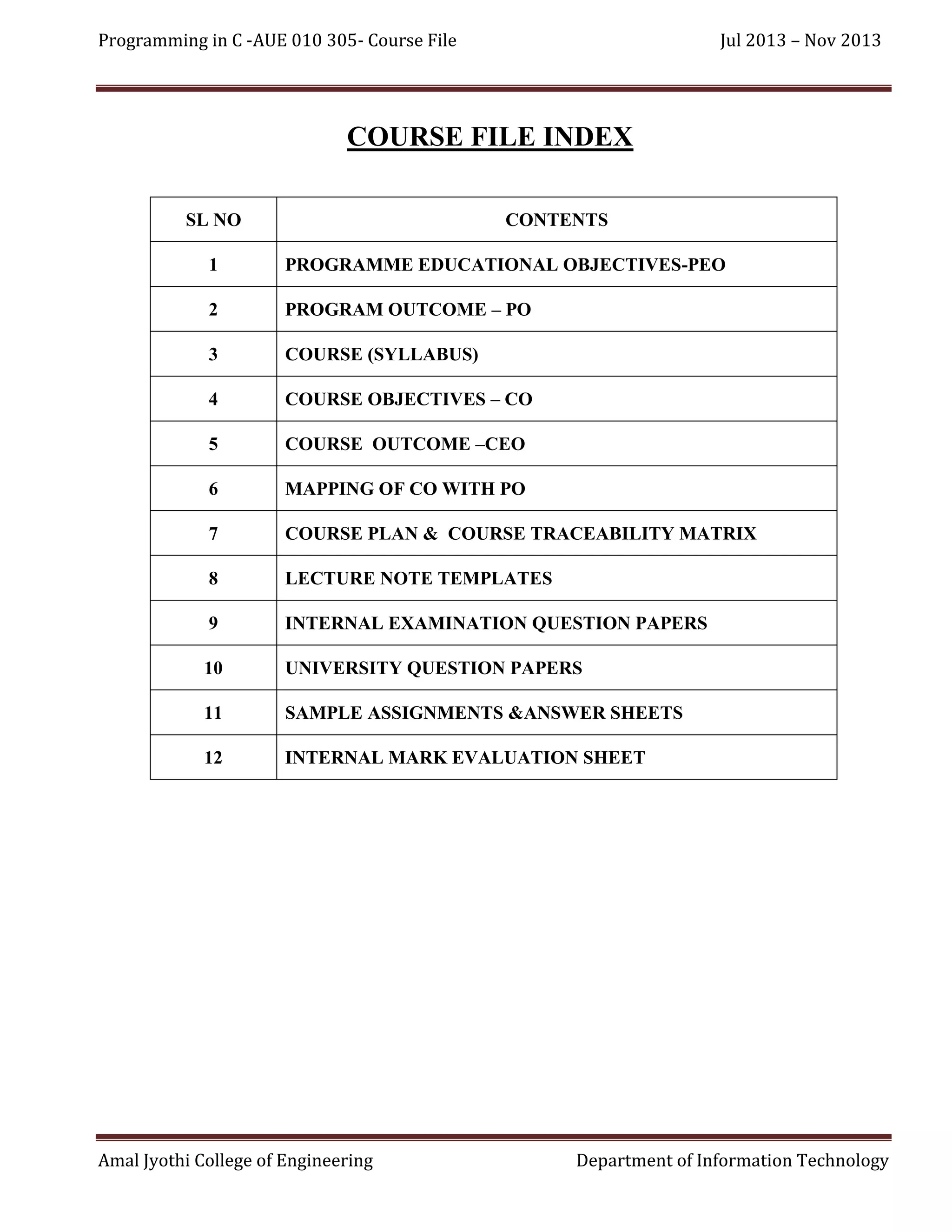
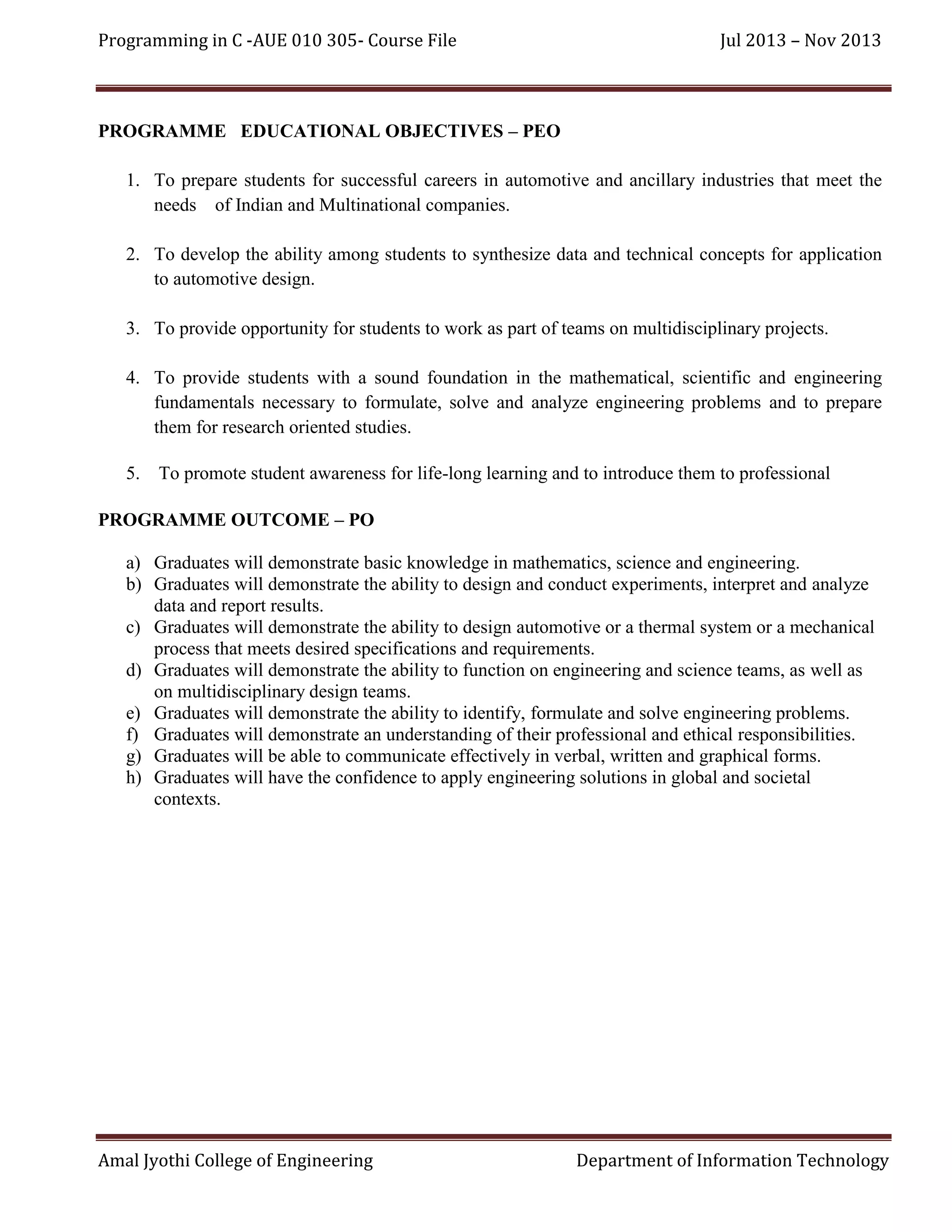
This document provides a course file for the "Programming in C" course offered from July 2013 to November 2013. It includes information on the course objectives, syllabus, lecture schedule, assignments, and assessments. The file also maps the course outcomes to the program outcomes to demonstrate how the course meets the overall program objectives.
