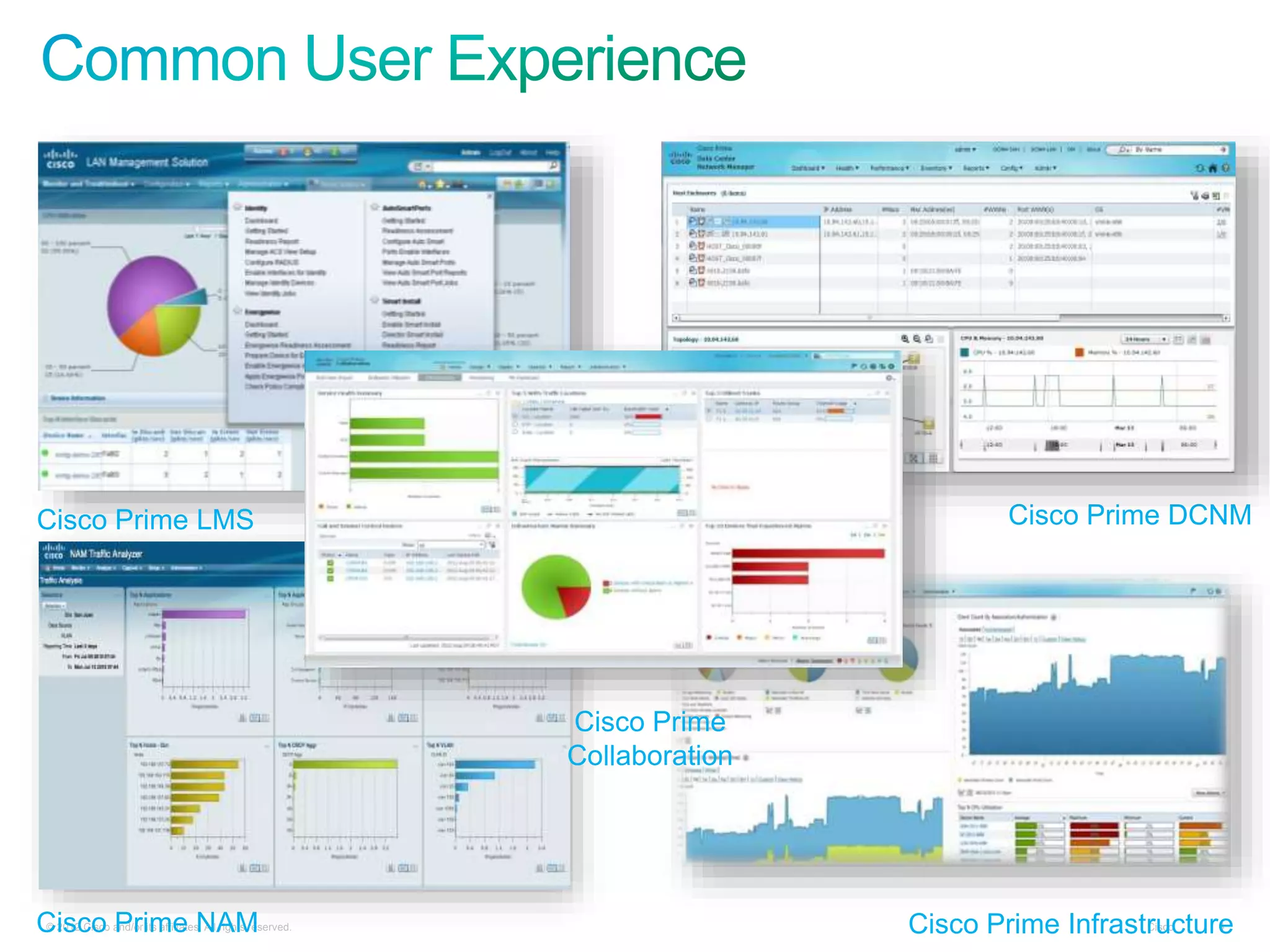
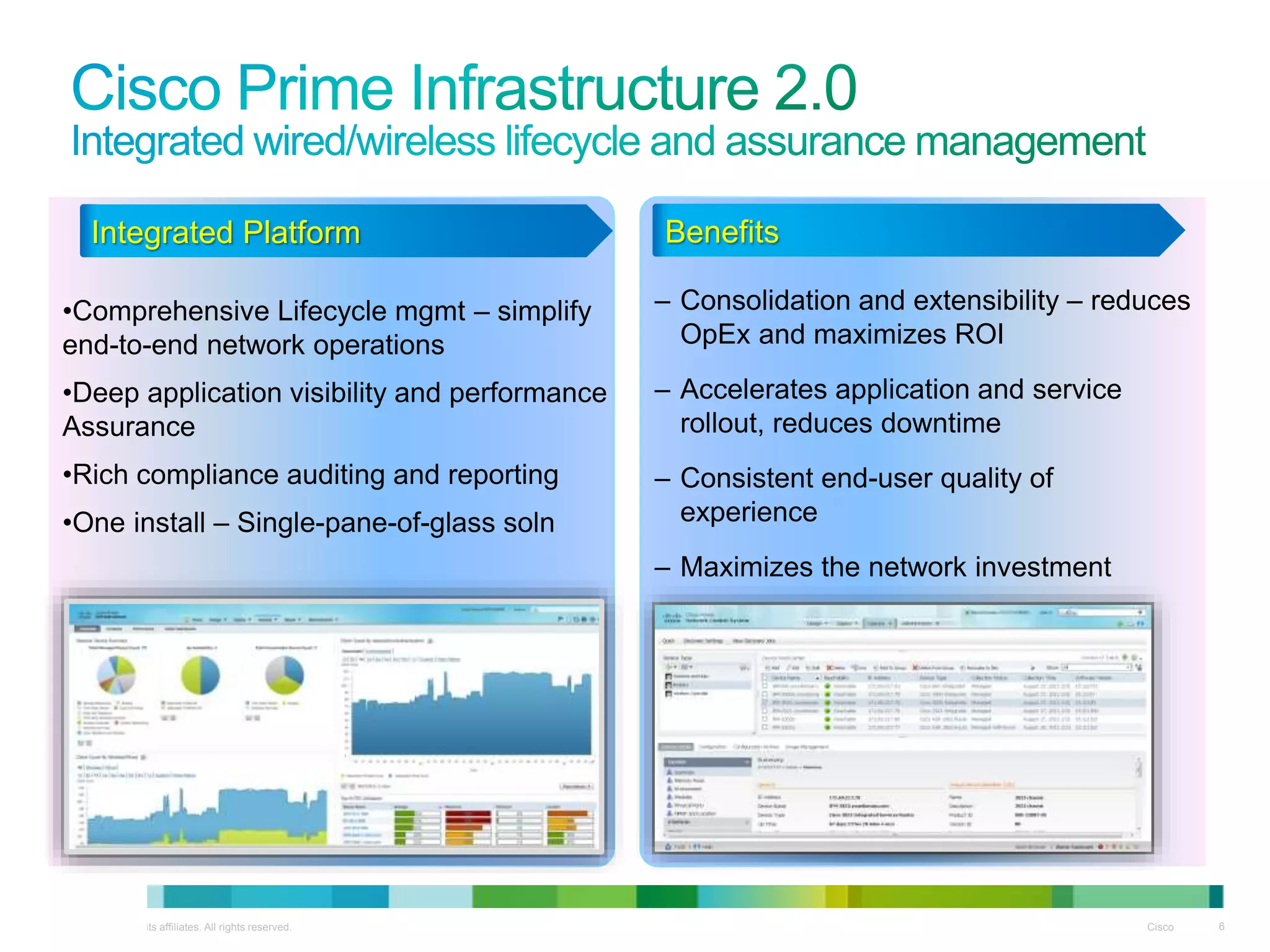
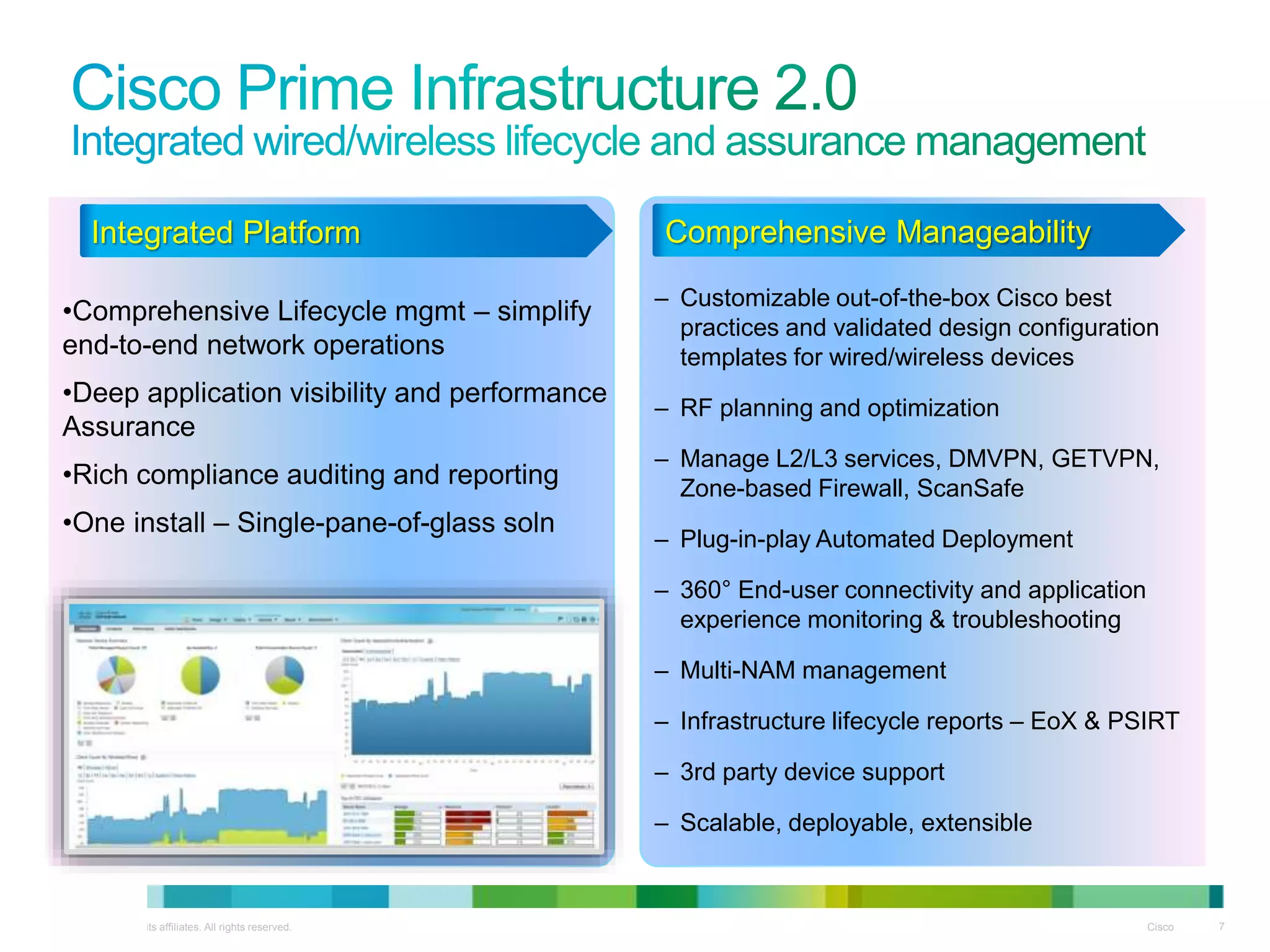
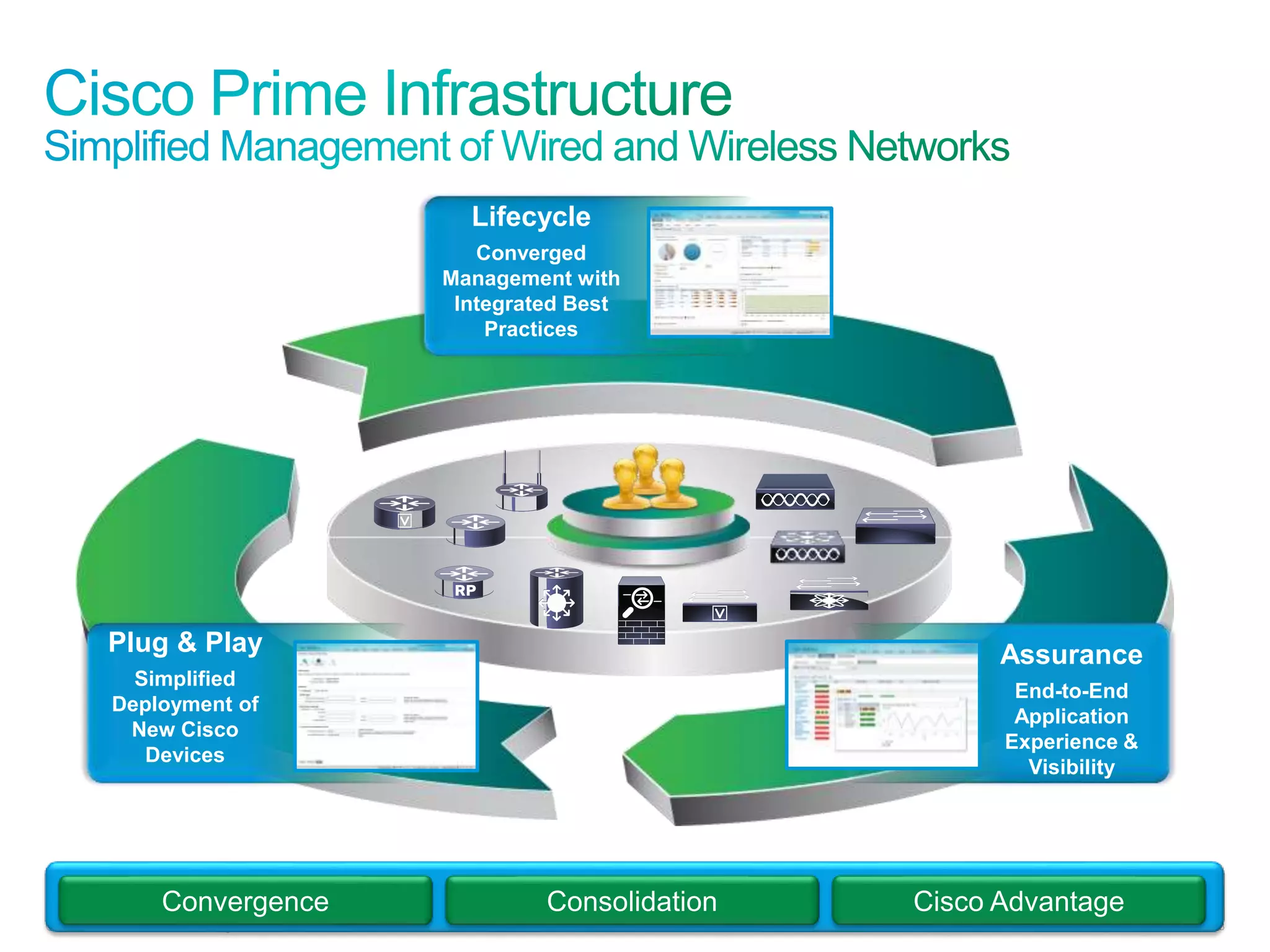
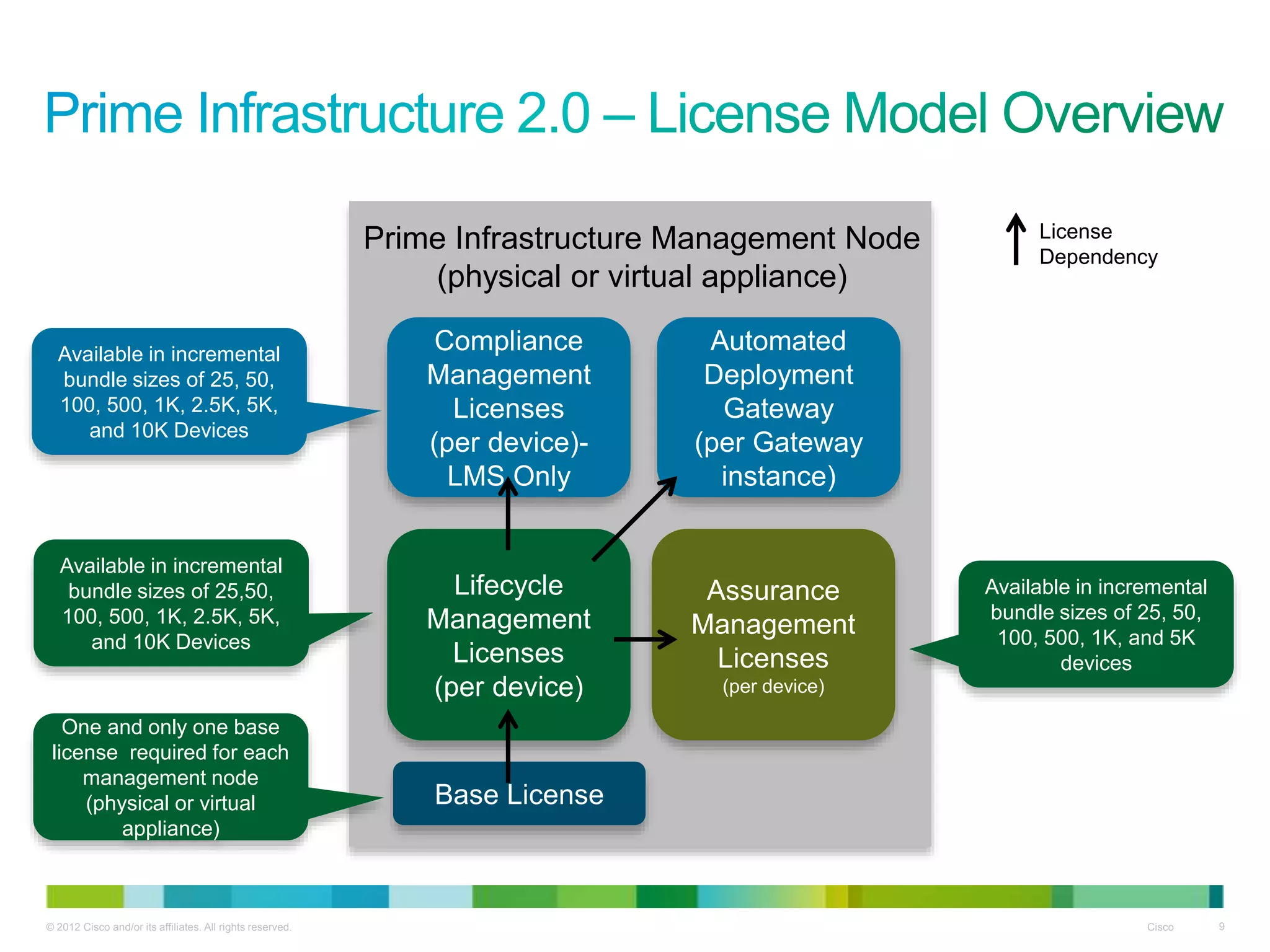
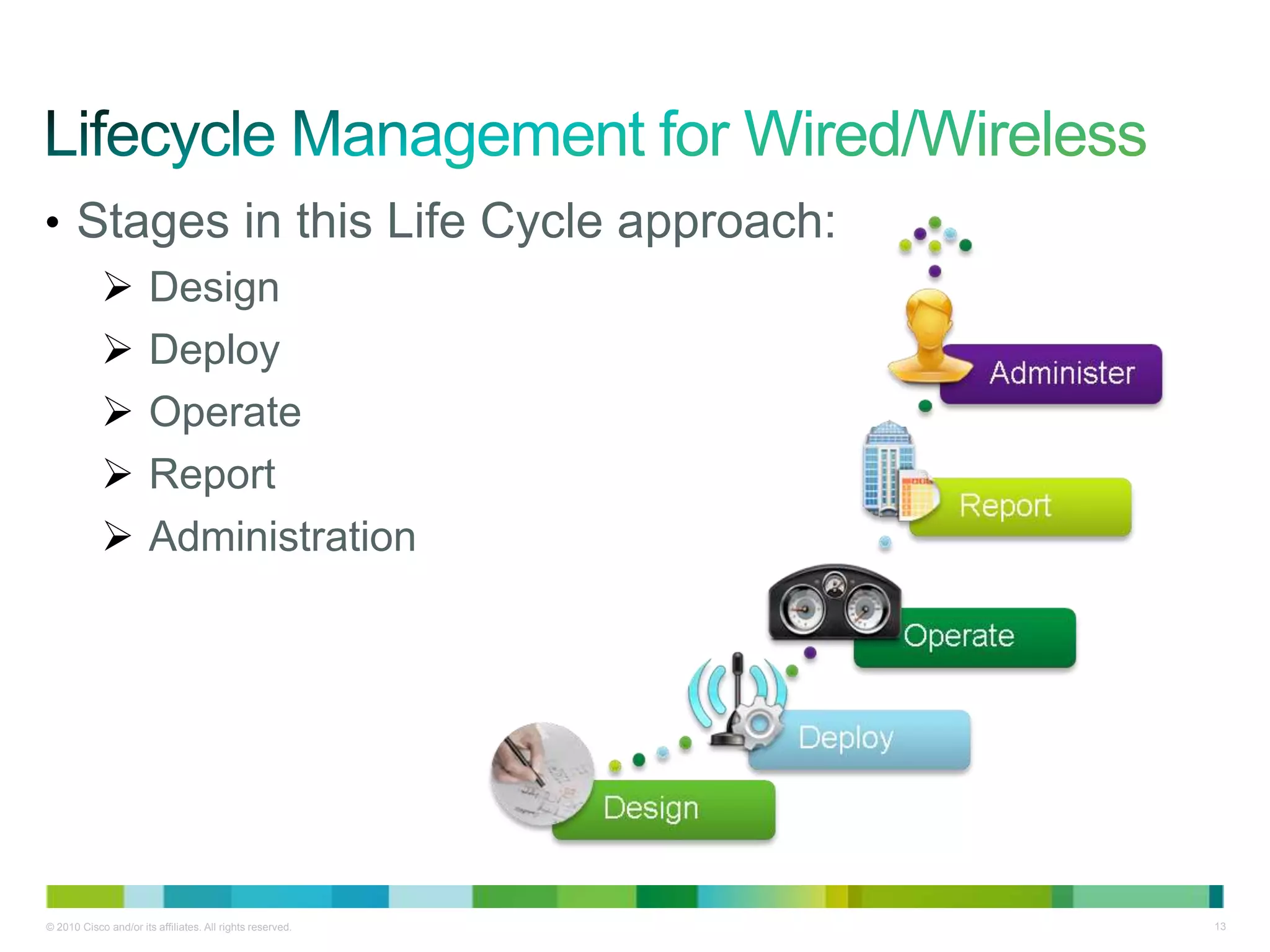
