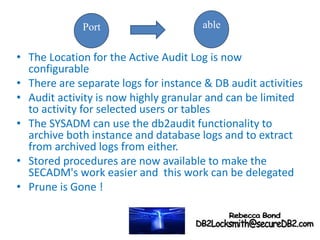
DB2 LUW Security introduces new auditing features in DB2 9.5 that make auditing more flexible and granular. Key points include:
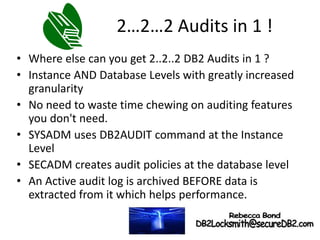
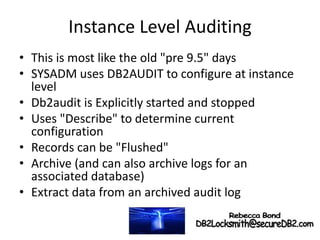
- Database auditing now has separate instance and database levels for more flexibility and separation of duties.
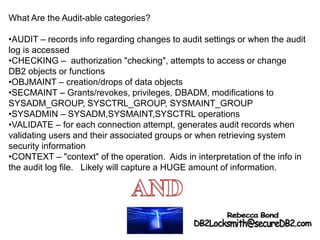
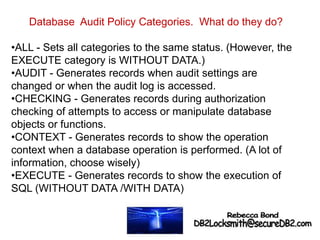
- New auditing categories like EXECUTE allow auditing just SQL statements instead of entire operation contexts.
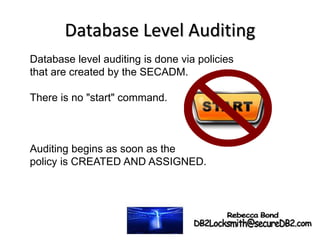
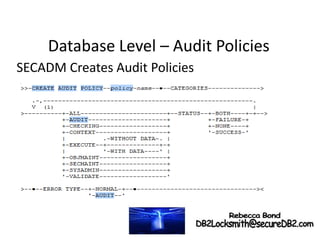
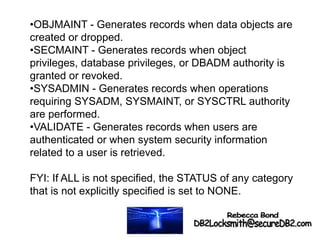
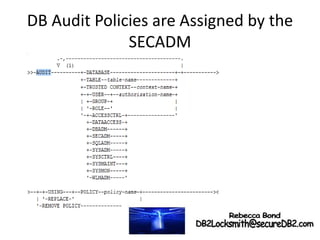
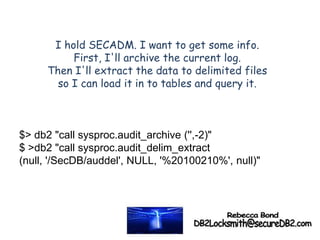
- Audit policies are used at the database level instead of the old db2audit commands. Policies are created and assigned to objects by SECADMs.
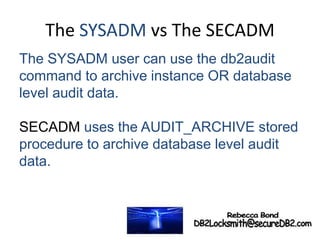
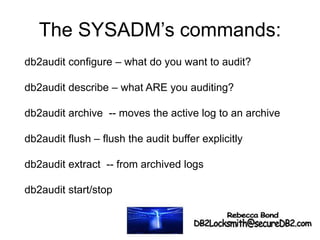
- Instance level auditing is still done with db2audit commands by SYSADMs, while database level uses stored procedures delegated by SECADMs.
- The new