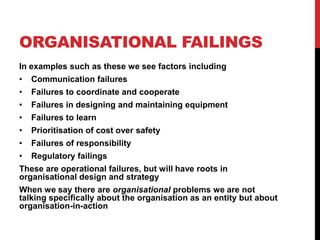
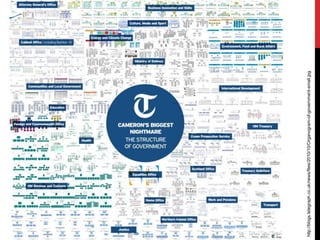
This document discusses organizational factors that can contribute to failures and disasters. It provides examples like the Herald of Free Enterprise ferry accident, Deepwater Horizon oil spill, Space Shuttle disasters, and Bhopal gas tragedy. Common organizational issues identified include communication failures, lack of coordination, cost prioritization over safety, and failures of responsibility. The document also discusses definitions of organizations, how their structure can impact dependability, and relationships between organizational and software structures.



![BHOPAL GAS DISASTER
In 1984, water was mixed with methyl isocyanate at a pesticide
plant in Bhopal, India, resulting in the release of toxic gas. There
were approximately 3000 deaths (in the short-term), and
hundreds of thousands of injuries including blindness, kidney and
liver failure.
According to Shrivastava [1] there were a series of organisational
antecedents to the accident including poor training, poor
motivation, poor manning, and low importance of the plant to its
parent organisation](https://image.slidesharecdn.com/l14-organisationsandfailure2-111207150117-phpapp01/85/CS5032-Lecture-14-Organisations-and-failure-2-15-320.jpg)
![ORGANISATIONAL AND
SOFTWARE STRUCTURE
The information technology used by an organisation often
has a close relation with organisational structure
• IT is often deployed as a part of re-structuring efforts
within organisations
• Many organisations seek to implement enterprise systems
• Enterprise does not necessarily mean organisation, but
can refer to distinctive parts of an organisation, and to
conglomerates of organisations.
• Generic, customisable systems are popular.
• These are not truly generic, but have an accrued
functionality – they do not represent an „ideal‟ organisation.
• Some evidence to show that the less customisation that
takes place, the more successful a deployment will be [6]](https://image.slidesharecdn.com/l14-organisationsandfailure2-111207150117-phpapp01/85/CS5032-Lecture-14-Organisations-and-failure-2-22-320.jpg)
![SOFTWARE STRUCTURE AND
ORGANISATIONAL STRUCTURE
Conway‟s law: organizations that design systems are constrained to
produce systems which are copies of the communication structures
of these organizations.
• “if you have four teams working on a compiler, you‟ll have a four
pass compiler” (Eric Raymond).
• The quality of systems interfaces reflects the quality of
organisational communication (e.g. Mars Orbiter crash)
• A study of Microsoft Vista [2] suggests organisational structure
is a better predictor of the failure proneness of software than
code-based metrics (churn, dependencies, test coverage, etc.).
• The more people who touch the code the lower the quality.
• A large loss of team members affects the knowledge retention and thus quality.
• The more edits to components the higher the instability and lower the quality.
• The lower level is the ownership the better is the quality.
• The more cohesive are the contributors (organizationally) the higher is the quality.
• The more cohesive is the contributions (edits) the higher is the quality.
• The more the diffused contribution to a binary the lower is the quality.
• The more diffused the different organizations contributing code, the lower is the
quality.](https://image.slidesharecdn.com/l14-organisationsandfailure2-111207150117-phpapp01/85/CS5032-Lecture-14-Organisations-and-failure-2-23-320.jpg)
![TESTING AND ORGANISATIONAL
STRUCTURE
Ahonen [3] suggests organisational structure has significant
influence on the quality of testing in an organisation.
Team based development models:
• A more pleasant working atmosphere, but leads to an uneven
and difficult-to-assure testing process.
Interdepartmental model:
• Teams can sometimes end up passing costs to each other,
but testing is easier to manage, and issues can be tracked.
