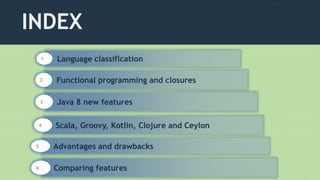
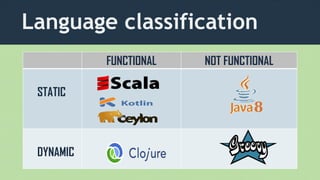
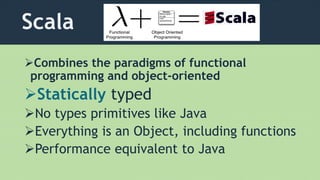
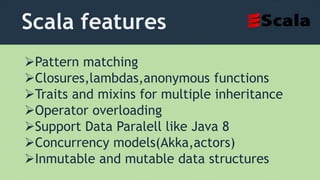
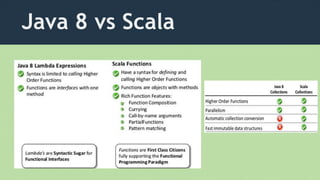
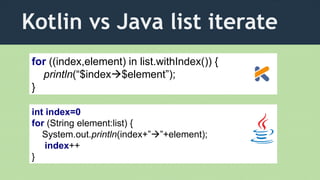
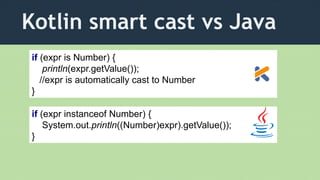
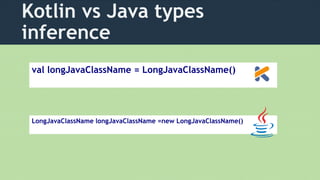
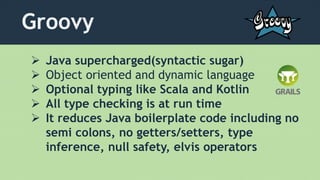
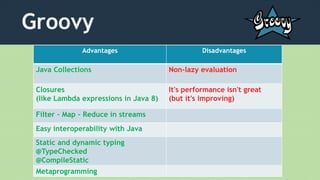
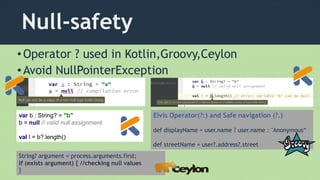
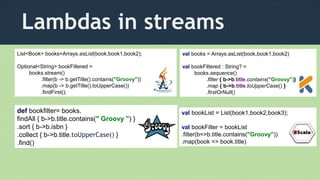
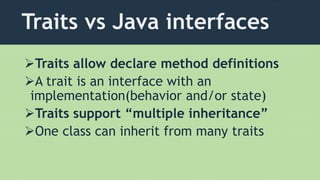
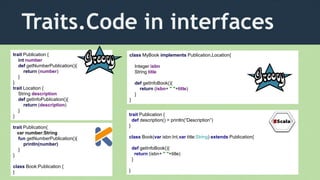
This document compares several JVM languages including Java, Scala, Groovy, Kotlin, Clojure and Ceylon. It discusses their classification as functional or object-oriented, static or dynamic typing. It also summarizes key features of each language such as support for functional programming paradigms, closures, immutable data structures, and parallel processing capabilities. The document provides code examples to illustrate concepts in Scala, Kotlin, and Groovy.

![Filter-Map-Reduce
Book book=new Book(123455,"Beginning Java 8");
Book book1=new Book(3232332,"Java 8 Advanced");
Book book2=new Book(43434343,"Groovy Advanced");
List<Book> books=Arrays.asList(book,book1,book2);
Predicate<Book> condition=(it) -> it.getTitle().contains("Java");
String jsonFormat=books
.stream()
.filter(condition)
.map(Book::toJSON)
.collect(Collectors.joining(", "));
[{isbn:123455,title:'Beginning Java 8'}, {isbn:3232332,title:'Java 8 Advanced'}]](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-8-320.jpg)
![Sequential vs Parallel
books.parallelStream().filter((it) -> it.getTitle().contains("Java")).
