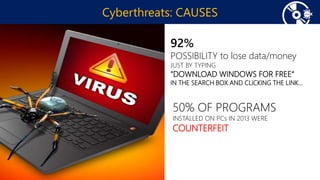
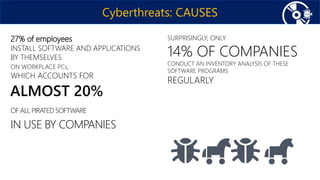
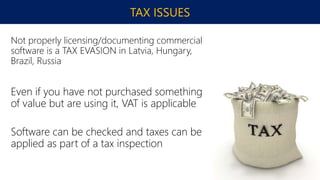
This document discusses the history and evolution of cyberthreats from early incidents in 2003-2004 caused by individuals for entertainment to modern sophisticated attacks by organized crime and states. It provides statistics on the number of people and businesses affected by cybercriminals each year. The top causes of cyberthreats are discussed, including pirated software containing vulnerabilities and users neglecting security updates. The document outlines consequences like losses to the IT industry and tax evasion. It recommends actions like using genuine software, security tools, and basic security rules. Finally, it describes security features of Windows 10 and Microsoft Office as well as Microsoft's cooperation with governments on security.