![Programming in C -AUE 010 305- Course File
Jul 2013 – Nov 2013
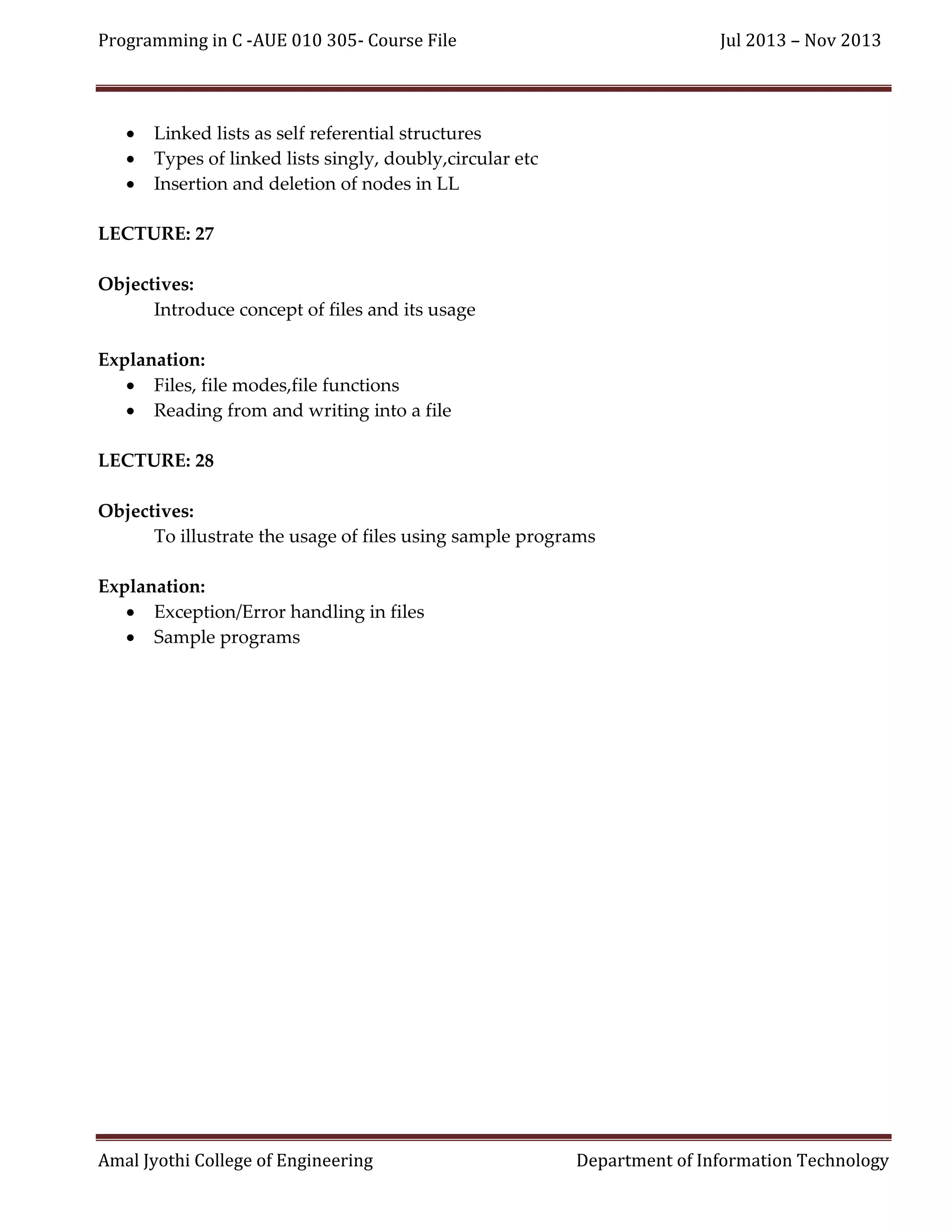
Text Books
1. Bryon S.Gottfried, Programming with C Language.
Reference Books
2. Balaguruswamy, Programming in ANSI C,
3. Deitel, How to Program C
4. Kamthane, Programming with ANSI and Turbo C
