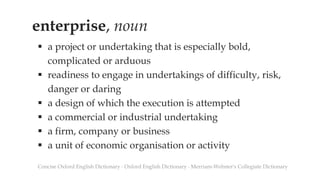
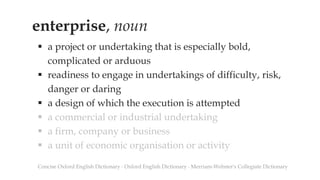
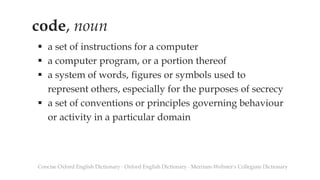
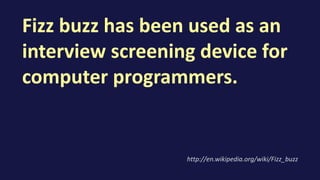
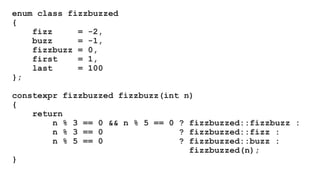
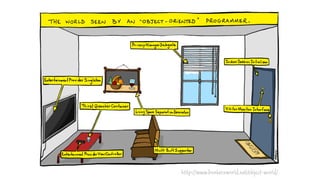
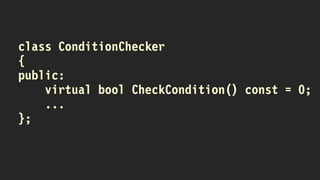
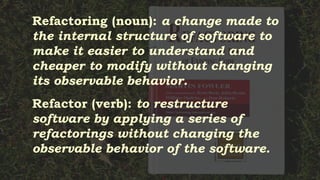
The document defines various terms such as 'enterprise' and 'code', explaining their meanings and applications. It also describes the Fizz Buzz game, its rules, and its variations, including its use in programming and interviews. Additionally, it touches on concepts like cargo cult programming, refactoring, and the importance of clear communication in coding.


![Adults may play Fizz buzz as a
drinking game, where making
a mistake leads to the player
having to make a drinking-
related forfeit.
http://en.wikipedia.org/wiki/Fizz_buzz
[citation needed]](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-18-320.jpg)
![// Define constants
#define FIZZ "fizz"
#define BUZZ "buzz"
#define NULL 0
#define PI 3.14
std::string FizzBuzzCalculator(int n)
{
// Declarations
char buffer[1024];
memset(buffer, 0, 1024);
std::string retval;
auto isDivisibleBy3 = [&]() { if (n % 3 == 0) { strcpy(buffer, FIZZ); return true; } return false; };
auto isDivisibleBy5 = [&]() { if (n % 5 == 0) { strcat(buffer, BUZZ); return true; } return false; };
// Check to see if argument is between 1 and 100, otherwise log and throw
if (n < 1 || n > 100)
{
sprintf(buffer, "FizzBuzzCalculator, argument must be in range: %i", n);
Log::Instance().Write(buffer);
throw std::invalid_argument(buffer);
}
// Check if need to write number
if (!isDivisibleBy3() & !isDivisibleBy5())
{
sprintf(buffer, "%i", n);
}
// Assign return value (retval) and return
retval.assign(buffer, strlen(buffer));
return retval;
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-21-320.jpg)
![// Define constants
#define FIZZ "fizz"
#define BUZZ "buzz"
#define NULL 0
#define PI 3.14
std::string FizzBuzzCalculator(int n)
{
// Declarations
char buffer[1024];
memset(buffer, 0, 1024);
std::string retval;
auto isDivisibleBy3 = [&]() { if (n % 3 == 0) { strcpy(buffer, FIZZ); return true; } return false; };
auto isDivisibleBy5 = [&]() { if (n % 5 == 0) { strcat(buffer, BUZZ); return true; } return false; };
// Check to see if argument is between 1 and 100, otherwise log and throw
if (n < 1 || n > 100)
{
sprintf(buffer, "FizzBuzzCalculator, argument must be in range: %i", n);
Log::Instance().Write(buffer);
throw std::invalid_argument(buffer);
}
// Check if need to write number
if (!isDivisibleBy3() & !isDivisibleBy5())
{
sprintf(buffer, "%i", n);
}
// Assign return value (retval) and return
retval.assign(buffer, strlen(buffer));
return retval;
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-22-320.jpg)
![// Define constants
#define FIZZ "fizz"
#define BUZZ "buzz"
#define NULL 0
#define PI 3.14
std::string FizzBuzzCalculator(int n)
{
// Declarations
char buffer[1024];
memset(buffer, 0, 1024);
std::string retval;
auto isDivisibleBy3 = [&]() { if (n % 3 == 0) { strcpy(buffer, FIZZ); return true; } return false; };
auto isDivisibleBy5 = [&]() { if (n % 5 == 0) { strcat(buffer, BUZZ); return true; } return false; };
// Check to see if argument is between 1 and 100, otherwise log and throw
if (n < 1 || n > 100)
{
sprintf(buffer, "FizzBuzzCalculator, argument must be in range: %i", n);
Log::Instance().Write(buffer);
throw std::invalid_argument(buffer);
}
