DHS Guidelines
•
1 like•192 views
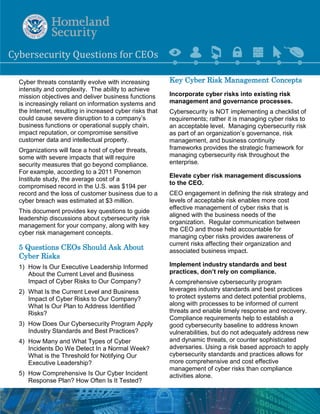
Cyber threats are constantly evolving and pose increasing risks to companies. Organizations face a variety of cyber threats that could severely disrupt business operations or compromise sensitive customer data. CEOs should ask five key questions to effectively manage cybersecurity risks, understand current threats, ensure compliance with best practices, and oversee incident response plans. A comprehensive risk management approach is needed to implement industry standards, evaluate specific organizational risks, and maintain awareness of the evolving cyber threat environment.
Report
Share
Report
Share
Download to read offline
Recommended
Cybersecurity Goverence for Boards of Directors

This paper discusses the emerging issue of Board of Directors Governance and Cybersecurity. Originally presented to the Boards of Directors of the IRC http://www.isorto.org/Pages/Home in May 2014. The paper is in a continuous improvement mode ultimately targeting being a resource for Boards of Directors in the energy (electricity and natural gas) industry. Suggested updates and improvements are welcome at PaulFeldman@Gmail.com The current copy is always at http://www.EnergyCollection.us/456.pdf
Information risk management

The presentation is about information risk management. It covers information threats, risks, vulnerabilities and importance of risk assessment for information security for software companies in India.
http://www.ifour-consultancy.com
Its time to rethink everything a governance risk compliance primer

Governance, Risk, & Compliance (GRC) is more than a catchy acronym – it is an approach to business culture. GRC is a three-legged stool that is necessary to effectively manage and steer the organization. This presentation will provide an introduction to GRC and discuss the collaboration and sharing of information, assessments, metrics, risks, policies, training, and losses across business roles and processes. GRC helps identify interrelationships in today’s complex and distributed business environment.
Strategy Insights - How to Quantify IT Risks 

It was a pleasure to moderate a workshop to assess cyber security risks hosted by Strategy Insights. We discussed options and practices to quantify confidentiality, integrity, and availability risks with delegates of the big players in the pharma, banking, retailing, and service sectors in the Nordics.
Thanks to Anna Rose Poyntz, Finlay Wilson, and Edgar Baier for the event coordination.
Round tables https://lnkd.in/e_m5eTW5
#cybersecurity #compliance #strategy #banking #ciso #riskmanagement
Recommended
Cybersecurity Goverence for Boards of Directors

This paper discusses the emerging issue of Board of Directors Governance and Cybersecurity. Originally presented to the Boards of Directors of the IRC http://www.isorto.org/Pages/Home in May 2014. The paper is in a continuous improvement mode ultimately targeting being a resource for Boards of Directors in the energy (electricity and natural gas) industry. Suggested updates and improvements are welcome at PaulFeldman@Gmail.com The current copy is always at http://www.EnergyCollection.us/456.pdf
Information risk management

The presentation is about information risk management. It covers information threats, risks, vulnerabilities and importance of risk assessment for information security for software companies in India.
http://www.ifour-consultancy.com
Its time to rethink everything a governance risk compliance primer

Governance, Risk, & Compliance (GRC) is more than a catchy acronym – it is an approach to business culture. GRC is a three-legged stool that is necessary to effectively manage and steer the organization. This presentation will provide an introduction to GRC and discuss the collaboration and sharing of information, assessments, metrics, risks, policies, training, and losses across business roles and processes. GRC helps identify interrelationships in today’s complex and distributed business environment.
Strategy Insights - How to Quantify IT Risks 

It was a pleasure to moderate a workshop to assess cyber security risks hosted by Strategy Insights. We discussed options and practices to quantify confidentiality, integrity, and availability risks with delegates of the big players in the pharma, banking, retailing, and service sectors in the Nordics.
Thanks to Anna Rose Poyntz, Finlay Wilson, and Edgar Baier for the event coordination.
Round tables https://lnkd.in/e_m5eTW5
#cybersecurity #compliance #strategy #banking #ciso #riskmanagement
The Significance of IT Security Management & Risk Assessment

