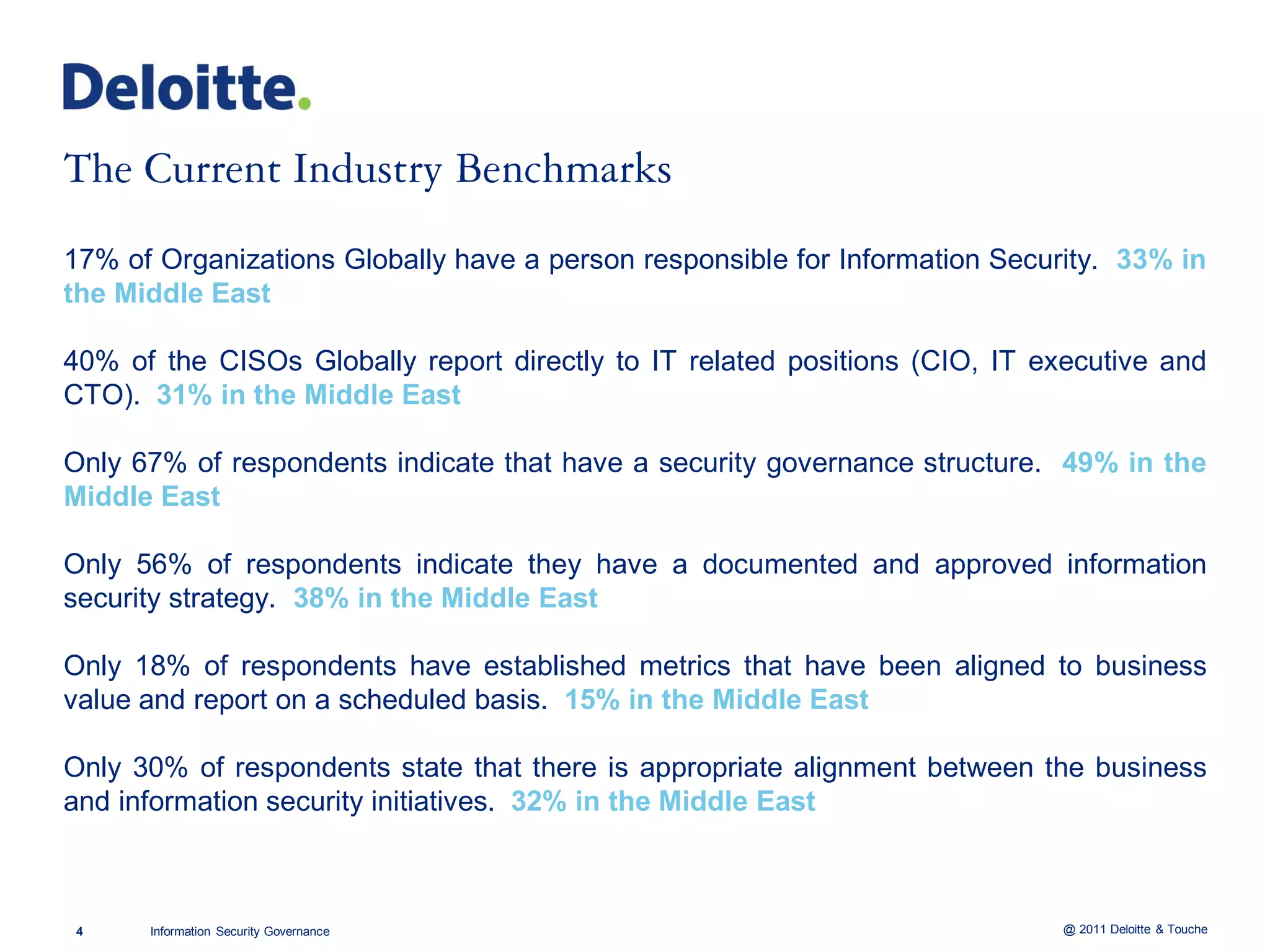
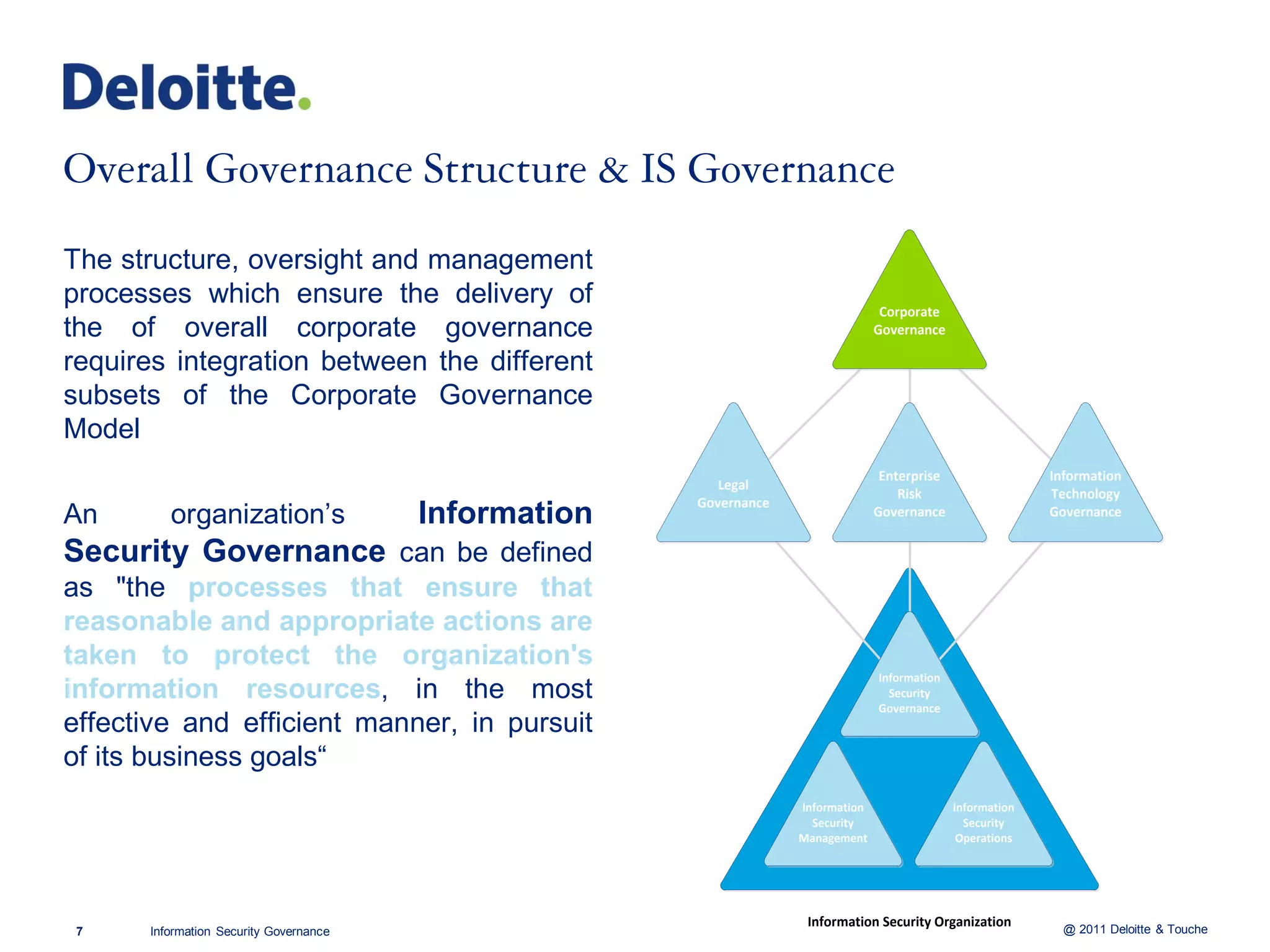