// Check if need to write number
if (!isDivisibleBy3() & !isDivisibleBy5())
{
sprintf(buffer, "%i", n);
}
// Assign return value (retval) and return
retval.assign(buffer, strlen(buffer));
return retval;
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-23-320.jpg)
![// Define constants
#define FIZZ "fizz"
#define BUZZ "buzz"
#define NULL 0
#define PI 3.14
std::string FizzBuzzCalculator(int n)
{
// Declarations
char buffer[1024];
memset(buffer, 0, 1024);
std::string retval;
auto isDivisibleBy3 = [&]() { if (n % 3 == 0) { strcpy(buffer, FIZZ); return true; } return false; };
auto isDivisibleBy5 = [&]() { if (n % 5 == 0) { strcat(buffer, BUZZ); return true; } return false; };
// Check to see if argument is between 1 and 100, otherwise log and throw
if (n < 1 || n > 100)
{
sprintf(buffer, "FizzBuzzCalculator, argument must be in range: %i", n);
Log::Instance().Write(buffer);
throw std::invalid_argument(buffer);
}
// Check if need to write number
if (!isDivisibleBy3() & !isDivisibleBy5())
{
sprintf(buffer, "%i", n);
}
// Assign return value (retval) and return
retval.assign(buffer, strlen(buffer));
return retval;
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-24-320.jpg)
![// Define constants
#define FIZZ "fizz"
#define BUZZ "buzz"
#define NULL 0
#define PI 3.14
std::string FizzBuzzCalculator(int n)
{
// Declarations
char buffer[1024];
memset(buffer, 0, 1024);
std::string retval;
auto isDivisibleBy3 = [&]() { if (n % 3 == 0) { strcpy(buffer, FIZZ); return true; } return false; };
auto isDivisibleBy5 = [&]() { if (n % 5 == 0) { strcat(buffer, BUZZ); return true; } return false; };
// Check to see if argument is between 1 and 100, otherwise log and throw
if (n < 1 || n > 100)
{
sprintf(buffer, "FizzBuzzCalculator, argument must be in range: %i", n);
Log::Instance().Write(buffer);
throw std::invalid_argument(buffer);
}
// Check if need to write number
if (!isDivisibleBy3() & !isDivisibleBy5())
{
sprintf(buffer, "%i", n);
}
// Assign return value (retval) and return
retval.assign(buffer, strlen(buffer));
return retval;
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-25-320.jpg)
![// Define constants
#define FIZZ "fizz"
#define BUZZ "buzz"
#define NULL 0
#define PI 3.14
std::string FizzBuzzCalculator(int n)
{
// Declarations
char buffer[1024];
memset(buffer, 0, 1024);
std::string retval;
auto isDivisibleBy3 = [&]() { if (n % 3 == 0) { strcpy(buffer, FIZZ); return true; } return false; };
auto isDivisibleBy5 = [&]() { if (n % 5 == 0) { strcat(buffer, BUZZ); return true; } return false; };
// Check to see if argument is between 1 and 100, otherwise log and throw
if (n < 1 || n > 100)
{
sprintf(buffer, "FizzBuzzCalculator, argument must be in range: %i", n);
Log::Instance().Write(buffer);
throw std::invalid_argument(buffer);
}
// Check if need to write number
if (!isDivisibleBy3() & !isDivisibleBy5())
{
sprintf(buffer, "%i", n);
}
// Assign return value (retval) and return
retval.assign(buffer, strlen(buffer));
return retval;
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-26-320.jpg)
![// Define constants
#define FIZZ "fizz"
#define BUZZ "buzz"
#define NULL 0
#define PI 3.14
std::string FizzBuzzCalculator(int n)
{
// Declarations
char buffer[1024];
memset(buffer, 0, 1024);
std::string retval;
auto isDivisibleBy3 = [&]() { if (n % 3 == 0) { strcpy(buffer, FIZZ); return true; } return false; };
auto isDivisibleBy5 = [&]() { if (n % 5 == 0) { strcat(buffer, BUZZ); return true; } return false; };
