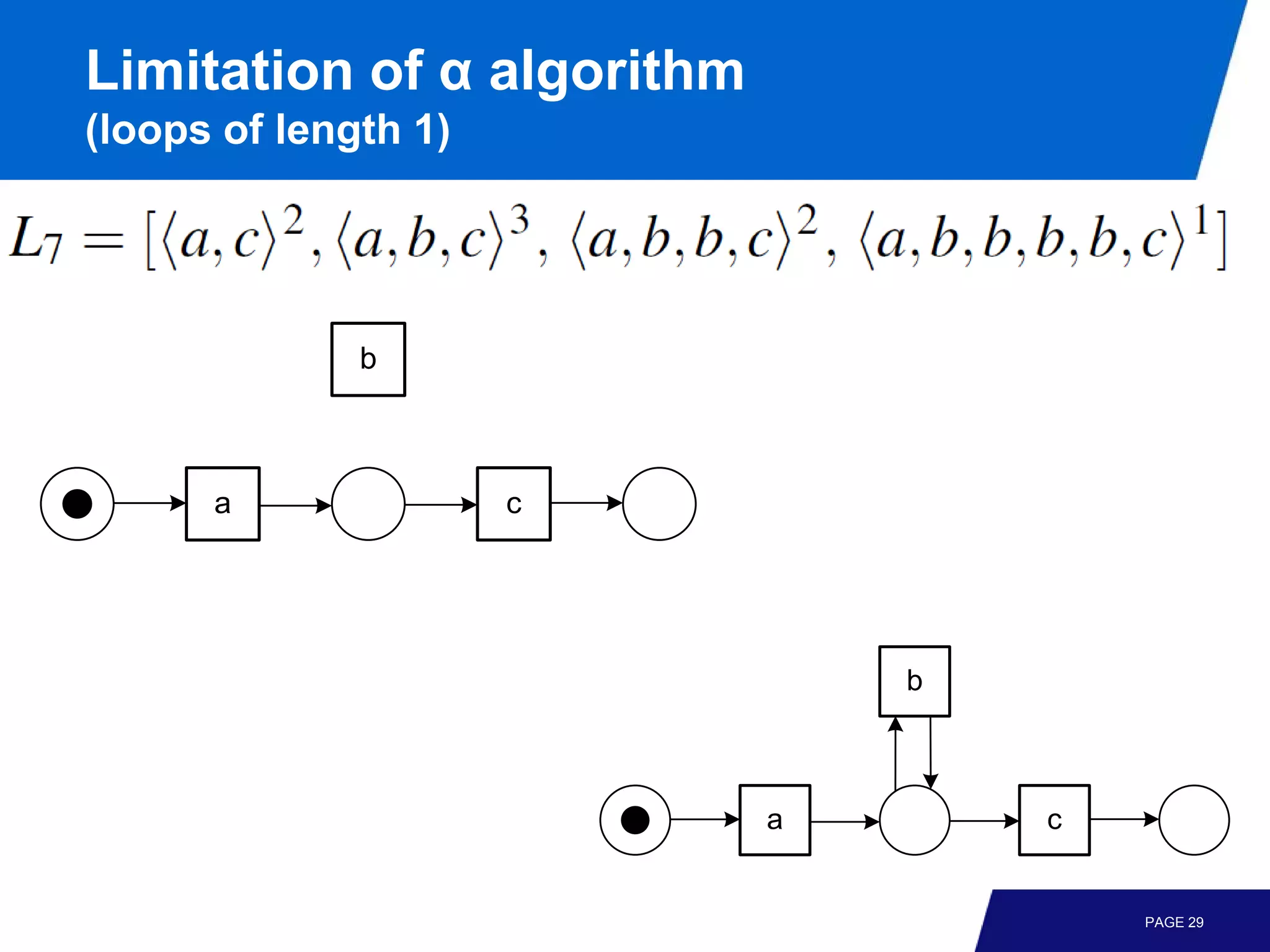
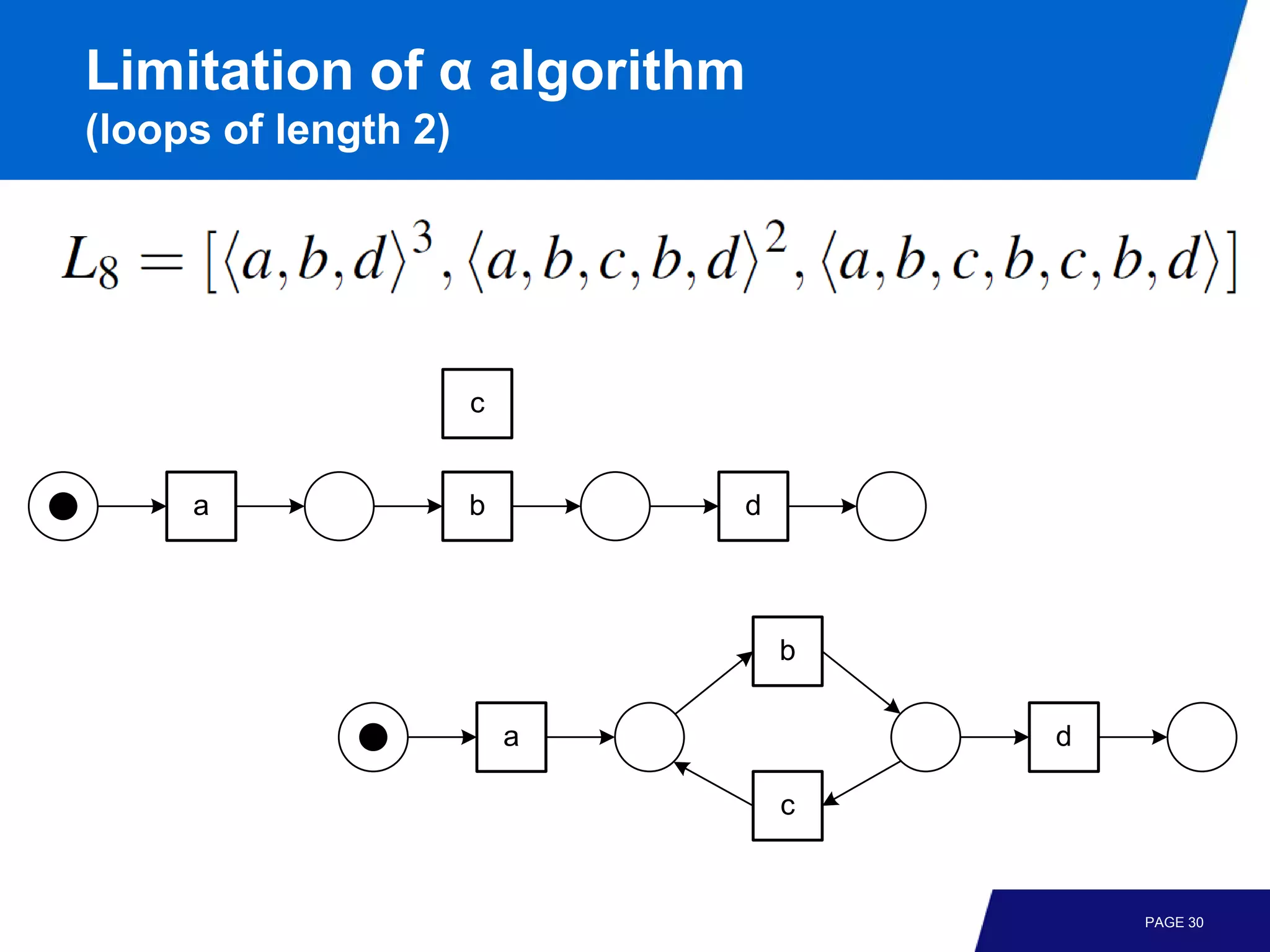
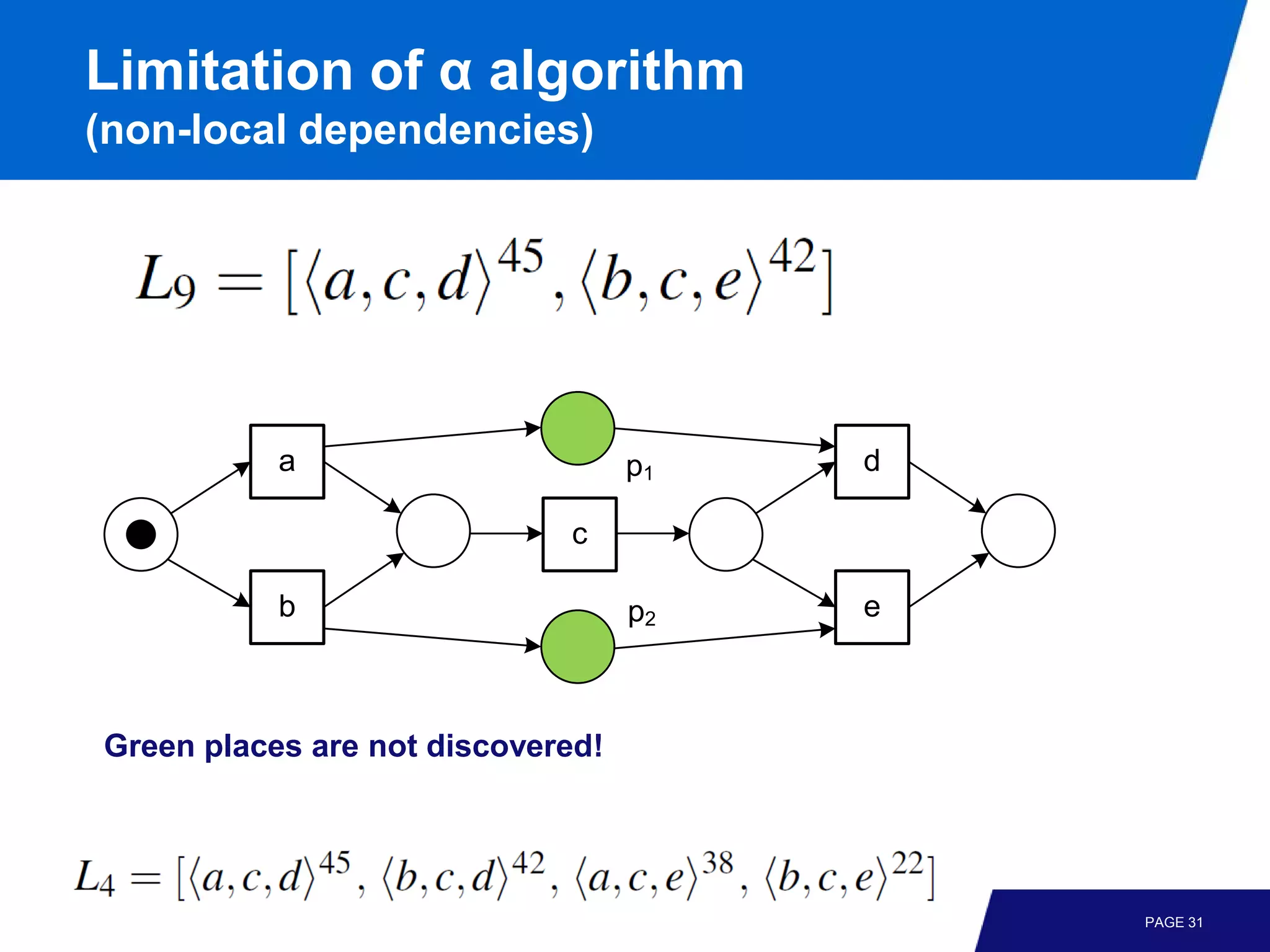
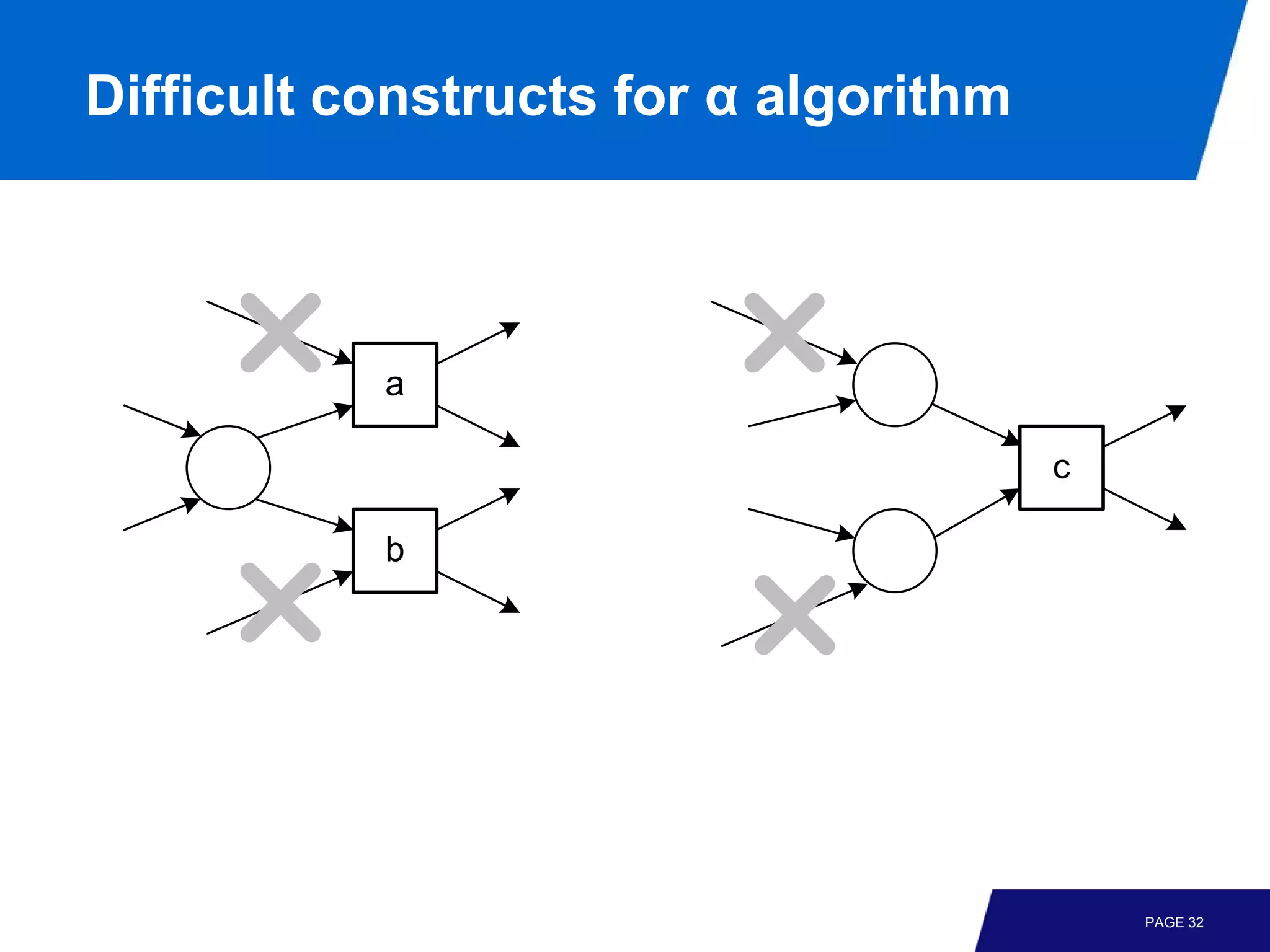
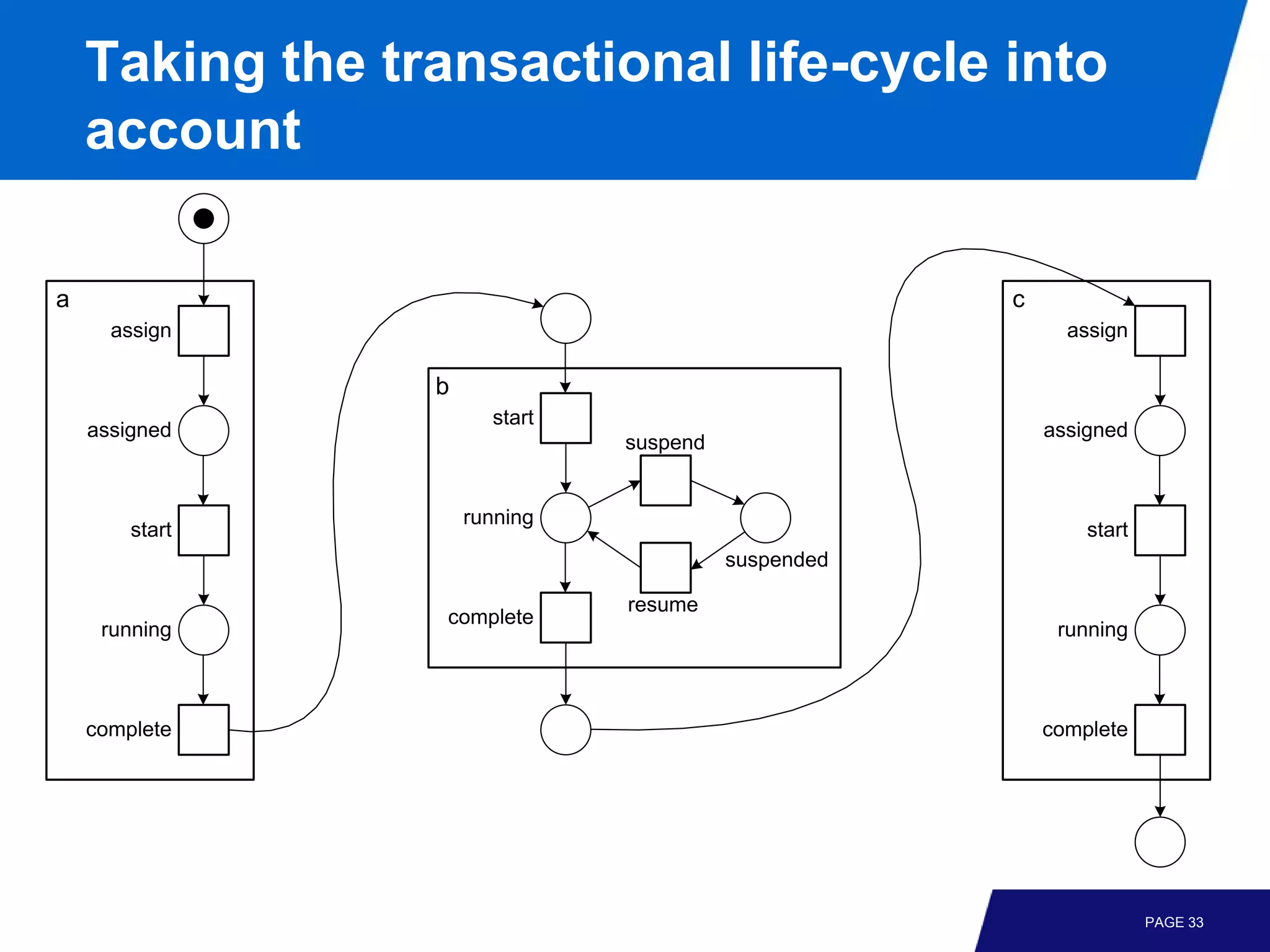