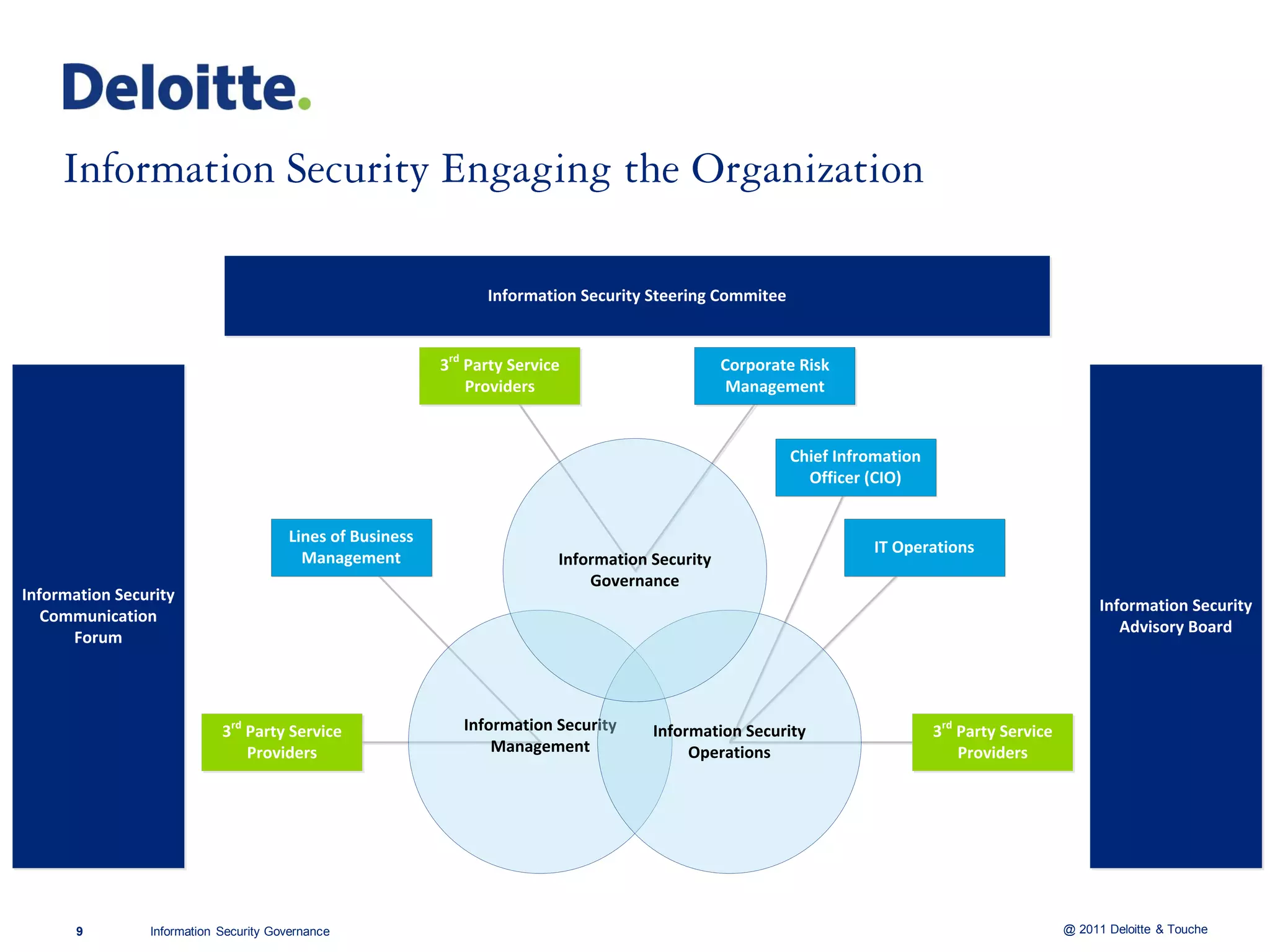
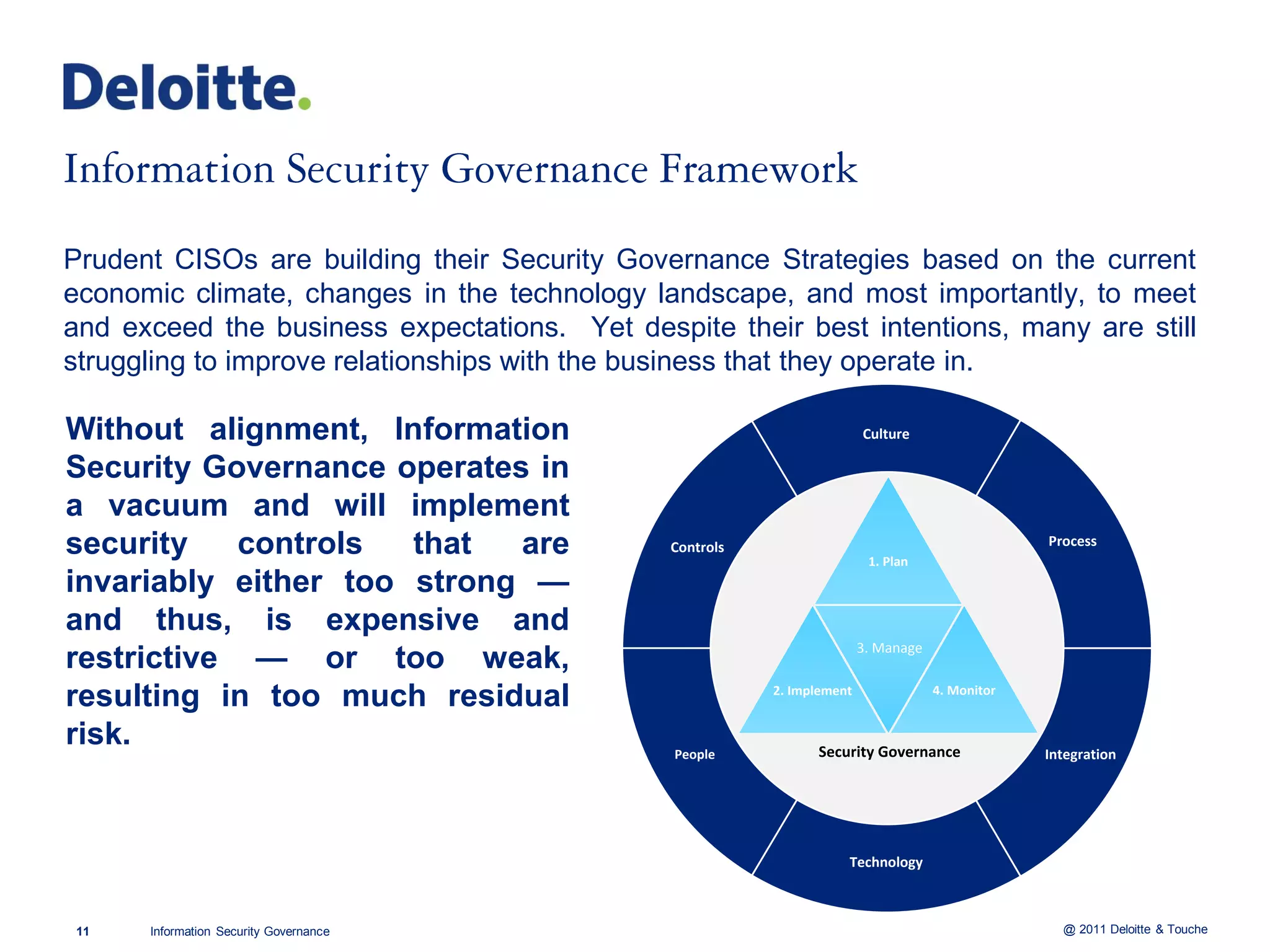
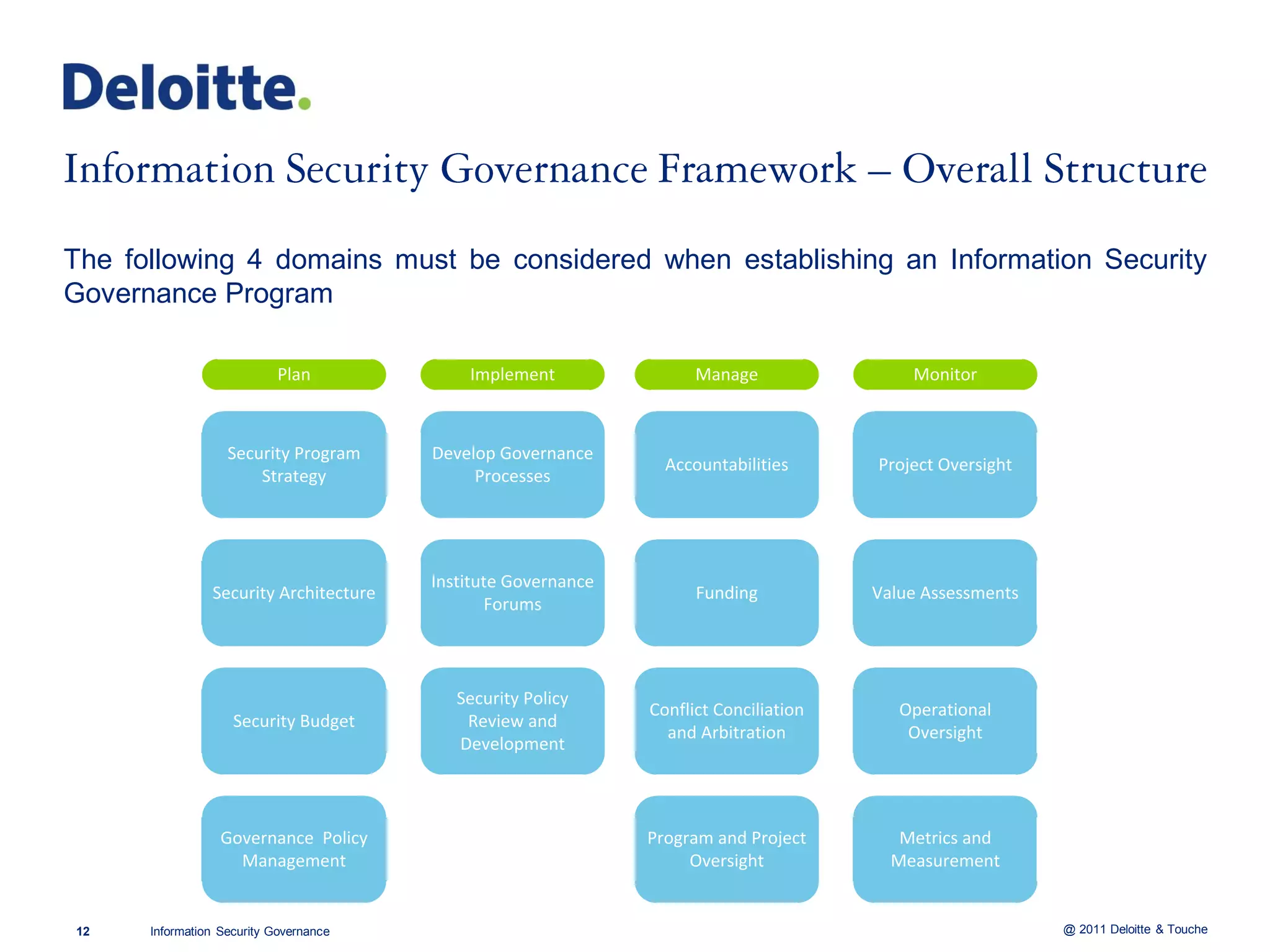
