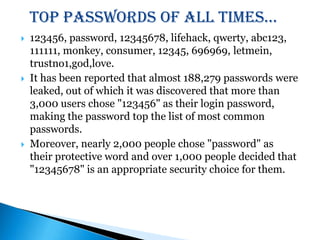
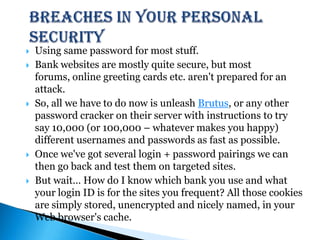
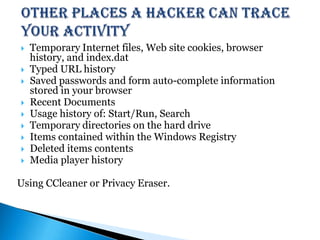
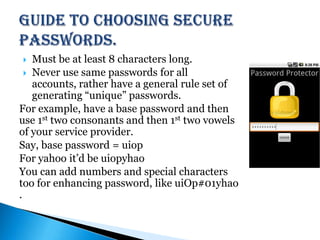
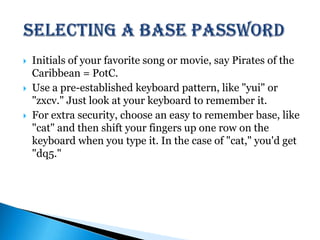
The document discusses common passwords and password security. It reports that the most common passwords are "123456", "password", and "12345678". Nearly 3,000 users chose "123456" as their password. The document provides tips for choosing more secure passwords such as using random letters, numbers, and symbols; avoiding common words and personal information; and not reusing the same password across accounts. It also warns about the risks of password cracking and accessing saved password information from browsers.