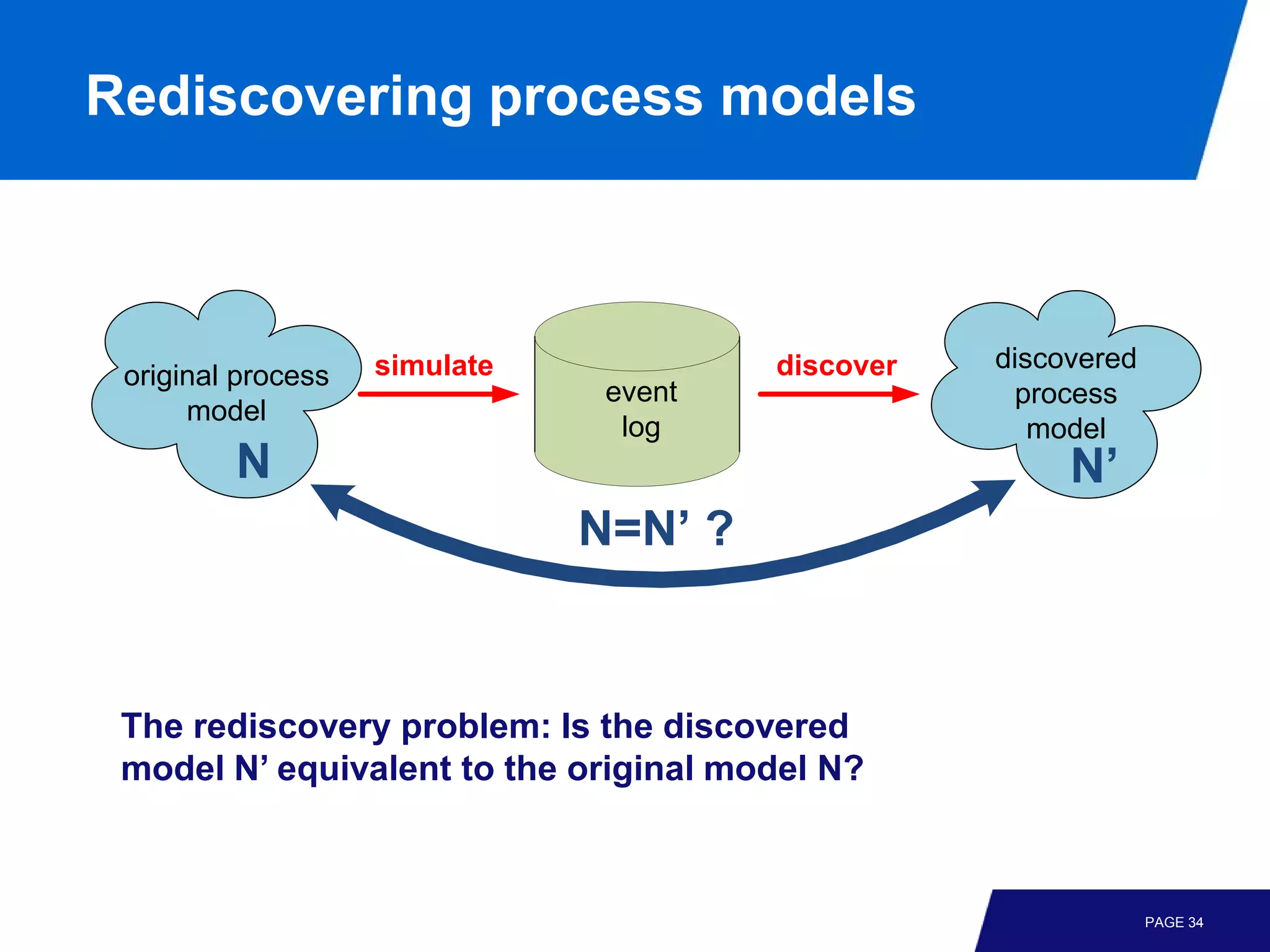
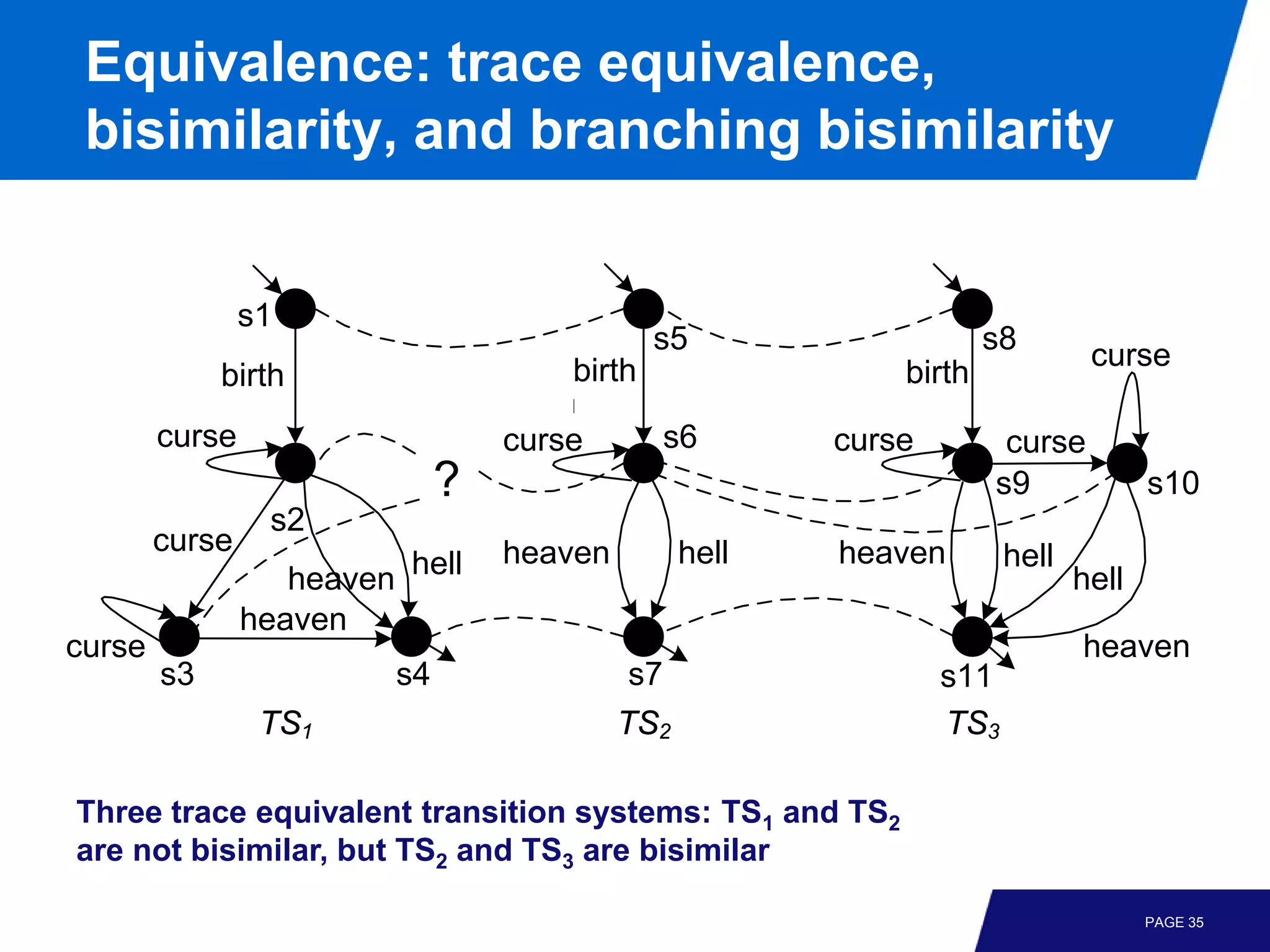
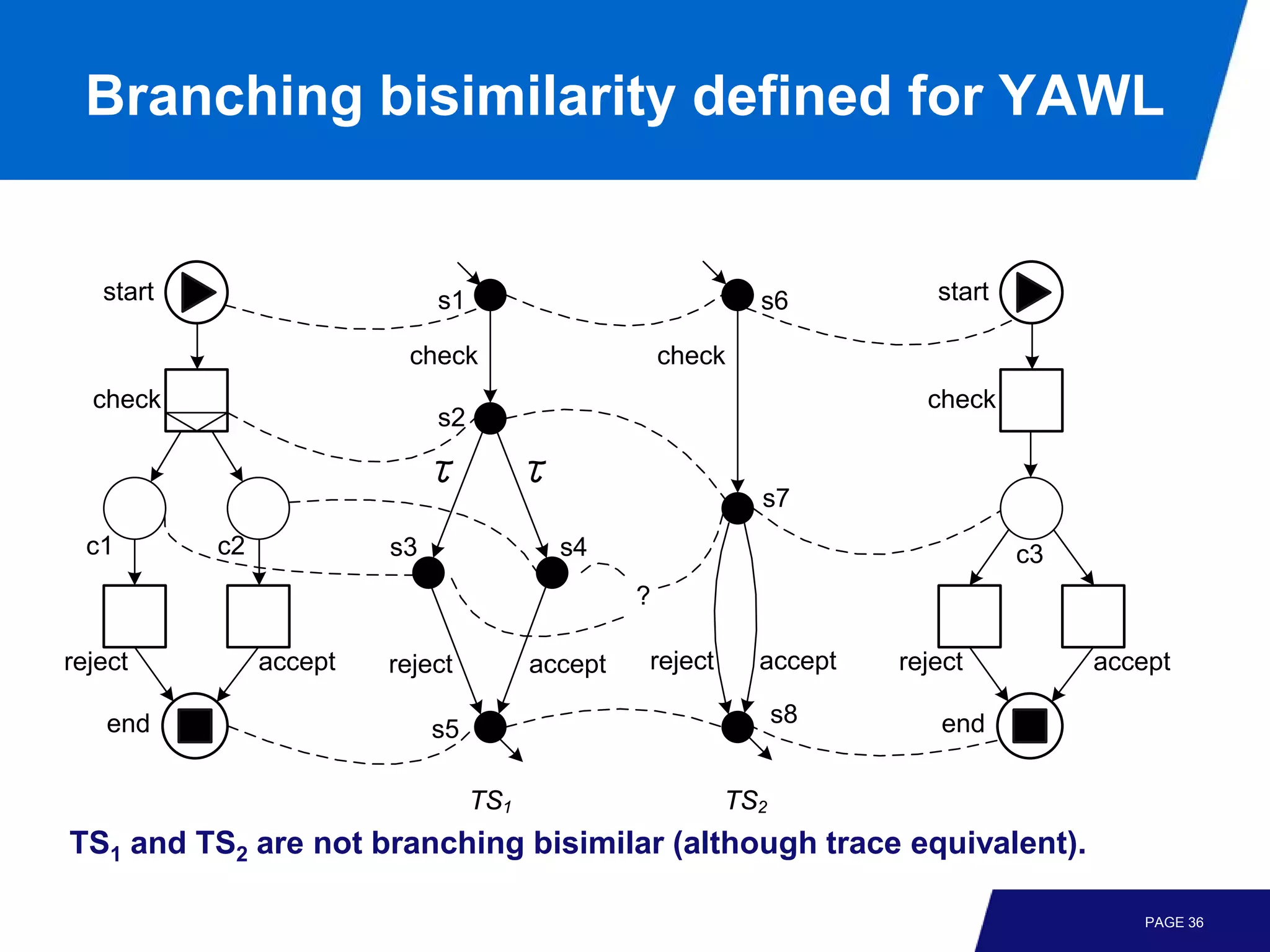
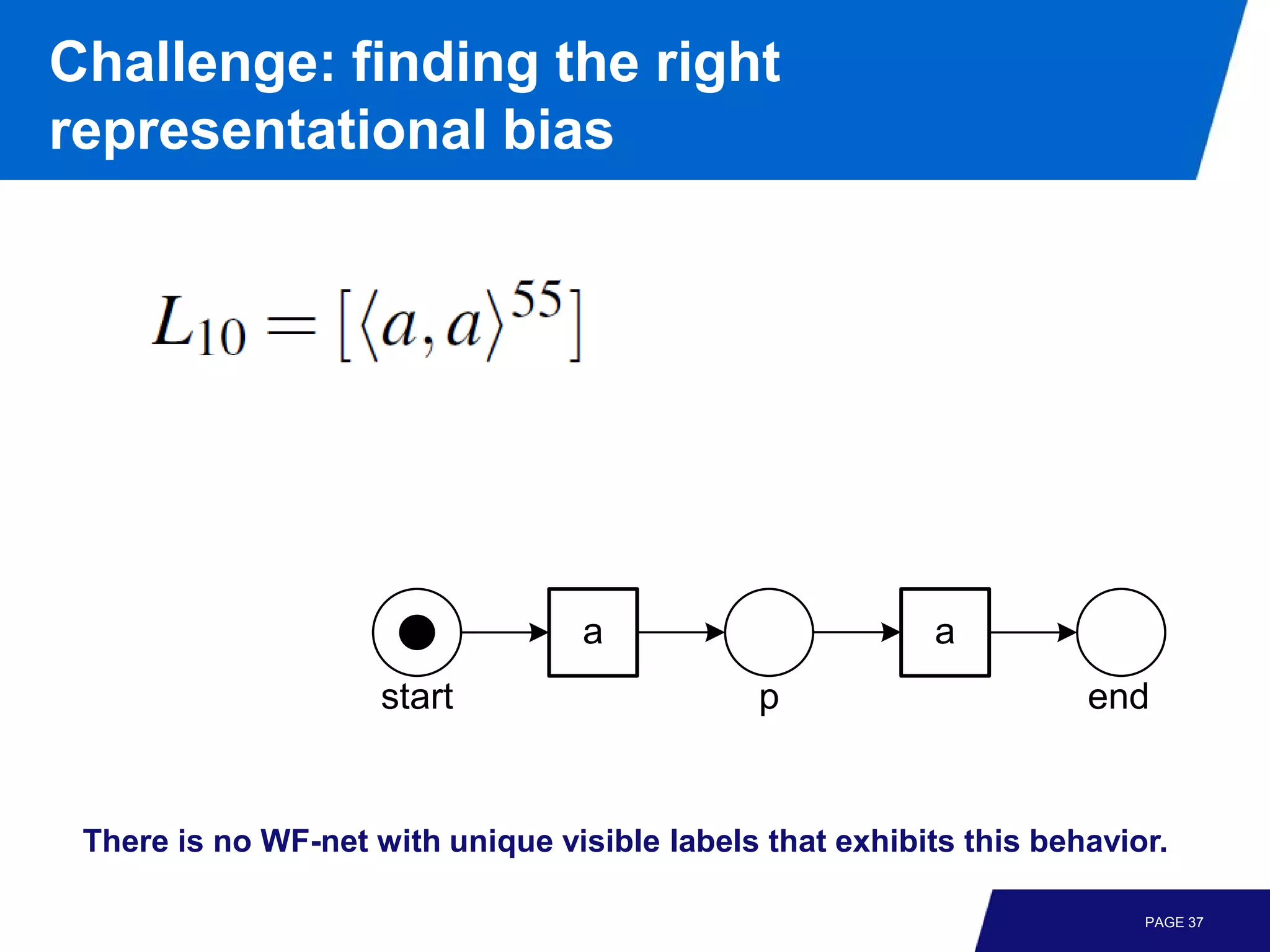
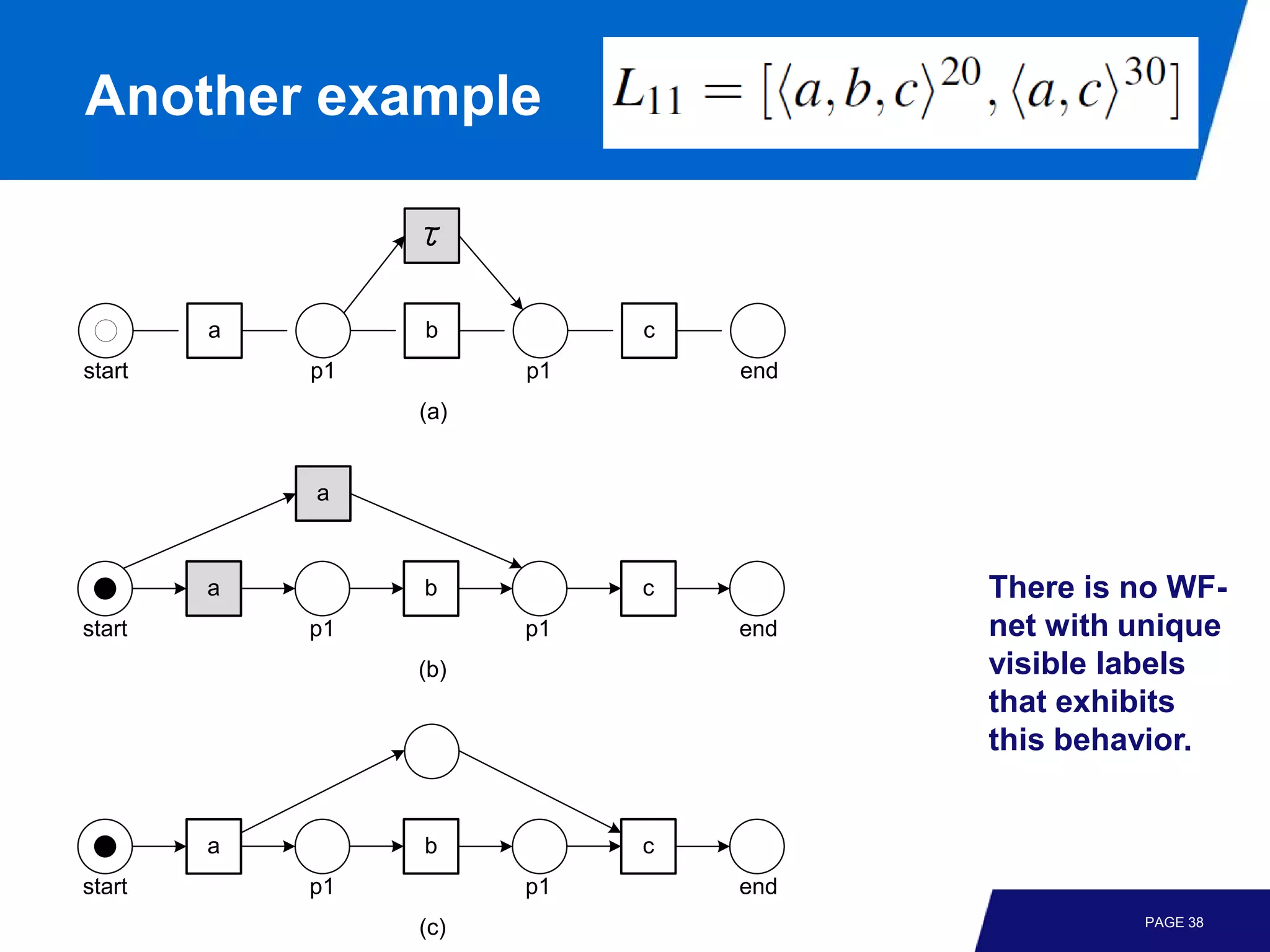