The Significance of IT Security Management & Risk Assessment
An overview of IT Security Management, which is comprised of standards, policies, plans, and procedures as well as risk assessment and the various techniques and approaches to minimize an organization’s financial impact due to the exploitation of numerous organizational assets.
Cybersecurity Actions for CEOs

Reaching the position of CEO inside a company is definitely one of the highest goals that a person can achieve, however the responsibilities that come together with this position are even higher.
Generally speaking, a CEO should have work experience and general knowledge. In addition, a CEO should be a good communicator, be eager to develop and present a vision and a strategy for the company, motivate others, garner respect and have knowledge about entire management processes inside the company.
However, no one can have a professional knowledge and be a master of everything; this is the reason why a CEO should be regularly informed over the company’s issues.
The data of negotiated contracts, marketing plan decisions, new employees’ CVs, customers’ information, ideas, etc. All these information a CEO can receive on a daily bases. The value of these received data goes beyond the written words, especially nowadays when the breaches toward these data are constantly evolving together with its cost. The Ponemon Institute published the results of data breach for 2014. According to this institute, the average total cost of a data breach in 2014 was $3.5 million, 15 percent higher as compared to the previous year, and it is rising to $5.85 million for an organization in the United States.
Information Risk Management Overview

Marsh Risk Consulting Boardroom Series - Information Risk Management - Elvin Chan
How to measure your cybersecurity performance

In order for organizations to stay competitive, they must always be improving. This too is true for their cybersecurity.
Being able to properly harvest and digest cybersecurity benchmarking information is critical for today’s CIOs. If you realize that your cybersecurity is not at the level it should be, evaluating it properly can help you raise appropriate resources to fix the issues.
Discover how to get the full picture of your organization's security performance compared to your peers. Learn why benchmarking is so critical for today's CIOs and how to clearly communicate benchmarking data to your board.
Information Technology Vendor Risk Management

Information Technology Vendor Risk Management
Identified Risks Throughout the Sourcing and Vendor Management Life Cycle
An Intro to Resolver's Incident Management Application

Interested in seeing how Resolver is tackling the future of Incident Management? What about implementing something today? Get a first look at the relaunch of Incident Management on Core. Learn how we have taken the best of Perspective to a whole new (and often simpler) level. And we’re not stopping there — learn about the incident/investigation functionality and see how it all ties together with risks that impact the security of your organization.
Cyber security reguations: The shape of things to come for captives?

Article discussing the potential impact of emerging cyber security regulations on captive insurance companies. Originally published in Captive Insurance Times, 5 April 2017.
Protect Yourself from Cyber Attacks Through Proper Third-Party Risk Management

Cyber attacks from nation-state actors and their proxies are on the rise. Many of these attackers seek a broader scale to do more damage than simply defacing a website with embarrassing propaganda or by causing a temporary internet outage with a DDOS attack. These hackers often have significant backing and resources from their nation-state sponsors, officially or unofficially.
Increasingly, they are targeting key infrastructures such as power utilities, financial networks, hospitals, healthcare organizations, and state and local governments. A popular tactic is to come in through vendors or managed service providers where they can leverage one successful hack to access dozens of entities. This makes proper vendor and third-party risk management more important than ever.
In this webinar, “Protect Yourself from Cyber Attacks Through Proper Third-Party Risk Management” we will discuss the threats, methods and attack vectors that hackers are using, with recent examples followed by best practice areas to focus on in order to secure your organization from these types of cyberattacks.
Business case for enterprise continuity planning

Executive brief outline for business continuity planning. This presentation also outlines the high-level steps to complete business continuity within your organization
Hernan Huwyler Corporate Risk Assesstment Compliance Risks

Performing a legal and compliance risk assessment. A Step-by-Step Implementation Guide-
Planning the Risk Assessment
Assessing and Prioritizing Risks
Improving Legal Risk Mitigation
Risk Management Approach to Cyber Security 

