Comcast SD-WAN Network Diagram
•Download as PPTX, PDF•
1 like•726 views
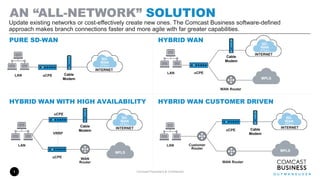
An “All-Network” Solution Update existing networks or cost-effectively create new ones. The Comcast Business software-defined approach makes branch connections faster and more agile with far greater capabilities.
Report
Share
Report
Share
Recommended
Comcast Enterprise | Ethernet Overview

Regardless of how complex your network needs are, Comcast has an Ethernet solution designed to help keep your business applications running smoothly and everyone in your organization connected with one robust and secure network. With a reliable Ethernet connection from Comcast, you’ll exchange data safely and securely, at up to 10Gbps.
Key Policy Considerations When Implementing Next-Generation Firewalls

This presentation examines next-generation firewalls, and provides practical advice on how to effectively and efficiently manage policies in a multi-product and even multi-vendor, defense-in-depth architecture.
By watching this webcast you will learn answers to the following questions:
-What constitutes a next-generation firewall and what problems does it solve?
What are the deployment options for next-generation firewalls?
What do policies in a defense-in-depth architecture look like?
How can you efficiently manage next-generation firewalls AND traditional firewall policies?
And much more
Overlay networks

Overlay networks are virtual networks built on top of existing networks that add additional layers of indirection. There are several types of overlay networks including caching, routing, and security overlays. Two examples of anonymous communication networks are ACN and I2P. I2P uses "garlic routing" which involves layered encryption, bundling multiple messages together, and ElGamal/AES encryption. It has a distributed, self-organizing design and uses short-lived, unidirectional tunnels to provide anonymity through its network.
Using Canary Honeypots for Network Security Monitoring

In this presentation I talk about how honeypots that have more traditionally been used for research purposes can also be used as an effective part of a network security monitoring strategy.
Software Defined Networks

Software Defined Networks
By: Thierry Couture, Consulting Systems Architect
There is currently a lot of buzz around OpenFlow and Software Defined Networks (SDN) in the industry. It would be a mistake to think that these are one and the same. The reality is that the current market conversation has loose semantics mixed in with hyperbole and hearsay that hide the simplicity of SDN behind terms like Openstack, Virtual Overlays, Network Function Virtualization, Orchestration, etc. This session will explain the origins of SDN, establish a basic terminology for SDN concepts, and offer a framework to both understand these trends and distill the applicability of SDN through a use case lens.
Introduction to Software Defined WANs

Introduction to Software Defined WANs, by Alastair Johnson.
A presentation given at APRICOT 2016’s Software Defined Networking session on 24 February 2016.
Maximizing SD-WAN Architecture with Service Chaining - VeloCloud

Enterprises continue to implement or evaluate shifting services which were typically hosted in the branch into the cloud. The reasons include creating a leaner branch, taking advantage of increases in broadband Internet bandwidth and reduced complexity and cost.
This presentation takes a deep dive into the Cloud-Delivered SD-WAN architecture for service chaining. You’ll understanding the architectural differentiation and benefits of this approach and why it offers a superior model for delivering secure, reliable, and high performance service chaining.
Introduction to OpenDaylight & Application Development

This document provides an introduction to OpenDaylight, an open source platform for Software-Defined Networking (SDN). It outlines what OpenDaylight is, its community and releases, the components within OpenDaylight including northbound and southbound interfaces, and some example network applications that can be built on OpenDaylight. It also provides an overview of how to develop applications using OpenDaylight, covering technologies like OSGi, MD-SAL, and the Yang modeling language.
Recommended
Comcast Enterprise | Ethernet Overview

Regardless of how complex your network needs are, Comcast has an Ethernet solution designed to help keep your business applications running smoothly and everyone in your organization connected with one robust and secure network. With a reliable Ethernet connection from Comcast, you’ll exchange data safely and securely, at up to 10Gbps.
Key Policy Considerations When Implementing Next-Generation Firewalls

This presentation examines next-generation firewalls, and provides practical advice on how to effectively and efficiently manage policies in a multi-product and even multi-vendor, defense-in-depth architecture.
By watching this webcast you will learn answers to the following questions:
-What constitutes a next-generation firewall and what problems does it solve?
What are the deployment options for next-generation firewalls?
What do policies in a defense-in-depth architecture look like?
How can you efficiently manage next-generation firewalls AND traditional firewall policies?
And much more
Overlay networks

Overlay networks are virtual networks built on top of existing networks that add additional layers of indirection. There are several types of overlay networks including caching, routing, and security overlays. Two examples of anonymous communication networks are ACN and I2P. I2P uses "garlic routing" which involves layered encryption, bundling multiple messages together, and ElGamal/AES encryption. It has a distributed, self-organizing design and uses short-lived, unidirectional tunnels to provide anonymity through its network.
Using Canary Honeypots for Network Security Monitoring

In this presentation I talk about how honeypots that have more traditionally been used for research purposes can also be used as an effective part of a network security monitoring strategy.
Software Defined Networks

Software Defined Networks
By: Thierry Couture, Consulting Systems Architect
There is currently a lot of buzz around OpenFlow and Software Defined Networks (SDN) in the industry. It would be a mistake to think that these are one and the same. The reality is that the current market conversation has loose semantics mixed in with hyperbole and hearsay that hide the simplicity of SDN behind terms like Openstack, Virtual Overlays, Network Function Virtualization, Orchestration, etc. This session will explain the origins of SDN, establish a basic terminology for SDN concepts, and offer a framework to both understand these trends and distill the applicability of SDN through a use case lens.
Introduction to Software Defined WANs

Introduction to Software Defined WANs, by Alastair Johnson.
A presentation given at APRICOT 2016’s Software Defined Networking session on 24 February 2016.
Maximizing SD-WAN Architecture with Service Chaining - VeloCloud