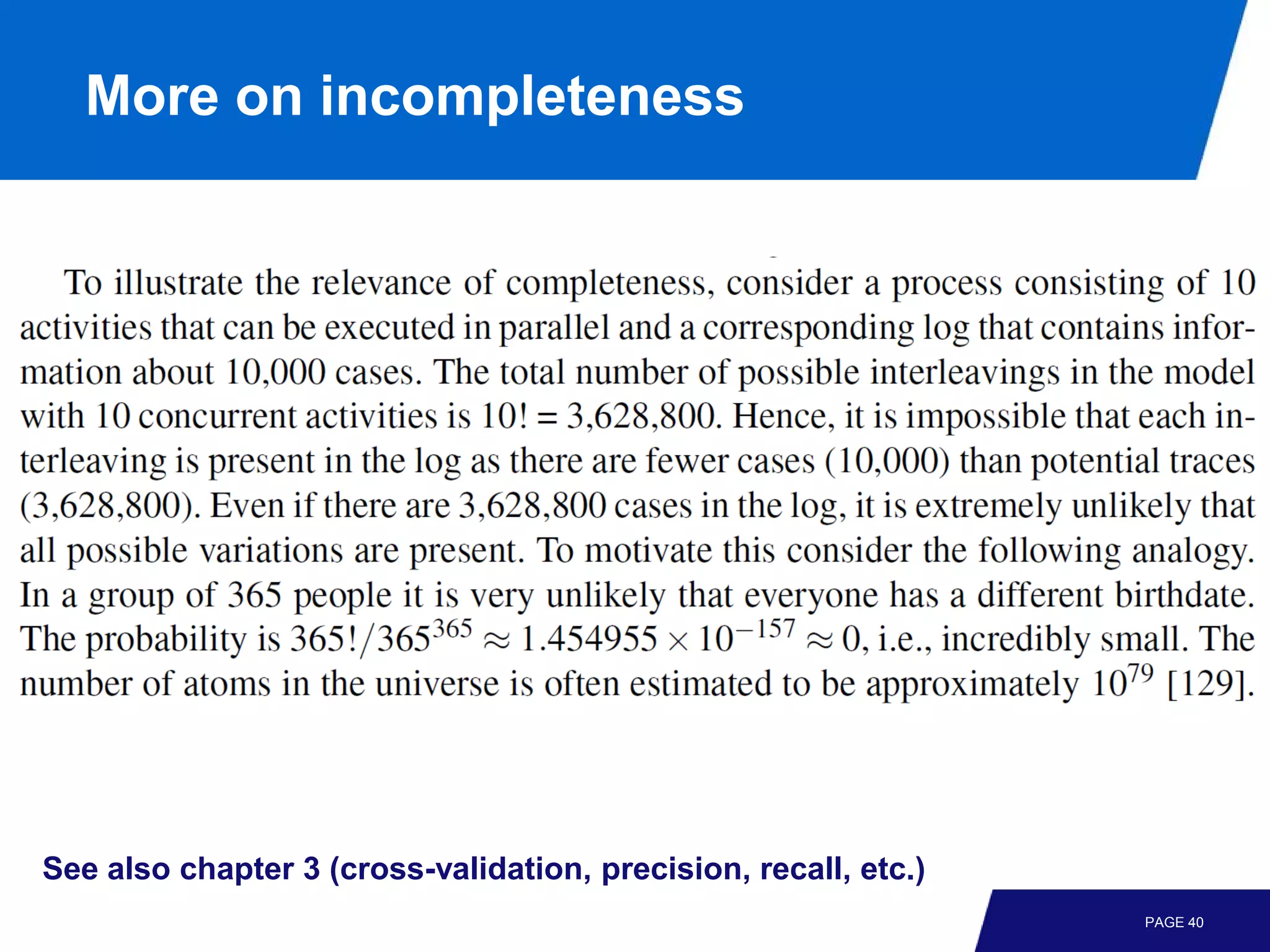
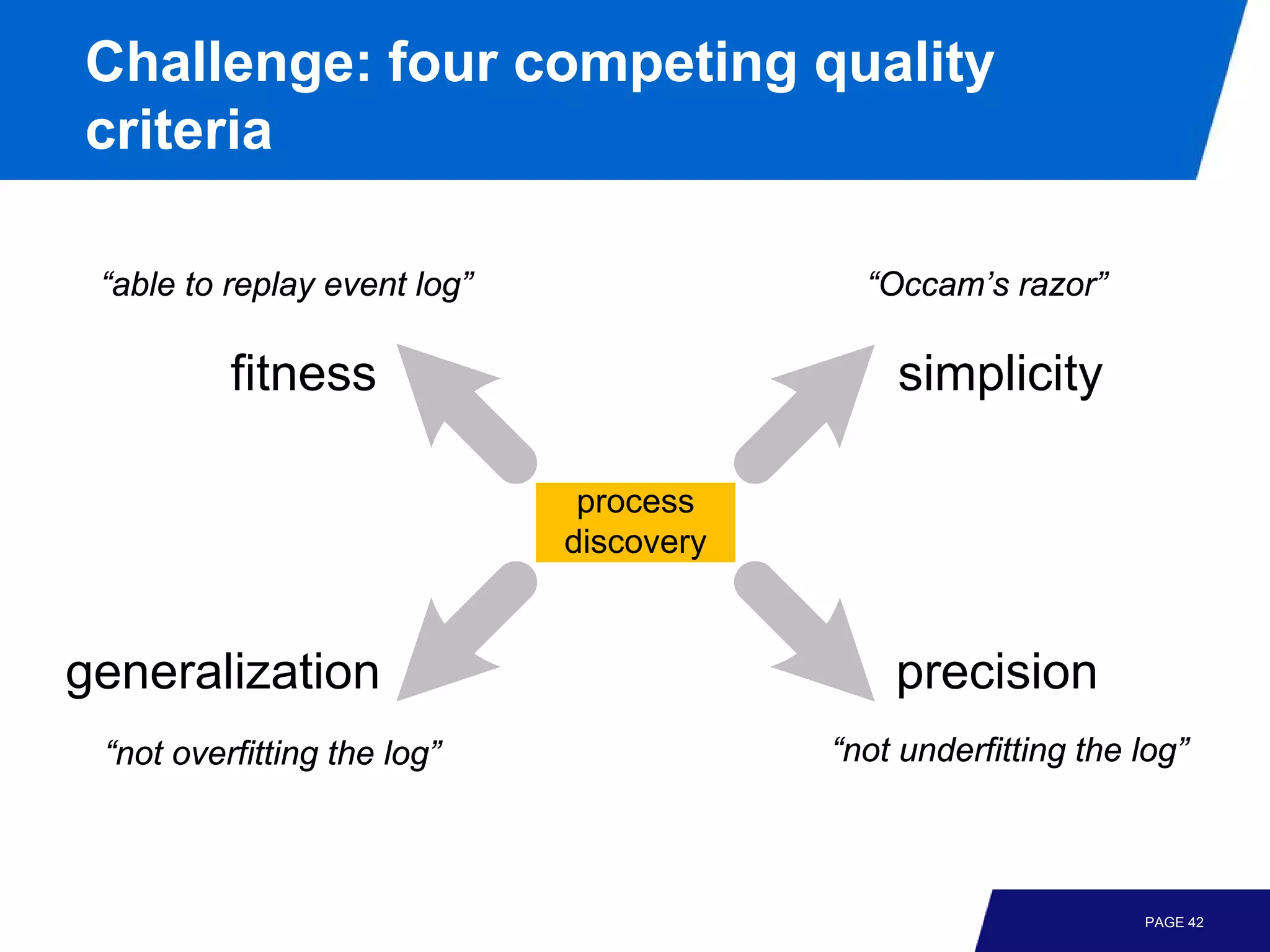
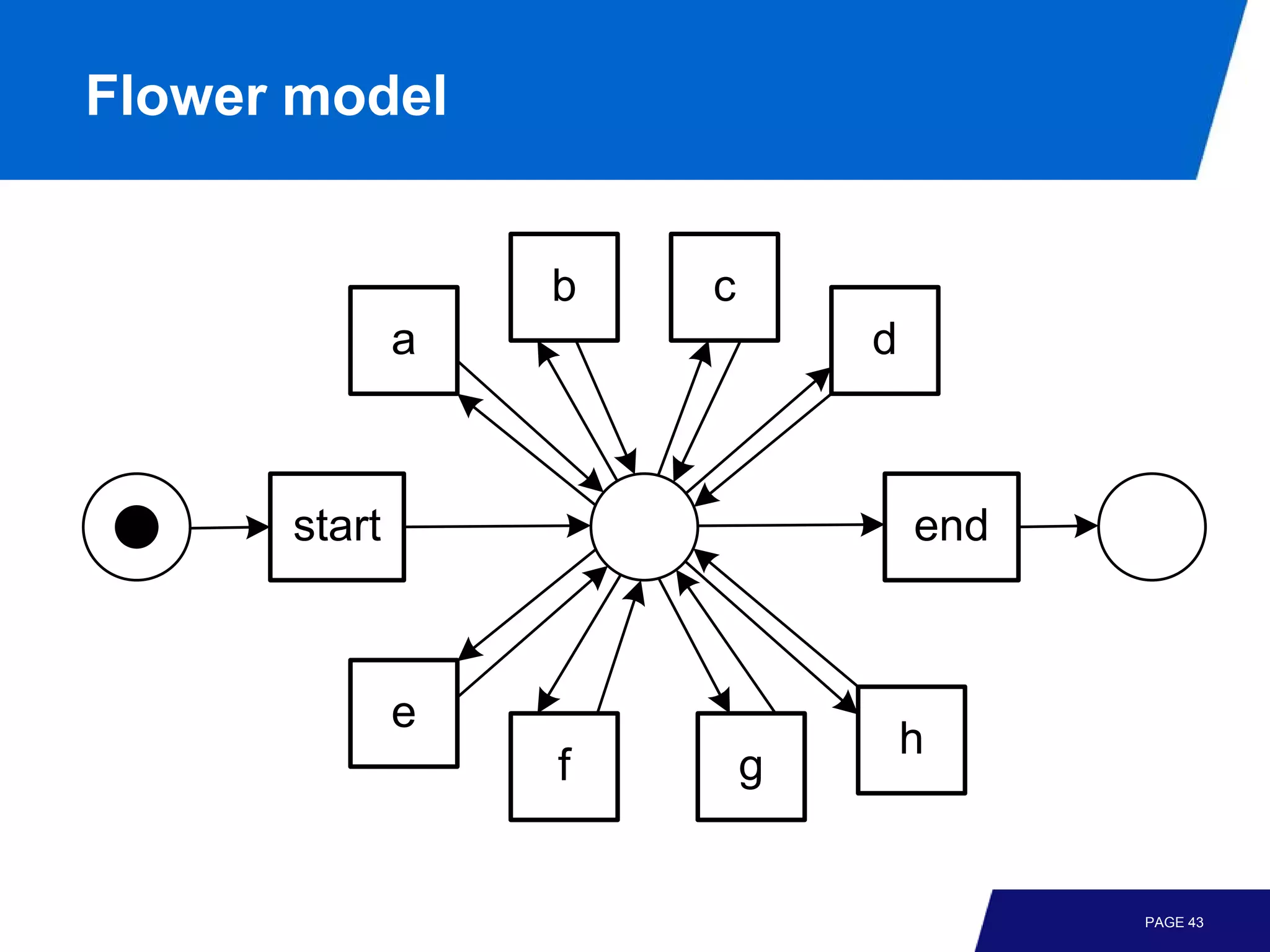
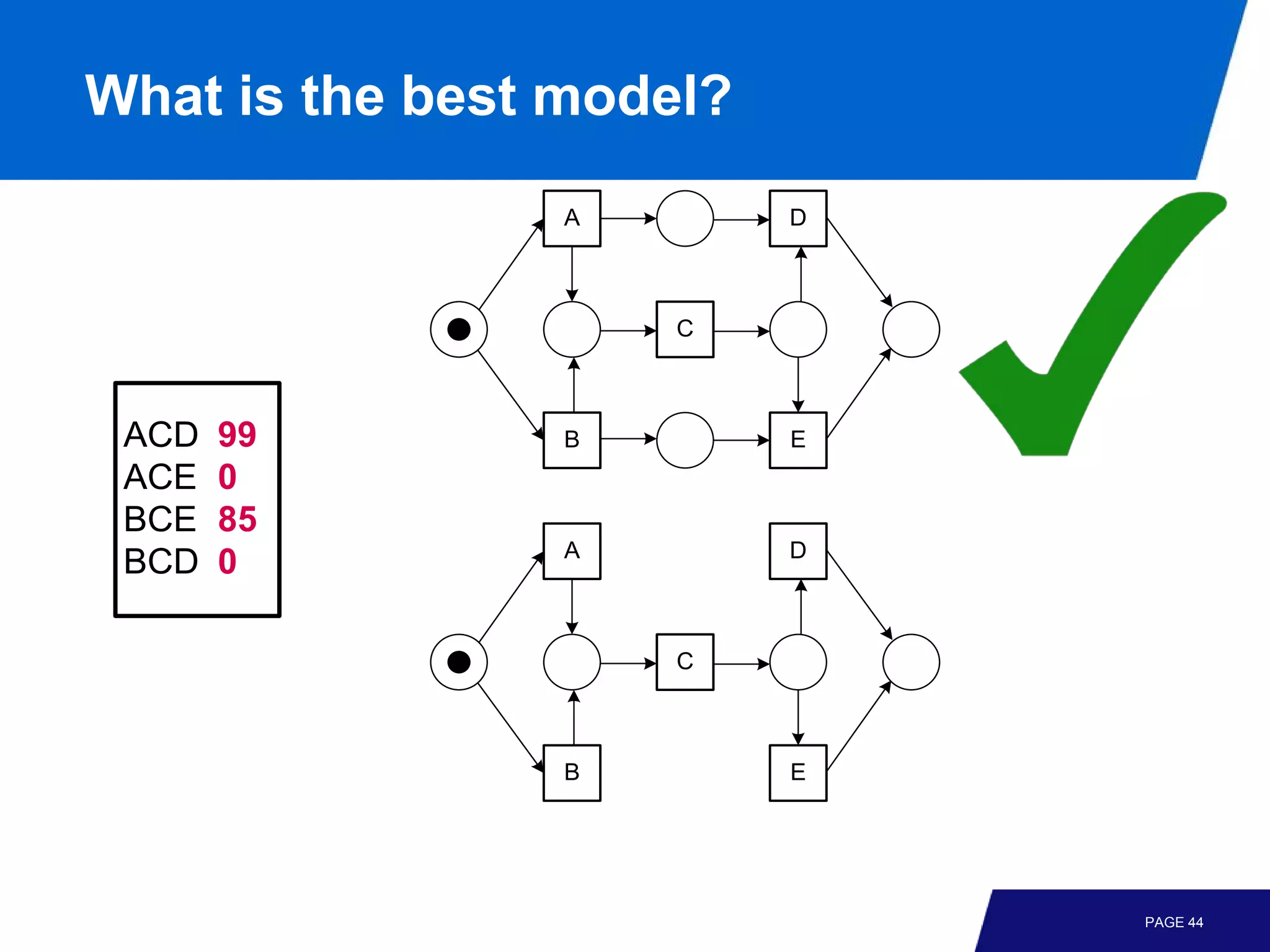