Why we need to use a Risk Management Approach to Cyber Security.
Cyber(in)security: systemic risks and responses

Presented at National Security 2008 in Brussels. Updated for British Computer Society, Deutsche Bank, Oxford University, and University of Southern Denmark.
More Related Content
What's hot
The Significance of IT Security Management & Risk Assessment

The Significance of IT Security Management & Risk Assessment
An overview of IT Security Management, which is comprised of standards, policies, plans, and procedures as well as risk assessment and the various techniques and approaches to minimize an organization’s financial impact due to the exploitation of numerous organizational assets.
Cybersecurity Actions for CEOs

Reaching the position of CEO inside a company is definitely one of the highest goals that a person can achieve, however the responsibilities that come together with this position are even higher.
Generally speaking, a CEO should have work experience and general knowledge. In addition, a CEO should be a good communicator, be eager to develop and present a vision and a strategy for the company, motivate others, garner respect and have knowledge about entire management processes inside the company.
However, no one can have a professional knowledge and be a master of everything; this is the reason why a CEO should be regularly informed over the company’s issues.
The data of negotiated contracts, marketing plan decisions, new employees’ CVs, customers’ information, ideas, etc. All these information a CEO can receive on a daily bases. The value of these received data goes beyond the written words, especially nowadays when the breaches toward these data are constantly evolving together with its cost. The Ponemon Institute published the results of data breach for 2014. According to this institute, the average total cost of a data breach in 2014 was $3.5 million, 15 percent higher as compared to the previous year, and it is rising to $5.85 million for an organization in the United States.
Information Risk Management Overview

Marsh Risk Consulting Boardroom Series - Information Risk Management - Elvin Chan
How to measure your cybersecurity performance

In order for organizations to stay competitive, they must always be improving. This too is true for their cybersecurity.
Being able to properly harvest and digest cybersecurity benchmarking information is critical for today’s CIOs. If you realize that your cybersecurity is not at the level it should be, evaluating it properly can help you raise appropriate resources to fix the issues.
Discover how to get the full picture of your organization's security performance compared to your peers. Learn why benchmarking is so critical for today's CIOs and how to clearly communicate benchmarking data to your board.
Information Technology Vendor Risk Management

Information Technology Vendor Risk Management
Identified Risks Throughout the Sourcing and Vendor Management Life Cycle
An Intro to Resolver's Incident Management Application

Interested in seeing how Resolver is tackling the future of Incident Management? What about implementing something today? Get a first look at the relaunch of Incident Management on Core. Learn how we have taken the best of Perspective to a whole new (and often simpler) level. And we’re not stopping there — learn about the incident/investigation functionality and see how it all ties together with risks that impact the security of your organization.
Cyber security reguations: The shape of things to come for captives?

Article discussing the potential impact of emerging cyber security regulations on captive insurance companies. Originally published in Captive Insurance Times, 5 April 2017.
Protect Yourself from Cyber Attacks Through Proper Third-Party Risk Management

Cyber attacks from nation-state actors and their proxies are on the rise. Many of these attackers seek a broader scale to do more damage than simply defacing a website with embarrassing propaganda or by causing a temporary internet outage with a DDOS attack. These hackers often have significant backing and resources from their nation-state sponsors, officially or unofficially.
Increasingly, they are targeting key infrastructures such as power utilities, financial networks, hospitals, healthcare organizations, and state and local governments. A popular tactic is to come in through vendors or managed service providers where they can leverage one successful hack to access dozens of entities. This makes proper vendor and third-party risk management more important than ever.
In this webinar, “Protect Yourself from Cyber Attacks Through Proper Third-Party Risk Management” we will discuss the threats, methods and attack vectors that hackers are using, with recent examples followed by best practice areas to focus on in order to secure your organization from these types of cyberattacks.
Business case for enterprise continuity planning

Executive brief outline for business continuity planning. This presentation also outlines the high-level steps to complete business continuity within your organization
Hernan Huwyler Corporate Risk Assesstment Compliance Risks

Performing a legal and compliance risk assessment. A Step-by-Step Implementation Guide-
Planning the Risk Assessment
Assessing and Prioritizing Risks
Improving Legal Risk Mitigation
Risk Management Approach to Cyber Security 

Why we need to use a Risk Management Approach to Cyber Security.
Cyber(in)security: systemic risks and responses

Presented at National Security 2008 in Brussels. Updated for British Computer Society, Deutsche Bank, Oxford University, and University of Southern Denmark.
What's hot (20)
The Significance of IT Security Management & Risk Assessment

The Significance of IT Security Management & Risk Assessment
An Intro to Resolver's Incident Management Application

An Intro to Resolver's Incident Management Application
Cyber security reguations: The shape of things to come for captives?