forEach((it)->System.out.println(it+" "+Thread.currentThread()));
Book{isbn=3232332, title='Java 8 Advanced'} Thread[main,5,main]
Book{isbn=123455, title='Beginning Java 8'} Thread[main,5,main]
books.stream().filter((it) -> it.getTitle().contains("Java")).
forEach((it)->System.out.println(it+" "+Thread.currentThread()));
Book{isbn=3232332, title='Java 8 Advanced'} Thread[main,5,main]
Book{isbn=123455, title='Beginning Java 8'} Thread[ForkJoinPool.commonPool-
worker-2,5,main]](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-10-320.jpg)
![Scala examples
def factorial(n : Int): Int = n match{
case 0 => 1
case x if x >0 => factorial(n-1) *n
}
val languages = List("Scala", "Groovy", "Clojure", "Kotlin")
val headList = languages.head // Scala
val tailList = languages.tail; //List( "Groovy", "Clojure", "Kotlin")
val empty = languages.isEmpty //false
def orderList(xs: List[String]): List[String] =
if (xs.isEmpty) Nil
else insert(xs.head, isort(xs.tail)
@BeanProperty
Annotation which is read by the Scala
compiler to generate getter and setter
class Bean {
@scala.reflect.BeanProperty
var name: String
}
val someNumbers = List(-11, -10, -5, 0, 5, 10)
someNumbers.filter((x) => x > 0)
someNumbers.filter(_ > 0)
List[Int] = List(5, 10)
scala.collection.immutable](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-13-320.jpg)
![Inmutability in Scala
scala> var languages = Set("Scala", "Kotlin")
languages : scala.collection.immutable.Set[java.lang.String] =
Set(Scala, Kotlin)
scala> languages += "Clojure"
scala> languages
res: scala.collection.immutable.Set[java.lang.String] =
Set(Scala, Kotlin, Clojure)
scala> languages -= " Kotlin "
scala> languages
res: scala.collection.immutable.Set[java.lang.String] =
Set(Scala, Clojure)
• You can add elements in a inmutable collection](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-14-320.jpg)
![Java 8 vs Scala streams
bookList.parallelStream().filter(b -> b.title.equals(”Clojure”))
.collect(Collectors.toList())
bookList.par.filter(_.title == “Clojure”)
bookList.par.filter( b =>b.title == “Clojure”)
val bookFilter = bookList.par.filter(_.title.contains("Groovy"))
.foreach{i=> println(Thread.currentThread) }
Thread[ForkJoinPool-1-worker-3,5,main]
Thread[ForkJoinPool-1-worker-5,5,main]](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-16-320.jpg)
![Kotlin
Higher order functions
• Lambda expressions
• it implicit parameter
val filter = books filter({ b: Book -> b.title.contains(“Kotlin") })
val book = Book(123455, "Beginning Java 8")
val book1 = Book(3232332, "Java 8 Advanced")
val book2 = Book(43434343, “Kotlin Advanced")
val books = Arrays.asList(book, book1,book2)
Filter[Book(isbn=43434343, title=Kotlin Advanced)]
val filter = books filter({ it.contains(“Kotlin") })](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-24-320.jpg)
![Groovy
Closures with lambda
or it implicit parameter
def upper = { s-> s.toUpperCase()}
def upper = {it.toUpperCase()}
Collections
def languages = ["Java":”James
Gosling”, "Scala":”Martin Odersky”,
"Clojure":”Rich Hickey”,
"Ceylon":”Gavin King”,
"Groovy":”James Strachan”]
languages.each { entry -> println}
languages.each { k,v -> println}
Methods as closures with .& operator
def object
object = 2
object = true
object = [1,2,3]
Optional typing](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-30-320.jpg)
![Java Groovy
def languages = ["Java", "Scala", "Clojure",
"Kotlin", "Ceylon","Groovy"]
def filter = languages.stream()
.findAll { it.size()>5 }
.collect { it.toUpperCase()}
.first()
List<String> languages = Arrays.asList("Java",
"Scala", "Clojure", "Kotlin","Ceylon","Groovy");
Optional<String> bookFiltered = languages.stream()
.filter(s -> s.length()>5 )
.map(s -> s.toUpperCase())
.findFirst();](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-35-320.jpg)
![Clojure
Alternate implementations in functions
(defn square-or-multiply
"squares a single argument, multiplies two arguments"
([] 0) # without arguments
([x] (* x x)) # one argument
([x y] (* x y))) # two arguments
List operations
