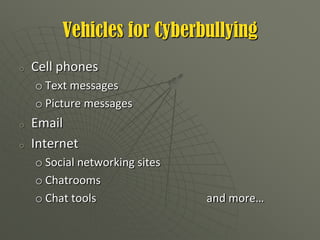
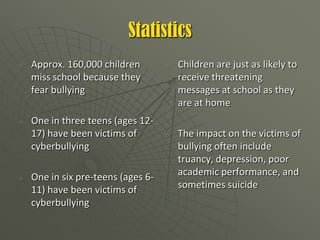
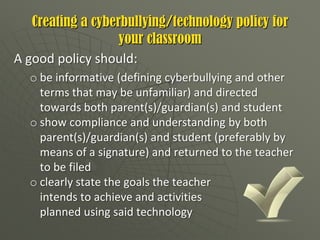
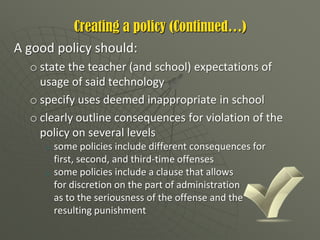
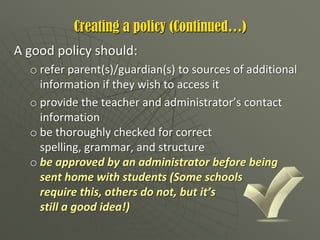
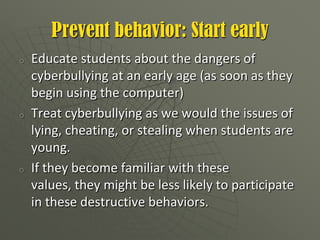
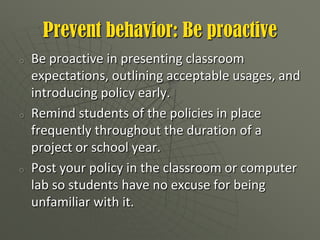
Cyberbullying involves inappropriate use of technology to harass, humiliate, or threaten others. It commonly affects students ages 8-15 and can occur through cell phones, emails, social media, and more. Teachers face challenges in addressing cyberbullying, such as determining what constitutes an offense and how to discipline incidents that occur off-campus but impact school. Creating a clear classroom technology policy that defines expectations and consequences can help prevent cyberbullying issues from arising. Teachers should also actively monitor student technology use and educate students early about cyberbullying dangers.