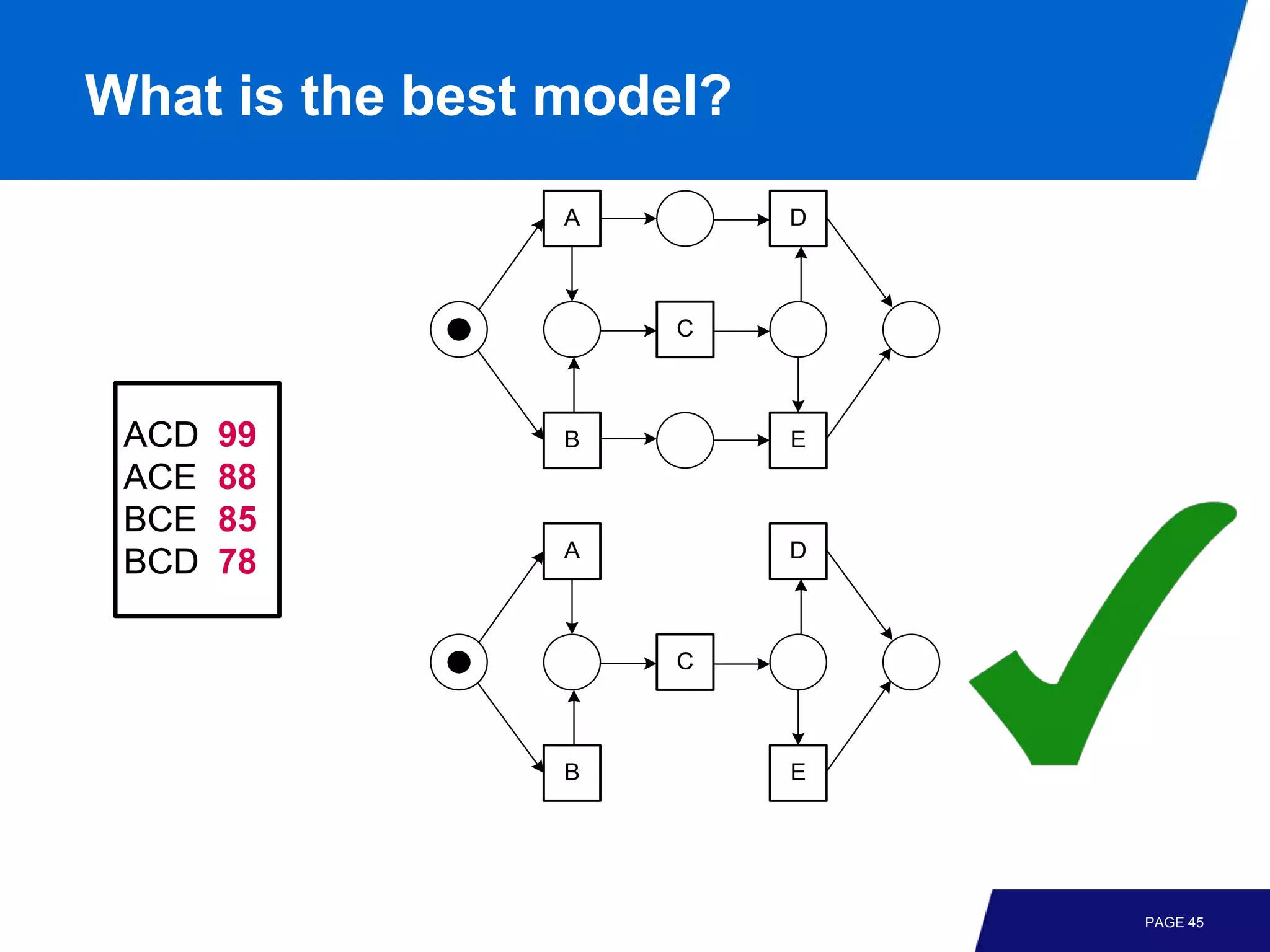
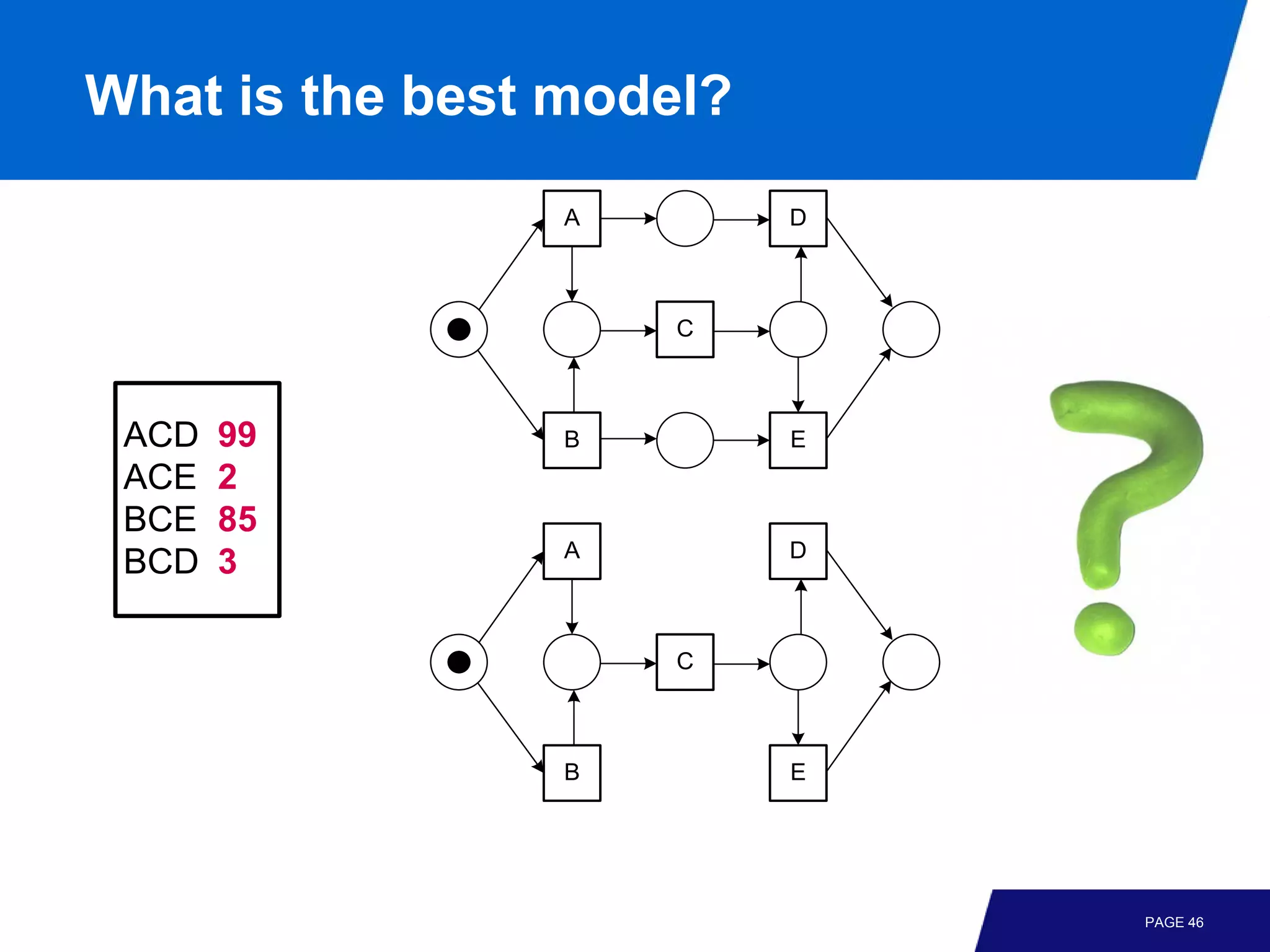
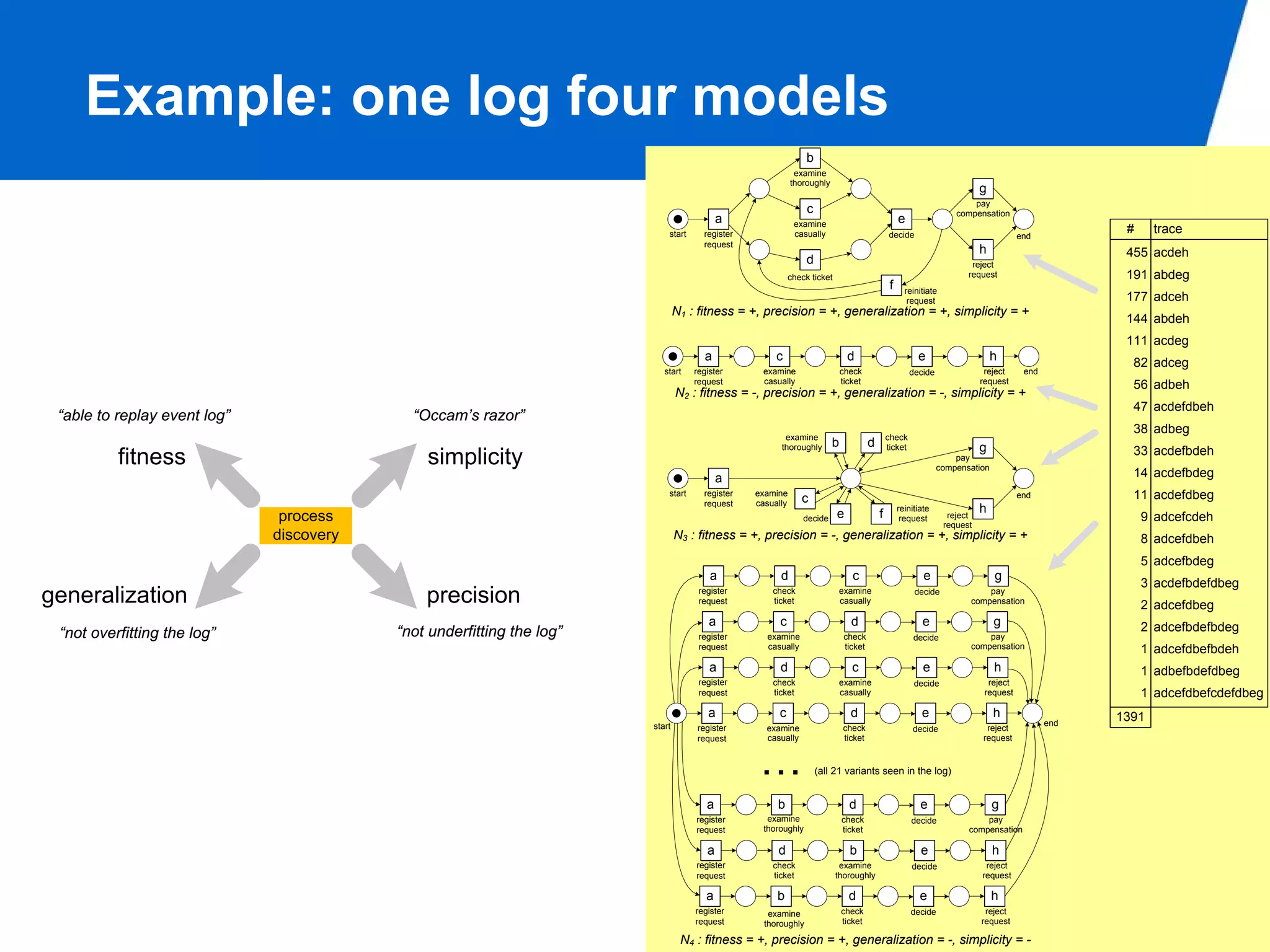
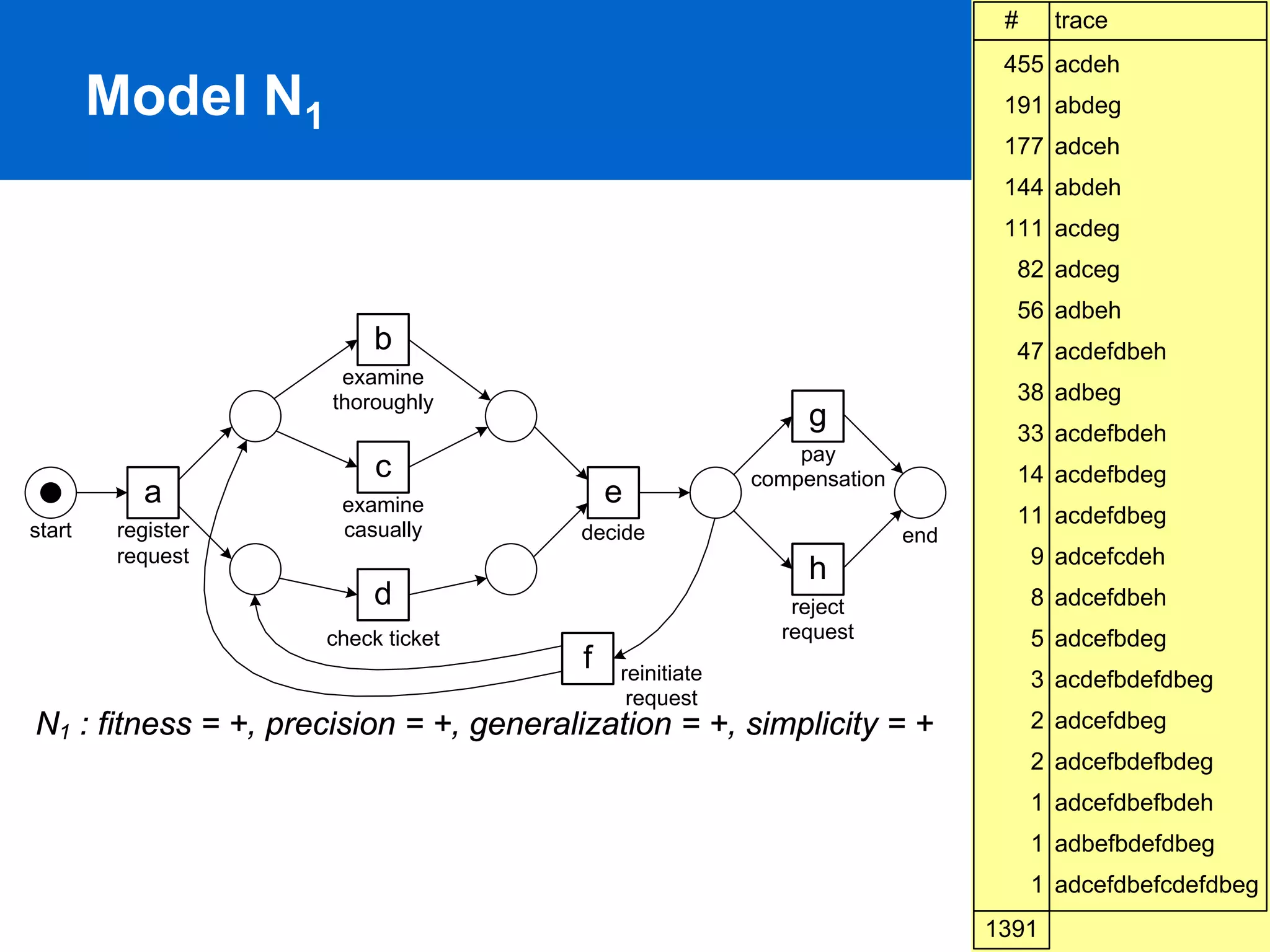
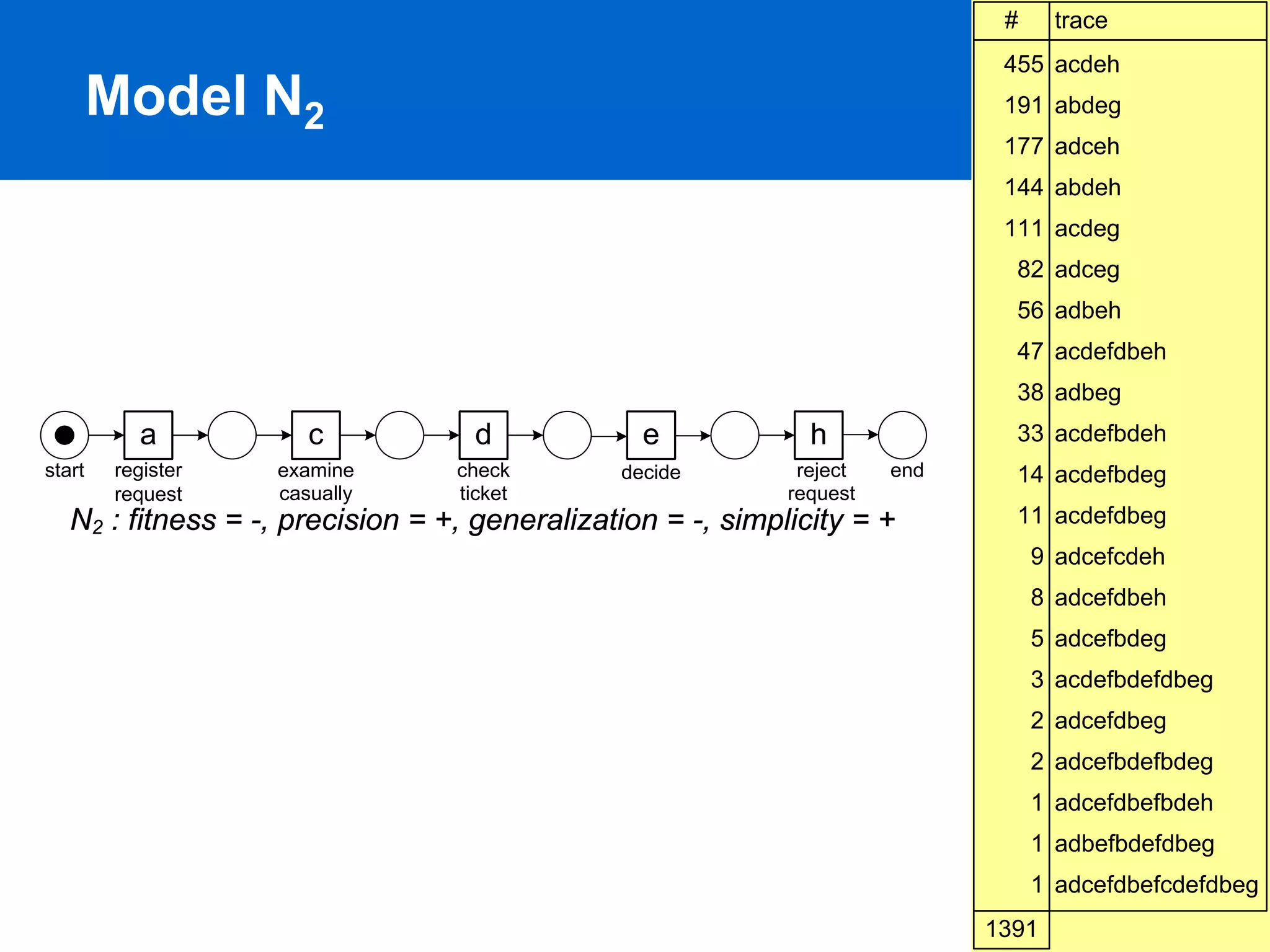
