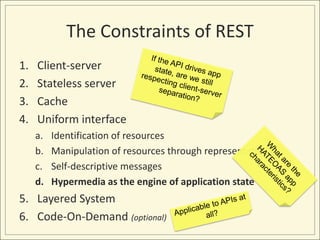
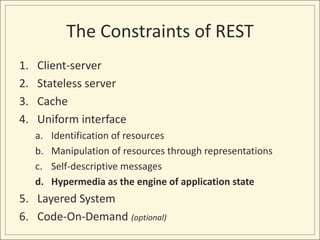
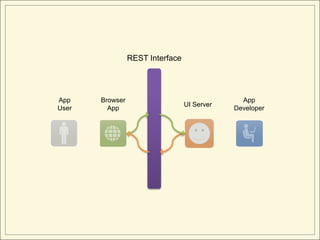
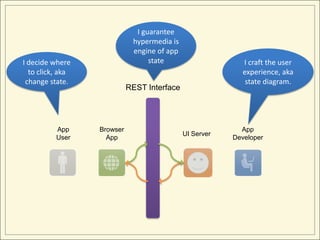
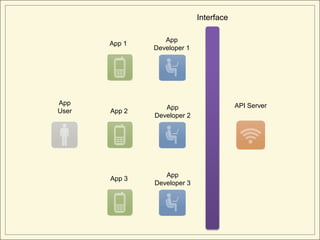
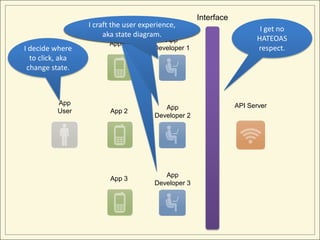
The document provides an introduction to HATEOAS (Hypermedia as the Engine of Application State), which is one of the constraints of REST.
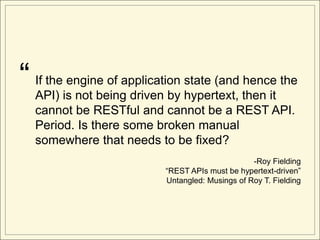
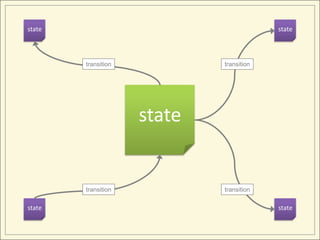
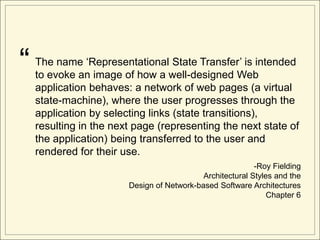
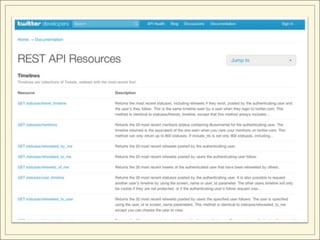
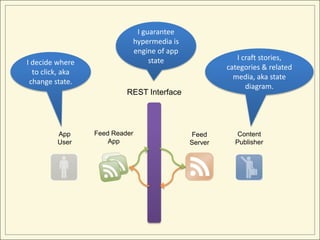
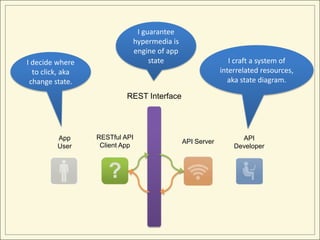
It defines HATEOAS as using hypermedia links in responses to drive application state, rather than through out-of-band information. Popular web APIs often violate HATEOAS by not including these links, unlike web user interfaces which adhere to it.
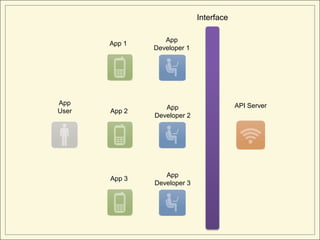
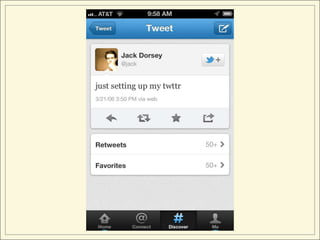
While including links in API responses may be helpful for developers, it does not truly implement HATEOAS unless the links drive the client application state at runtime, rather than the developer deciding application flow. A true HATEOAS client would handle generic RESTful APIs similar to how a feed reader handles synd







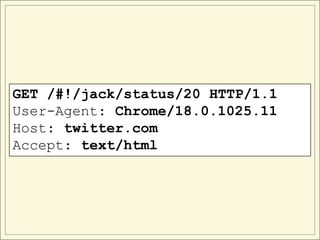
![<!DOCTYPE html>
<html data-nav-highlight-class-name="highlight-global-nav-home">
<head>
<title>Twitter</title>
<meta http-equiv="X-UA-Compatible" content="IE=edge">
<meta charset="utf-8" />
<meta name="description" content="Instantly connect to what's most important to
you. Follow your friends, experts, favorite celebrities, and breaking news." />
<link rel="dns-prefetch" href="http://a0.twimg.com"/>
<link rel="dns-prefetch" href="http://api.twitter.com"/>
<script type="text/javascript" charset="utf-8">
document.domain = 'twitter.com';
// this will be copied to twttr.appStartTime once our JS has started up
document.startTime = new Date().getTime();
var twttr = {};
twttr.versionName = 'phoenix';
twttr.isT1 = true;
twttr.didPingKeynote = false;
twttr.keynoteTTFTPing = function() {
if (!twttr.didPingKeynote && window.location.href.indexOf('keynoteTest') > 0) {
var image = document.createElement('img');
image.src = '/images/keynote.gif';
twttr.didPingKeynote = true;
}
}
window.console||function(){var
a=["log","debug","info","warn","error","assert","dir","dirxml","group","groupEnd","time","t
imeEnd","count","trace","profile","profileEnd"];window.console={};for(var
b=0;b<a.length;++b)window.console[a[b]]=function(){}}();
</script>
…](https://image.slidesharecdn.com/hateoas-120403180331-phpapp01/85/HATEOAS-101-Opinionated-Introduction-to-a-REST-API-Style-26-320.jpg)








![“ However, the style does not assume that all applications
are browsers. In fact, the application details are hidden
from the server by the generic connector interface, and
thus a user agent could equally be an automated robot
performing information retrieval for an indexing service,
a personal agent looking for data that matches certain
criteria, or a maintenance spider busy patrolling the
information for broken references or modified content
[39].
-Roy Fielding
Architectural Styles and the
Design of Network-based Software Architectures
Chapter 5](https://image.slidesharecdn.com/hateoas-120403180331-phpapp01/85/HATEOAS-101-Opinionated-Introduction-to-a-REST-API-Style-110-320.jpg)