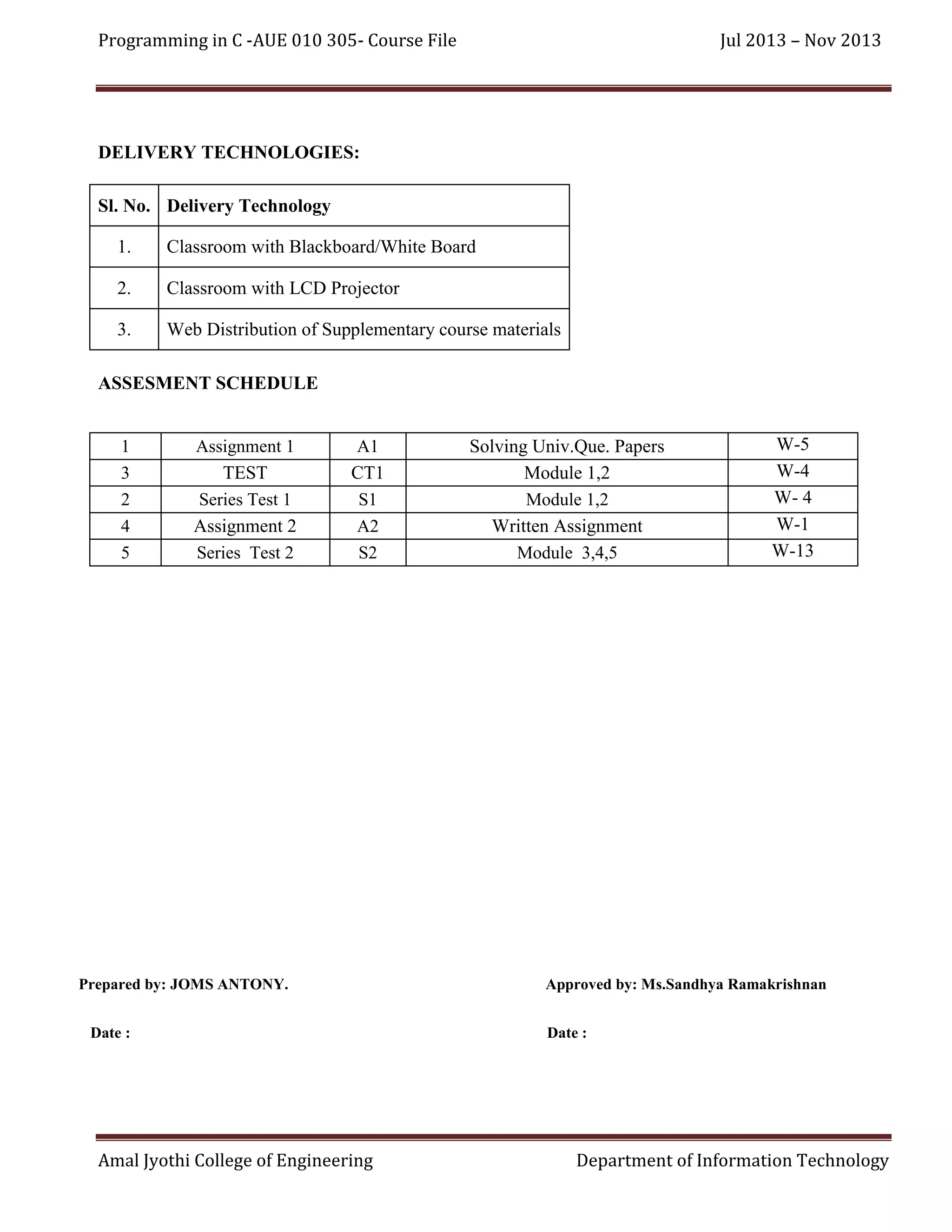
Internal Continuous Assessment (Maximum Marks-50)
60% - Tests (minimum 2)
20% - Assignments (minimum 2) such as home work, problem solving, group discussions,
quiz, literature survey, seminar, term-project, software exercises, etc.