Enterprises continue to implement or evaluate shifting services which were typically hosted in the branch into the cloud. The reasons include creating a leaner branch, taking advantage of increases in broadband Internet bandwidth and reduced complexity and cost.
This presentation takes a deep dive into the Cloud-Delivered SD-WAN architecture for service chaining. You’ll understanding the architectural differentiation and benefits of this approach and why it offers a superior model for delivering secure, reliable, and high performance service chaining.
Introduction to OpenDaylight & Application Development

This document provides an introduction to OpenDaylight, an open source platform for Software-Defined Networking (SDN). It outlines what OpenDaylight is, its community and releases, the components within OpenDaylight including northbound and southbound interfaces, and some example network applications that can be built on OpenDaylight. It also provides an overview of how to develop applications using OpenDaylight, covering technologies like OSGi, MD-SAL, and the Yang modeling language.
End-to-Eend security with Palo Alto Networks (Onur Kasap, Palo Alto Networks)

Palo Alto Networks - инновационная платформа сетевой безопасности ядром которой является next generation firewall, на базе уникальной, разработанной PA Networks технологии App-ID, обеспечивает безопасность сети на уровне приложений, пользователей и контента с использованием как физической так и виртуальной архитектуры. Решения сетевой защиты PAN соответствуют самым высоким требованиям к сетевой безопасности, как по производительности так и по функциональности, и являются безусловными лидерами отрасли, что подтверждено отчетами Gartner, количеством пользователей и растущим объемом продаж компании.
Waris l2vpn-tutorial

The document is a tutorial on L2VPN (Layer 2 Virtual Private Networks) that provides an agenda covering introductions, concepts, transports, services, pseudowire stitching, QoS, and demonstrations. It defines L2VPN as providing an end-to-end layer 2 connection across a service provider's MPLS or IP core, allowing legacy services like Frame Relay and ATM to be migrated to an MPLS/IP infrastructure. It also describes the need for L2VPN, models like VPLS and VPWS, basic building blocks of pseudowires, and control plane requirements.
wsn routing protocol

This document discusses wireless sensor networks and routing protocols for wireless sensor networks. It defines what a wireless sensor network is and its key characteristics. It then discusses objectives like understanding ad hoc network basics and various routing protocols. It covers topics like the differences between WSNs and ad hoc networks, what a network simulator is and reasons for using NS2, various routing techniques like flooding, gossiping, and hierarchical routing. It also discusses routing challenges, wireless nodes, packet transmission, applications and the future scope of WSNs.
Subscriber Traffic & Policy Management (BNG) on the ASR9000 & ASR1000

This presentation discusses the next wave of broadband, ISG overview, ASR 1k as BNG/ISG and ASR 9k as BNG.
Access Network Evolution 

The document provides housekeeping notes for a Cisco Connect Toronto 2015 session. It reminds attendees to silence electronic devices, provides information on how to provide feedback and enter a prize drawing, and advertises the Cisco dCloud platform and Cisco Spark collaboration app. It also includes an agenda for the session on access network evolution, next generation EPN architecture, network services evolution, and SDN evolution.
Implementing cisco mpls

This document provides an overview and student guide for the "Implementing Cisco MPLS (MPLS) Version 2.2" course. It introduces basic MPLS concepts including the MPLS architecture, labels, label stacks, and applications such as MPLS VPNs and traffic engineering. It also covers frame-mode MPLS implementation on Cisco IOS platforms, including configuration, monitoring, and troubleshooting tasks. Finally, it discusses MPLS VPN technology in depth, including the MPLS VPN architecture, routing model, and packet forwarding mechanisms.
Presentation

The document discusses recent trends in using artificial neural networks (ANNs) for analog circuit design. It provides an introduction to analog design flows and challenges. ANNs can help automate analog circuit sizing and placement tasks. The document reviews literature on using ANNs for tasks like sizing circuits for different technologies and optimizing parameters. In conclusion, ANNs show promise for reducing analog design time and efforts by training on previous simulation data to optimize circuits.
Vlan 

VLANs logically segment LANs into broadcast domains by using switches to assign ports and their attached devices to VLAN groups based on their MAC address, IP subnet, or switch port. This allows devices that are physically located on different floors or buildings to belong to the same logical LAN segment while preventing Layer 2 broadcasts from crossing VLAN boundaries. VLAN trunk links between switches allow multiple VLANs to be transmitted over the same physical link.
Introduction to Mobile Ad hoc Networks

Introduction
Applications
Challenges
Medium Access Control
Routing
- Proactive routing protocols
- Reactive routing protocols
Getting the most out of the aruba policy enforcement firewall

Getting the most out of the aruba policy enforcement firewallAruba, a Hewlett Packard Enterprise company
In this day and age, it's probably a good idea to get your WLAN ready for voice and video. And it's also a good idea to classify and prioritize web applications based on policies you set. Protecting your mobile devices and network infrastructure against outside or inside attacks needs to be part of the plan, too. Join to us to learn more about these and other functions of Aruba's policy enforcement firewall integrated to its access points, switches, and controllers.NFV +SDN (Network Function Virtualization)

NFV +SDN
(Network Function Virtualization + Software Defined Networking)
- What, Why and When NFV and SDN?
- Basic concepts and definition of NFV, SDN.
- Benefits of NFV.
- NFV Architecture
[cb22] Tales of 5G hacking by Karsten Nohl![[cb22] Tales of 5G hacking by Karsten Nohl](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[cb22] Tales of 5G hacking by Karsten Nohl](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
An expert in mobile network security provided a summary of hacking 5G networks. Some key points include:
1) Standard IT security techniques uncovered issues when applied to upgraded legacy 4G networks, such as unpatched operating systems, weak configurations, and lack of encryption.
2) Future 5G networks introduce new security risks due to increased complexity from virtualization and automation layers, as well as a continuously evolving attack surface extending into cloud infrastructure.
3) Red team exercises show that hacking mobile networks has become a multi-step process, where initial access through one vulnerability can enable lateral movement and privilege escalation to compromise critical systems or customer data.
Mobile Transport Evolution with Unified MPLS

