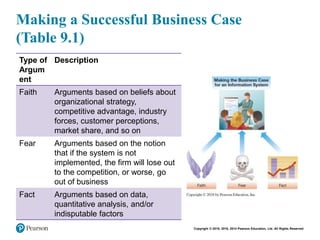
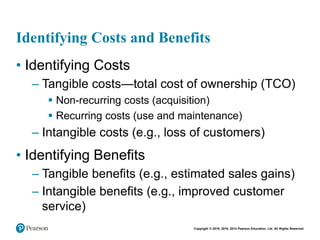
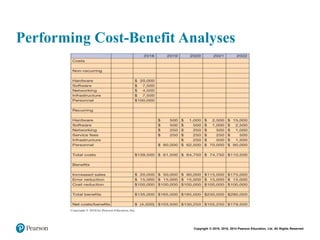
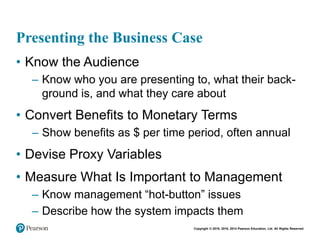
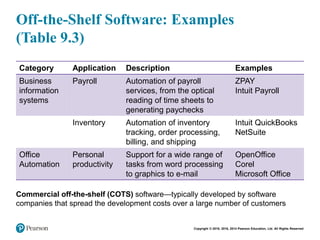
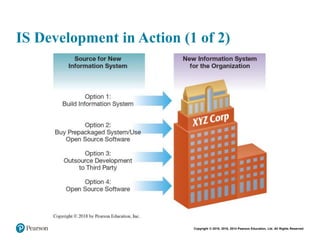
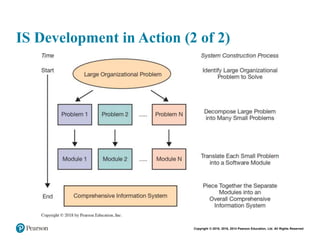
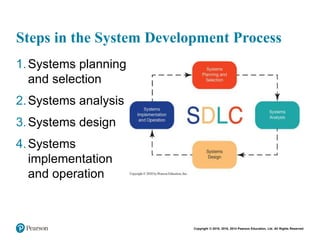
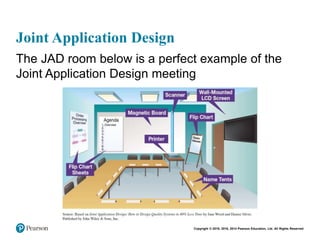
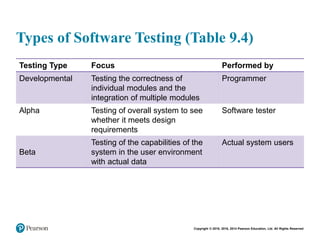
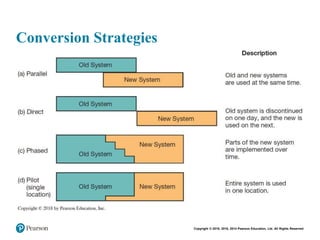
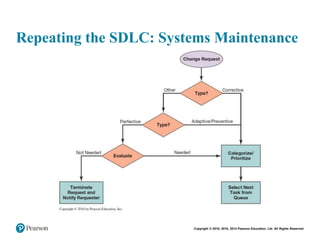
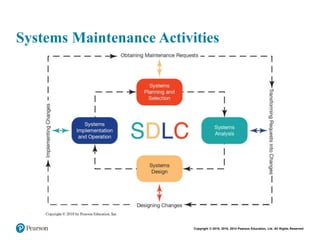
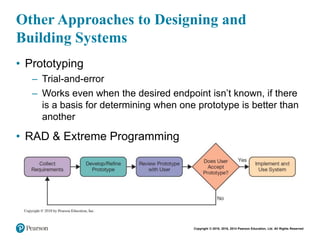
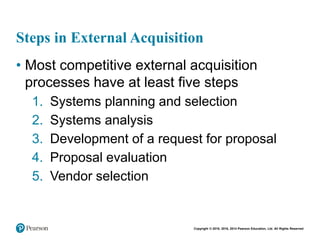
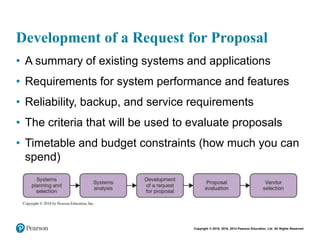
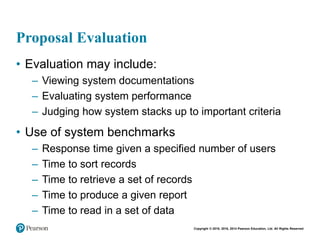
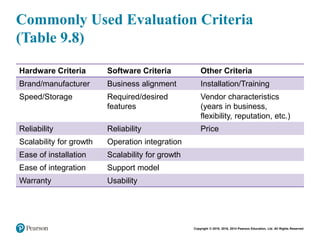
This document discusses the systems development life cycle and how organizations develop and acquire information systems. It describes the various phases of the systems development life cycle, including planning, analysis, design, implementation, and maintenance. It also discusses how organizations can develop systems using custom, off-the-shelf, or open source software, as well as how to formulate a business case to obtain approval and funding for new system development projects.