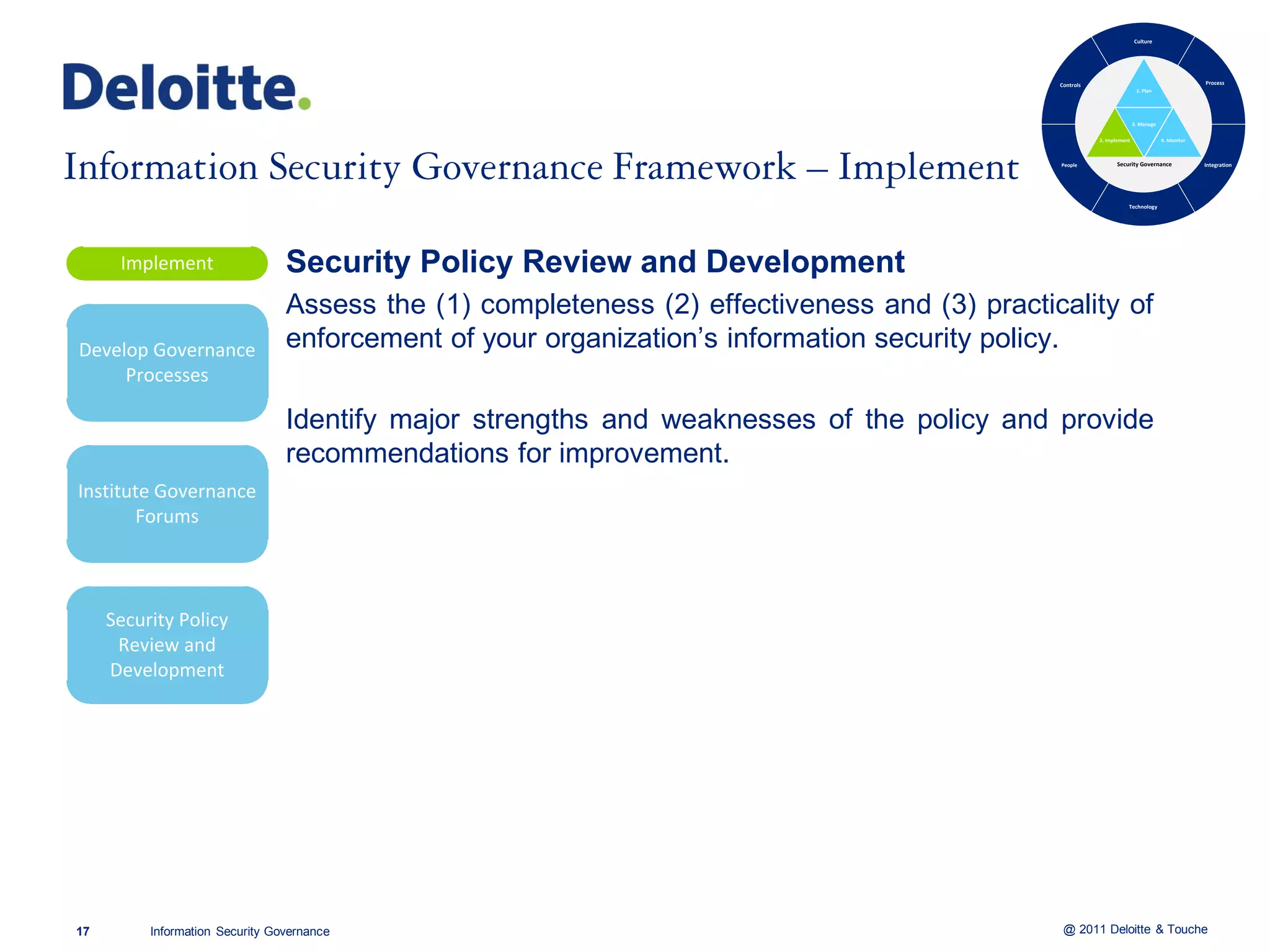
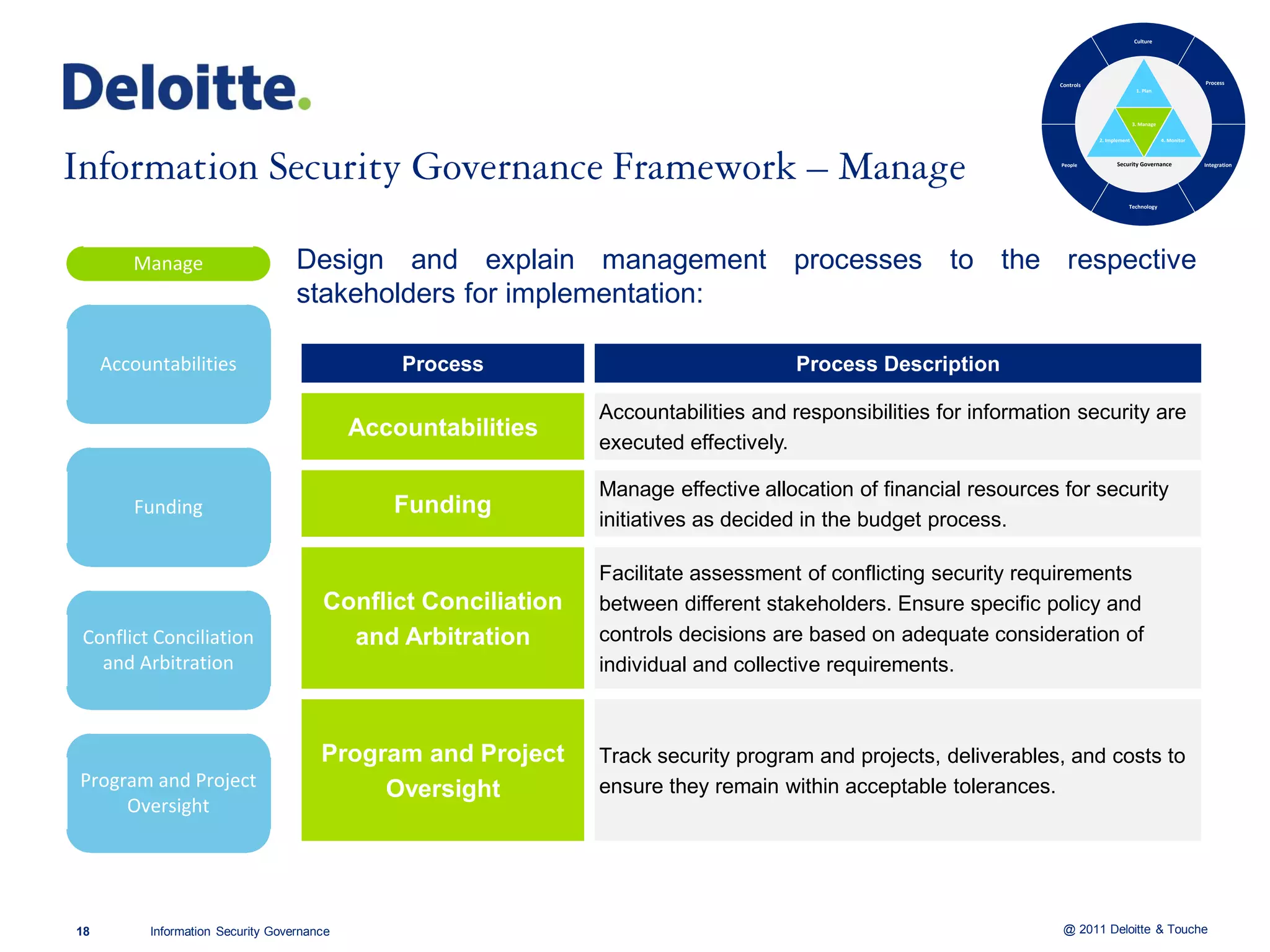