Mobile Service Providers are seeing unprecedented challenges in relation to their Transport architectures with the 3GPP evolution towards IP based Node Bs, LTE (Long Term Evolution) and LTE-Advanced. This presentation will initially discuss the network migration trends and factors that are changing how mobile networks are evolving. A description is provided on Unified MPLS and the current issues that need to be fixed and how this architecture addresses this. A more detailed analysis will then examine the options available for transporting GSM/2G, UMTS/3G traffic and IP/Ethernet Node B deployments and some of factors that need consideration like scalability, resiliency and security. Finally, there is a detailed description of the LTE/LTE - A evolution and the feature requirements made on the transport network. There will be detailed analysis of different LTE models and also some technical enhancements and proposals considered for the implementation of LTE in a Unified MPLS environment.
Software-Defined WAN: A Real World Success Story

The document discusses a case study of MWH Global implementing a software-defined WAN with Cisco and Glue Networks. MWH Global had challenges with provisioning remote sites, operational complexity, and high WAN costs. Using Cisco's software-defined WAN technology and Glue Network's orchestration platform, MWH Global saw benefits like 10-15 times more bandwidth, significant cost savings, and faster deployment of remote sites. The solution provided flexibility, resiliency and automation to simplify their network while reducing costs.
Security Issues in MANET

This presentation covers Security Issues in Mobile Adhoc Network in brief, highlighting various attacks such as Sleep Deprivation, Wormhole, Blackhole and Eavesdropping in particulars.
Network Address Translation (NAT)

Network address translation (NAT) is a method of remapping one IP address space into another by modifying network address information in Internet Protocol (IP) datagram packet headers while they are in transit across a traffic routing device.
Understanding Cisco Next Generation SD-WAN Solution

The document discusses Cisco's next generation SD-WAN solution which includes four main planes - orchestration, control, data, and management. The control plane is managed by Cisco vSmart controllers which facilitate fabric discovery, distribute policies to vEdge routers, and implement control plane policies. The data plane consists of Cisco vEdge routers which provide secure connectivity and implement data and application-aware routing policies. The solution offers a single pane of glass management system through Cisco vManage and provides analytics through Cisco vAnalytics.
F5 Solutions for Service Providers

Presentation of Bart Salaets, Solution Architect, EMEA, F5 Networks at the conference F5 Agility Kyiv (27/11/2014)
Tutorial WiFi driver code - Opening Nuts and Bolts of Linux WiFi Subsystem

While we understand the complex interplay of OSI layers, in theory, in practice understanding their implementation is a non-trivial task. The implementation details that enables a network interface card to communicate with its peers are oblivious to the end-users. Developers venturing into this domain for the first time often find it hard to find relevant tutorials that enable them to understand these implementation details. The aim of this talk is to provide an overview of WiFi Subsystem implemented in the Linux operating system. Specifically, this talk will explain the sequence of events that occur from application layer till physical layer when a connection is established over WiFi. After this talk, the audience will understand
(1) the bird's eye view of Linux WiFi Subsystem,
(2) what happens in an operating system when a WiFi card is plugged-in,
(3) how is a packet received/transmitted from physical layer to operating system kernel and vice-versa,
(4) brief overview of code structure of open-source drivers, and lastly
(5) important pointers to kick start driver code modifications.
Video Available here: https://www.youtube.com/watch?v=pa1oEyc7Dm0
Security in WSN

1) Wireless sensor networks consist of hundreds or thousands of low-cost, low-power sensor nodes deployed to monitor environments. They require security to protect data confidentiality, integrity, and availability given their resource constraints and vulnerability to physical attacks.
2) Standard approaches to achieve security include encrypting data for confidentiality, using protocols like uTESLA for integrity and time synchronization for freshness. However, sensor nodes face obstacles like limited memory, energy constraints, and unreliable communication.
3) Wireless sensor networks are susceptible to various network layer attacks like spoofing, selective forwarding, sinkhole attacks, Sybil attacks, and wormholes. Countermeasures include link layer security, geographic routing, multi-path routing, and authentication.
Comcast LAYER 2 VS. MPLS

• Eliminates the need for QoS as service
• No coordination needed to make any LAN or WAN changes.
• Voice and Data don’t share bandwidth. Each has their own separate connection.
• Simplified flat network topology
• We deliver 1 GIG of Bandwidth to each location. We rate limit based on your subscribed speed.
• Easily Scalable
• More cost Effective
Hybrid SD-WAN...

Businesses are increasingly dependent on cloud resources and mobile access for employees, which legacy networks like MPLS struggle to support due to limited bandwidth and high costs of upgrading. Software-defined wide area networking (SD-WAN) provides a more flexible, affordable alternative that leverages widely available broadband internet connections. A hybrid SD-WAN solution allows businesses to incrementally transition to SD-WAN while maintaining their existing MPLS network, routing traffic dynamically between both networks. Comcast Business' hybrid SD-WAN works with MPLS networks and supports connecting multiple broadband internet connections from different providers for increased reliability and performance monitoring.
More Related Content
What's hot
End-to-Eend security with Palo Alto Networks (Onur Kasap, Palo Alto Networks)

Palo Alto Networks - инновационная платформа сетевой безопасности ядром которой является next generation firewall, на базе уникальной, разработанной PA Networks технологии App-ID, обеспечивает безопасность сети на уровне приложений, пользователей и контента с использованием как физической так и виртуальной архитектуры. Решения сетевой защиты PAN соответствуют самым высоким требованиям к сетевой безопасности, как по производительности так и по функциональности, и являются безусловными лидерами отрасли, что подтверждено отчетами Gartner, количеством пользователей и растущим объемом продаж компании.
Waris l2vpn-tutorial