(first '(:scala :groovy :clojure))return scala
(rest '(:scala :groovy :clojure))return all elements excepts the first
(cons :kotlin '(:scala :groovy :clojure))add kotlin to head in the list](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-37-320.jpg)
![Clojure
Sequences
(defn count-down [n]
(if (<= n 0)
'(0)
(cons n (lazy-seq (count-down (dec n))))))
Filter – Map - Reduce
(filter integer? [1 2.71 3.14 5 42]) => (1 5 42)
(map (fn [n] (* n n)) [1 2 3 4 5]) => (1 4 9 16 25)
(reduce + [1 2 3 4]) => 10
user=> (count-down 8)
(8 7 6 5 4 3 2 1 0)](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-38-320.jpg)
![Clojure
Records
(defrecord Book [isbn title])
(def bookList [(Book. 432423 "Clojure")(Book. 534243 "Kotlin")
(Book. 432424 "Groovy")])
(println "count bookList "(count bookList))
(dorun (for [item bookList]
(println (:title item)(:isbn item))))
(println (filter #(= "Clojure" (get % :title)) bookList))
count bookList 3
Clojure 432423
Kotlin 534243
Groovy 432424
(#user.Book{:isbn 432423, :title
Clojure})
(defrecord Object [prop1 propn])](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-39-320.jpg)
![Clojure
Recursive functions with trampoline and memoize
(defn factorial ([x] (trampoline (factorial (dec x) x)))
([x a] (if (<= x 1) a #(factorial (dec x) (*' x a)))))
(def fibonaci
(memoize (fn [n]
(if (< n 2)
n
(+ (fibonaci (dec n))
(fibonaci (dec (dec n))))))))
(time(println (factorial 20)))
(time(println (fibonaci 30)))
"Elapsed time: 0.692549 msecs"
832040
"Elapsed time: 1.263175 msecs"
"Elapsed time: 24.574218 msecs"
832040
"Elapsed time: 118.678434 msecs"
2432902008176640000](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-40-320.jpg)
![Clojure vs Java
Code reducing
(defn blank [str]
(every#? (Character/isWhitespace %)
str))
public class StringUtils {
public static boolean isBlank(String str) {
int strLen;
if (str == null || (strLen = str.length()) == 0) {
return true;
}
for (int i = 0; i < strLen; i++) {
if ((Character.isWhitespace(str.charAt(i)))) {
return true;
}}
return false;
}}](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-42-320.jpg)
![Optional Types
Optional<Object> optional = findObject(id);
//check if Optional object has value
if (optional.isPresent()) {
System.out.println(optional.get());
}
Type safe Option[T] in Scala
New class java.util.Optional](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-49-320.jpg)
![Optional Type in Scala
private val languages = Map(1 -> Language(1, "Java", Some("Gosling")),
2 -> Language(2, "Scala", Some("Odersky")))
def findById(id: Int): Option[Language] = languages.get(id)
def findAll = languages.values
def main(args: Array[String]) {
val language = Optional.findById(1)
if (language.isDefined) {
println(language.get.name)
}
}
val language = Optional.findById(3) None](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-50-320.jpg)
![Optional Type in Scala
val languages =Map("Java"->"Gosling","Scala"->"Odersky")
languages:scala.collection.immutale.Map[java.lang.String,java.lang.String]
languages get "Scala"
Option[java.lang.String] = Some(Odersky)
languages get "Groovy"
Option[java.lang.String] = None](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-51-320.jpg)
![Pattern matching
• Is a generalization of Java switch/case
def generalSize(x: Any) = x match {
case s: String => s.length
case m: Map[_, _] => m.size
case _ => -1
}
scala> generalSize("abc")
res: Int = 3
scala> generalSize(Map(1 -> 'a', 2 -> 'b'))
res: Int = 2
fun fib(n: Int): Int {
return when (n) {
1, 2 -> 1
else -> fib(n - 1) + fib(n - 2)
}
}
fun patternMatching(x:Any) {
when (x) {
is Int -> print(x)
is List<*> ->{print(x.size())}
is String -> print("String")
!is Number -> print("Not even a number")
else -> print("can't do anything")
}
}](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-53-320.jpg)
![Java interoperability
object list extends App {
import java.util.ArrayList
var list : ArrayList[String] = new ArrayList[String]()
list.add("hello")
list.add("world")
println(list)
}
import collection.JavaConversions._
java.util.Arrays.asList(1,2,3).