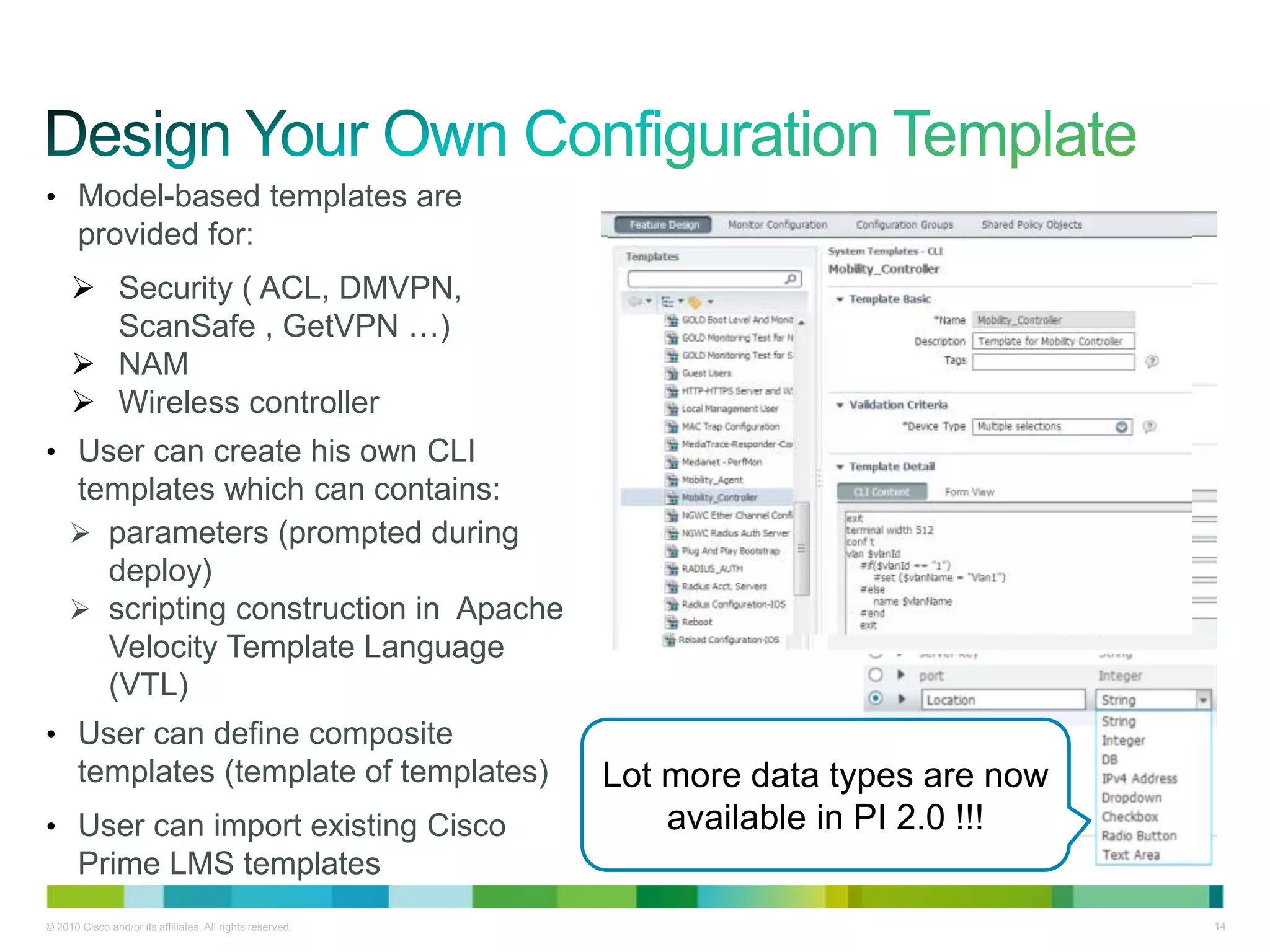
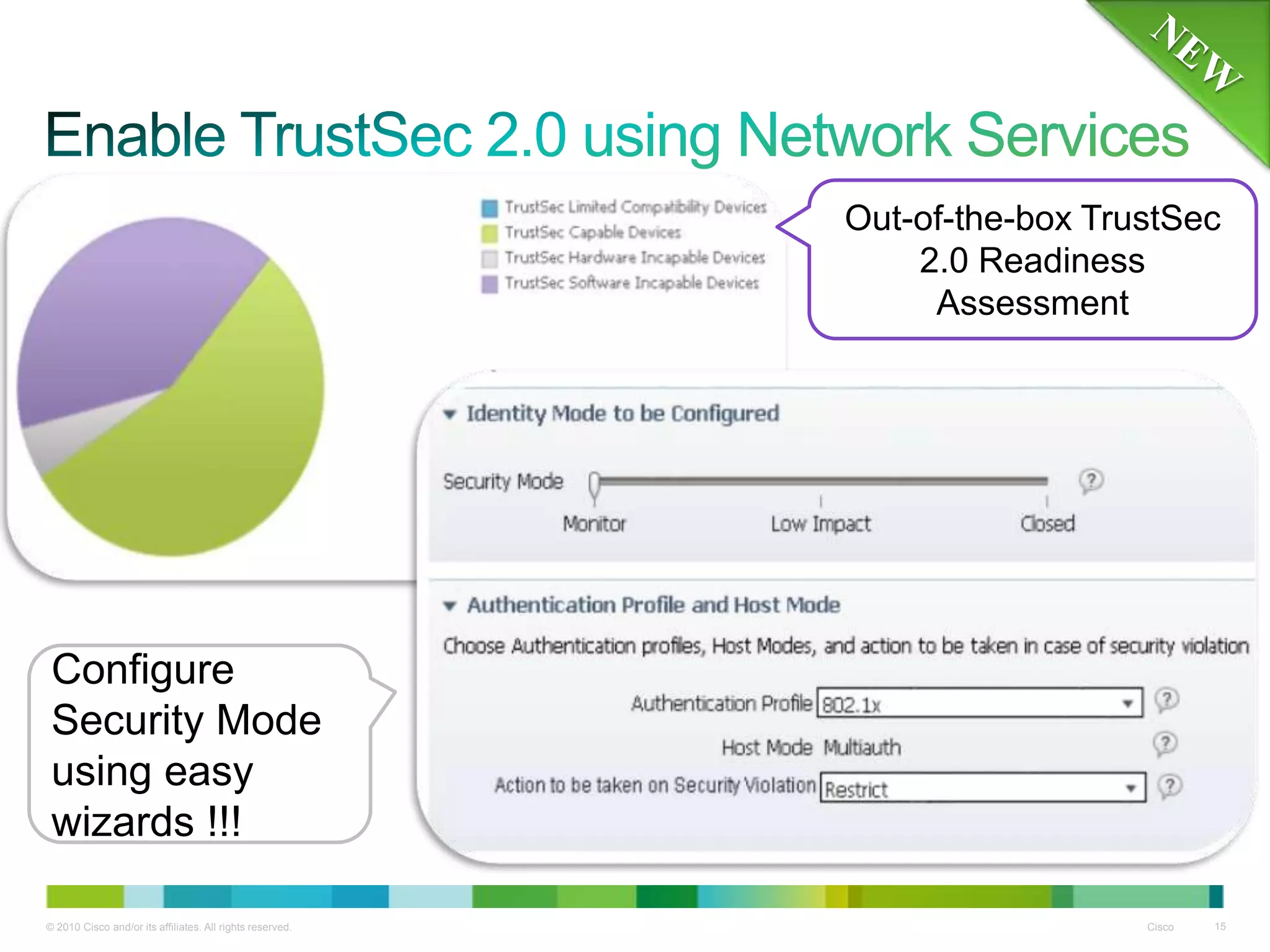
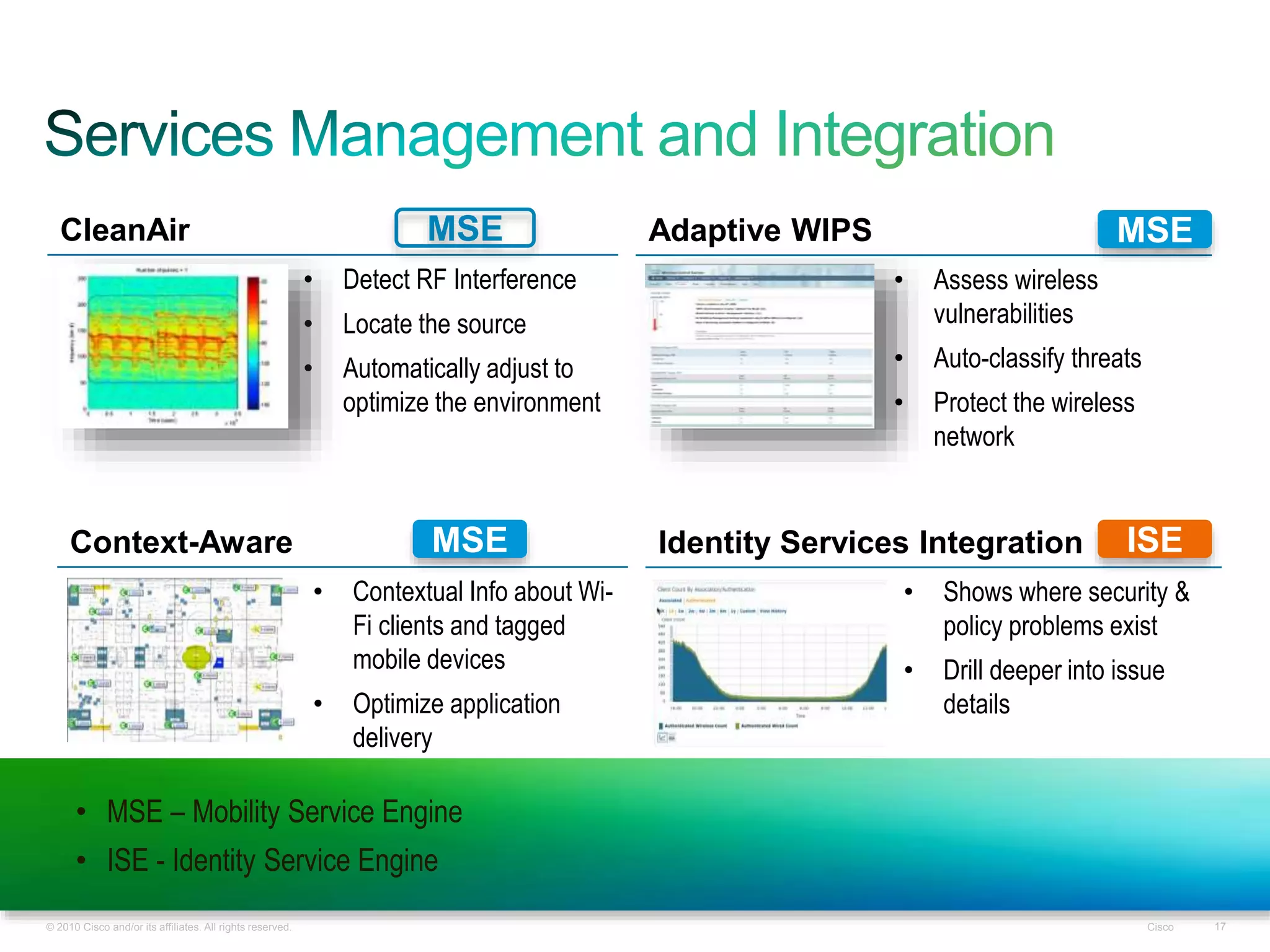
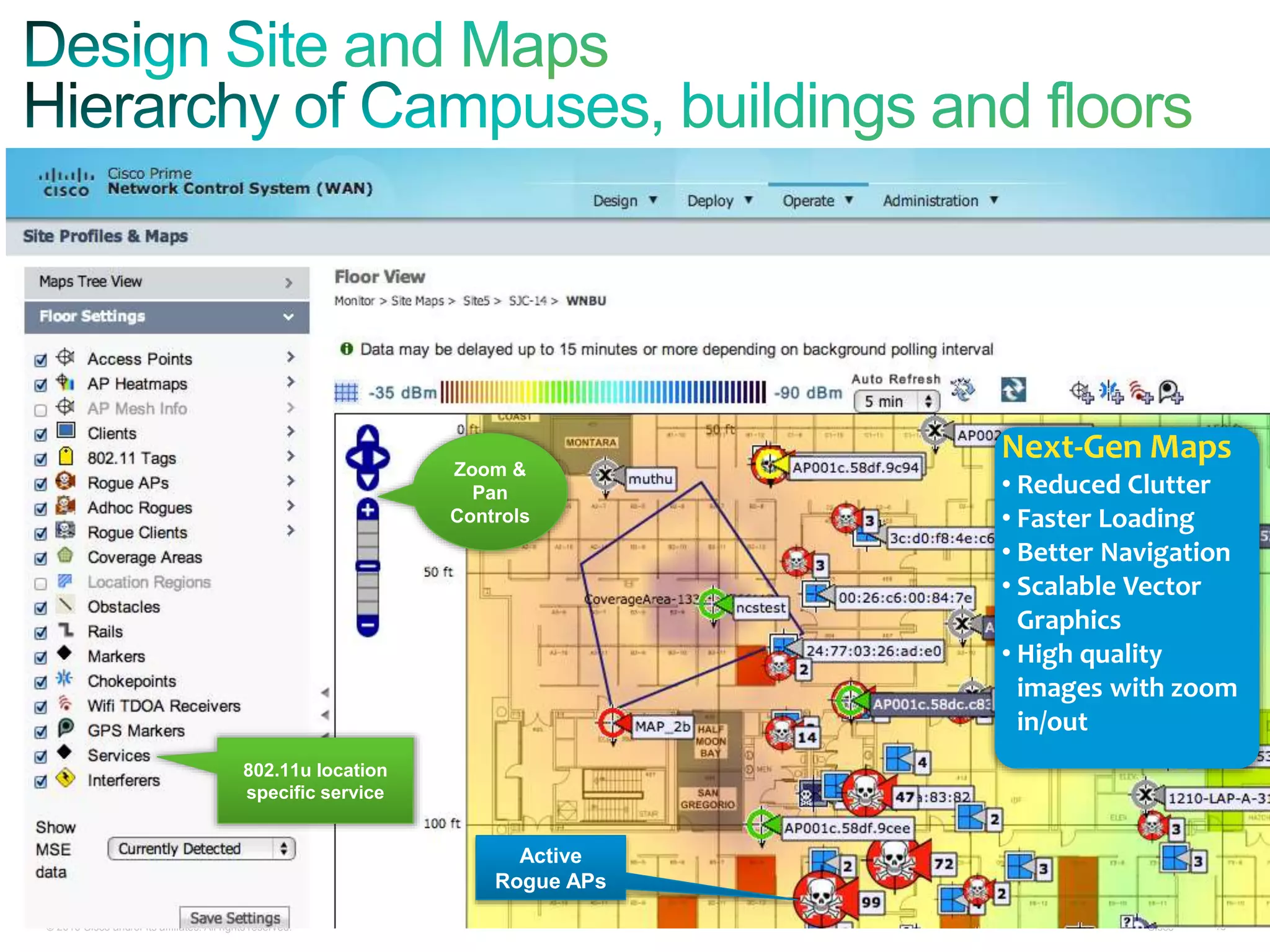
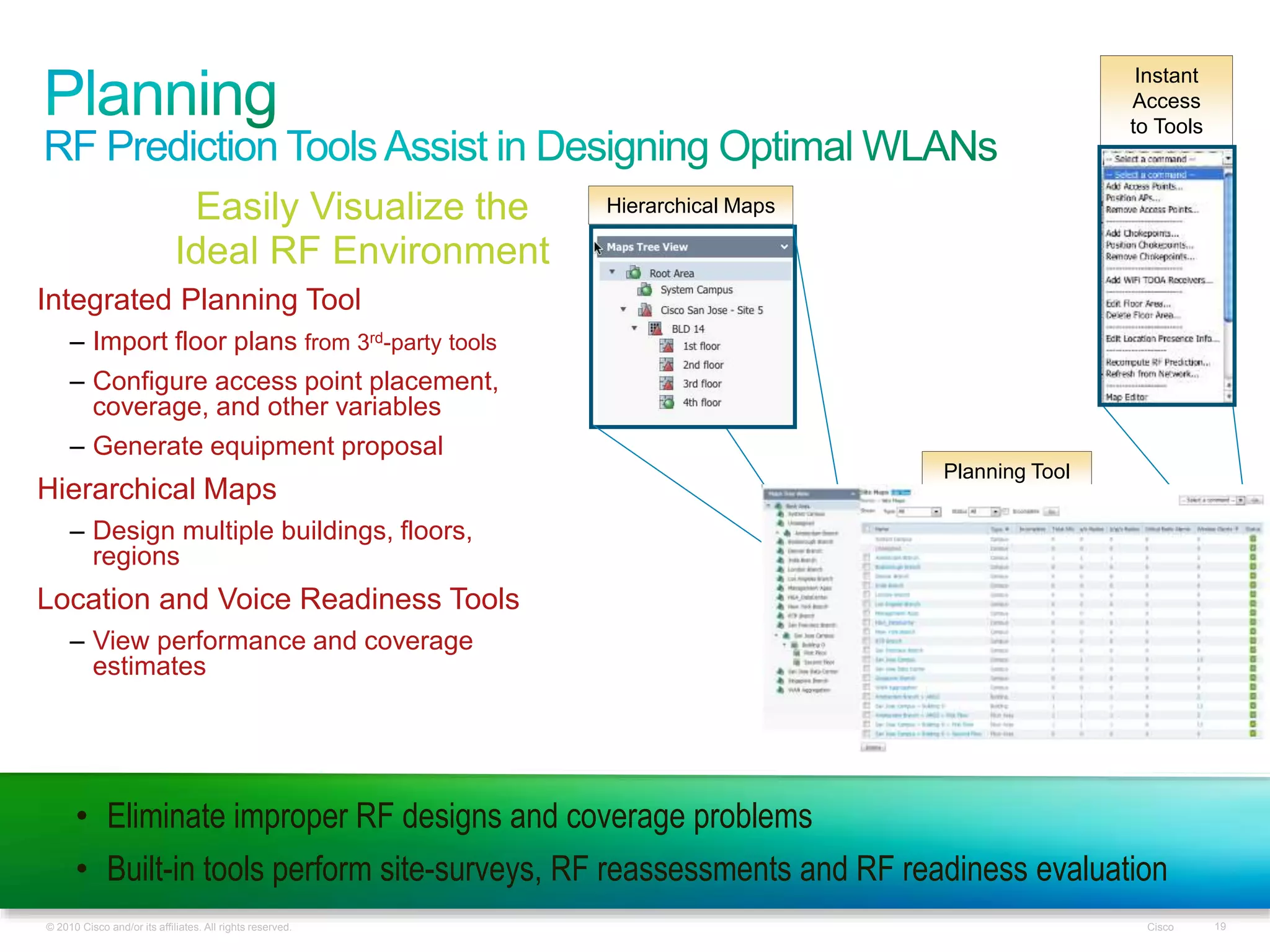
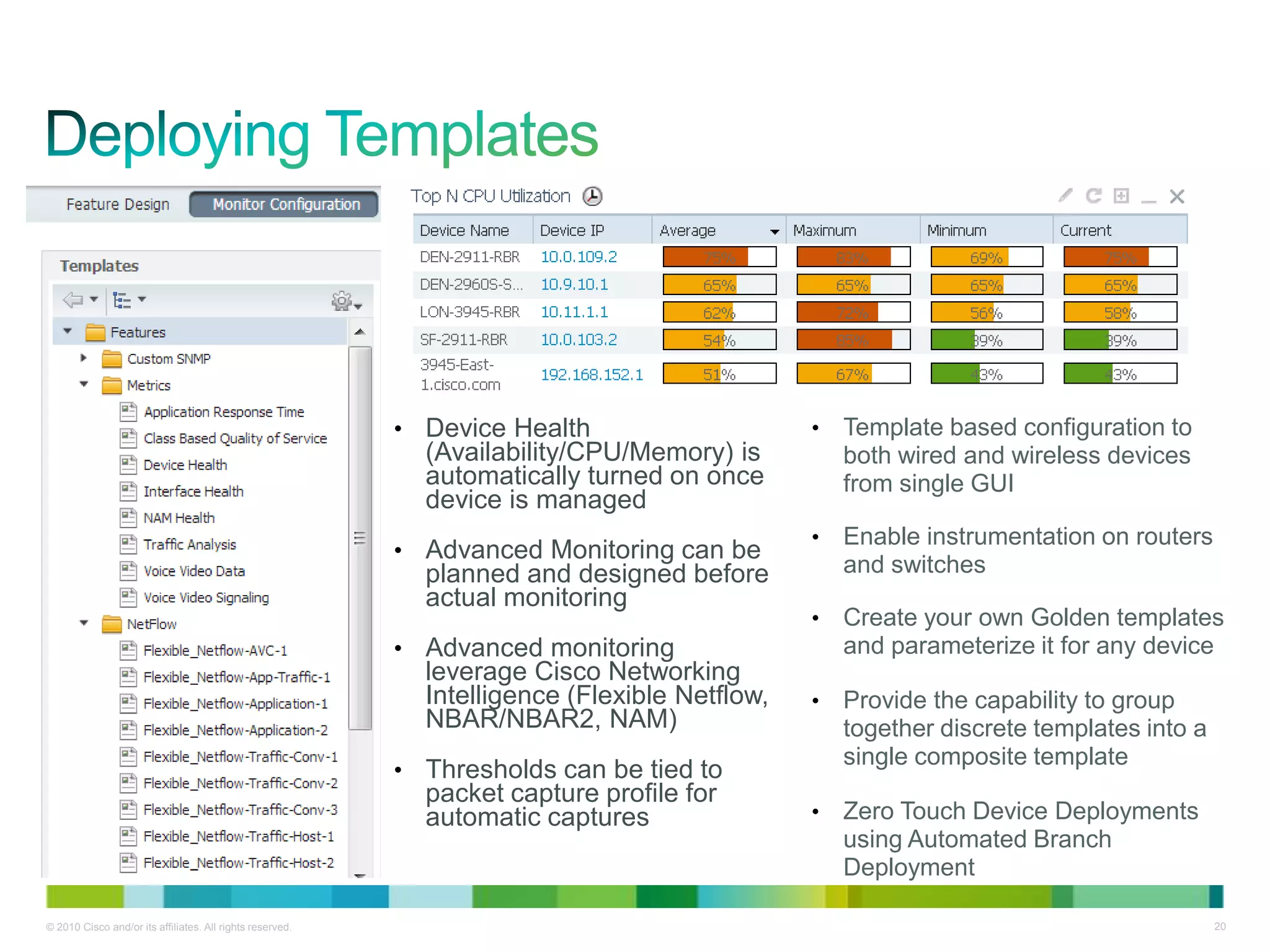
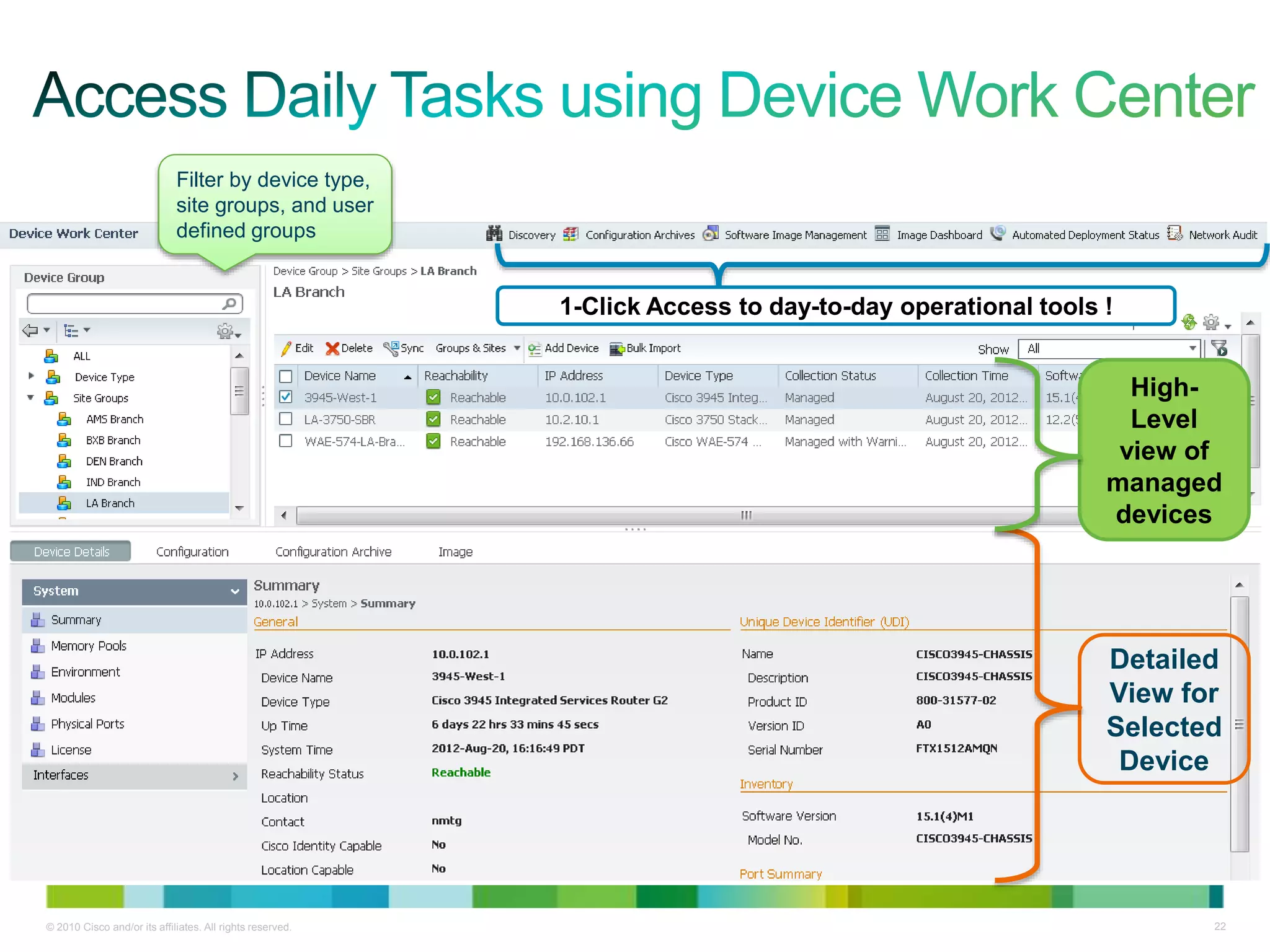
