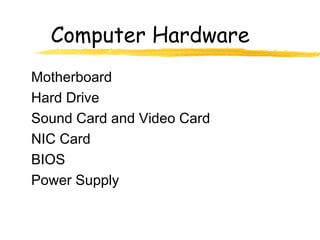
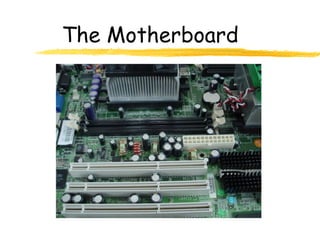
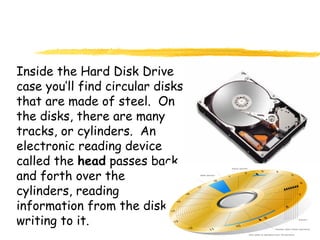
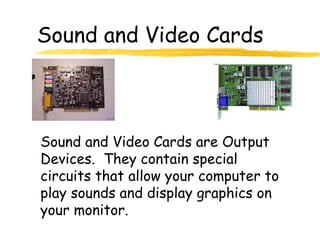
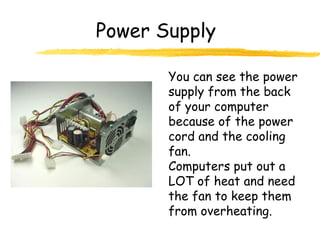
Computer consists of many parts that work together, including the central processing unit (CPU) that acts as the computer's brain. Information is input using devices like keyboards and mice, processed by the CPU using memory components, and output through devices like monitors and printers. The motherboard forms the core of the computer, connecting the CPU and memory chips. Storage devices like hard drives and flash drives hold programs and files on magnetic disks, while other components like video and sound cards manage outputs.