// Check to see if argument is between 1 and 100, otherwise log and throw
if (n < 1 || n > 100)
{
sprintf(buffer, "FizzBuzzCalculator, argument must be in range: %i", n);
Log::Instance().Write(buffer);
throw std::invalid_argument(buffer);
}
// Check if need to write number
if (!isDivisibleBy3() & !isDivisibleBy5())
{
sprintf(buffer, "%i", n);
}
// Assign return value (retval) and return
retval.assign(buffer, strlen(buffer));
return retval;
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-27-320.jpg)




![string fizzbuzz(int n)
{
static const string fizzed[] { "", "Fizz" };
static const string buzzed[] { "", "Buzz" };
const string result =
fizzed[n % 3 == 0] + buzzed[n % 5 == 0];
return result.empty() ? to_string(n) : result;
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-37-320.jpg)
> f)
{
return
n % 3 == 0
? [=](auto) { return "Fizz" + f(""); }
: f;
};
auto buzz =
[=](function<string(string)> f)
{
return
n % 5 == 0
? [=](auto) { return "Buzz" + f(""); }
: f;
};
auto id = [](auto s) { return s; };
return fizz(buzz(id))(to_string(n));
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-39-320.jpg)
> f)
{
return
n % d == 0
? [=](string) { return s + f(""); }
: f;
};
auto fizz = bind(test, 3, "Fizz", _1);
auto buzz = bind(test, 5, "Buzz", _1);
auto id = [](auto s) { return s; };
return fizz(buzz(id))(to_string(n));
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-40-320.jpg)





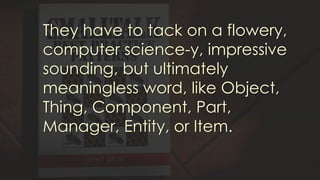
![People will be using the words
you choose in their conversation
for the next 20 years. You want
to be sure you do it right.
Unfortunately, many people get
all formal [...]. Just calling it what
it is isn't enough.](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-52-320.jpg)



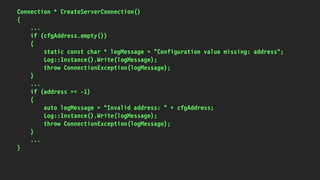
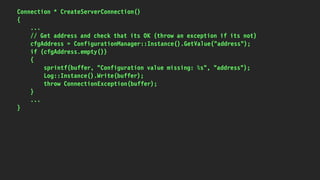
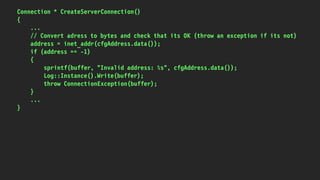
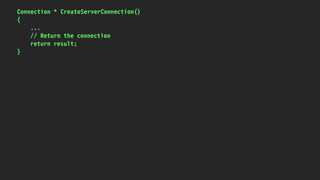
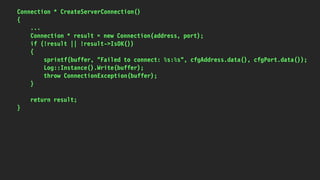
![Connection * CreateServerConnection()
{
// Declarations
char buffer[1024];
std::string cfgAddress;
unsigned long address;
std::string cfgPort;
unsigned short port;
Connection * result;
// Get address and check that its OK (throw an exception if its not)
cfgAddress = ConfigurationManager::Instance().GetValue("address");
if (cfgAddress.empty())
{
sprintf(buffer, "Configuration value missing: %s", "address");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
// Convert adress to bytes and check that its OK (throw an exception if its not)
address = inet_addr(cfgAddress.data());
if (address == -1)
{
sprintf(buffer, "Invalid address: %s", cfgAddress.data());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
// Get port and check that its OK (throw an exception if its not)
cfgPort = ConfigurationManager::Instance().GetValue("port");
if (cfgPort.empty())
{
sprintf(buffer, "Configuration value missing: %s", "port");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
// Convert port too bytes
port = htons(atoi(cfgPort.data()));
// Creation connection and check that its OK (throw an exception if its not)
result = new Connection(address, port);
if (!result || !result->IsOK())
{
sprintf(buffer, "Failed to connect: %s:%s", cfgAddress.data(), cfgPort.data());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
// Return the connection
return result;
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-61-320.jpg)
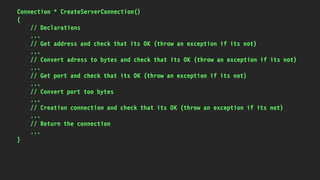
![Connection * CreateServerConnection()
{
// Declarations
char buffer[1024];