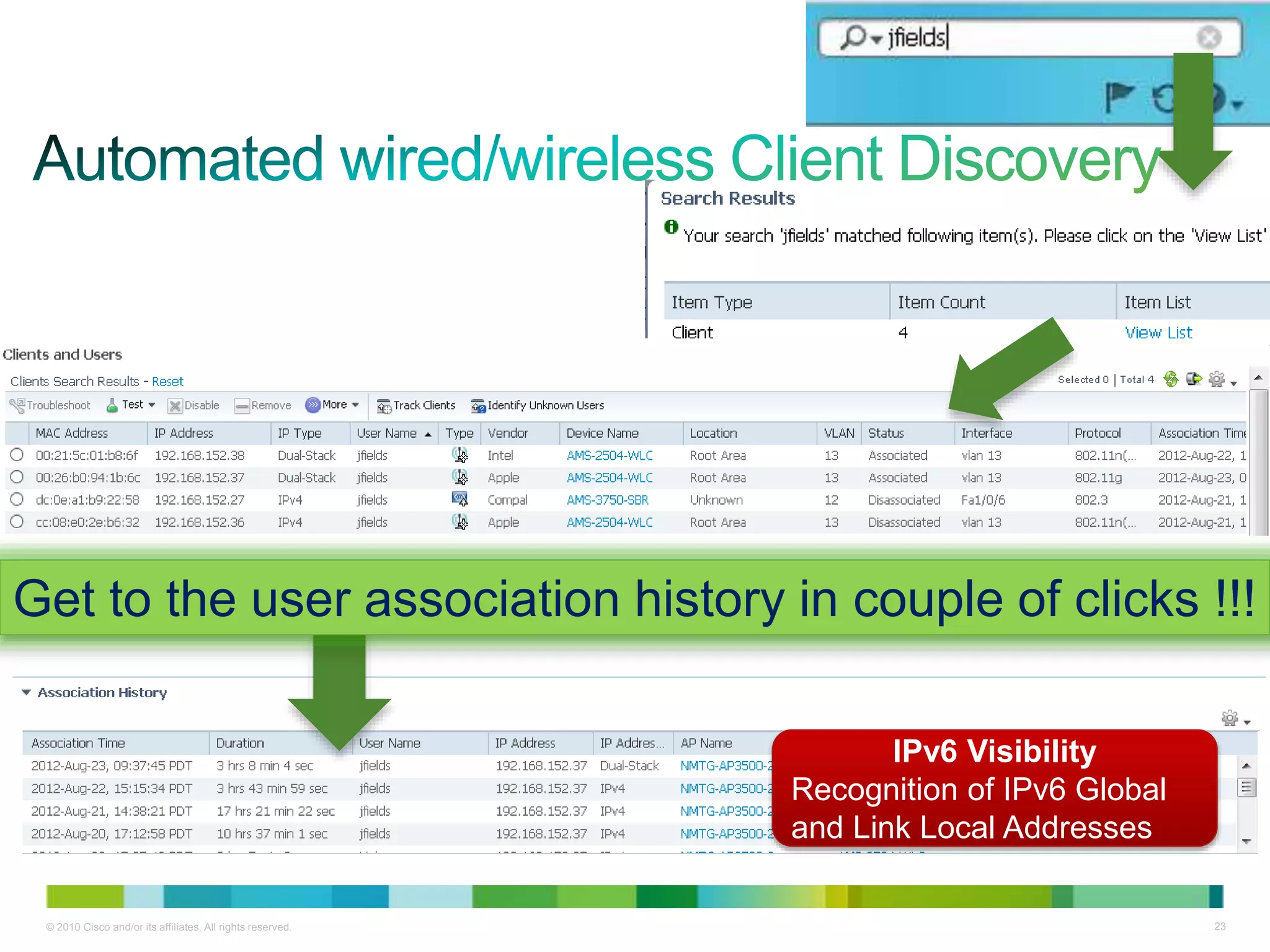
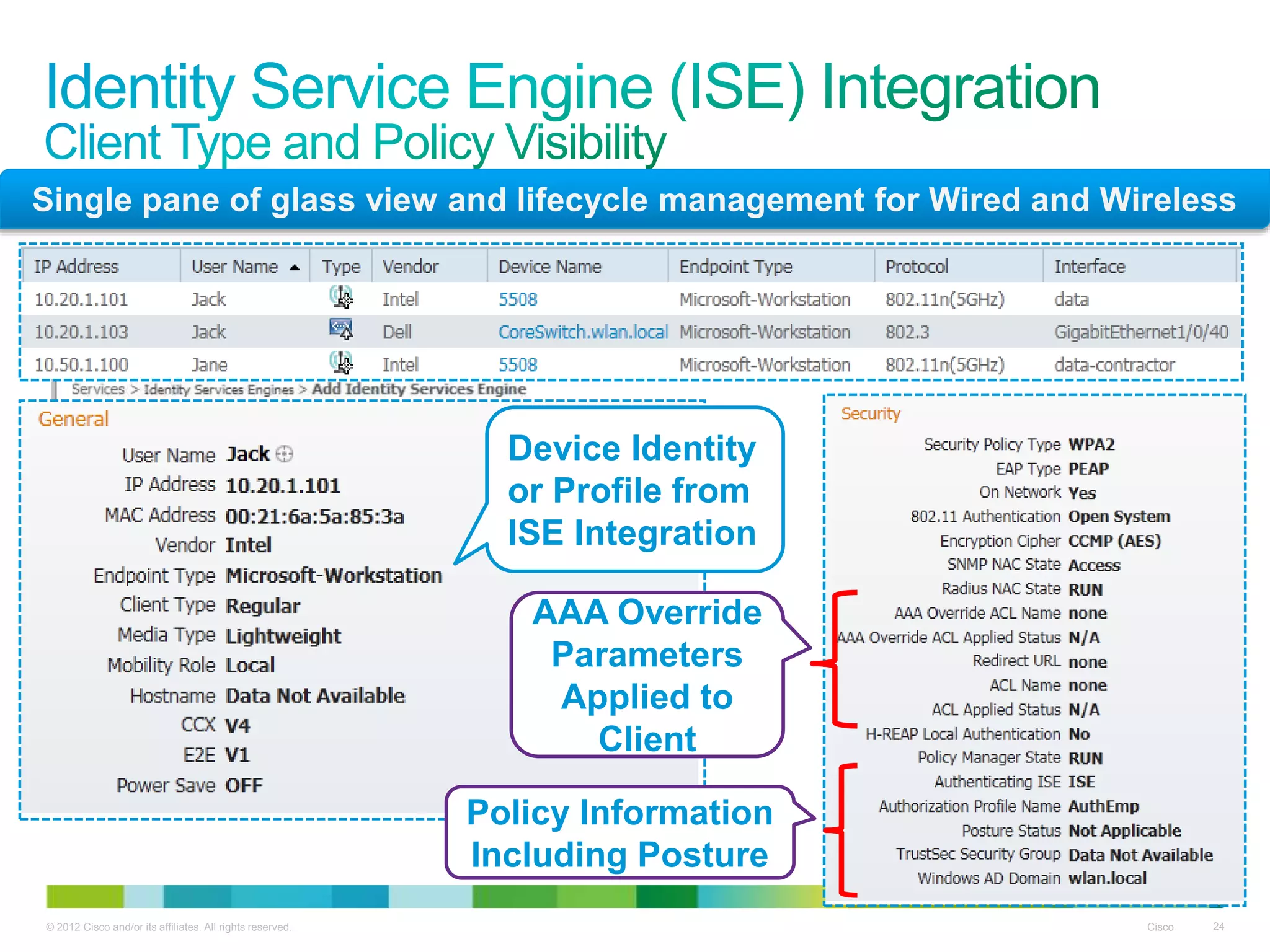
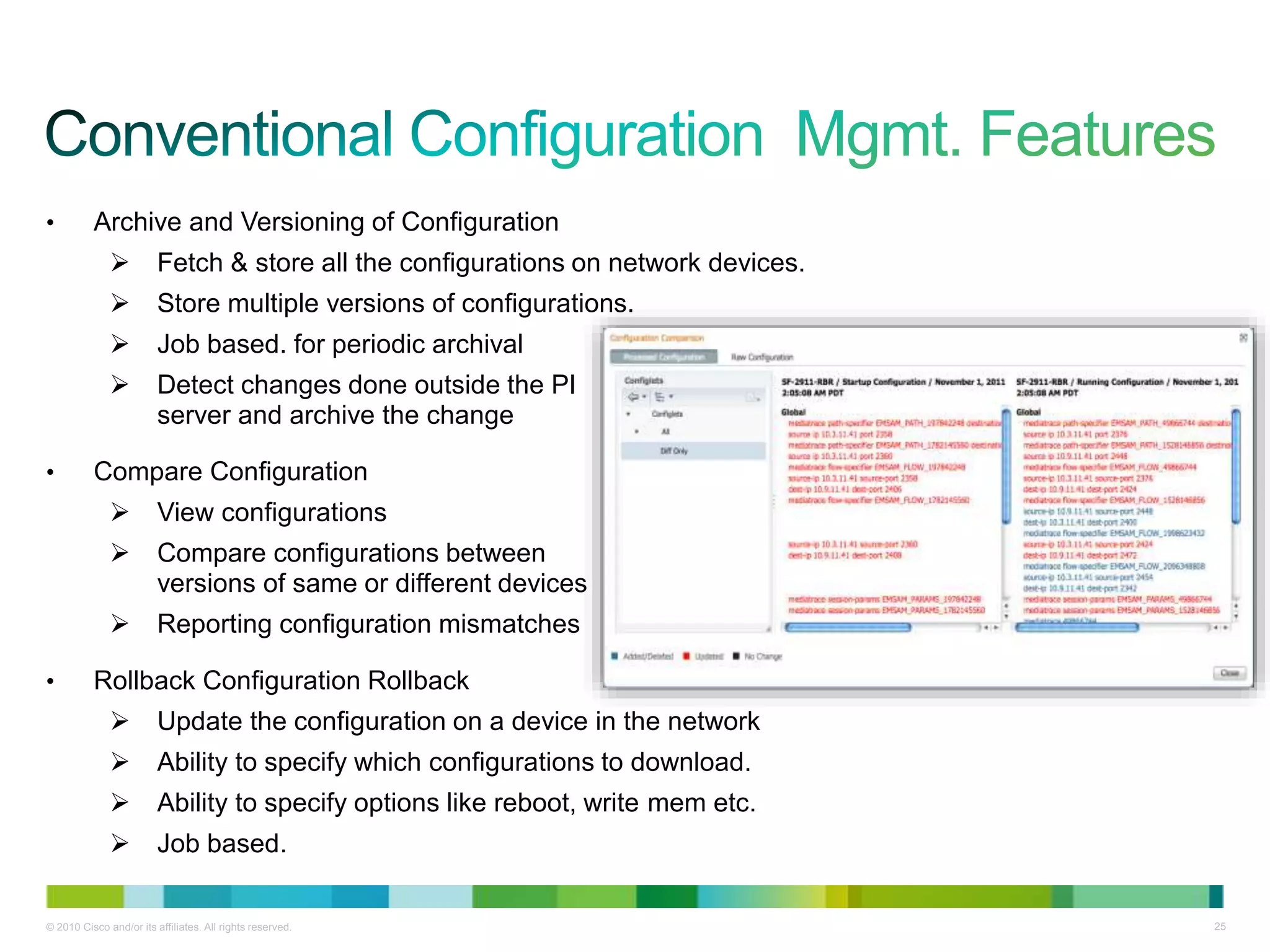
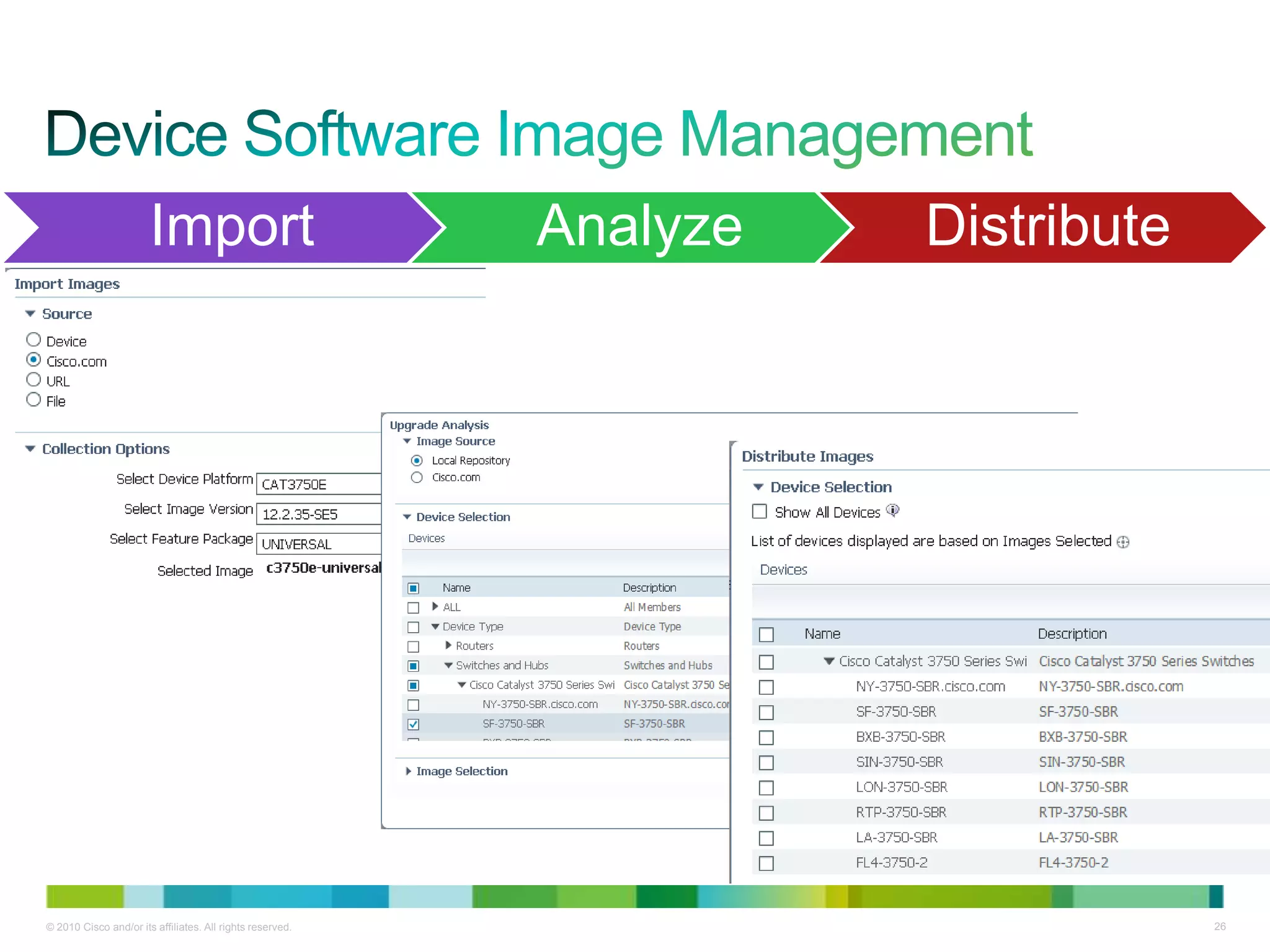
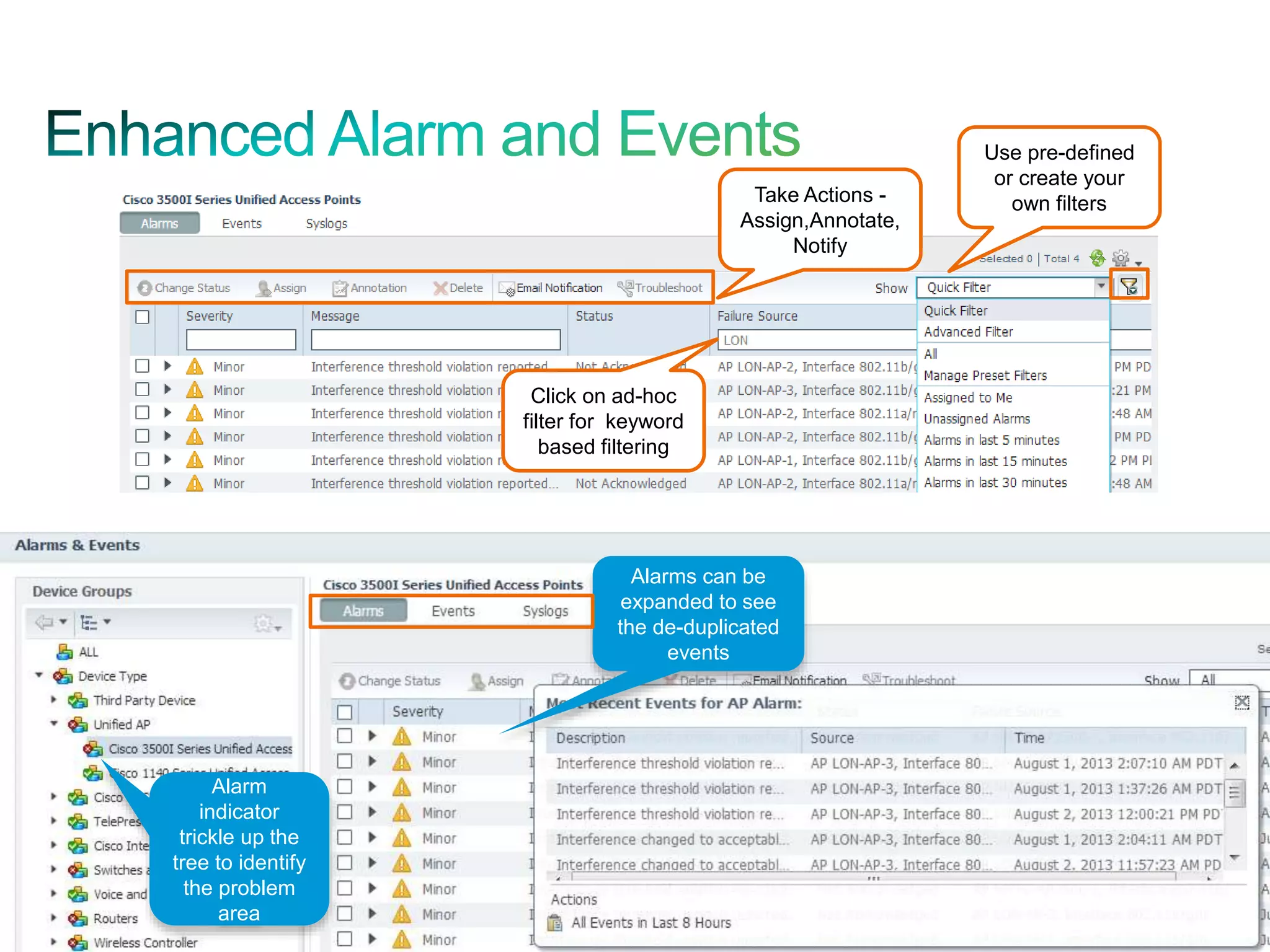
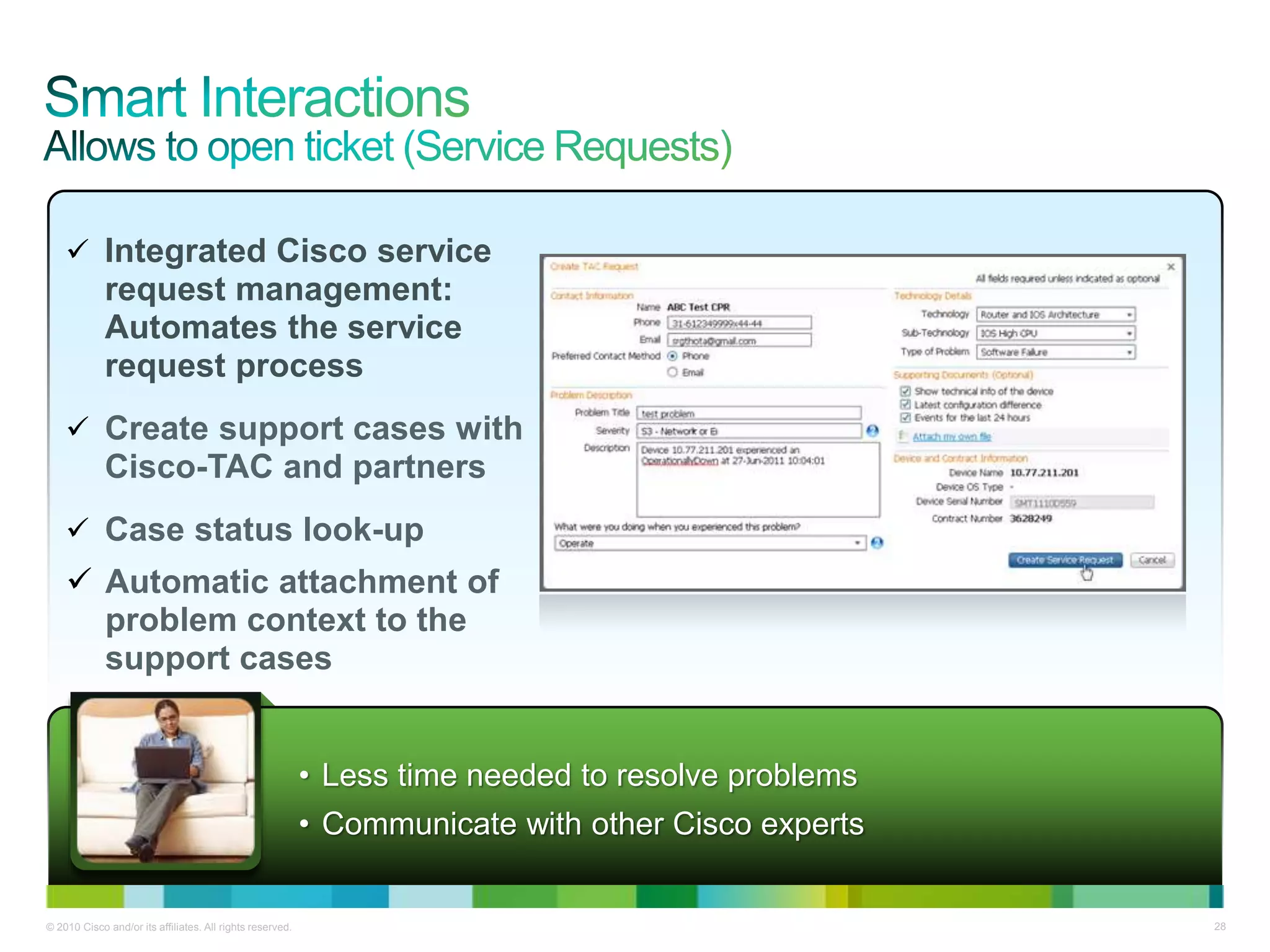