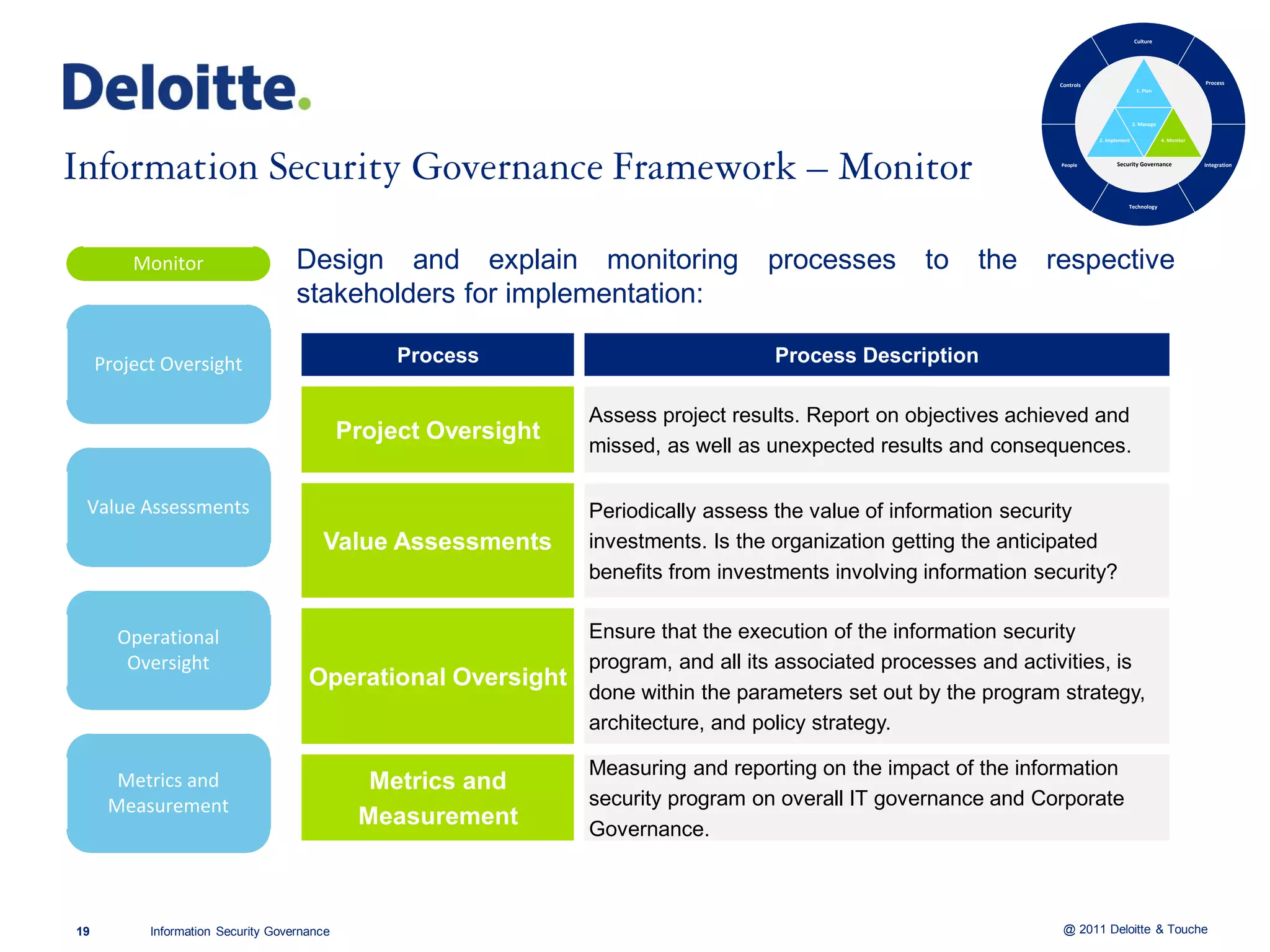
The document discusses information security governance. It notes that there is no single model for organizational structure to ensure information security requirements are met, and there is uncertainty around what information security governance consists of. It also states that information security governance does not function in isolation. The document then provides statistics on how organizations globally and in the Middle East operate in regards to information security governance.