The document is a tutorial on L2VPN (Layer 2 Virtual Private Networks) that provides an agenda covering introductions, concepts, transports, services, pseudowire stitching, QoS, and demonstrations. It defines L2VPN as providing an end-to-end layer 2 connection across a service provider's MPLS or IP core, allowing legacy services like Frame Relay and ATM to be migrated to an MPLS/IP infrastructure. It also describes the need for L2VPN, models like VPLS and VPWS, basic building blocks of pseudowires, and control plane requirements.
wsn routing protocol

This document discusses wireless sensor networks and routing protocols for wireless sensor networks. It defines what a wireless sensor network is and its key characteristics. It then discusses objectives like understanding ad hoc network basics and various routing protocols. It covers topics like the differences between WSNs and ad hoc networks, what a network simulator is and reasons for using NS2, various routing techniques like flooding, gossiping, and hierarchical routing. It also discusses routing challenges, wireless nodes, packet transmission, applications and the future scope of WSNs.
Subscriber Traffic & Policy Management (BNG) on the ASR9000 & ASR1000

This presentation discusses the next wave of broadband, ISG overview, ASR 1k as BNG/ISG and ASR 9k as BNG.
Access Network Evolution 

The document provides housekeeping notes for a Cisco Connect Toronto 2015 session. It reminds attendees to silence electronic devices, provides information on how to provide feedback and enter a prize drawing, and advertises the Cisco dCloud platform and Cisco Spark collaboration app. It also includes an agenda for the session on access network evolution, next generation EPN architecture, network services evolution, and SDN evolution.
Implementing cisco mpls

This document provides an overview and student guide for the "Implementing Cisco MPLS (MPLS) Version 2.2" course. It introduces basic MPLS concepts including the MPLS architecture, labels, label stacks, and applications such as MPLS VPNs and traffic engineering. It also covers frame-mode MPLS implementation on Cisco IOS platforms, including configuration, monitoring, and troubleshooting tasks. Finally, it discusses MPLS VPN technology in depth, including the MPLS VPN architecture, routing model, and packet forwarding mechanisms.
Presentation

The document discusses recent trends in using artificial neural networks (ANNs) for analog circuit design. It provides an introduction to analog design flows and challenges. ANNs can help automate analog circuit sizing and placement tasks. The document reviews literature on using ANNs for tasks like sizing circuits for different technologies and optimizing parameters. In conclusion, ANNs show promise for reducing analog design time and efforts by training on previous simulation data to optimize circuits.
Vlan 

VLANs logically segment LANs into broadcast domains by using switches to assign ports and their attached devices to VLAN groups based on their MAC address, IP subnet, or switch port. This allows devices that are physically located on different floors or buildings to belong to the same logical LAN segment while preventing Layer 2 broadcasts from crossing VLAN boundaries. VLAN trunk links between switches allow multiple VLANs to be transmitted over the same physical link.
Introduction to Mobile Ad hoc Networks

Introduction
Applications
Challenges
Medium Access Control
Routing
- Proactive routing protocols
- Reactive routing protocols
Getting the most out of the aruba policy enforcement firewall

Getting the most out of the aruba policy enforcement firewallAruba, a Hewlett Packard Enterprise company
In this day and age, it's probably a good idea to get your WLAN ready for voice and video. And it's also a good idea to classify and prioritize web applications based on policies you set. Protecting your mobile devices and network infrastructure against outside or inside attacks needs to be part of the plan, too. Join to us to learn more about these and other functions of Aruba's policy enforcement firewall integrated to its access points, switches, and controllers.NFV +SDN (Network Function Virtualization)

NFV +SDN
(Network Function Virtualization + Software Defined Networking)
- What, Why and When NFV and SDN?
- Basic concepts and definition of NFV, SDN.
- Benefits of NFV.
- NFV Architecture
[cb22] Tales of 5G hacking by Karsten Nohl![[cb22] Tales of 5G hacking by Karsten Nohl](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[cb22] Tales of 5G hacking by Karsten Nohl](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
An expert in mobile network security provided a summary of hacking 5G networks. Some key points include:
1) Standard IT security techniques uncovered issues when applied to upgraded legacy 4G networks, such as unpatched operating systems, weak configurations, and lack of encryption.
2) Future 5G networks introduce new security risks due to increased complexity from virtualization and automation layers, as well as a continuously evolving attack surface extending into cloud infrastructure.
3) Red team exercises show that hacking mobile networks has become a multi-step process, where initial access through one vulnerability can enable lateral movement and privilege escalation to compromise critical systems or customer data.
Mobile Transport Evolution with Unified MPLS

Mobile Service Providers are seeing unprecedented challenges in relation to their Transport architectures with the 3GPP evolution towards IP based Node Bs, LTE (Long Term Evolution) and LTE-Advanced. This presentation will initially discuss the network migration trends and factors that are changing how mobile networks are evolving. A description is provided on Unified MPLS and the current issues that need to be fixed and how this architecture addresses this. A more detailed analysis will then examine the options available for transporting GSM/2G, UMTS/3G traffic and IP/Ethernet Node B deployments and some of factors that need consideration like scalability, resiliency and security. Finally, there is a detailed description of the LTE/LTE - A evolution and the feature requirements made on the transport network. There will be detailed analysis of different LTE models and also some technical enhancements and proposals considered for the implementation of LTE in a Unified MPLS environment.
Software-Defined WAN: A Real World Success Story

The document discusses a case study of MWH Global implementing a software-defined WAN with Cisco and Glue Networks. MWH Global had challenges with provisioning remote sites, operational complexity, and high WAN costs. Using Cisco's software-defined WAN technology and Glue Network's orchestration platform, MWH Global saw benefits like 10-15 times more bandwidth, significant cost savings, and faster deployment of remote sites. The solution provided flexibility, resiliency and automation to simplify their network while reducing costs.
Security Issues in MANET