20% - Regularity in the class
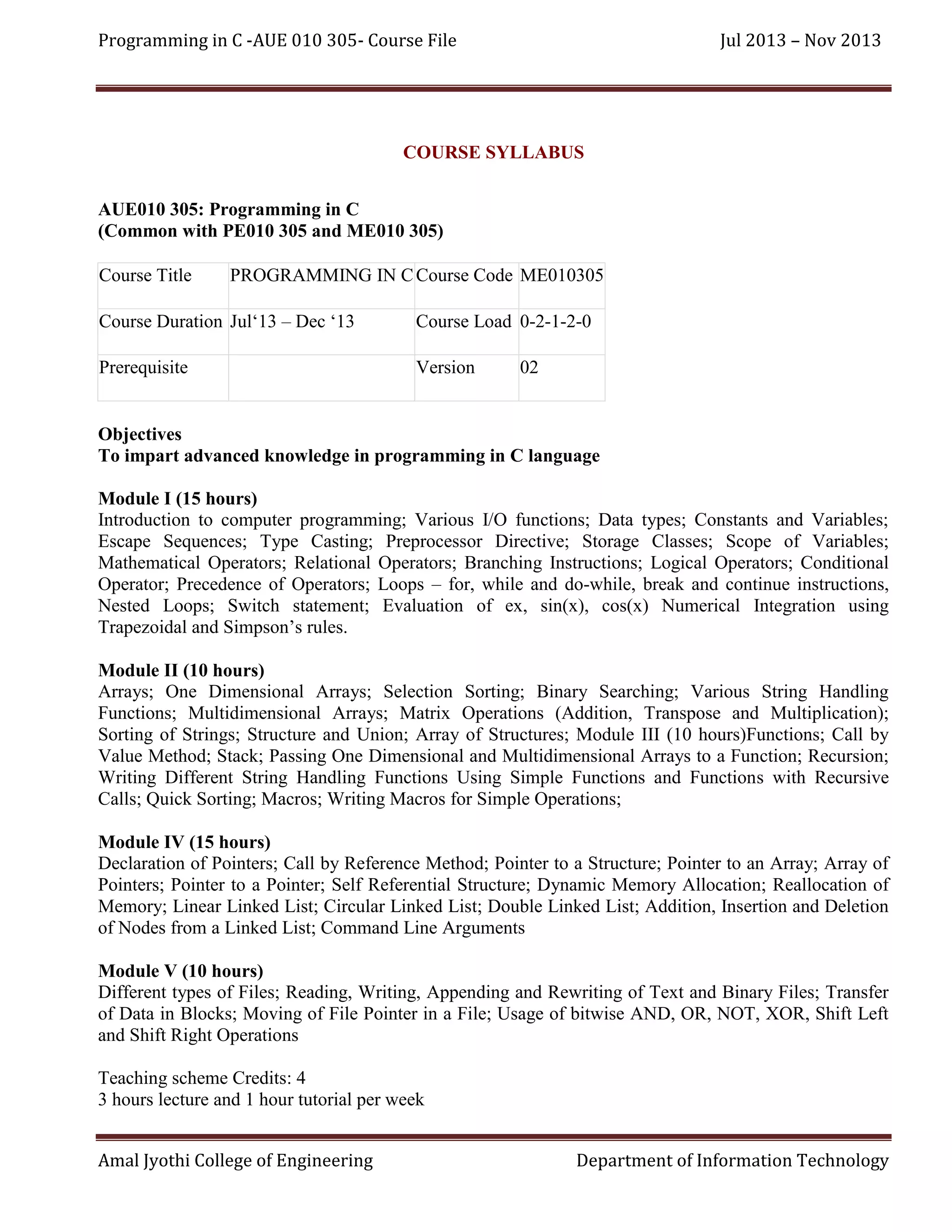
COURSE OBJECTIVES
[CO1] Illustrate the importance of programming and its applications.
[CO2]Provide an insight about problem solving using computers.
[CO3] Illustrate the basic programming approach using C.
[CO4]Impart advanced knowledge in C programming.
COURSE OUTCOME
[CEO1] Able to appreciate the importance of programming.
[CEO2] Able to develop problem solving algorithms and convert them into programs.
[CEO3] Able to appreciate modular(functions) programming approach.
[CEO3] Ability to understand and apply memory references and allocation.
[CEO5] Ability to apply the knowledge of files in different applications.