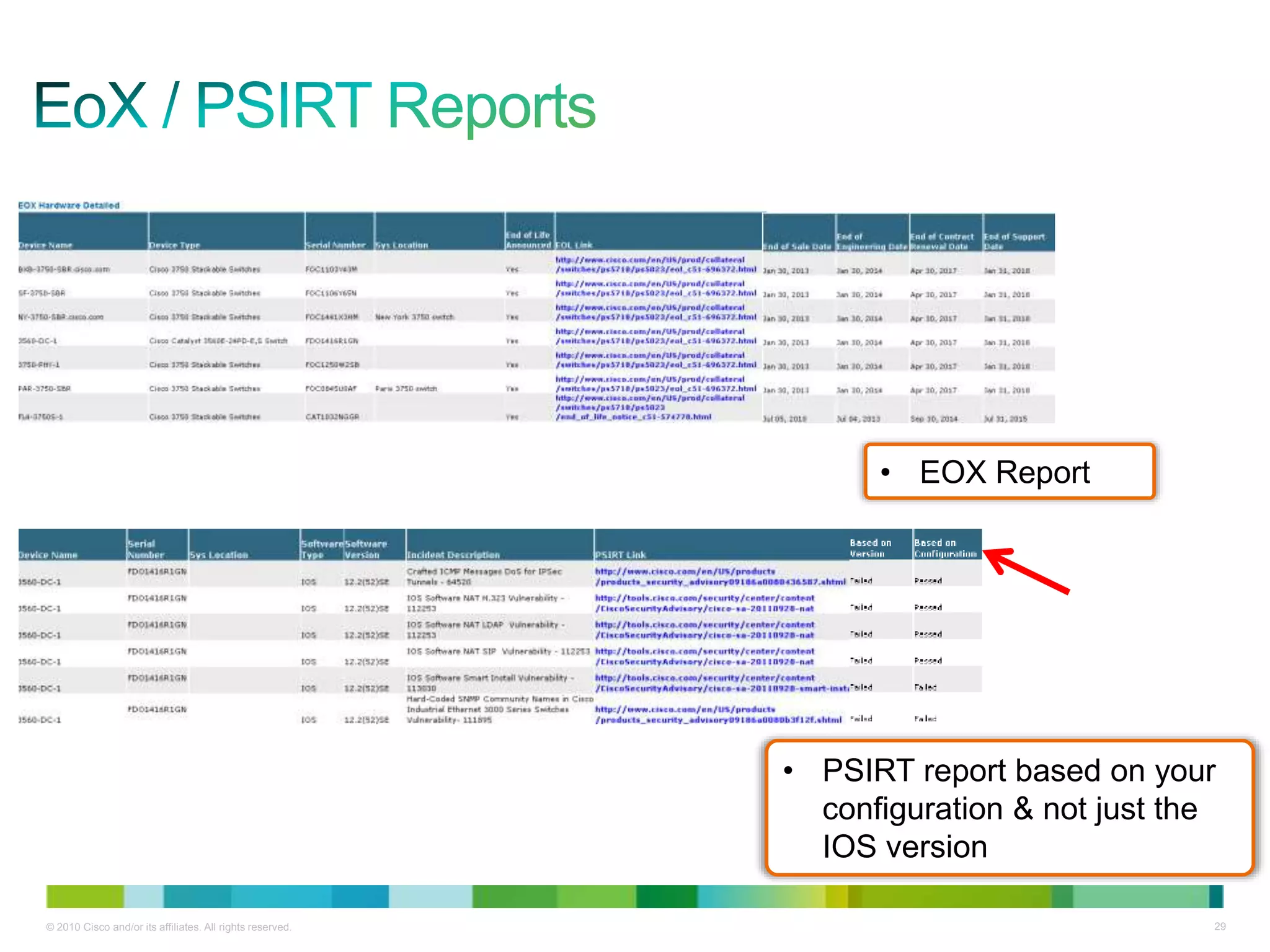
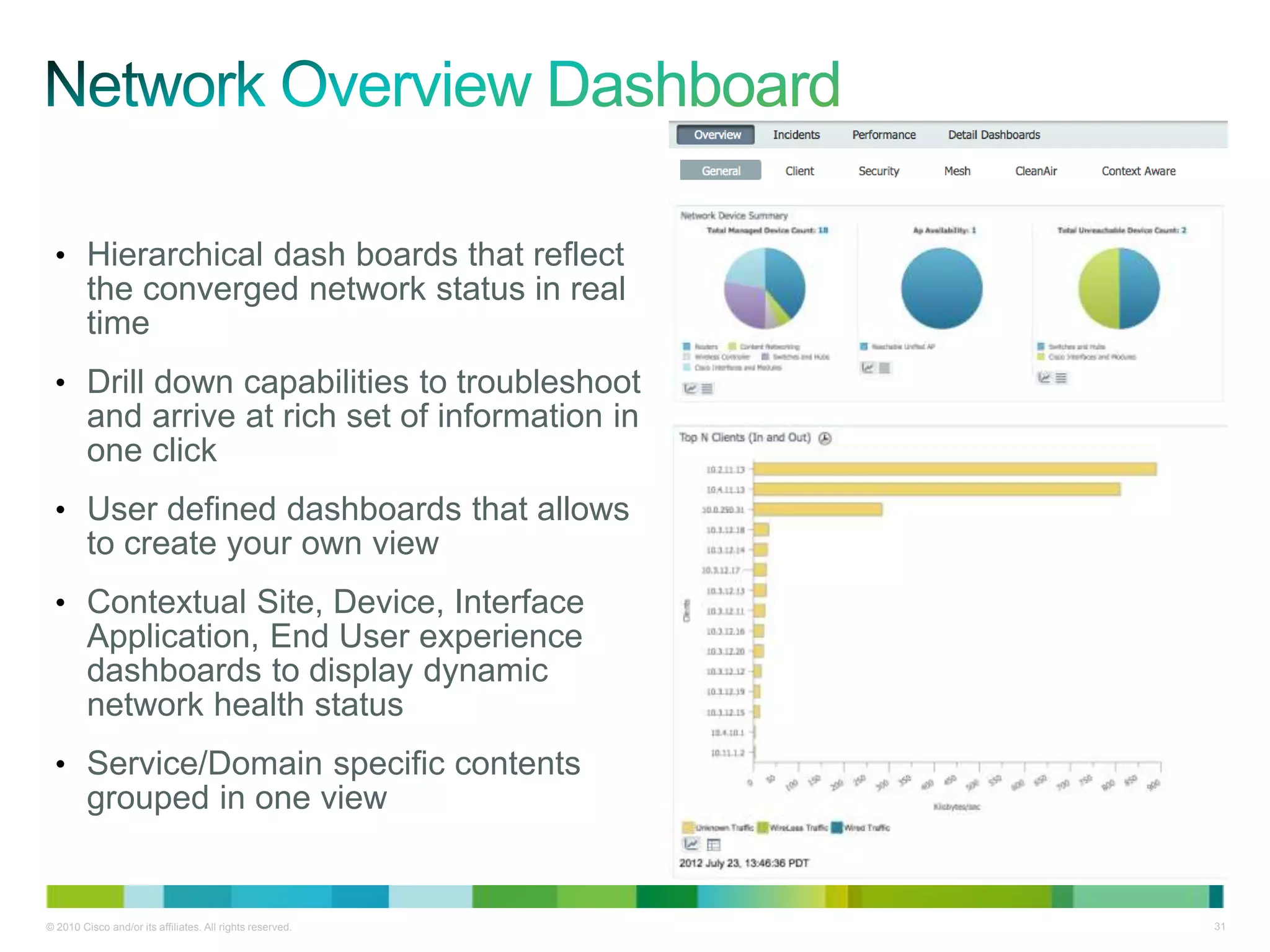
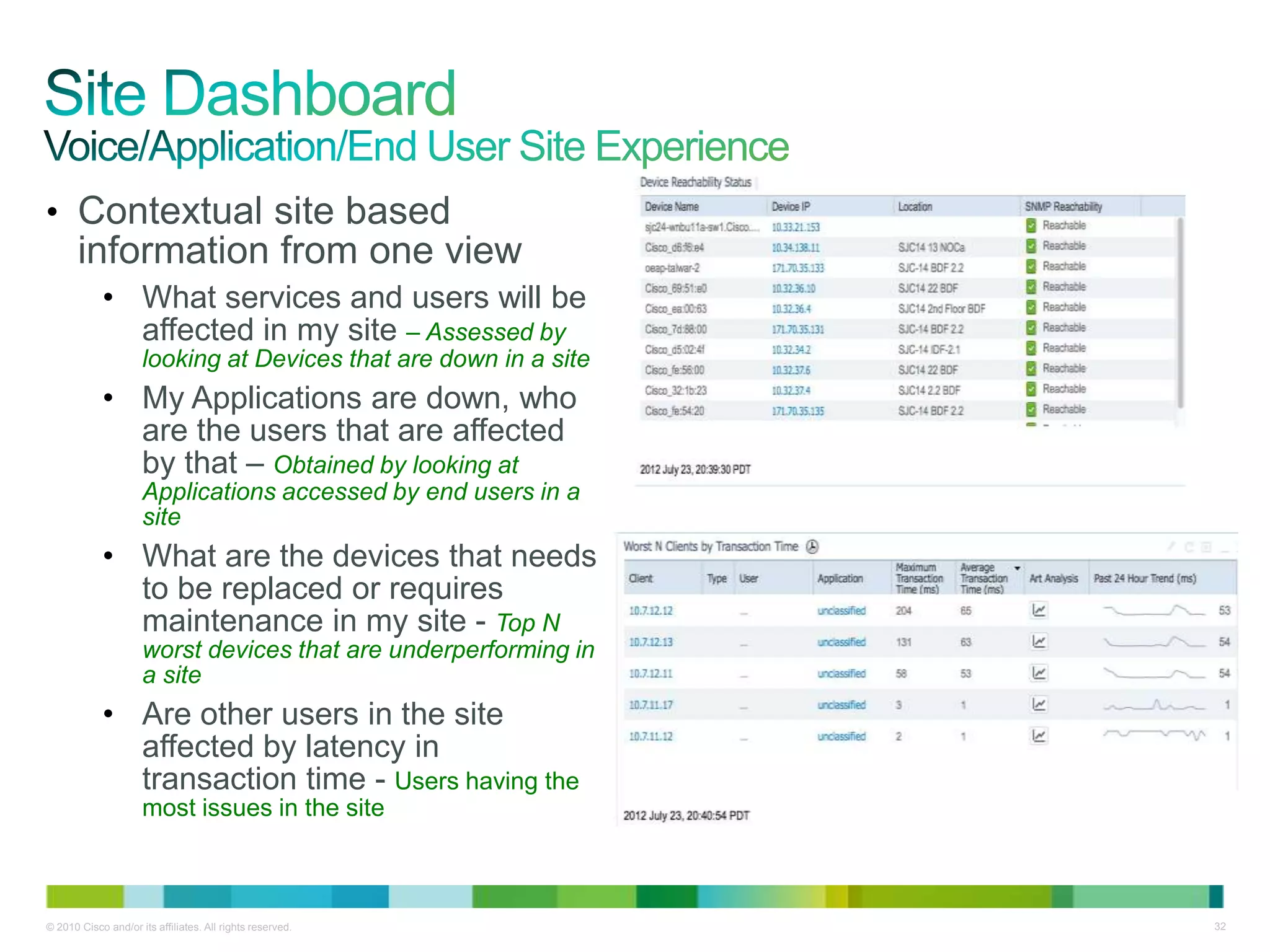
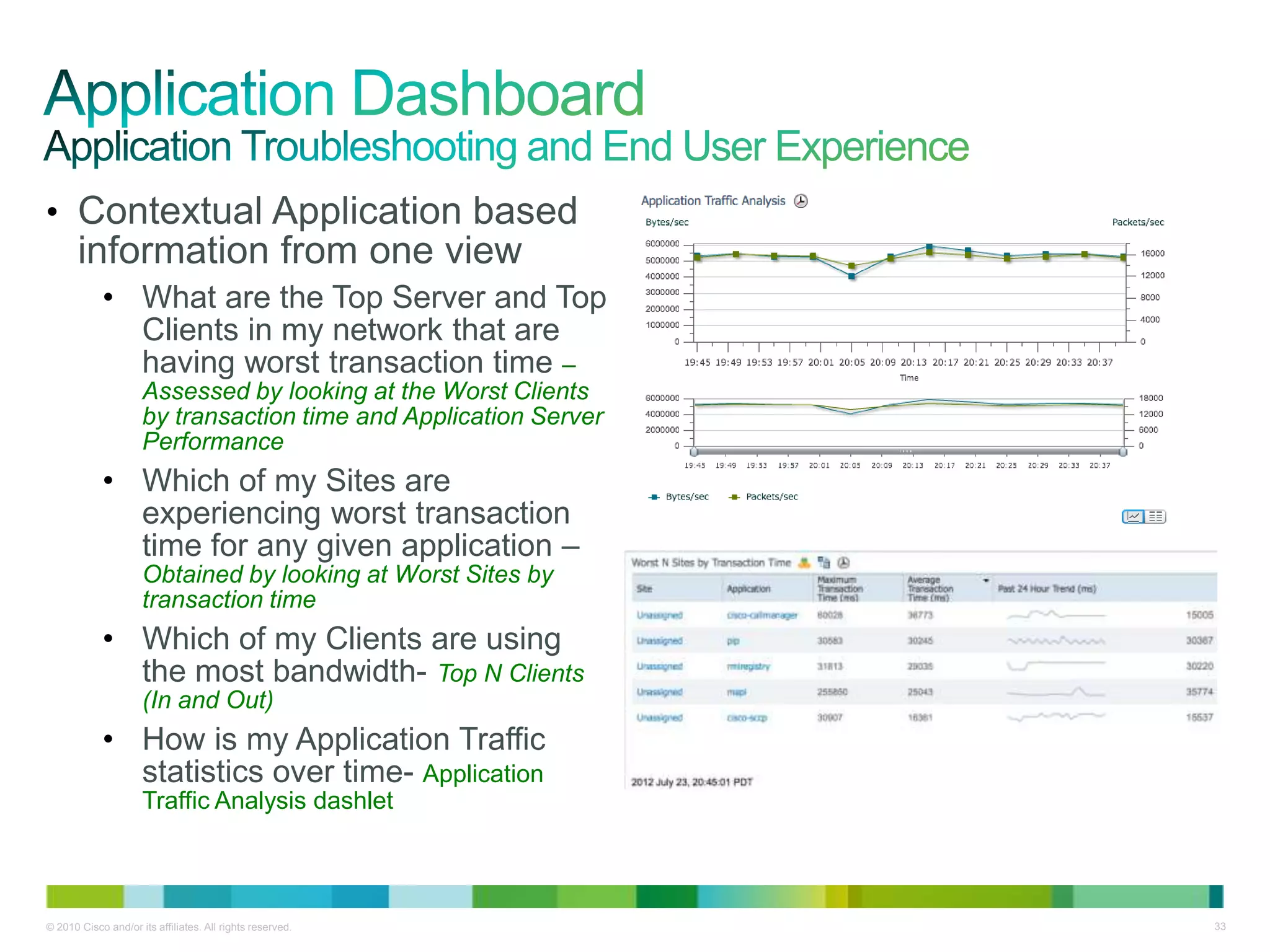
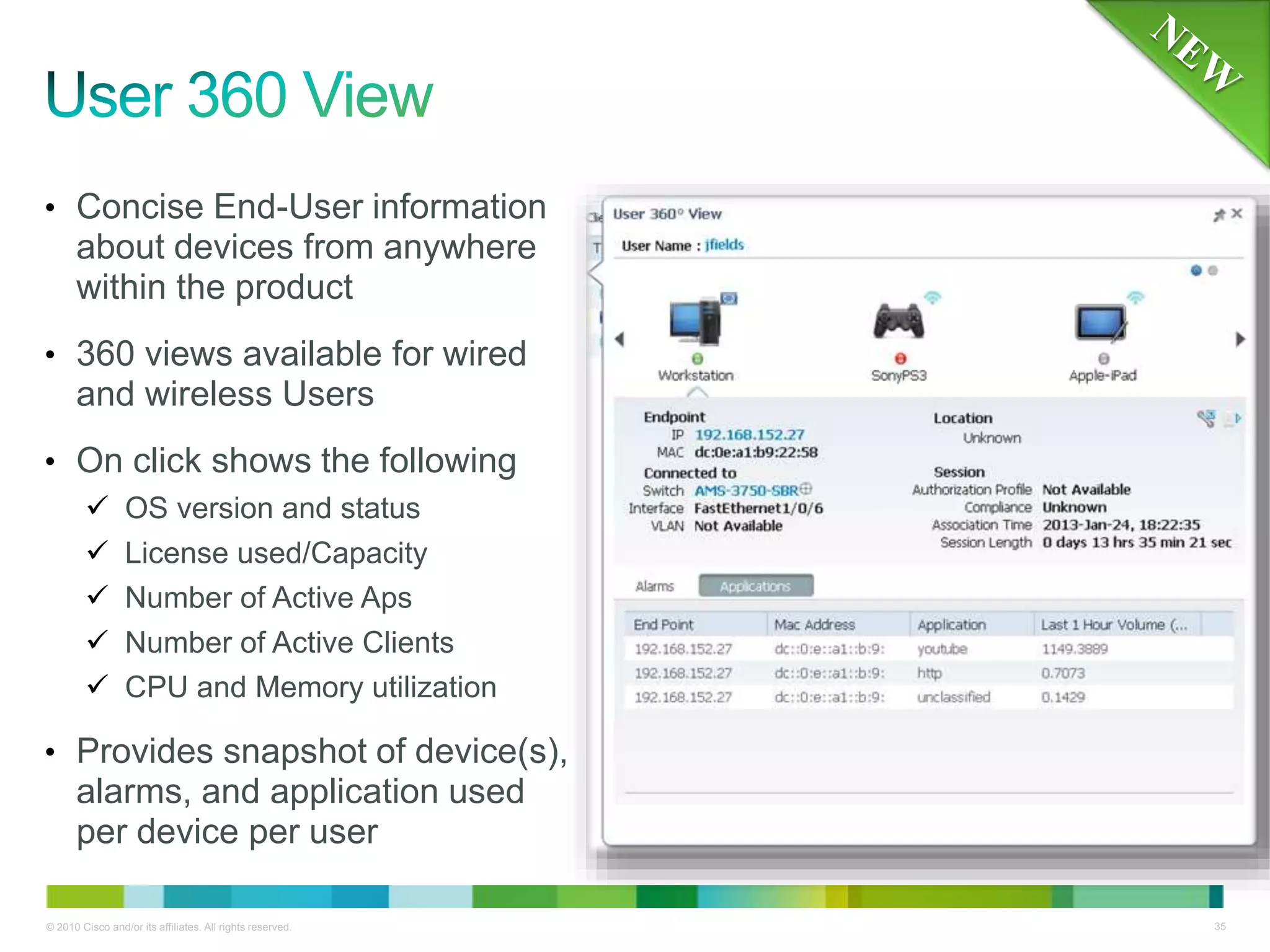
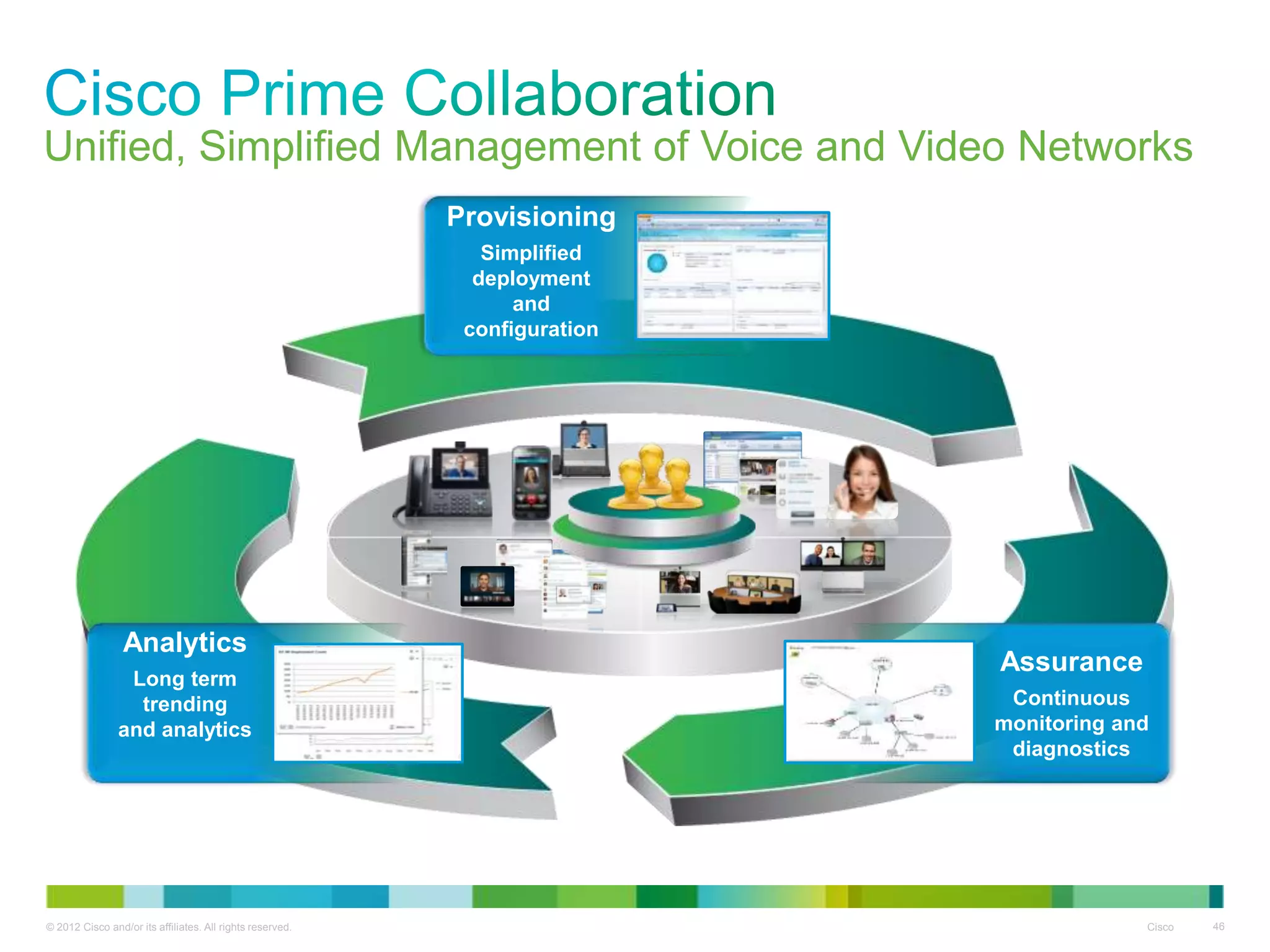