This presentation covers Security Issues in Mobile Adhoc Network in brief, highlighting various attacks such as Sleep Deprivation, Wormhole, Blackhole and Eavesdropping in particulars.
Network Address Translation (NAT)

Network address translation (NAT) is a method of remapping one IP address space into another by modifying network address information in Internet Protocol (IP) datagram packet headers while they are in transit across a traffic routing device.
Understanding Cisco Next Generation SD-WAN Solution

The document discusses Cisco's next generation SD-WAN solution which includes four main planes - orchestration, control, data, and management. The control plane is managed by Cisco vSmart controllers which facilitate fabric discovery, distribute policies to vEdge routers, and implement control plane policies. The data plane consists of Cisco vEdge routers which provide secure connectivity and implement data and application-aware routing policies. The solution offers a single pane of glass management system through Cisco vManage and provides analytics through Cisco vAnalytics.
F5 Solutions for Service Providers

Presentation of Bart Salaets, Solution Architect, EMEA, F5 Networks at the conference F5 Agility Kyiv (27/11/2014)
Tutorial WiFi driver code - Opening Nuts and Bolts of Linux WiFi Subsystem

While we understand the complex interplay of OSI layers, in theory, in practice understanding their implementation is a non-trivial task. The implementation details that enables a network interface card to communicate with its peers are oblivious to the end-users. Developers venturing into this domain for the first time often find it hard to find relevant tutorials that enable them to understand these implementation details. The aim of this talk is to provide an overview of WiFi Subsystem implemented in the Linux operating system. Specifically, this talk will explain the sequence of events that occur from application layer till physical layer when a connection is established over WiFi. After this talk, the audience will understand
(1) the bird's eye view of Linux WiFi Subsystem,
(2) what happens in an operating system when a WiFi card is plugged-in,
(3) how is a packet received/transmitted from physical layer to operating system kernel and vice-versa,
(4) brief overview of code structure of open-source drivers, and lastly
(5) important pointers to kick start driver code modifications.
Video Available here: https://www.youtube.com/watch?v=pa1oEyc7Dm0
Security in WSN

1) Wireless sensor networks consist of hundreds or thousands of low-cost, low-power sensor nodes deployed to monitor environments. They require security to protect data confidentiality, integrity, and availability given their resource constraints and vulnerability to physical attacks.
2) Standard approaches to achieve security include encrypting data for confidentiality, using protocols like uTESLA for integrity and time synchronization for freshness. However, sensor nodes face obstacles like limited memory, energy constraints, and unreliable communication.
3) Wireless sensor networks are susceptible to various network layer attacks like spoofing, selective forwarding, sinkhole attacks, Sybil attacks, and wormholes. Countermeasures include link layer security, geographic routing, multi-path routing, and authentication.
What's hot (20)
End-to-Eend security with Palo Alto Networks (Onur Kasap, Palo Alto Networks)

End-to-Eend security with Palo Alto Networks (Onur Kasap, Palo Alto Networks)
Subscriber Traffic & Policy Management (BNG) on the ASR9000 & ASR1000

Subscriber Traffic & Policy Management (BNG) on the ASR9000 & ASR1000
Getting the most out of the aruba policy enforcement firewall

Getting the most out of the aruba policy enforcement firewall
Understanding Cisco Next Generation SD-WAN Solution

Understanding Cisco Next Generation SD-WAN Solution
Tutorial WiFi driver code - Opening Nuts and Bolts of Linux WiFi Subsystem

Tutorial WiFi driver code - Opening Nuts and Bolts of Linux WiFi Subsystem
More from Mallory Zemelis
Comcast LAYER 2 VS. MPLS

• Eliminates the need for QoS as service
• No coordination needed to make any LAN or WAN changes.
• Voice and Data don’t share bandwidth. Each has their own separate connection.
• Simplified flat network topology
• We deliver 1 GIG of Bandwidth to each location. We rate limit based on your subscribed speed.
• Easily Scalable
• More cost Effective
Hybrid SD-WAN...

Businesses are increasingly dependent on cloud resources and mobile access for employees, which legacy networks like MPLS struggle to support due to limited bandwidth and high costs of upgrading. Software-defined wide area networking (SD-WAN) provides a more flexible, affordable alternative that leverages widely available broadband internet connections. A hybrid SD-WAN solution allows businesses to incrementally transition to SD-WAN while maintaining their existing MPLS network, routing traffic dynamically between both networks. Comcast Business' hybrid SD-WAN works with MPLS networks and supports connecting multiple broadband internet connections from different providers for increased reliability and performance monitoring.
Sd wan 

SD-WAN brings today's Software Defined Networking concepts and principles to the world of Wide Area Networks (WAN) allowing IT Managers and Network Operators to provision, manage and upgrade services and network functions (Routing, Security, Threat Management, etc.) in a more agile and efficient way by:
Tightly integrating a massively scalable set of network functions for ease of operations and management
Virtualizing key network functions at the customer premise
Routing functions
VPN (securely encapsulating customer data)
Internet Security and Firewall
Focusing on real-time visibility, analytics and configurability
Features include application based routing and local internet access
Can support load balancing/failover between Comcast connection and customer’s existing network
Supports multiple WAN topologies
Any-to-Any
Hub/Spoke
Using the Public Internet as the underlying transport
Comcast Business Internet
Comcast Ethernet Dedicated Internet
Off-Net partner broadband
Replacing dedicated customer premise equipment with a Comcast owned/managed universal CPE (uCPE) deployed at each customer site
Across the US
Transforming the Enerprise with SD-WAN

As business IT models expand to include distributed locations and cloud resources, software-defined networking has emerged as the enabling platform
SDN FOR THE FINANCIAL INDUSTRY

