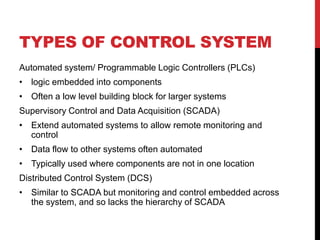
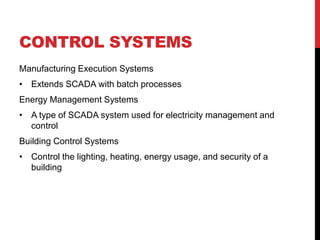
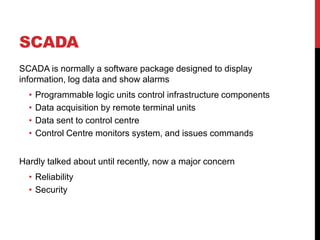
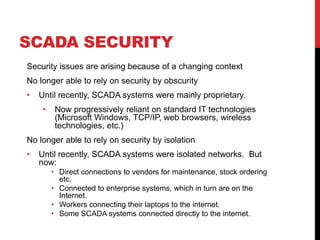
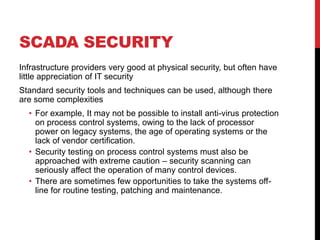
The document discusses critical infrastructure and control systems. It focuses on SCADA systems which are commonly used to monitor and control infrastructure. The document outlines concerns about the security and dependability of SCADA systems as they increasingly rely on standard IT technologies. It then discusses the internet as digital infrastructure and notes concerns about the resilience of the internet, citing studies that found the internet could experience failures without proper protections and understanding of its components. The document recommends better understanding failures, further resilience research, promoting good practices, and greater policymaker engagement.