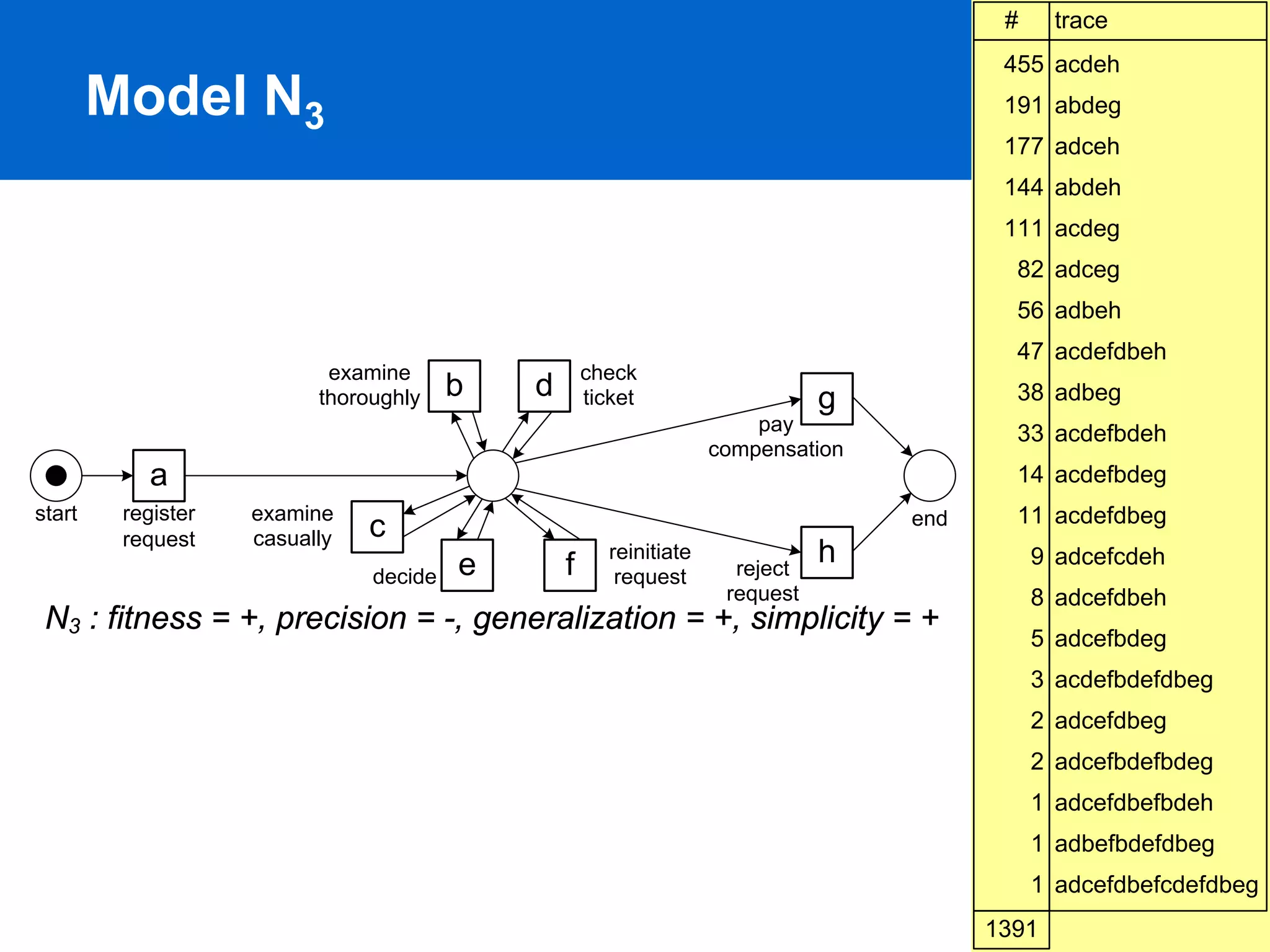
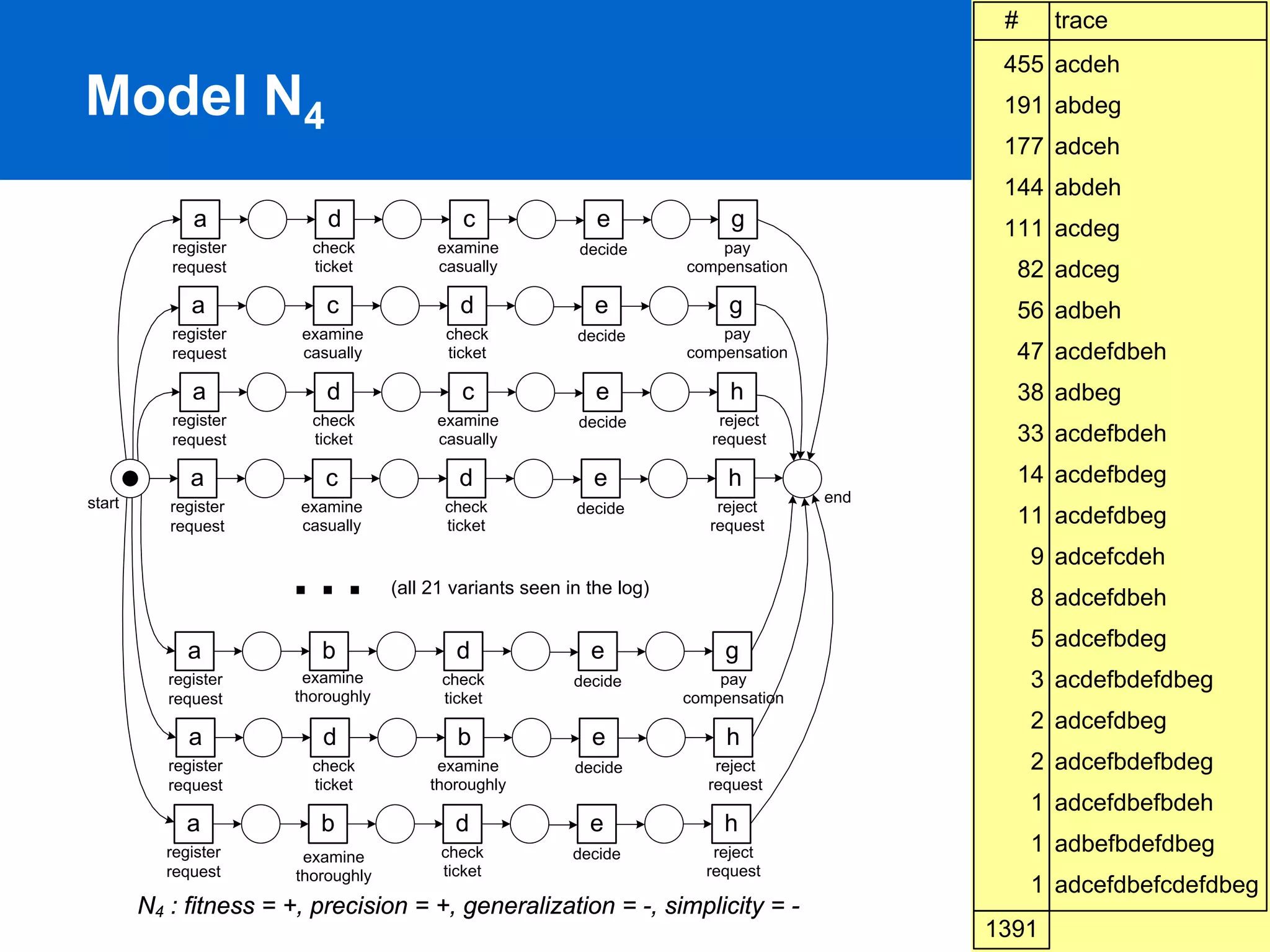
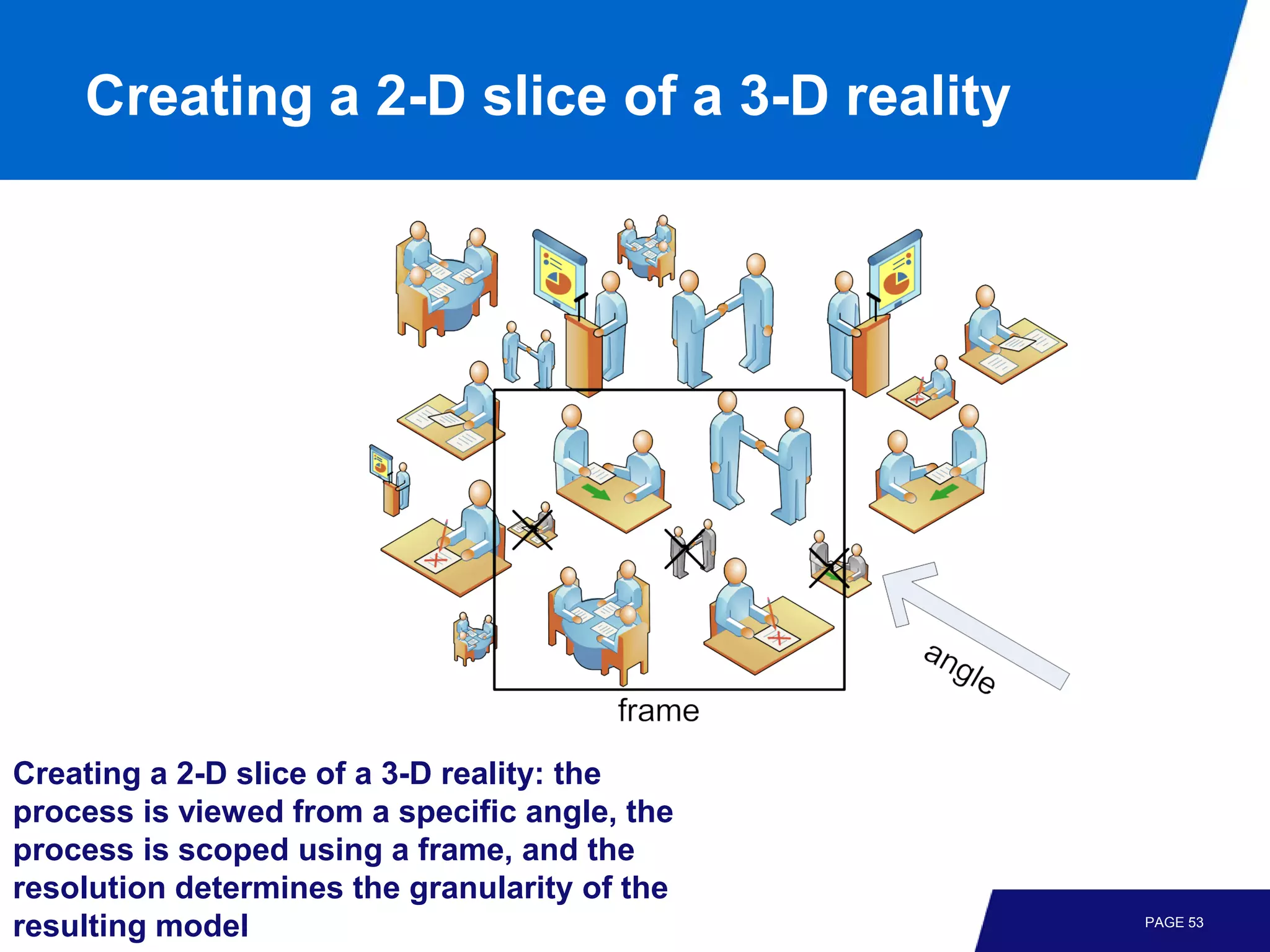
The document discusses process discovery and introduces the α algorithm. It begins by defining key terms like process discovery, fitness, precision, generalization, and simplicity. It then walks through examples of event logs and the corresponding process models that could be discovered from them. The α algorithm is introduced and explained as a basic process discovery technique. Limitations of the α algorithm are also discussed, such as its inability to handle implicit places, loops, and non-local dependencies. The challenges of process discovery are summarized, including noise, incompleteness, and balancing between underfitting and overfitting models.