The financial services industry is increasingly at a crossroads. Faced with mounting pressure from external forces, such a competition from FinTech companies and a more demanding client base, banks and financial services firms are working to become more customer-centric in their approach to business. However, the need to keep sensitive customer and business information secure and ensure compliance with government regulations can stymie those efforts
GETTING YOUR BUSINESS ULTRA-CONNECTED

Having secure and consistent connectivity allows Ultra-Connected companies to offer services across a wider footprint and a greater breadth of portfolio. For this reason, more large enterprises are turning to Comcast Business for advanced network services. With one of the nation’s largest IP
networks, and Ethernet services accessible to more than two
million buildings, Comcast Business helps companies scale
quickly, easily, and incrementally up to 100 Gbps.
Ethernet Services for Multi-Site Connectivity

Comcast Enterprise Solutions offer a complete range of MEF certified business Ethernet services including Ethernet Private Line, Ethernet Virtual Private Line, Ethernet Network Service (MEF E-LAN compliant) and Ethernet Dedicated Internet. Each service is offered with a 10 Mbps, 100 Mbps, 1 Gbps, or 10 Gbps Ethernet port in customer-selectable bandwidth increments ranging from 2 Mbps to 10 Gbps and beyond.
Comcast wide area ethernet

Comcast offers wide area Ethernet services across more than 100 metro areas in the United States, including the top 20 markets. Their national IP backbone provides comprehensive inter-market connectivity. Services are available at the metro, regional, and continental levels, with metro connectivity within a single Comcast metro area, regional connecting two metros in a region, and continental spanning two or more regions. They provide flexible, scalable solutions from 1 Mbps to 10 Gbps and enterprise-level support.
Ethernet over hybrid fiber coax

Comcast offers several Ethernet service types over their Hybrid Fiber Coax network including Ethernet Dedicated Internet, Ethernet Private Line, and Ethernet Virtual Private Line. Ethernet over Hybrid Fiber Coax provides businesses with Ethernet connectivity at speeds between 2-10 Mbps over Comcast's existing cable infrastructure, allowing them to connect smaller remote offices to larger locations more easily and at a lower cost than fiber deployment. Using Comcast's Hybrid Fiber Coax network provides businesses with fast installation times and avoids construction costs since it leverages their existing infrastructure.
Network as business growth engine

Trends such as Big Data and BYOD have made the network more critical than ever. Research shows the pain points IT departments are experiencing with network infrastructure—and the investments they’re making to improve capacity , scalability and flexibility.
Ethernet Dedicated Internet Service

Comcast Business Class Ethernet Dedicated Internet (EDI) Service
is a simple, reliable and more fl exible option to traditional private line
dedicated Internet access services, providing higher bandwidth and
increased efficiencies
Ethernet Private Line Sales Sheet

Comcast offers Ethernet Private Line Service, which provides dedicated high-bandwidth connectivity between two customer sites using Comcast's fiber network. The service allows customers to connect their customer premise equipment at both sites with flexible bandwidth options up to 10Gbps. It offers three classes of service and redundant paths can be provided for added reliability. Comcast monitors and supports the private line network 24/7 through their network operations center.
More from Mallory Zemelis (12)
Recently uploaded
Removing Uninteresting Bytes in Software Fuzzing

Imagine a world where software fuzzing, the process of mutating bytes in test seeds to uncover hidden and erroneous program behaviors, becomes faster and more effective. A lot depends on the initial seeds, which can significantly dictate the trajectory of a fuzzing campaign, particularly in terms of how long it takes to uncover interesting behaviour in your code. We introduce DIAR, a technique designed to speedup fuzzing campaigns by pinpointing and eliminating those uninteresting bytes in the seeds. Picture this: instead of wasting valuable resources on meaningless mutations in large, bloated seeds, DIAR removes the unnecessary bytes, streamlining the entire process.
In this work, we equipped AFL, a popular fuzzer, with DIAR and examined two critical Linux libraries -- Libxml's xmllint, a tool for parsing xml documents, and Binutil's readelf, an essential debugging and security analysis command-line tool used to display detailed information about ELF (Executable and Linkable Format). Our preliminary results show that AFL+DIAR does not only discover new paths more quickly but also achieves higher coverage overall. This work thus showcases how starting with lean and optimized seeds can lead to faster, more comprehensive fuzzing campaigns -- and DIAR helps you find such seeds.
- These are slides of the talk given at IEEE International Conference on Software Testing Verification and Validation Workshop, ICSTW 2022.
Mind map of terminologies used in context of Generative AI

Mind map of common terms used in context of Generative AI.
20240605 QFM017 Machine Intelligence Reading List May 2024

Everything I found interesting about machines behaving intelligently during May 2024
GraphSummit Singapore | The Future of Agility: Supercharging Digital Transfor...

