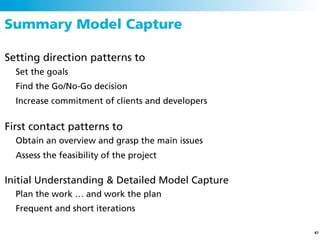
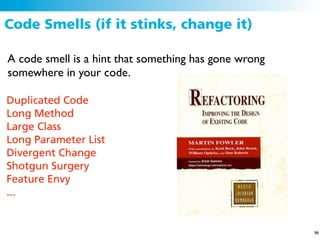
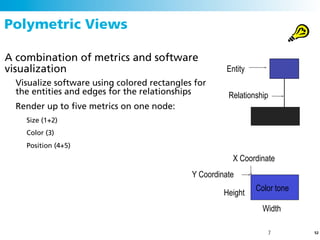
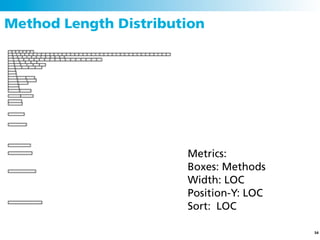
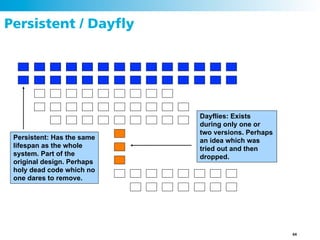
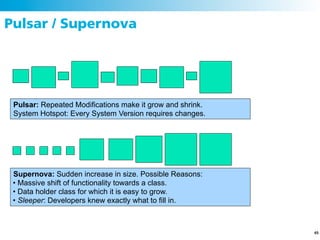
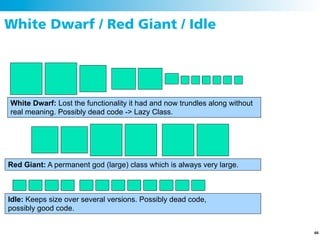
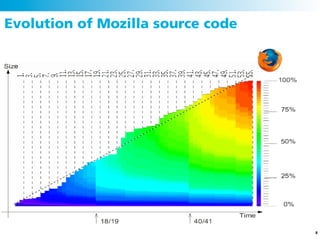
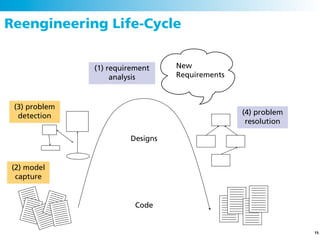
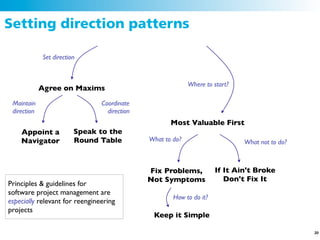
The document discusses the concept of software reengineering, highlighting the importance of addressing legacy software and the need for maintenance due to increasing complexity and design issues. It outlines the reengineering process, goals, and best practices, emphasizing the significance of reverse engineering and problem detection to improve software systems. Additionally, it mentions various tools and methodologies for analyzing and visualizing software code to identify 'code smells' and enhance understandability, modifiability, and maintainability.

![Let’s reengineer
Definition:
“Reengineering is the examination and alteration of a subject
system to reconstitute it in a new form and the subsequent
implementation of the new form.”
[Demeyer, Ducasse, Nierstrasz]
http://scg.unibe.ch/download/oorp/
14](https://image.slidesharecdn.com/devnologybacktoschoolsoftwarereengineering-110609014523-phpapp02/85/Devnology-back-toschool-software-reengineering-14-320.jpg)
![What is Reverse Engineering and why?
Reverse Engineering is the process of analyzing a subject system
to identify the system’s components and their interrelationships and
create representations of the system in another form or at a higher level
of abstraction [Chikofsky & Cross, ’90]
Motivation
Understanding other people’s code, the design and architecture in order
to maintain and evolve a software system
27](https://image.slidesharecdn.com/devnologybacktoschoolsoftwarereengineering-110609014523-phpapp02/85/Devnology-back-toschool-software-reengineering-27-320.jpg)