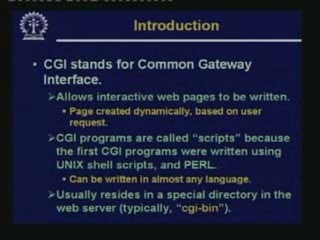
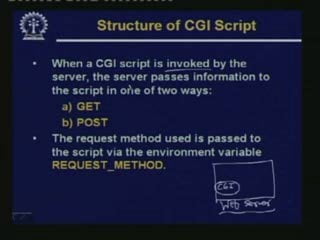
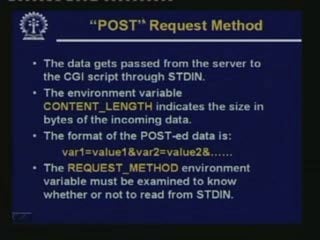
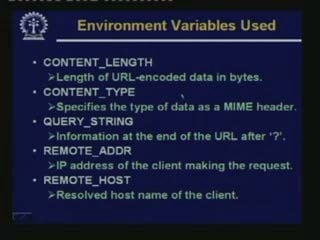
This document discusses CGI programming and HTTP cookies. It provides an overview of CGI and how it is used to send data to servers via the GET and POST methods. It also explains how templates can be used to dynamically generate web pages. Finally, it covers HTTP cookies in detail, including how they are delivered, valid parameters for setting cookies, the different types (persistent and non-persistent), and how they are stored on a user's device.





























![In the template:In the template:
<TMPL_LOOP NAME=EMPLOYEE_INFO><TMPL_LOOP NAME=EMPLOYEE_INFO>
Name: <TMPL_VAR NAME=NAME>Name: <TMPL_VAR NAME=NAME>
Job: <TMPL_VAR NAME=JOB> <br>Job: <TMPL_VAR NAME=JOB> <br>
</TMPL_LOOP></TMPL_LOOP>
In the script:In the script:
$template->param (EMPLOYEE_INFO => [$template->param (EMPLOYEE_INFO => [
{ name => 'Sam', job => 'programmer' },{ name => 'Sam', job => 'programmer' },
{ name => 'Steve', job => 'student' },{ name => 'Steve', job => 'student' },
]]
););
print $template->output();print $template->output();
The output in a browser:The output in a browser:
Name: Sam Job: programmerName: Sam Job: programmer
Name: Steve Job: studentName: Steve Job: student](https://image.slidesharecdn.com/cgifinalunit1-170712030347/85/Common-Gateway-Interface-35-320.jpg)





















