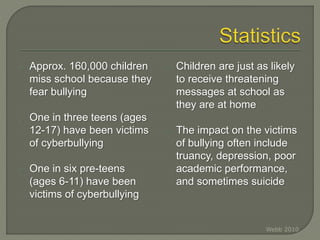
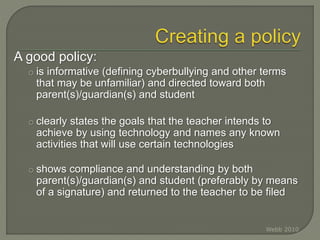
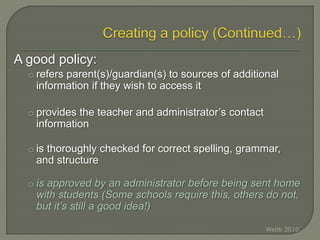
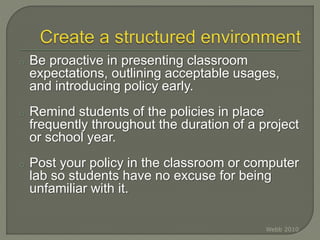
The document discusses ways for teachers to help address cyberbullying among students. It notes that cyberbullying involves inappropriate use of technology to harass or threaten others. Many students ages 8-15 experience cyberbullying through means like cell phones, social media, and more. The impacts on victims can include truancy, depression, and sometimes suicide. While laws and policies aim to address cyberbullying, more research is still needed on effective prevention and intervention methods. The document provides guidance for teachers on creating a classroom technology policy to help prevent cyberbullying and set clear expectations and consequences for inappropriate technology use among students.