Leonard Jayamohan, Partner & Generative AI Lead, Deloitte
This keynote will reveal how Deloitte leverages Neo4j’s graph power for groundbreaking digital twin solutions, achieving a staggering 100x performance boost. Discover the essential role knowledge graphs play in successful generative AI implementations. Plus, get an exclusive look at an innovative Neo4j + Generative AI solution Deloitte is developing in-house.
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-und-domino-lizenzkostenreduzierung-in-der-welt-von-dlau/
DLAU und die Lizenzen nach dem CCB- und CCX-Modell sind für viele in der HCL-Community seit letztem Jahr ein heißes Thema. Als Notes- oder Domino-Kunde haben Sie vielleicht mit unerwartet hohen Benutzerzahlen und Lizenzgebühren zu kämpfen. Sie fragen sich vielleicht, wie diese neue Art der Lizenzierung funktioniert und welchen Nutzen sie Ihnen bringt. Vor allem wollen Sie sicherlich Ihr Budget einhalten und Kosten sparen, wo immer möglich. Das verstehen wir und wir möchten Ihnen dabei helfen!
Wir erklären Ihnen, wie Sie häufige Konfigurationsprobleme lösen können, die dazu führen können, dass mehr Benutzer gezählt werden als nötig, und wie Sie überflüssige oder ungenutzte Konten identifizieren und entfernen können, um Geld zu sparen. Es gibt auch einige Ansätze, die zu unnötigen Ausgaben führen können, z. B. wenn ein Personendokument anstelle eines Mail-Ins für geteilte Mailboxen verwendet wird. Wir zeigen Ihnen solche Fälle und deren Lösungen. Und natürlich erklären wir Ihnen das neue Lizenzmodell.
Nehmen Sie an diesem Webinar teil, bei dem HCL-Ambassador Marc Thomas und Gastredner Franz Walder Ihnen diese neue Welt näherbringen. Es vermittelt Ihnen die Tools und das Know-how, um den Überblick zu bewahren. Sie werden in der Lage sein, Ihre Kosten durch eine optimierte Domino-Konfiguration zu reduzieren und auch in Zukunft gering zu halten.
Diese Themen werden behandelt
- Reduzierung der Lizenzkosten durch Auffinden und Beheben von Fehlkonfigurationen und überflüssigen Konten
- Wie funktionieren CCB- und CCX-Lizenzen wirklich?
- Verstehen des DLAU-Tools und wie man es am besten nutzt
- Tipps für häufige Problembereiche, wie z. B. Team-Postfächer, Funktions-/Testbenutzer usw.
- Praxisbeispiele und Best Practices zum sofortigen Umsetzen
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Discover the seamless integration of RPA (Robotic Process Automation), COMPOSER, and APM with AWS IDP enhanced with Slack notifications. Explore how these technologies converge to streamline workflows, optimize performance, and ensure secure access, all while leveraging the power of AWS IDP and real-time communication via Slack notifications.
Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!

As the digital landscape continually evolves, operating systems play a critical role in shaping user experiences and productivity. The launch of Nitrux Linux 3.5.0 marks a significant milestone, offering a robust alternative to traditional systems such as Windows 11. This article delves into the essence of Nitrux Linux 3.5.0, exploring its unique features, advantages, and how it stands as a compelling choice for both casual users and tech enthusiasts.
20240607 QFM018 Elixir Reading List May 2024

Everything I found interesting about the Elixir programming ecosystem in May 2024
UiPath Test Automation using UiPath Test Suite series, part 6

Welcome to UiPath Test Automation using UiPath Test Suite series part 6. In this session, we will cover Test Automation with generative AI and Open AI.
UiPath Test Automation with generative AI and Open AI webinar offers an in-depth exploration of leveraging cutting-edge technologies for test automation within the UiPath platform. Attendees will delve into the integration of generative AI, a test automation solution, with Open AI advanced natural language processing capabilities.
Throughout the session, participants will discover how this synergy empowers testers to automate repetitive tasks, enhance testing accuracy, and expedite the software testing life cycle. Topics covered include the seamless integration process, practical use cases, and the benefits of harnessing AI-driven automation for UiPath testing initiatives. By attending this webinar, testers, and automation professionals can gain valuable insights into harnessing the power of AI to optimize their test automation workflows within the UiPath ecosystem, ultimately driving efficiency and quality in software development processes.
What will you get from this session?
1. Insights into integrating generative AI.
2. Understanding how this integration enhances test automation within the UiPath platform
3. Practical demonstrations
4. Exploration of real-world use cases illustrating the benefits of AI-driven test automation for UiPath
Topics covered:
What is generative AI
Test Automation with generative AI and Open AI.
UiPath integration with generative AI
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Programming Foundation Models with DSPy - Meetup Slides

Prompting language models is hard, while programming language models is easy. In this talk, I will discuss the state-of-the-art framework DSPy for programming foundation models with its powerful optimizers and runtime constraint system.
Cosa hanno in comune un mattoncino Lego e la backdoor XZ?

ABSTRACT: A prima vista, un mattoncino Lego e la backdoor XZ potrebbero avere in comune il fatto di essere entrambi blocchi di costruzione, o dipendenze di progetti creativi e software. La realtà è che un mattoncino Lego e il caso della backdoor XZ hanno molto di più di tutto ciò in comune.
Partecipate alla presentazione per immergervi in una storia di interoperabilità, standard e formati aperti, per poi discutere del ruolo importante che i contributori hanno in una comunità open source sostenibile.
BIO: Sostenitrice del software libero e dei formati standard e aperti. È stata un membro attivo dei progetti Fedora e openSUSE e ha co-fondato l'Associazione LibreItalia dove è stata coinvolta in diversi eventi, migrazioni e formazione relativi a LibreOffice. In precedenza ha lavorato a migrazioni e corsi di formazione su LibreOffice per diverse amministrazioni pubbliche e privati. Da gennaio 2020 lavora in SUSE come Software Release Engineer per Uyuni e SUSE Manager e quando non segue la sua passione per i computer e per Geeko coltiva la sua curiosità per l'astronomia (da cui deriva il suo nickname deneb_alpha).
Microsoft - Power Platform_G.Aspiotis.pdf

Revolutionizing Application Development
with AI-powered low-code, presentation by George Aspiotis, Sr. Partner Development Manager, Microsoft
Pushing the limits of ePRTC: 100ns holdover for 100 days

At WSTS 2024, Alon Stern explored the topic of parametric holdover and explained how recent research findings can be implemented in real-world PNT networks to achieve 100 nanoseconds of accuracy for up to 100 days.
GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

Dr. Sean Tan, Head of Data Science, Changi Airport Group
Discover how Changi Airport Group (CAG) leverages graph technologies and generative AI to revolutionize their search capabilities. This session delves into the unique search needs of CAG’s diverse passengers and customers, showcasing how graph data structures enhance the accuracy and relevance of AI-generated search results, mitigating the risk of “hallucinations” and improving the overall customer journey.
National Security Agency - NSA mobile device best practices