Cyber security reguations: The shape of things to come for captives?
Protect Yourself from Cyber Attacks Through Proper Third-Party Risk Management

Protect Yourself from Cyber Attacks Through Proper Third-Party Risk Management
Meraj Ahmad - Information security in a borderless world

Meraj Ahmad - Information security in a borderless world
Hernan Huwyler Corporate Risk Assesstment Compliance Risks

Hernan Huwyler Corporate Risk Assesstment Compliance Risks
Cybersecurity Preparedness Benchmark Study_Webex 27 Ocober 2016

Cybersecurity Preparedness Benchmark Study_Webex 27 Ocober 2016
Viewers also liked
20131003 H2020 Pamplona Andrés Montero: H2020 y asociaciones europeas para la...

20131003 H2020 Pamplona Andrés Montero: H2020 y asociaciones europeas para la innovación. eip de agricultura sostenible y su conexión con h2020
Viewers also liked (6)
20131003 H2020 Pamplona Andrés Montero: H2020 y asociaciones europeas para la...

20131003 H2020 Pamplona Andrés Montero: H2020 y asociaciones europeas para la...
Heide-Mieke Scherpereel - Sensotec WoDy Audiokrant

Heide-Mieke Scherpereel - Sensotec WoDy Audiokrant
Similar to DHS Guidelines
Mastering Cybersecurity Risk Management: Strategies to Safeguard Your Digital...

In today’s time, where businesses heavily depend on technology for their daily operations, the danger of cyberattacks is a big concern. Companies need to have a solid plan in place to manage the risks associated with cybersecurity. This means taking the necessary steps to protect sensitive data and systems from bad guys who want to cause harm. In this article, we’ll explain why cybersecurity risk management is so important and share some practical strategies to help you keep your digital assets safe. So, let’s dive in and explore how you can protect your business from cyber threats!
10 Questions for the C-Suite in Assessing Cyber Risk

Deloitte 17 page whitepaper and 10 questions to help C-Suite and Boards to assess their Cyber Security Maturity
Cybersecurity Incident Response Planning.pdf

In this blog, we’ll delve into the importance of cybersecurity incident response planning and provide a guide for building a resilient response strategy.
Cyber presentation spet 2019 v8sentfor upload

An accountant is a valuable asset to any organization. He or she is a professional who performs accounting functions. Accounting is not only confined to tax and financial matters as per what people generally think.
Weakest links of an organization's Cybersecurity chain

What is Cyber Security
What is Cyber Threat and Threat Landscape
Is Cybersecurity an IT Problem? It’s a human Problem
Role of a CFO
Well accepted Cybersecurity Frameworks and common Themes
SOC (Service Organization Control) and SOC for Cybersecurity
Recommended risk mitigation strategies for the weakest links of the Cybersecurity chain
Key Takeaways
Best Practices
For Corporate Boards, a Cyber Security Top 10

Corporate boards of directors have a fiduciary duty to understand and oversee cyber security. For most effective oversight, boards should approach cyber security from a good management-practices perspective rather than a technical perspective.
Defensive Cybersecurity: A Modern Approach to Safeguarding Digital Assets

As cyber threats continue to multiply and evolve in complexity, the importance of a strong defensive cybersecurity strategy cannot be overstated.
w-cyber-risk-modeling Owasp cyber risk quantification 2018

Presented at https://open-security-summit.org/
Improving Cyber Readiness with the NIST Cybersecurity Framework

Still need a prime on the CSF? Check out my article for the Access Business Team January 2017 Newsletter on how business can improve their cyber readiness with the NIST Cybersecurity Framework.
Cybersecurity Risk Management for Financial Institutions

The New York State Department of Financial Services has been closely monitoring this ever-growing threat and has proposed regulations that would require financial services companies to adopt a cybersecurity program to protect their customers, employees, data and operations. Its proposed changes are expected to take effect on March 1, 2017. Financial services companies would have until Feb. 15, 2018, to submit a certificate of compliance with the program. Components of New York's proposed cybersecurity program are outlined in this article.
CyberM3 Business Enablement: Cybersecurity That Empowers Your Business with C...