Resource pool based model:
• This can have severe problems on working atmosphere, but
is the most suitable for supporting an effective testing
regime.](https://image.slidesharecdn.com/l14-organisationsandfailure2-111207150117-phpapp01/85/CS5032-Lecture-14-Organisations-and-failure-2-24-320.jpg)
![ORGANISATIONAL
CHANGE
Organisations are not static but change over time
• Organisations often go through periods of restructuring
The goal is not to find the perfect organisational form, but to
manage a changing organisation in a changing context.
Restructuring is necessary because of factors including:
• Growth, Mergers, Changing purpose, Changing
technology, Changing context.
Ciborra [4] argued there is a cycle in organistions between
control and drift.
• Change occurs naturally, and is punctuated by efforts to
regain control](https://image.slidesharecdn.com/l14-organisationsandfailure2-111207150117-phpapp01/85/CS5032-Lecture-14-Organisations-and-failure-2-25-320.jpg)
![From Ciborra [4]](https://image.slidesharecdn.com/l14-organisationsandfailure2-111207150117-phpapp01/85/CS5032-Lecture-14-Organisations-and-failure-2-26-320.jpg)
![ORGANISATIONAL
BOUNDARIES
Boundaries can lead to “silo working”.
• People working in proximity to each other but within
„closed‟ arenas
According to Page [5], Silos occur because of:
• Turf wars
• Budget protection
• Bureaucratic politics
• Ignorance
• Legal reasons
• Technology reasons](https://image.slidesharecdn.com/l14-organisationsandfailure2-111207150117-phpapp01/85/CS5032-Lecture-14-Organisations-and-failure-2-28-320.jpg)
![PROFESSIONALISM
An alternative source of power in work and organisations arises
through professional bodies
• Professional bodies develop around skilled areas of work,
what Abbot [7] describes as Jurisdictions
• Not all areas are able to professionalise. Software
development has had significant problems [7].
Professional bodies also seek to regulate the environments in
which their members work, to ensure they can work effectively.
• To become a member of a profession usually requires some
demonstration of skill
Trades Unions also seek to represent the interests of members
• Unions have been instrumental in the development of
participatory design, and socio-technical approaches](https://image.slidesharecdn.com/l14-organisationsandfailure2-111207150117-phpapp01/85/CS5032-Lecture-14-Organisations-and-failure-2-36-320.jpg)

![LOCAL VARIABILITY
There can be variance across ostensibly equivalent parts of an
organisation
• For example, there is large variation between NHS hospitals,
and even between wards on the same hospital.
• Work is contingent upon local resources and constraints.
• Practices are implemented, emerge and evolve locally.
Organisations will go through periods of standardisation, often
through the deployment of technology
• But at local levels standards will always be interpreted,
“gamed” or perhaps ignored.
• A classic study by Barley [8] found that the deployment of
the same technology in different hospitals led not to further
diversities in their practices.](https://image.slidesharecdn.com/l14-organisationsandfailure2-111207150117-phpapp01/85/CS5032-Lecture-14-Organisations-and-failure-2-38-320.jpg)
![INTER ORGANISATIONAL
RELATIONSHIPS
When organisations collaborate or provide services there will usually
be a formal agreement
• Eg. Contracts, SLAs
However, the ties between organisations need to be stronger than just
having written agreements
• Eg. emergency workers do not just need to fulfill their specified roles
but to work effectively together
• A well known example was Toyota‟s ability to restart production just
days after a supplier of a complex component suffered a catastrophic
fire. [9]
Organisations are sometimes conceptualised in terms of ecosystems
• Formal and informal relations and dependencies exist between
organisations
• Organistions can enter into strategic ecosystems, where they
cooperate with others to supply services or build a market](https://image.slidesharecdn.com/l14-organisationsandfailure2-111207150117-phpapp01/85/CS5032-Lecture-14-Organisations-and-failure-2-43-320.jpg)