std::string cfgAddress;
unsigned long address;
std::string cfgPort;
unsigned short port;
Connection * result;
...
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-62-320.jpg)
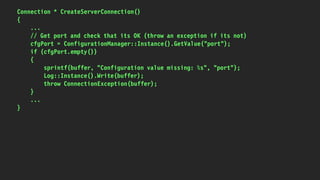
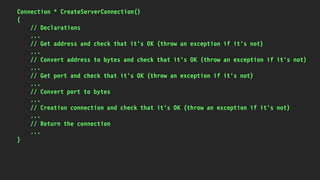
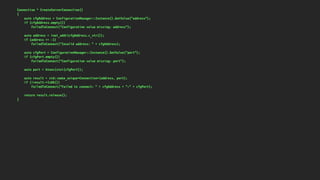
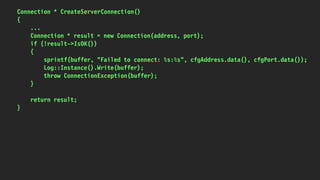
![Connection * CreateServerConnection()
{
char buffer[1024];
std::string cfgAddress;
unsigned long address;
std::string cfgPort;
unsigned short port;
Connection * result;
cfgAddress = ConfigurationManager::Instance().GetValue("address");
if (cfgAddress.empty())
{
sprintf(buffer, "Configuration value missing: %s", "address");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
address = inet_addr(cfgAddress.data());
if (address == -1)
{
sprintf(buffer, "Invalid address: %s", cfgAddress.data());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
cfgPort = ConfigurationManager::Instance().GetValue("port");
if (cfgPort.empty())
{
sprintf(buffer, "Configuration value missing: %s", "port");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
port = htons(atoi(cfgPort.data()));
result = new Connection(address, port);
if (!result || !result->IsOK())
{
sprintf(buffer, "Failed to connect: %s:%s", cfgAddress.data(), cfgPort.data());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
return result;
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-72-320.jpg)
![Connection * CreateServerConnection()
{
char buffer[1024];
std::string cfgAddress = ConfigurationManager::Instance().GetValue("address");
if (cfgAddress.empty())
{
sprintf(buffer, "Configuration value missing: %s", "address");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
unsigned long address = inet_addr(cfgAddress.data());
if (address == -1)
{
sprintf(buffer, "Invalid address: %s", cfgAddress.data());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
std::string cfgPort = ConfigurationManager::Instance().GetValue("port");
if (cfgPort.empty())
{
sprintf(buffer, "Configuration value missing: %s", "port");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
unsigned short port = htons(atoi(cfgPort.data()));
Connection * result = new Connection(address, port);
if (!result || !result->IsOK())
{
sprintf(buffer, "Failed to connect: %s:%s", cfgAddress.data(), cfgPort.data());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
return result;
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-73-320.jpg)
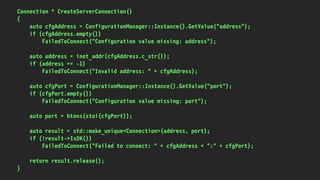
![Connection * CreateServerConnection()
{
char buffer[1024];
auto cfgAddress = ConfigurationManager::Instance().GetValue("address");
if (cfgAddress.empty())
{
sprintf(buffer, "Configuration value missing: %s", "address");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto address = inet_addr(cfgAddress.data());
if (address == -1)
{
sprintf(buffer, "Invalid address: %s", cfgAddress.data());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto cfgPort = ConfigurationManager::Instance().GetValue("port");
if (cfgPort.empty())
{
sprintf(buffer, "Configuration value missing: %s", "port");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto port = htons(atoi(cfgPort.data()));
Connection * result = new Connection(address, port);
if (!result || !result->IsOK())
{
sprintf(buffer, "Failed to connect: %s:%s", cfgAddress.data(), cfgPort.data());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
return result;
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-74-320.jpg)