foreach(i =>println(i))
java.util.Arrays.asList(1,2,3).
filter(_ % 2 ==0)
fun list(source: List<Int>):ArrayList<Int> {
val list = ArrayList<Int>()
for (item in source)
list.add(item)
for (i in 0..source.size() - 1)
list[i] = source[i]
return list
}
(ns clojure-http-server.core
(:require [clojure.string])
(:import (java.net ServerSocket SocketException)
(java.util Date)
(java.io PrintWriter BufferedReader
InputStreamReader BufferedOutputStream)))](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-56-320.jpg)
![Java interoperability
import scala.beans.BeanProperty
class Language(
@BeanProperty var name: String,
@BeanProperty var author: String) {
}
public static void main(String[] args) {
Language l1 = new Language(“Java",”Gosling”);
Language l2 = new Language(“Scala",”Odersky”);
ArrayList<Language> list = new ArrayList<>();
list.add(l1);
list.add(l2);
}](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-57-320.jpg)
![List Partitions
• We can use partition over a list for obtain 2 lists
scala> List(1, 2, 3, 4, 5) partition (_ % 2 == 0)
res: (List[Int], List[Int]) = (List(2, 4),List(1, 3, 5))
// partition the values 1 to 10 into a pair of lists of even and odd numbers
assertEquals(Pair(listOf(2, 4, 6, 8, 10), listOf(1, 3, 5, 7, 9)), (1..10)
.partition{ it % 2 == 0 })](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-58-320.jpg)
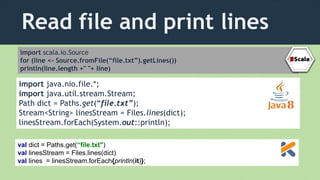
![Read file and print lines
(defn read-file [file]
(with-open [rdr (clojure.java.io/reader file)]
(doseq [line (line-seq rdr)]
(println line))))
(read-file (file “file.txt"))
Files.lines(Paths.get(“file.txt")).forEach{println it};](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-60-320.jpg)
![Performance in recursion
(defn factorial ([x] (trampoline (factorial (dec x) x)))
([x a] (if (<= x 1) a #(factorial (dec x) (*' x a)))))
@TailRecursive
def fact(BigInteger n,acumulator = 1G) {
if (n <2){
acumulator
}else{
fact(n-1,n*acumulator)
}
}
@scala.annotation.tailrec
def factorialrec(fact:BigInt,number:BigInt=1):BigInt = {
if (fact<2) return number
else factorialrec(fact-1,fact*number)
}](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-61-320.jpg)

![Palindrome
(use 'clojure.java.io)
(defn palindrome? [s]
(let [sl (.toLowerCase s)]
(= sl (apply str (reverse sl)))))
(defn find-palindromes[s]
(filter palindrome? (clojure.string/split s #" ")))
fun isPalindrome(s : String) : Boolean {
return s== s.reverse()
}
fun findPalindrome(s:List<String>): List<String>{
return s.filter {isPalindrome(it)}.map {it}
}
def isPalindrome(x:String) = x==x.reverse
def findPalindrome(s:Seq[String]) = s find isPalindrome
def isPalindrome(s) {
def s1 = s.toLowerCase()
s1 == s1.reverse()
}
def findAllPalindrome(list) {
list.findAll{isPalindrome(it)}
}](https://image.slidesharecdn.com/jbcnconf-150628202044-lva1-app6891/85/Comparing-JVM-languages-63-320.jpg)