CyberM3 Business Enablement: Booz Allen Hamilton’s Cybersecurity Reference Model empowers your business with comprehensive information security.
A Guide for Businesses.pdf

Stay informed and protected with our Data Breaches Blog - Your source for the latest insights, news, and strategies.
Cyber-Security-Whitepaper.pdf

Cyber-attacks are an alarming threat to all types of businesses & organizations.The risk of a cyber-attack is not just a risk to your company but also to your privacy.Hence, cybersecurity is crucial for every business. Cybersecurity protects critical data from cyber attackers. This includes sensitive data, governmental and industry information, personal information, personally identifiable information (PII), intellectual property, and protected health information (PHI). If you are looking for tools to fight against cyber threats, then Techwave’s tools & technologies with adequate controls will help your organization stay protected.
Cyber-Security-Whitepaper.pdf

Cyber-attacks are an alarming threat to all types of businesses & organizations.The risk of a cyber-attack is not just a risk to your company but also to your privacy.Hence, cybersecurity is crucial for every business. Cybersecurity protects critical data from cyber attackers. This includes sensitive data, governmental and industry information, personal information, personally identifiable information (PII), intellectual property, and protected health information (PHI). If you are looking for tools to fight against cyber threats, then Techwave’s tools & technologies with adequate controls will help your organization stay protected.
Similar to DHS Guidelines (20)
Mastering Cybersecurity Risk Management: Strategies to Safeguard Your Digital...

Mastering Cybersecurity Risk Management: Strategies to Safeguard Your Digital...
10 Questions for the C-Suite in Assessing Cyber Risk

10 Questions for the C-Suite in Assessing Cyber Risk
Weakest links of an organization's Cybersecurity chain

Weakest links of an organization's Cybersecurity chain
Defensive Cybersecurity: A Modern Approach to Safeguarding Digital Assets

Defensive Cybersecurity: A Modern Approach to Safeguarding Digital Assets
w-cyber-risk-modeling Owasp cyber risk quantification 2018

w-cyber-risk-modeling Owasp cyber risk quantification 2018
Improving Cyber Readiness with the NIST Cybersecurity Framework

Improving Cyber Readiness with the NIST Cybersecurity Framework
Cybersecurity Risk Management for Financial Institutions

Cybersecurity Risk Management for Financial Institutions
CyberM3 Business Enablement: Cybersecurity That Empowers Your Business with C...

CyberM3 Business Enablement: Cybersecurity That Empowers Your Business with C...
Integrating-Cyber-Security-for-Increased-Effectiveness

Integrating-Cyber-Security-for-Increased-Effectiveness
More from Meg Weber
Working with Law Enforcement on Cyber Security Strategies

Join Cyber Risk Summit Speakers as they discuss the best practices in working with law enforcement
More from Meg Weber (20)
Audit summary from security solutions and ovation tech

Audit summary from security solutions and ovation tech
Nemours case study nemours embraces app innovation with mobile iron

Nemours case study nemours embraces app innovation with mobile iron
Working with Law Enforcement on Cyber Security Strategies

Working with Law Enforcement on Cyber Security Strategies
Recently uploaded
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovation With Your Product by VP of Product Design, Warner Music Group
Knowledge engineering: from people to machines and back

Keynote at the 21st European Semantic Web Conference
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
Search and Society: Reimagining Information Access for Radical Futures