Amal Jyothi College of Engineering
Department of Information Technology](https://image.slidesharecdn.com/coursefile-lt01-131117112647-phpapp01/75/Course-File-AUE010305-5-2048.jpg)
![Programming in C -AUE 010 305- Course File
Jul 2013 – Nov 2013
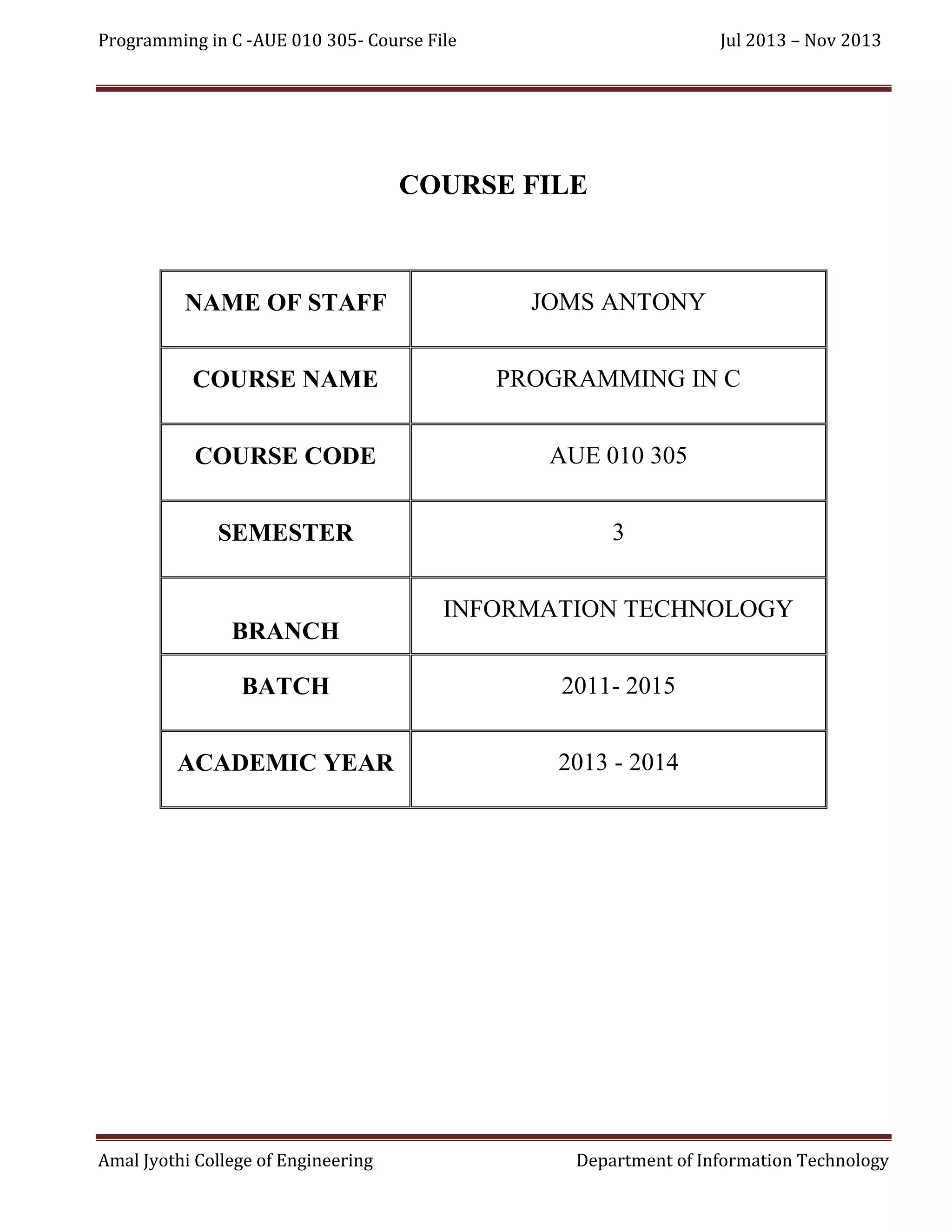
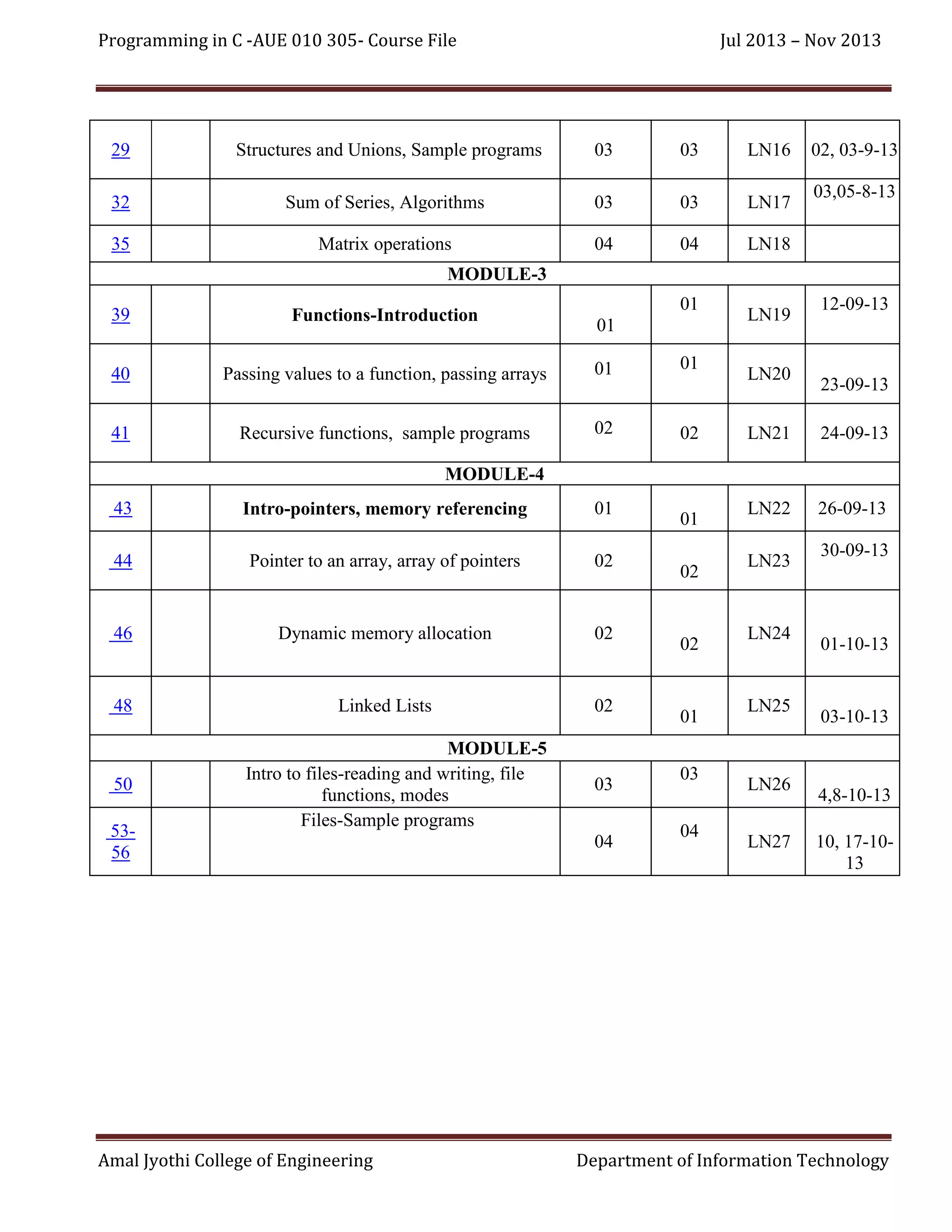
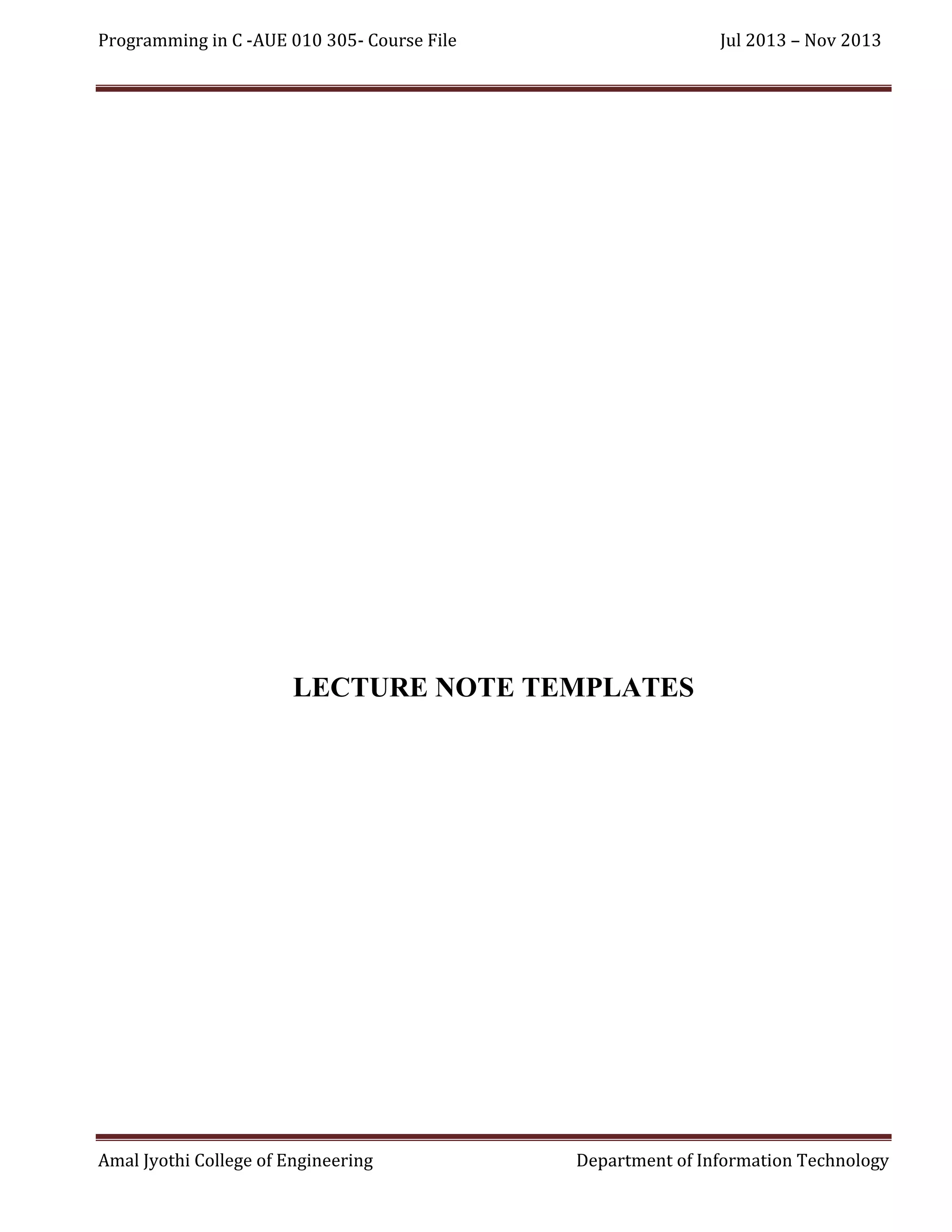
Introduction to pointers
Memory referencing and de-referncing
Usage of * and & operators
Pointer Arithmetic
Sample programs
LECTURE: 23
Objectives:
To introduce the concept pointer to an array and array of pointers
Explanation:
Memory referencing for arrays
Meaning of *(a+i) and a[i]
Array of pointers
Sample programs
LECTURE: 24
Objectives:
To introduce the concept of dynamic memory allocation and its implementation
Explanation:
Effective memory utilization
Dynamic memory allocation function malloc(),calloc(),realloc(),free()
Sample programs
LECTURE: 25
Objectives:
To introduce the concept of linked lists and their usage
Explanation:
Linked lists as self referential structures
Types of linked lists singly, doubly,circular etc
Insertion and deletion of nodes in LL
LECTURE: 26
Objectives:
To introduce the concept of linked lists and their usage
Explanation:
Amal Jyothi College of Engineering
Department of Information Technology](https://image.slidesharecdn.com/coursefile-lt01-131117112647-phpapp01/75/Course-File-AUE010305-16-2048.jpg)