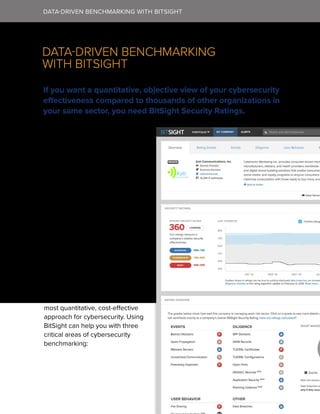
This document discusses the challenges of cybersecurity benchmarking for CIOs and introduces Security Ratings as a solution. Some of the key challenges of benchmarking include: the difficulty gathering accurate metrics over time to compare performance to peers; clearly communicating benchmarking results to boards; and identifying security issues affecting competitors. Security Ratings provide an objective, quantitative method to continuously monitor an organization's cybersecurity performance and compare to others in the same industry through daily analysis of external network data, helping CIOs address these challenges.