The field of Information retrieval (IR) is currently undergoing a transformative shift, at least partly due to the emerging applications of generative AI to information access. In this talk, we will deliberate on the sociotechnical implications of generative AI for information access. We will argue that there is both a critical necessity and an exciting opportunity for the IR community to re-center our research agendas on societal needs while dismantling the artificial separation between the work on fairness, accountability, transparency, and ethics in IR and the rest of IR research. Instead of adopting a reactionary strategy of trying to mitigate potential social harms from emerging technologies, the community should aim to proactively set the research agenda for the kinds of systems we should build inspired by diverse explicitly stated sociotechnical imaginaries. The sociotechnical imaginaries that underpin the design and development of information access technologies needs to be explicitly articulated, and we need to develop theories of change in context of these diverse perspectives. Our guiding future imaginaries must be informed by other academic fields, such as democratic theory and critical theory, and should be co-developed with social science scholars, legal scholars, civil rights and social justice activists, and artists, among others.
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

Reflecting on new architectures for knowledge based systems in light of generative ai
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
When stars align: studies in data quality, knowledge graphs, and machine lear...

Keynote at DQMLKG workshop at the 21st European Semantic Web Conference 2024
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Essentials of Automations: Optimizing FME Workflows with Parameters

Are you looking to streamline your workflows and boost your projects’ efficiency? Do you find yourself searching for ways to add flexibility and control over your FME workflows? If so, you’re in the right place.
Join us for an insightful dive into the world of FME parameters, a critical element in optimizing workflow efficiency. This webinar marks the beginning of our three-part “Essentials of Automation” series. This first webinar is designed to equip you with the knowledge and skills to utilize parameters effectively: enhancing the flexibility, maintainability, and user control of your FME projects.
Here’s what you’ll gain:
- Essentials of FME Parameters: Understand the pivotal role of parameters, including Reader/Writer, Transformer, User, and FME Flow categories. Discover how they are the key to unlocking automation and optimization within your workflows.
- Practical Applications in FME Form: Delve into key user parameter types including choice, connections, and file URLs. Allow users to control how a workflow runs, making your workflows more reusable. Learn to import values and deliver the best user experience for your workflows while enhancing accuracy.
- Optimization Strategies in FME Flow: Explore the creation and strategic deployment of parameters in FME Flow, including the use of deployment and geometry parameters, to maximize workflow efficiency.
- Pro Tips for Success: Gain insights on parameterizing connections and leveraging new features like Conditional Visibility for clarity and simplicity.
We’ll wrap up with a glimpse into future webinars, followed by a Q&A session to address your specific questions surrounding this topic.
Don’t miss this opportunity to elevate your FME expertise and drive your projects to new heights of efficiency.
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic (NeSy) AI is on the rise. However, simply machine learning on just any symbolic structure is not sufficient to really harvest the gains of NeSy. These will only be gained when the symbolic structures have an actual semantics. I give an operational definition of semantics as “predictable inference”.
All of this illustrated with link prediction over knowledge graphs, but the argument is general.
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
Recently uploaded (20)
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...
Knowledge engineering: from people to machines and back

Knowledge engineering: from people to machines and back
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
Search and Society: Reimagining Information Access for Radical Futures

Search and Society: Reimagining Information Access for Radical Futures
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

To Graph or Not to Graph Knowledge Graph Architectures and LLMs
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
When stars align: studies in data quality, knowledge graphs, and machine lear...

When stars align: studies in data quality, knowledge graphs, and machine lear...
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
Essentials of Automations: Optimizing FME Workflows with Parameters

