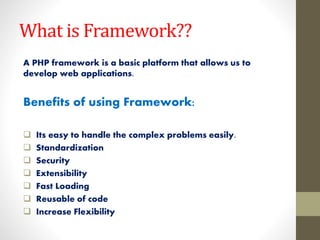
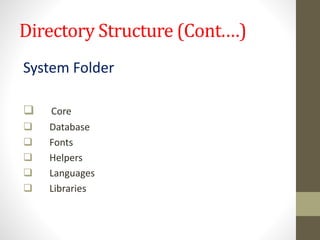
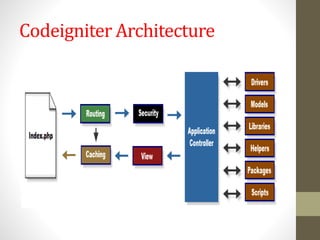
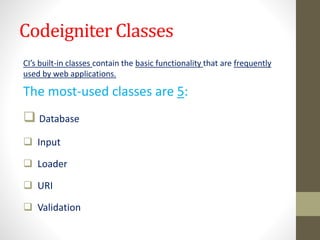
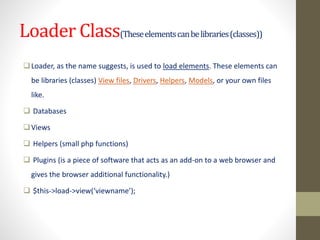
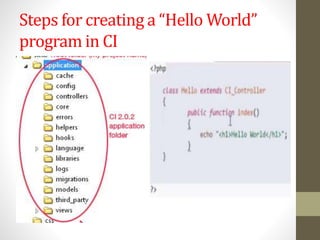
The document discusses PHP frameworks, specifically CodeIgniter, highlighting its benefits such as ease of handling complex problems, standardization, security, and reusability of code. It outlines the architecture, key components, and classes like database, input, loader, uri, and validation, which facilitate web application development. Additionally, it mentions the directory structure of CodeIgniter and provides references for further information on PHP frameworks.