Threats to mobile devices are more prevalent and increasing in scope and complexity. Users of mobile devices desire to take full advantage of the features
available on those devices, but many of the features provide convenience and capability but sacrifice security. This best practices guide outlines steps the users can take to better protect personal devices and information.
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Discover how MongoDB Atlas and vector search technology can revolutionize your application's search capabilities. This comprehensive presentation covers:
* What is Vector Search?
* Importance and benefits of vector search
* Practical use cases across various industries
* Step-by-step implementation guide
* Live demos with code snippets
* Enhancing LLM capabilities with vector search
* Best practices and optimization strategies
Perfect for developers, AI enthusiasts, and tech leaders. Learn how to leverage MongoDB Atlas to deliver highly relevant, context-aware search results, transforming your data retrieval process. Stay ahead in tech innovation and maximize the potential of your applications.
#MongoDB #VectorSearch #AI #SemanticSearch #TechInnovation #DataScience #LLM #MachineLearning #SearchTechnology
Building Production Ready Search Pipelines with Spark and Milvus

Spark is the widely used ETL tool for processing, indexing and ingesting data to serving stack for search. Milvus is the production-ready open-source vector database. In this talk we will show how to use Spark to process unstructured data to extract vector representations, and push the vectors to Milvus vector database for search serving.
Artificial Intelligence for XMLDevelopment

In the rapidly evolving landscape of technologies, XML continues to play a vital role in structuring, storing, and transporting data across diverse systems. The recent advancements in artificial intelligence (AI) present new methodologies for enhancing XML development workflows, introducing efficiency, automation, and intelligent capabilities. This presentation will outline the scope and perspective of utilizing AI in XML development. The potential benefits and the possible pitfalls will be highlighted, providing a balanced view of the subject.
We will explore the capabilities of AI in understanding XML markup languages and autonomously creating structured XML content. Additionally, we will examine the capacity of AI to enrich plain text with appropriate XML markup. Practical examples and methodological guidelines will be provided to elucidate how AI can be effectively prompted to interpret and generate accurate XML markup.
Further emphasis will be placed on the role of AI in developing XSLT, or schemas such as XSD and Schematron. We will address the techniques and strategies adopted to create prompts for generating code, explaining code, or refactoring the code, and the results achieved.
The discussion will extend to how AI can be used to transform XML content. In particular, the focus will be on the use of AI XPath extension functions in XSLT, Schematron, Schematron Quick Fixes, or for XML content refactoring.
The presentation aims to deliver a comprehensive overview of AI usage in XML development, providing attendees with the necessary knowledge to make informed decisions. Whether you’re at the early stages of adopting AI or considering integrating it in advanced XML development, this presentation will cover all levels of expertise.
By highlighting the potential advantages and challenges of integrating AI with XML development tools and languages, the presentation seeks to inspire thoughtful conversation around the future of XML development. We’ll not only delve into the technical aspects of AI-powered XML development but also discuss practical implications and possible future directions.
“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...

“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2024/06/building-and-scaling-ai-applications-with-the-nx-ai-manager-a-presentation-from-network-optix/
Robin van Emden, Senior Director of Data Science at Network Optix, presents the “Building and Scaling AI Applications with the Nx AI Manager,” tutorial at the May 2024 Embedded Vision Summit.
In this presentation, van Emden covers the basics of scaling edge AI solutions using the Nx tool kit. He emphasizes the process of developing AI models and deploying them globally. He also showcases the conversion of AI models and the creation of effective edge AI pipelines, with a focus on pre-processing, model conversion, selecting the appropriate inference engine for the target hardware and post-processing.
van Emden shows how Nx can simplify the developer’s life and facilitate a rapid transition from concept to production-ready applications.He provides valuable insights into developing scalable and efficient edge AI solutions, with a strong focus on practical implementation.Recently uploaded (20)
Mind map of terminologies used in context of Generative AI

Mind map of terminologies used in context of Generative AI
20240605 QFM017 Machine Intelligence Reading List May 2024

20240605 QFM017 Machine Intelligence Reading List May 2024
GraphSummit Singapore | The Future of Agility: Supercharging Digital Transfor...

GraphSummit Singapore | The Future of Agility: Supercharging Digital Transfor...
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack
Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!

Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!
UiPath Test Automation using UiPath Test Suite series, part 6

UiPath Test Automation using UiPath Test Suite series, part 6
Programming Foundation Models with DSPy - Meetup Slides

Programming Foundation Models with DSPy - Meetup Slides
Cosa hanno in comune un mattoncino Lego e la backdoor XZ?

Cosa hanno in comune un mattoncino Lego e la backdoor XZ?
Pushing the limits of ePRTC: 100ns holdover for 100 days

Pushing the limits of ePRTC: 100ns holdover for 100 days
GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...
National Security Agency - NSA mobile device best practices

National Security Agency - NSA mobile device best practices
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf
Building Production Ready Search Pipelines with Spark and Milvus

Building Production Ready Search Pipelines with Spark and Milvus
“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...

“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...
Comcast SD-WAN Network Diagram
- 1. Comcast Proprietary & Confidential AN “ALL-NETWORK” SOLUTION 1 PURE SD-WAN HYBRID WAN HYBRID WAN WITH HIGH AVAILABILITY HYBRID WAN CUSTOMER DRIVEN Update existing networks or cost-effectively create new ones. The Comcast Business software-defined approach makes branch connections faster and more agile with far greater capabilities. INTERNET SD- WAN (IPSec) uCPE Cable Modem LAN LAN INTERNET SD- WAN (IPSec) Cable Modem uCPE MPLS Customer Router WAN Router INTERNET SD- WAN (IPSec) MPLS LAN uCPE Cable Modem VRRP uCPE LAN uCPE WAN Router INTERNET SD- WAN (IPSec) MPLS Cable Modem WAN Router