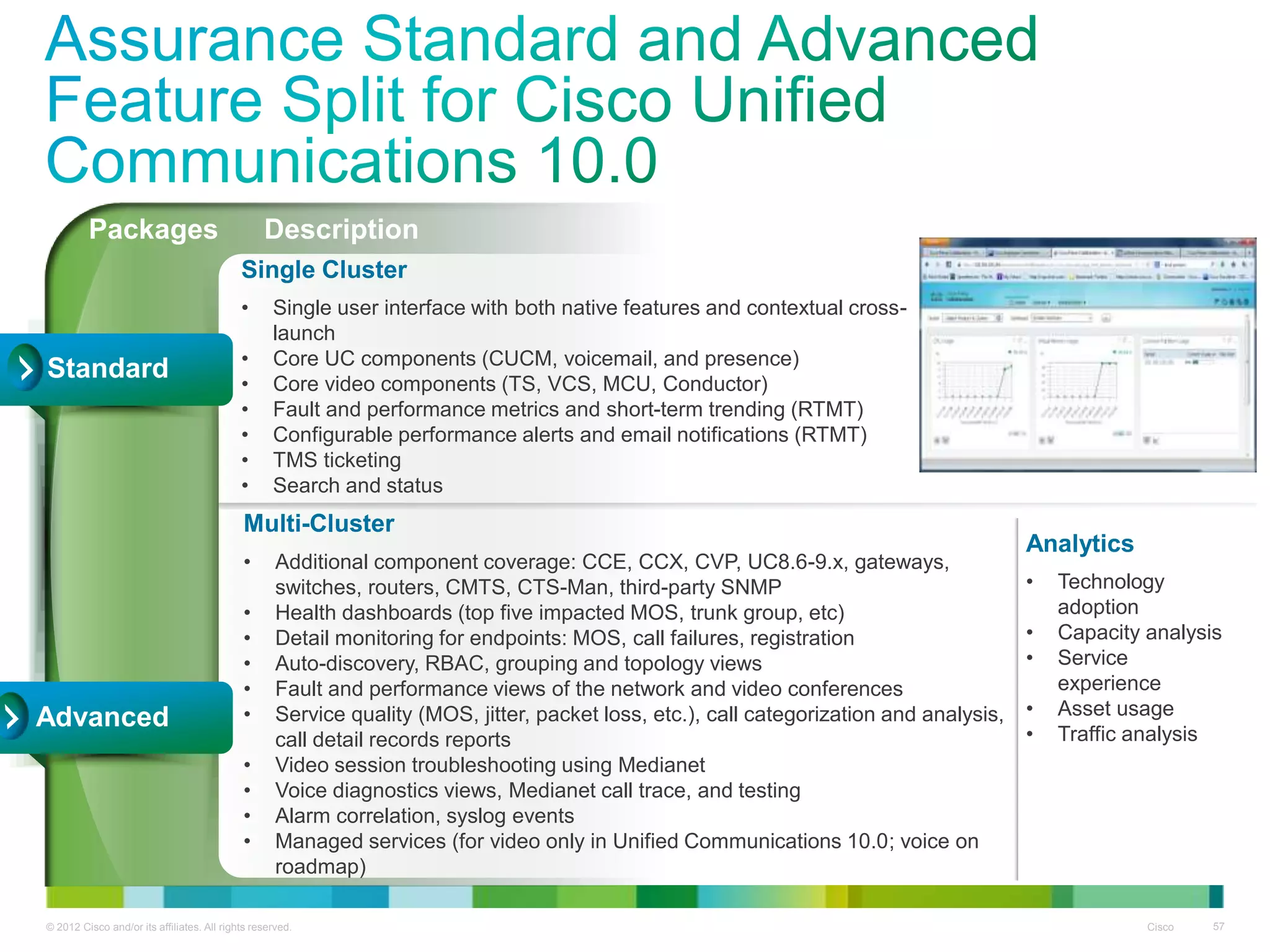
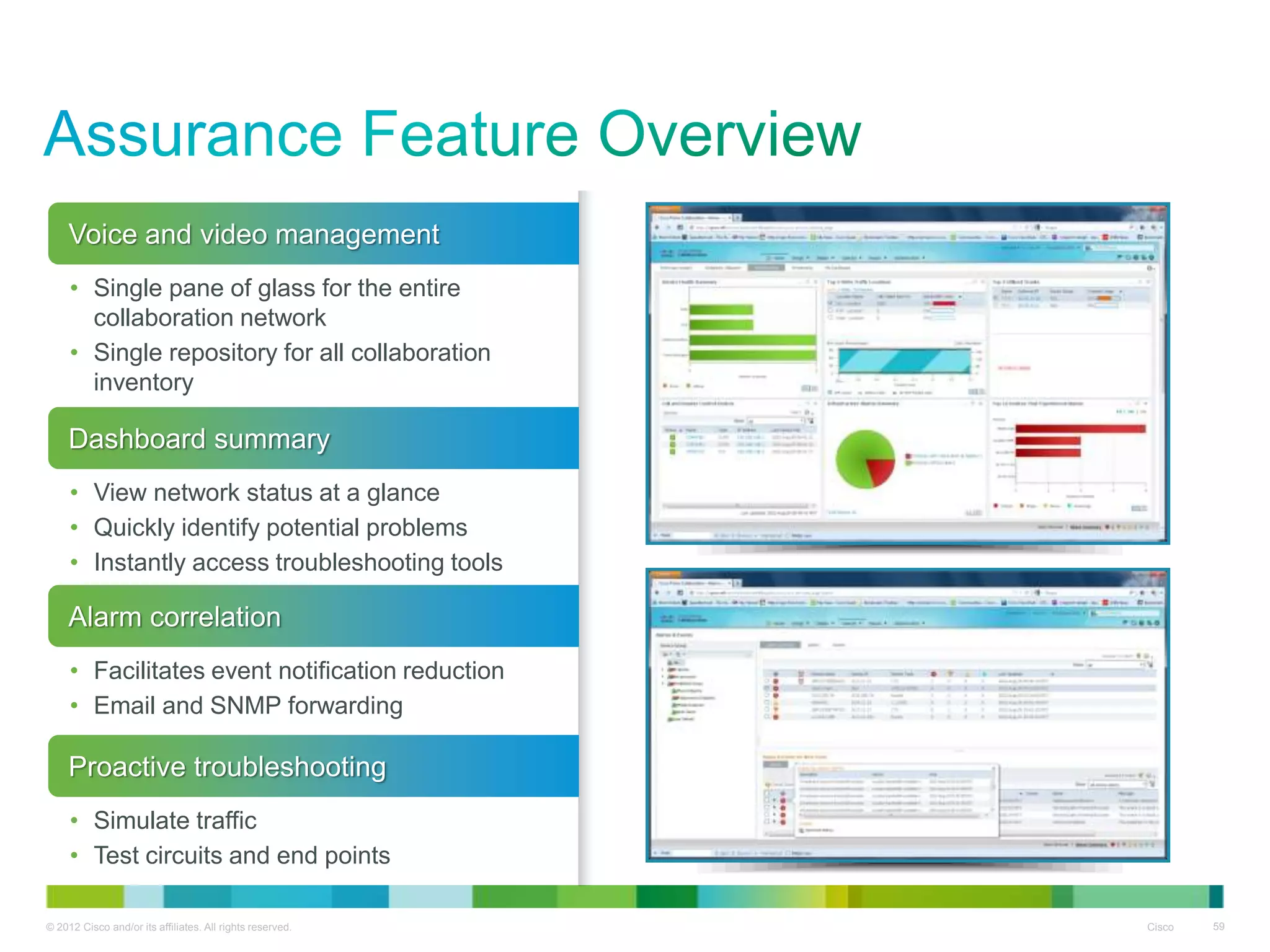
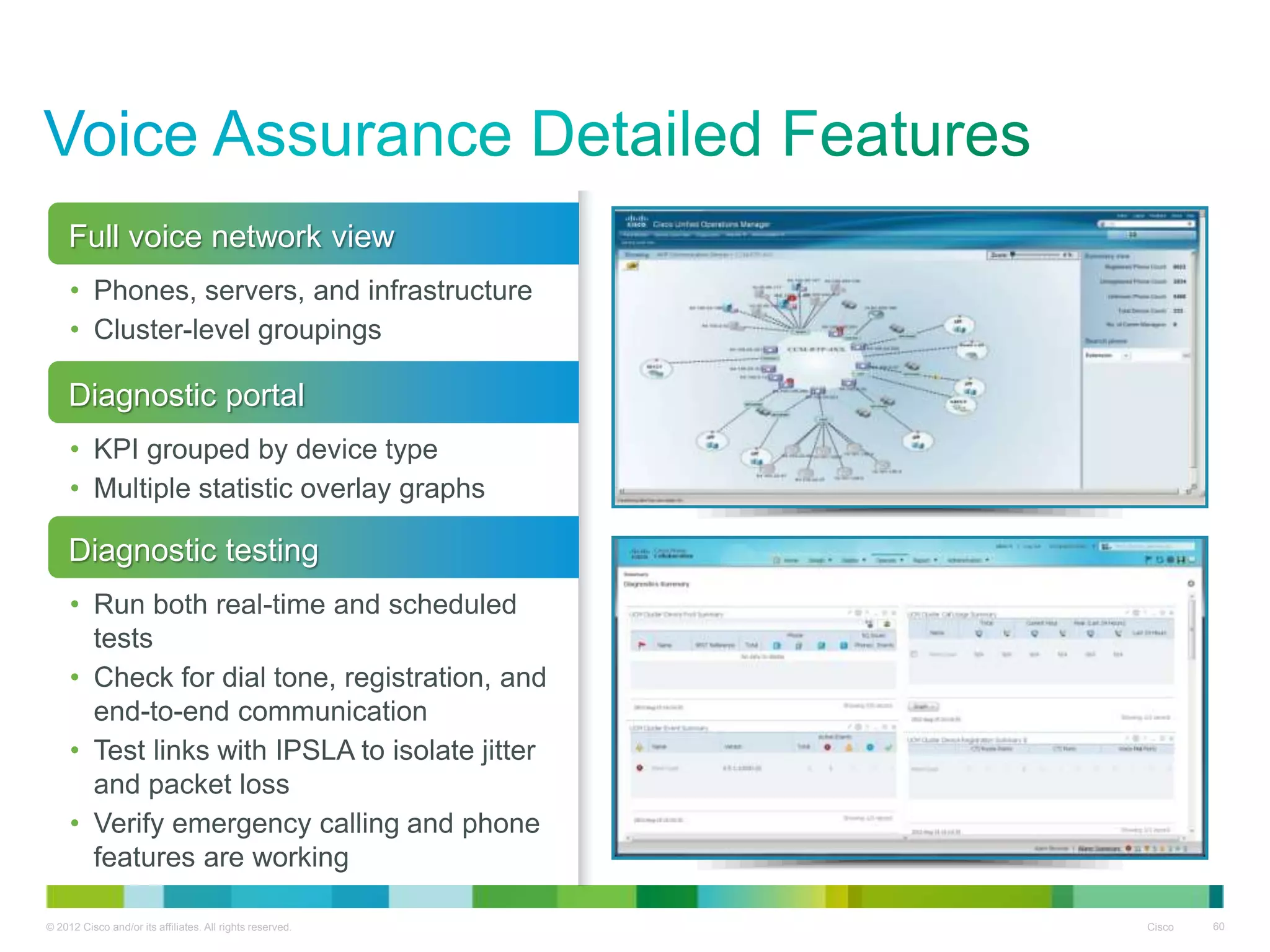
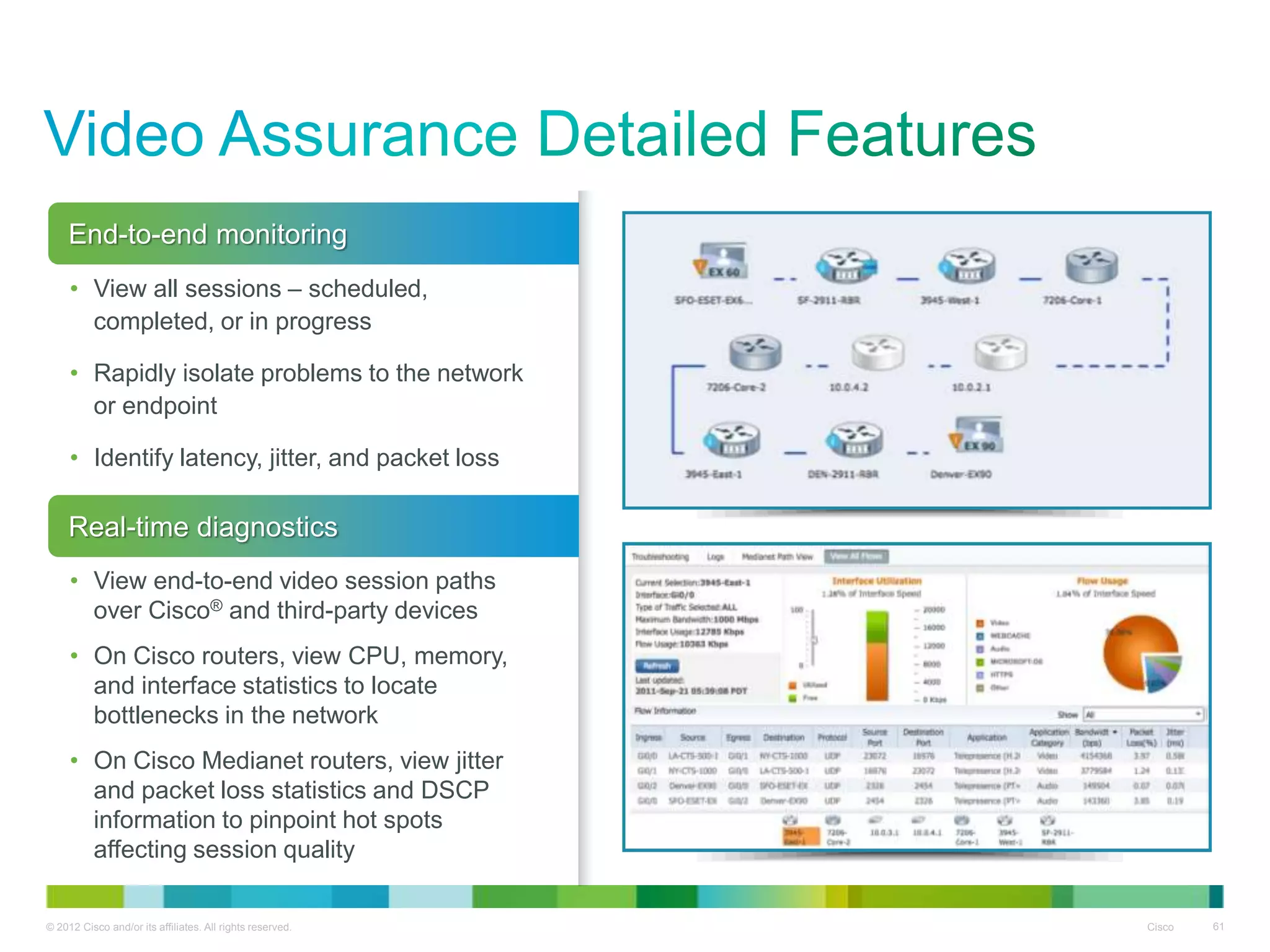
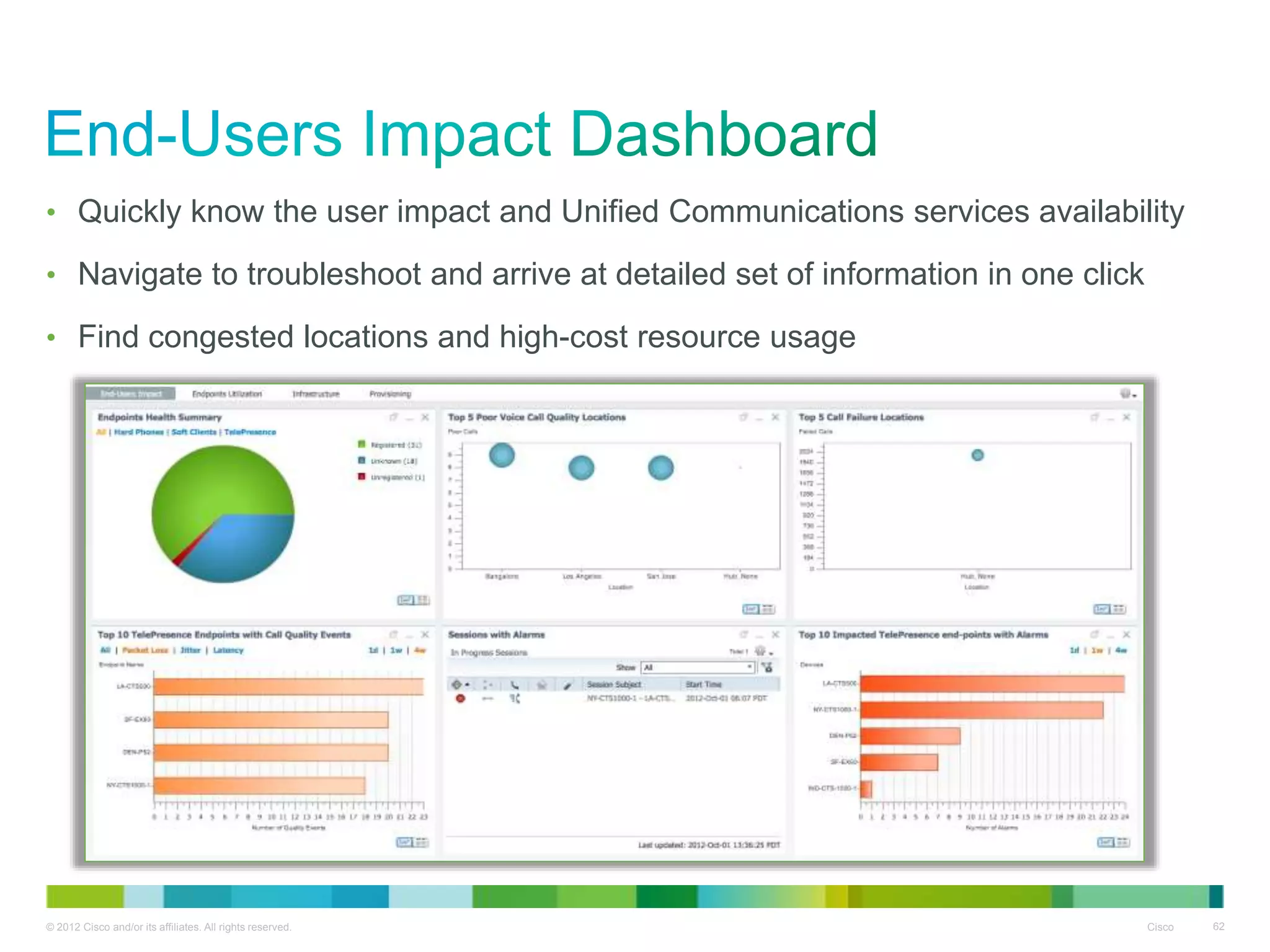
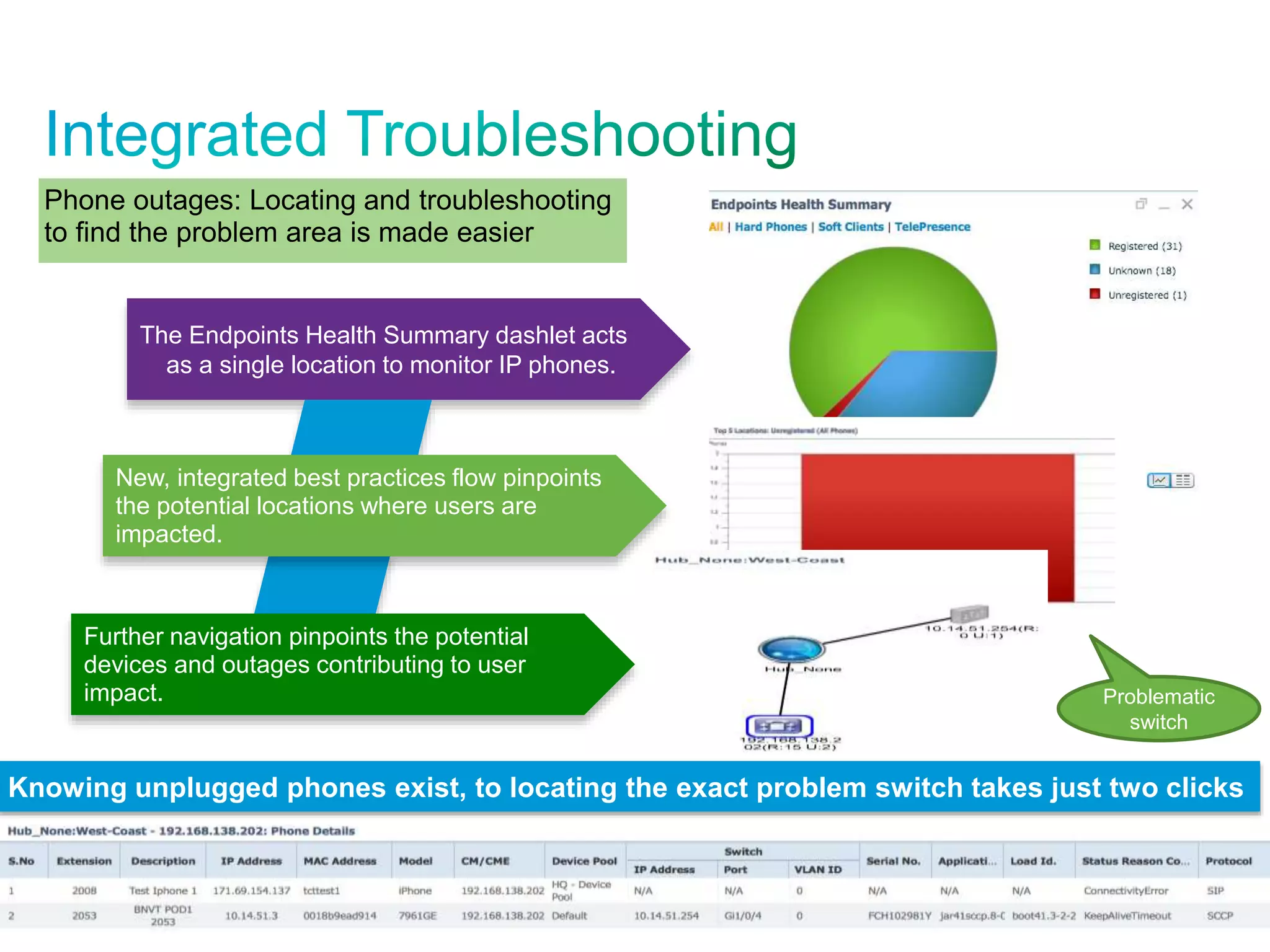
