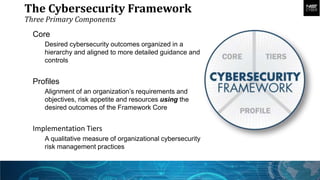
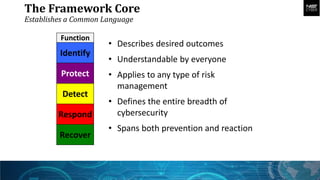
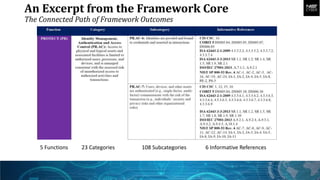
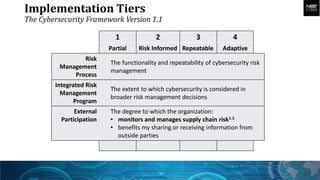
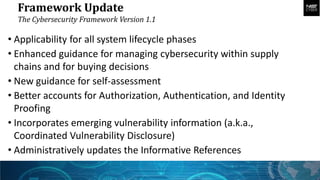
The document summarizes the Cybersecurity Framework, which provides a common language to manage cybersecurity risk across complex operations and partnerships. It has three main components: the Core establishes desired outcomes across functions like Identify and Protect; Profiles align requirements to the Core; and Implementation Tiers qualify risk management practices. The Framework is adaptable, risk-based, and guided by public and private perspectives to help organizations address cybersecurity challenges.