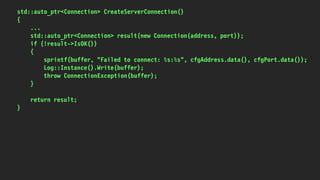
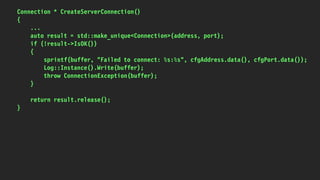
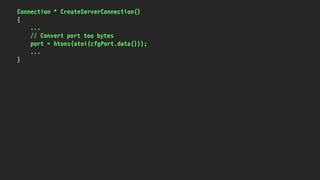
![Connection * CreateServerConnection()
{
char buffer[1024];
auto cfgAddress = ConfigurationManager::Instance().GetValue("address");
if (cfgAddress.empty())
{
sprintf(buffer, "Configuration value missing: %s", "address");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto address = inet_addr(cfgAddress.data());
if (address == -1)
{
sprintf(buffer, "Invalid address: %s", cfgAddress.data());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto cfgPort = ConfigurationManager::Instance().GetValue("port");
if (cfgPort.empty())
{
sprintf(buffer, "Configuration value missing: %s", "port");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto port = htons(atoi(cfgPort.data()));
auto result = std::make_unique<Connection>(address, port);
if (!result->IsOK())
{
sprintf(buffer, "Failed to connect: %s:%s", cfgAddress.data(), cfgPort.data());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
return result.release();
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-80-320.jpg)
![Connection * CreateServerConnection()
{
char buffer[1024];
auto cfgAddress = ConfigurationManager::Instance().GetValue("address");
if (cfgAddress.empty())
{
sprintf(buffer, "Configuration value missing: %s", "address");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto address = inet_addr(cfgAddress.data());
if (address == -1)
{
sprintf(buffer, "Invalid address: %s", cfgAddress.data());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto cfgPort = ConfigurationManager::Instance().GetValue("port");
if (cfgPort.empty())
{
sprintf(buffer, "Configuration value missing: %s", "port");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto port = htons(atoi(cfgPort.data()));
auto result = std::make_unique<Connection>(address, port);
if (!result->IsOK())
{
sprintf(buffer, "Failed to connect: %s:%s", cfgAddress.data(), cfgPort.data());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
return result.release();
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-81-320.jpg)
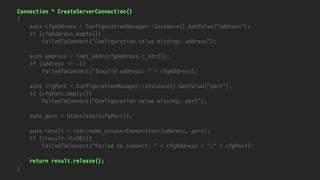
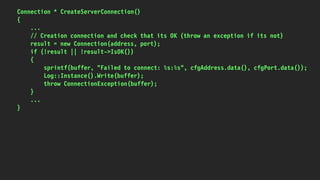
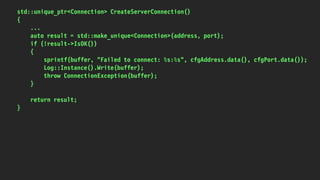
![Connection * CreateServerConnection()
{
char buffer[1024];
auto cfgAddress = ConfigurationManager::Instance().GetValue("address");
if (cfgAddress.empty())
{
sprintf(buffer, "Configuration value missing: %s", "address");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto address = inet_addr(cfgAddress.c_str());
if (address == -1)
{
sprintf(buffer, "Invalid address: %s", cfgAddress.c_str());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto cfgPort = ConfigurationManager::Instance().GetValue("port");
if (cfgPort.empty())
{
sprintf(buffer, "Configuration value missing: %s", "port");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto port = htons(atoi(cfgPort.c_str()));
auto result = std::make_unique<Connection>(address, port);
if (!result->IsOK())
{
sprintf(buffer, "Failed to connect: %s:%s", cfgAddress.c_str(), cfgPort.c_str());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
return result.release();
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-82-320.jpg)
![Connection * CreateServerConnection()
{
char buffer[1024];
auto cfgAddress = ConfigurationManager::Instance().GetValue("address");
if (cfgAddress.empty())
{