Essentials of Automations: Optimizing FME Workflows with Parameters
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic is not enough, we need neuro-*semantic*
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
DHS Guidelines
- 1. Cyb ersecurity Que stions for CEO s Cyber threats constantly evolve with increasing intensity and complexity. The ability to achieve mission objectives and deliver business functions is increasingly reliant on information systems and the Internet, resulting in increased cyber risks that could cause severe disruption to a company’s business functions or operational supply chain, impact reputation, or compromise sensitive customer data and intellectual property. Organizations will face a host of cyber threats, some with severe impacts that will require security measures that go beyond compliance. For example, according to a 2011 Ponemon Institute study, the average cost of a compromised record in the U.S. was $194 per record and the loss of customer business due to a cyber breach was estimated at $3 million. This document provides key questions to guide leadership discussions about cybersecurity risk management for your company, along with key cyber risk management concepts. 5 Questions CEOs Should Ask About Cyber Risks 1) How Is Our Executive Leadership Informed About the Current Level and Business Impact of Cyber Risks to Our Company? 2) What Is the Current Level and Business Impact of Cyber Risks to Our Company? What Is Our Plan to Address Identified Risks? 3) How Does Our Cybersecurity Program Apply Industry Standards and Best Practices? 4) How Many and What Types of Cyber Incidents Do We Detect In a Normal Week? What is the Threshold for Notifying Our Executive Leadership? 5) How Comprehensive Is Our Cyber Incident Response Plan? How Often Is It Tested? Key Cyber Risk Management Concepts Incorporate cyber risks into existing risk management and governance processes. Cybersecurity is NOT implementing a checklist of requirements; rather it is managing cyber risks to an acceptable level. Managing cybersecurity risk as part of an organization’s governance, risk management, and business continuity frameworks provides the strategic framework for managing cybersecurity risk throughout the enterprise. Elevate cyber risk management discussions to the CEO. CEO engagement in defining the risk strategy and levels of acceptable risk enables more cost effective management of cyber risks that is aligned with the business needs of the organization. Regular communication between the CEO and those held accountable for managing cyber risks provides awareness of current risks affecting their organization and associated business impact. Implement industry standards and best practices, don’t rely on compliance. A comprehensive cybersecurity program leverages industry standards and best practices to protect systems and detect potential problems, along with processes to be informed of current threats and enable timely response and recovery. Compliance requirements help to establish a good cybersecurity baseline to address known vulnerabilities, but do not adequately address new and dynamic threats, or counter sophisticated adversaries. Using a risk based approach to apply cybersecurity standards and practices allows for more comprehensive and cost effective management of cyber risks than compliance activities alone.
- 2. h Cybersecurity Questions for CEOs Evaluate and manage your organization’s specific cyber risks. Identifying critical assets and associated impacts from cyber threats are critical to understanding a company’s specific risk exposure– whether financial, competitive, reputational, or regulatory. Risk assessment results are a key input to identify and prioritize specific protective measures, allocate resources, inform long-term investments, and develop policies and strategies to manage cyber risks to an acceptable level. Provide oversight and review. Executives are responsible to manage and oversee enterprise risk management. Cyber oversight activities include the regular evaluation of cybersecurity budgets, IT acquisition plans, IT outsourcing, cloud services, incident reports, risk assessment results, and top-level policies. Develop and test incident response plans and procedures. Even a well-defended organization will experience a cyber incident at some point. When network defenses are penetrated, a CEO should be prepared to answer, “What is our Plan B?” Documented cyber incident response plans that are exercised regularly help to enable timely response and minimize impacts. Coordinate cyber incident response planning across the enterprise. Early response actions can limit or even prevent possible damage. A key component of cyber incident response preparation is planning in conjunction with the Chief Information Officer/Chief Information Security Officer, business leaders, continuity planners, system operators, general counsel, and public affairs. This includes integrating cyber incident response policies and procedures with existing disaster recovery and business continuity plans. Maintain situational awareness of cyber threats. Situational awareness of an organization’s cyber risk environment involves timely detection of cyber incidents, along with the awareness of current threats and vulnerabilities specific to that organization and associated business impacts. Analyzing, aggregating, and integrating risk data from various sources and participating in threat information sharing with partners helps organizations identify and respond to incidents quickly and ensure protective efforts are commensurate with risk. A network operations center can provide real-time and trend data on cyber events. Business-line managers can help identify strategic risks, such as risks to the supply chain created through third- party vendors or cyber interdependencies. Sector Information-Sharing and Analysis Centers, government and intelligence agencies, academic institutions, and research firms also serve as valuable sources of threat and vulnerability information that can be used to enhance situational awareness. About DHS The Department of Homeland Security (DHS) is responsible for safeguarding our Nation’s critical infrastructure from physical and cyber threats that can affect our national security, public safety, and economic prosperity. For more information, please visit: www.dhs.gov/cyber. To report a cyber incident: https://forms.us-cert.gov/report/ or (888) 282-0870