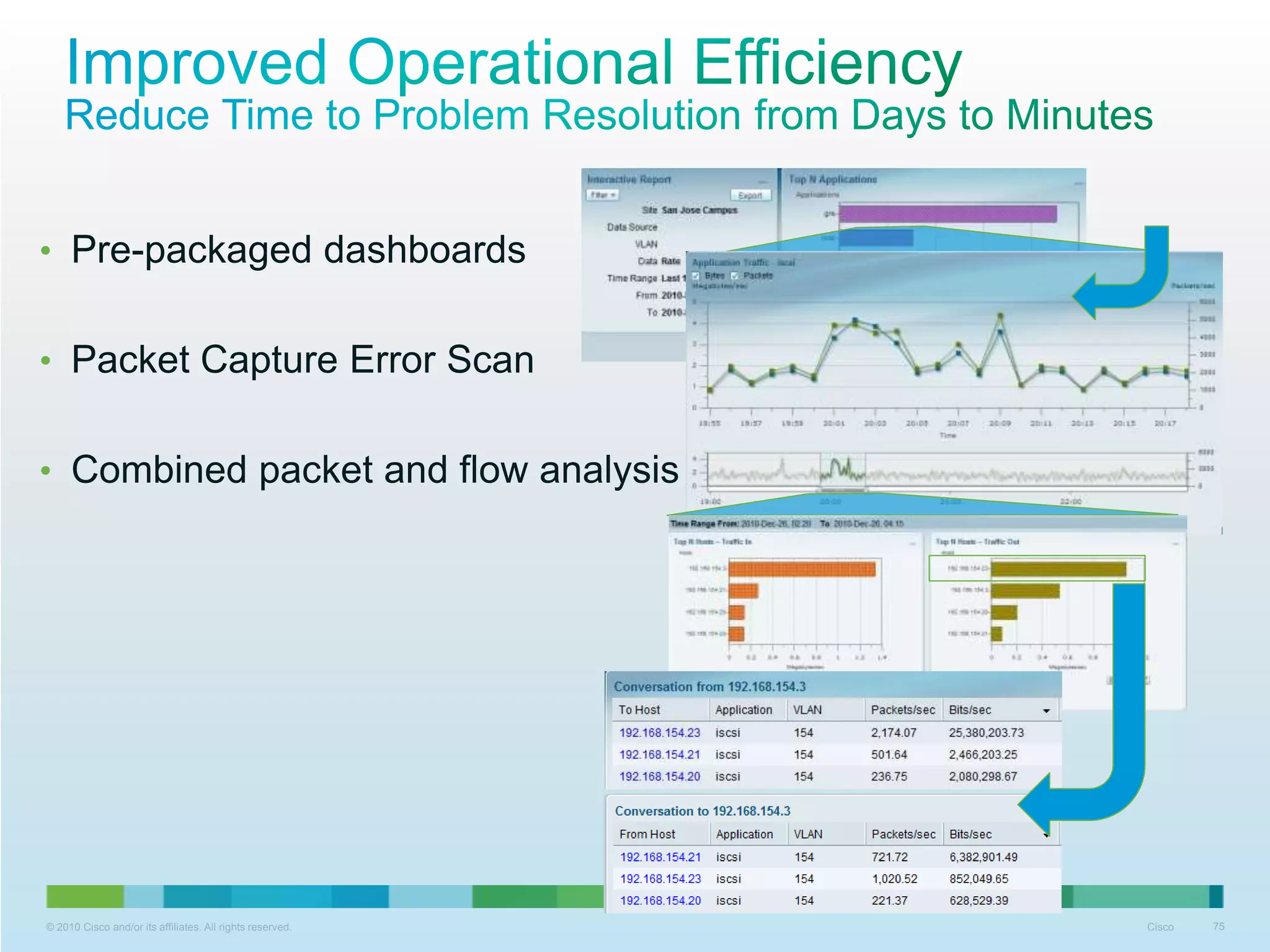
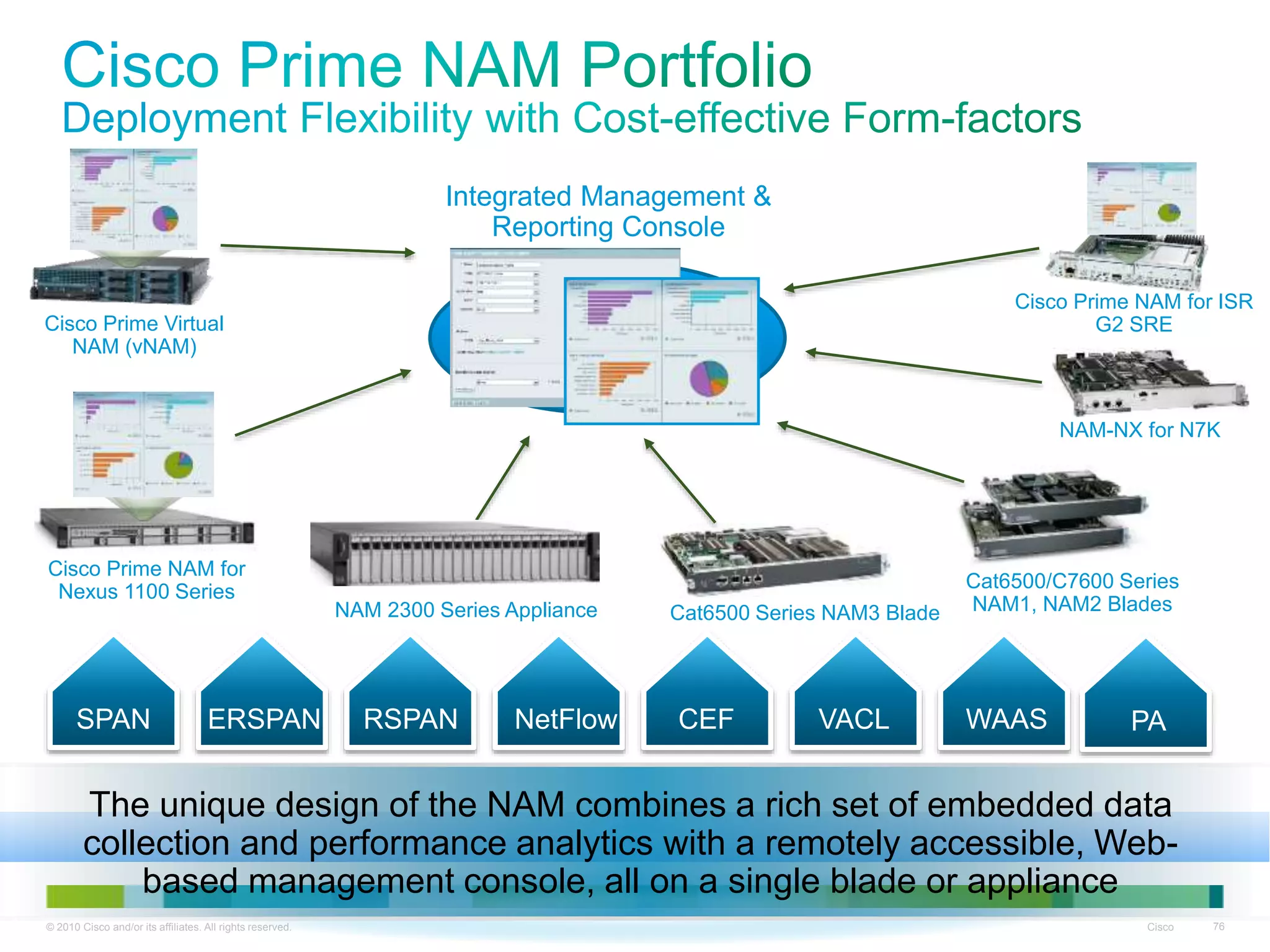
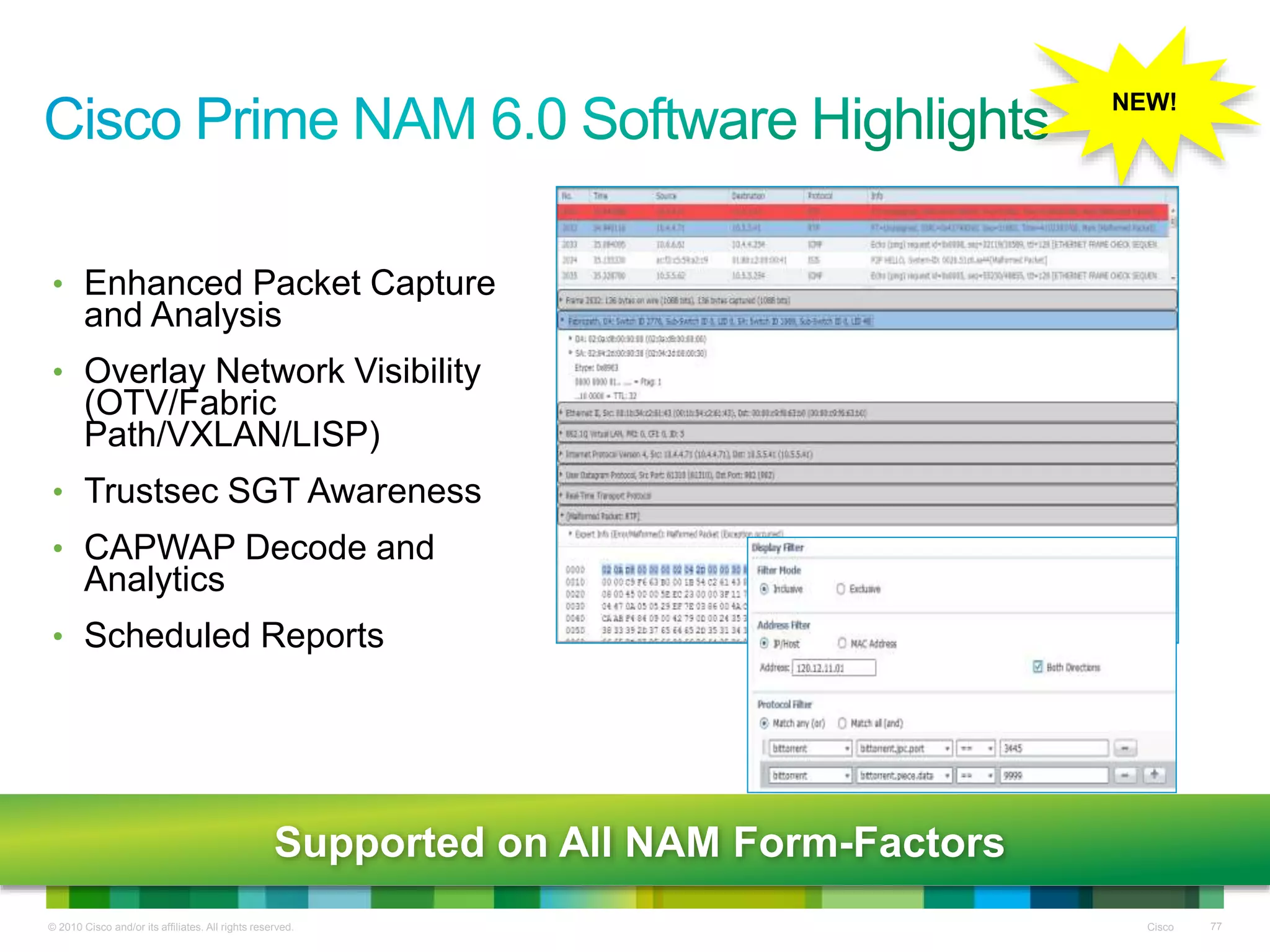
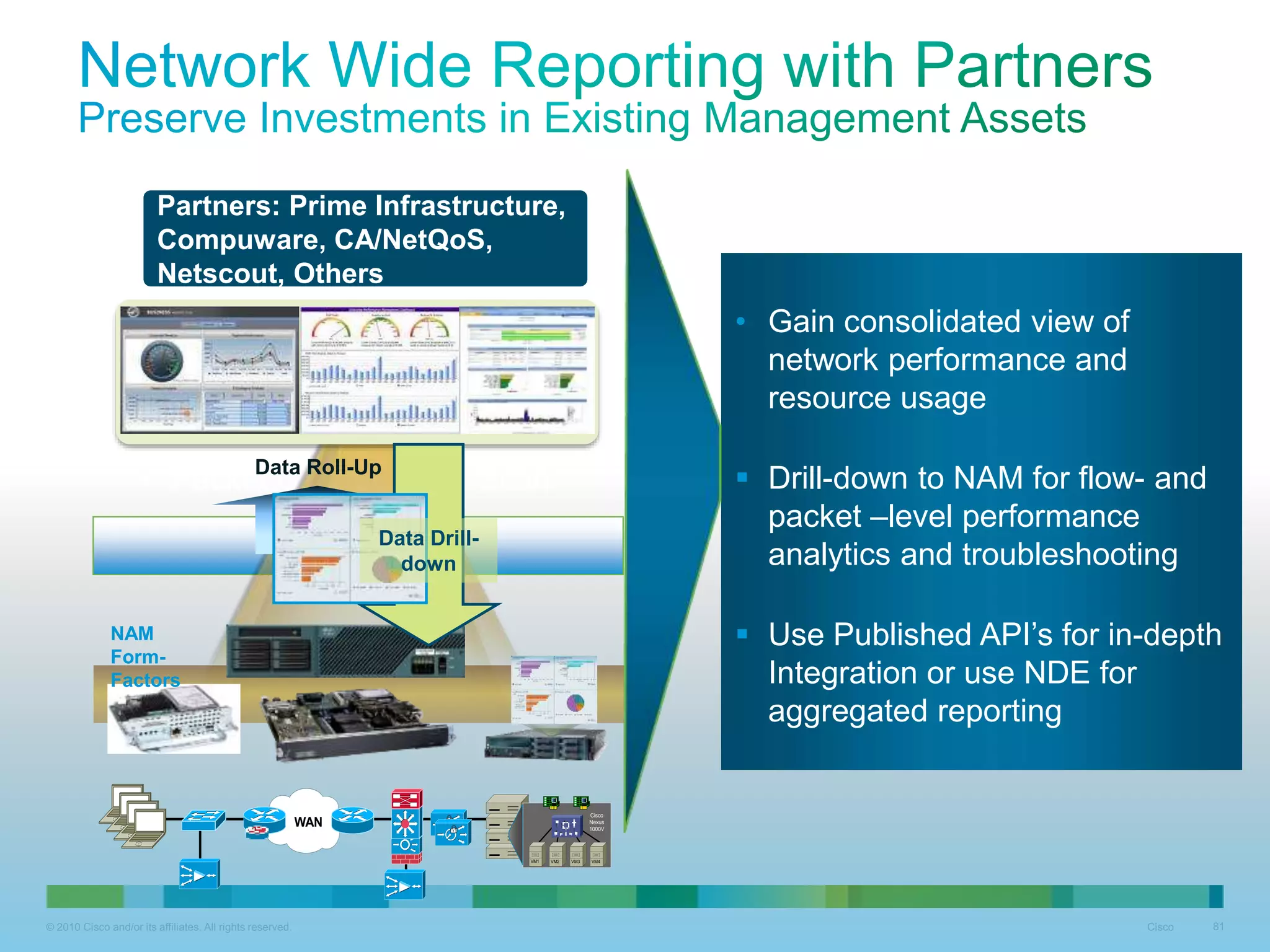
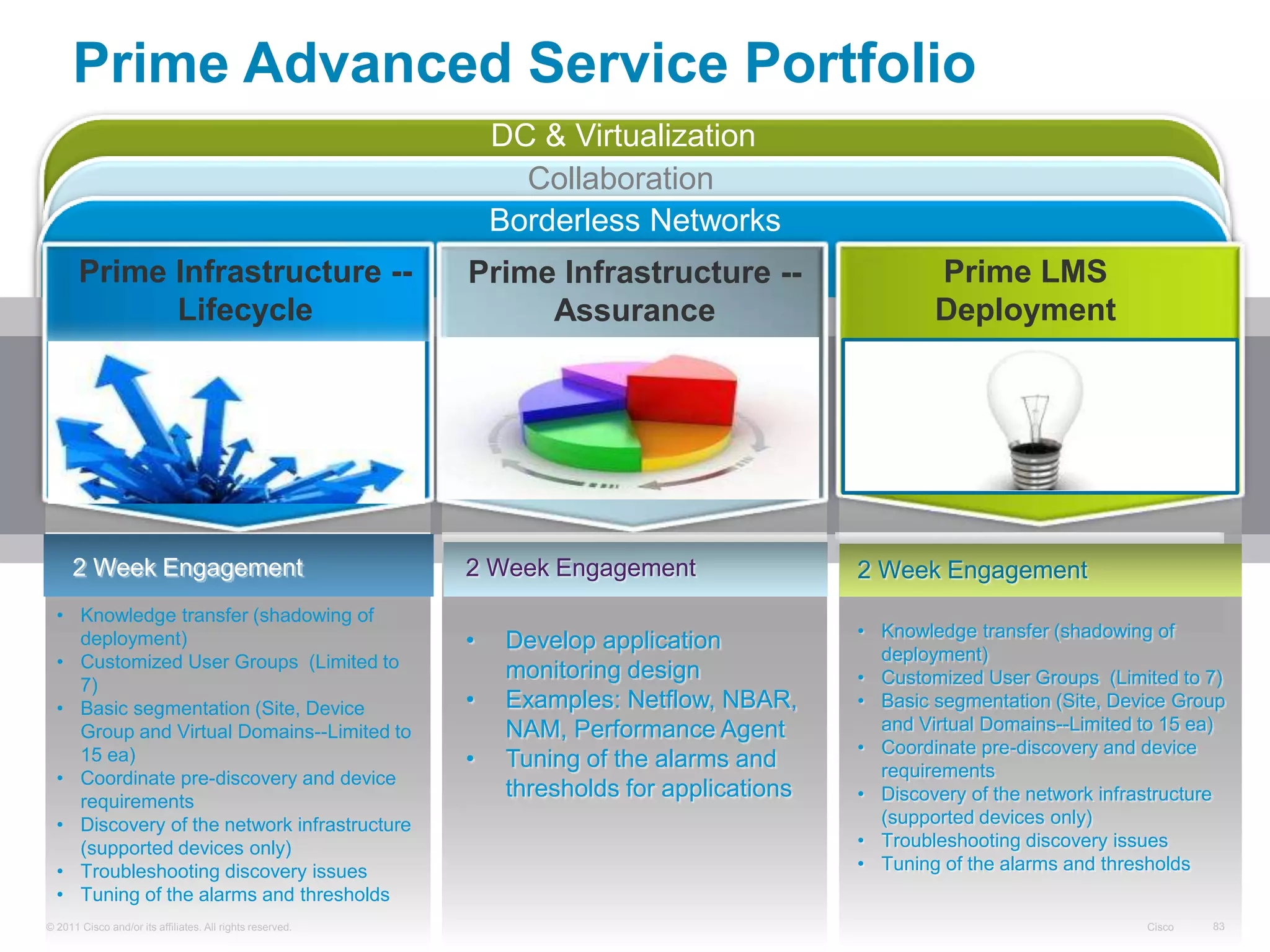
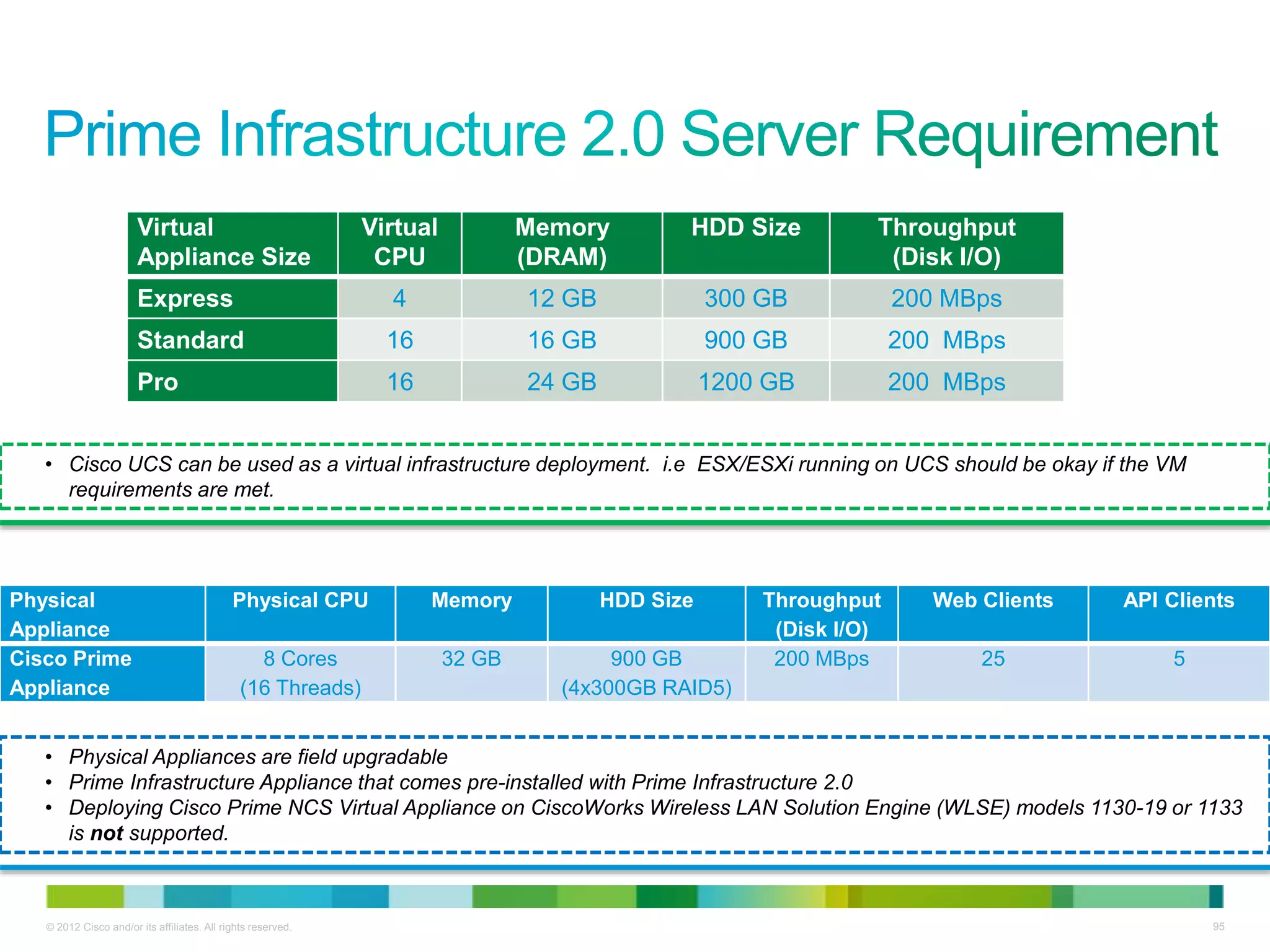
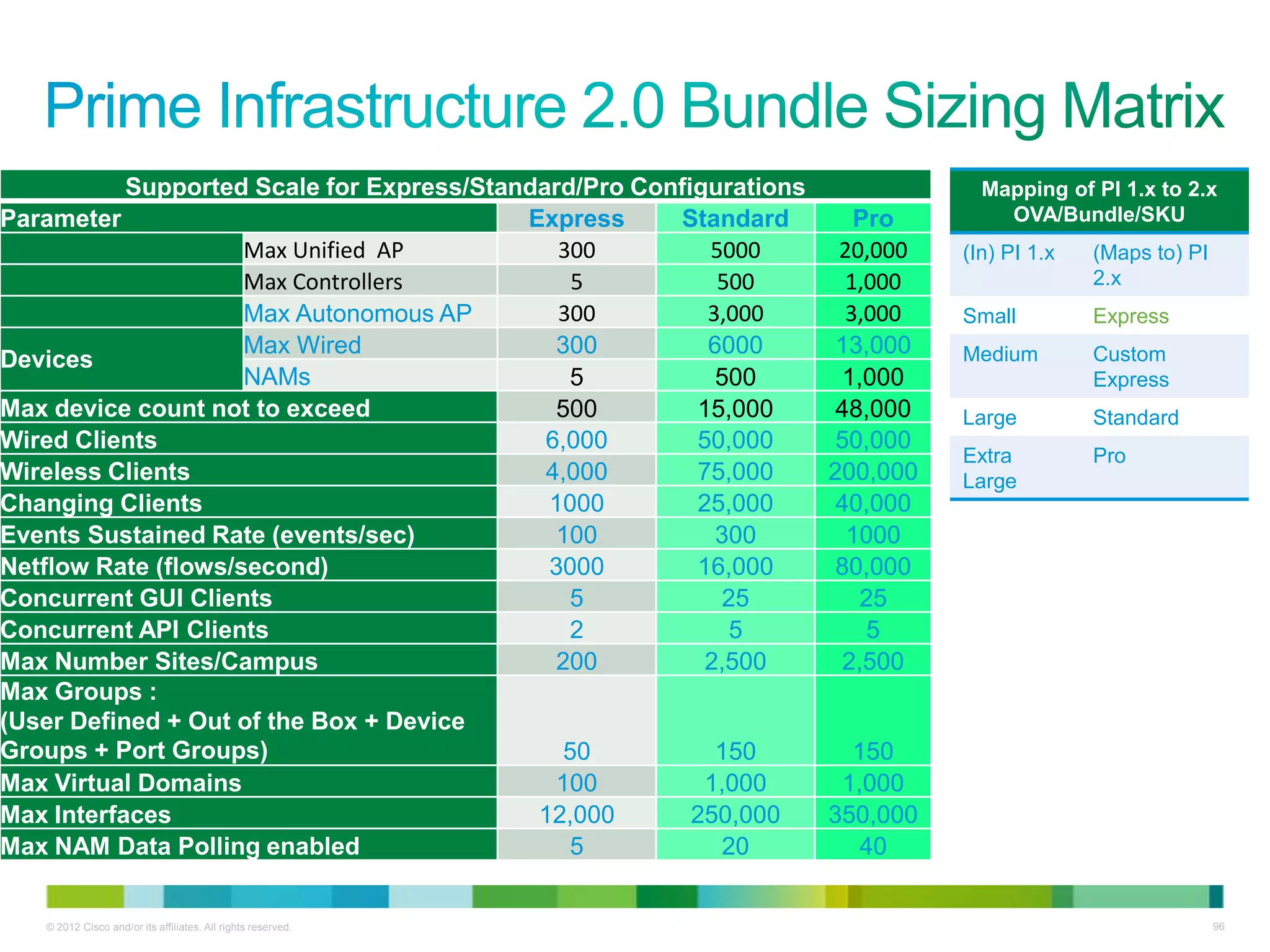
This document discusses Cisco Prime Network Management and its benefits over traditional point-product network management solutions. It provides an overview of Cisco Prime's integrated workflows, common user experience, consolidated management capabilities, and support for the full device lifecycle. Key features highlighted include comprehensive device manageability, assurance of application experience and visibility, simplified deployment of Cisco devices, and support for network lifecycle management.