sprintf(buffer, "Configuration value missing: %s", "address");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto address = inet_addr(cfgAddress.c_str());
if (address == -1)
{
sprintf(buffer, "Invalid address: %s", cfgAddress.c_str());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto cfgPort = ConfigurationManager::Instance().GetValue("port");
if (cfgPort.empty())
{
sprintf(buffer, "Configuration value missing: %s", "port");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto port = htons(stoi(cfgPort));
auto result = std::make_unique<Connection>(address, port);
if (!result->IsOK())
{
sprintf(buffer, "Failed to connect: %s:%s", cfgAddress.c_str(), cfgPort.c_str());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
return result.release();
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-83-320.jpg)
![Connection * CreateServerConnection()
{
char buffer[1024];
auto cfgAddress = ConfigurationManager::Instance().GetValue("address");
if (cfgAddress.empty())
{
sprintf(buffer, "Configuration value missing: %s", "address");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto address = inet_addr(cfgAddress.c_str());
if (address == -1)
{
sprintf(buffer, "Invalid address: %s", cfgAddress.c_str());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto cfgPort = ConfigurationManager::Instance().GetValue("port");
if (cfgPort.empty())
{
sprintf(buffer, "Configuration value missing: %s", "port");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto port = htons(stoi(cfgPort));
auto result = std::make_unique<Connection>(address, port);
if (!result->IsOK())
{
sprintf(buffer, "Failed to connect: %s:%s", cfgAddress.c_str(), cfgPort.c_str());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
return result.release();
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-84-320.jpg)
![Connection * CreateServerConnection()
{
char buffer[1024];
auto cfgAddress = ConfigurationManager::Instance().GetValue("address");
if (cfgAddress.empty())
{
snprintf(buffer, sizeof buffer, "Configuration value missing: %s", "address");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto address = inet_addr(cfgAddress.c_str());
if (address == -1)
{
snprintf(buffer, sizeof buffer, "Invalid address: %s", cfgAddress.c_str());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto cfgPort = ConfigurationManager::Instance().GetValue("port");
if (cfgPort.empty())
{
snprintf(buffer, sizeof buffer, "Configuration value missing: %s", "port");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
auto port = htons(stoi(cfgPort));
auto result = std::make_unique<Connection>(address, port);
if (!result->IsOK())
{
snprintf(buffer, sizeof buffer, "Failed to connect: %s:%s", cfgAddress.c_str(), cfgPort.c_str());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
return result.release();
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-85-320.jpg)
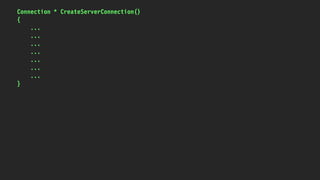
![Connection * CreateServerConnection()
{
char buffer[1024];
...
if (cfgAddress.empty())
{
snprintf(buffer, sizeof buffer, "Configuration value missing: %s", "address");
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
...
if (address == -1)
{
snprintf(buffer, sizeof buffer, "Invalid address: %s", cfgAddress.c_str());
Log::Instance().Write(buffer);
throw ConnectionException(buffer);
}
...
}](https://image.slidesharecdn.com/cleancodershatewhathappenstoyourcodewhenyouusetheseenterpriseprogrammingtricks-170627153348/85/Clean-Coders-Hate-What-Happens-To-Your-Code-When-You-Use-These-Enterprise-Programming-Tricks-86-320.jpg)