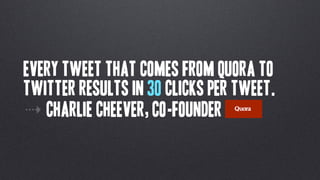
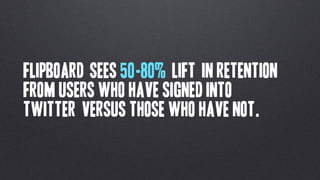
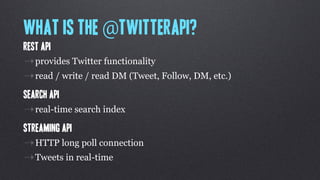
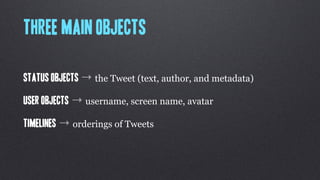
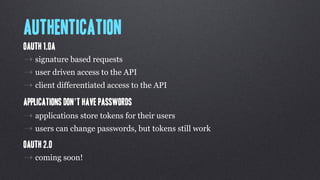
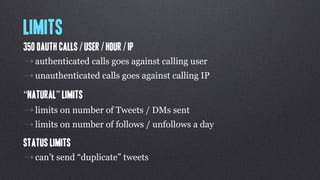
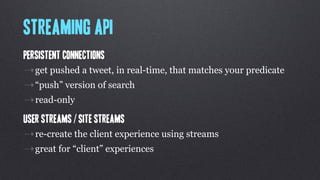
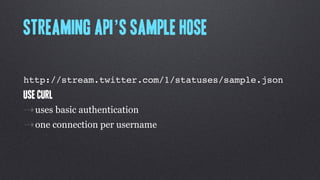
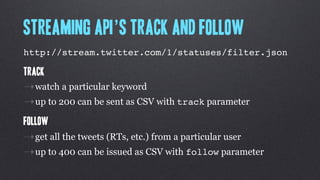
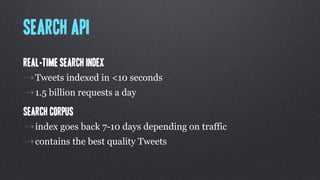
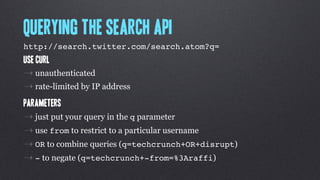
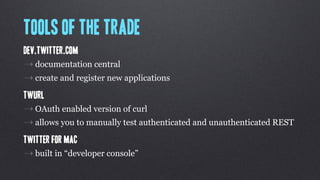
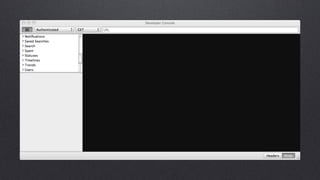
At a Techcrunch Disrupt Hackathon, the speaker gave a talk about the Twitter API and watched people hack. The speaker discussed that the Twitter API allows over 660k developers to access over 900k applications and the official Twitter applications. The speaker then went into details about the Twitter API, including how it provides read/write access to Tweets, follows, direct messages through a REST API, real-time search through a Search API, and real-time streams of data through the Streaming API.