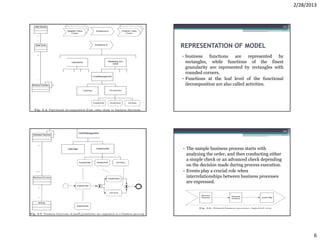
The document discusses business process modeling and introduces several key concepts:
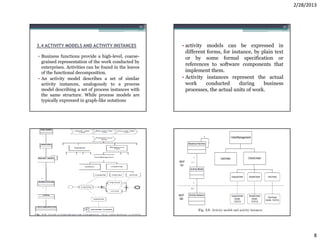
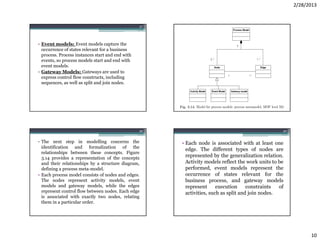
1) It defines the different types of activities that make up business processes - system activities, user interaction activities, and manual activities.
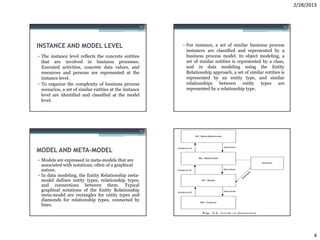
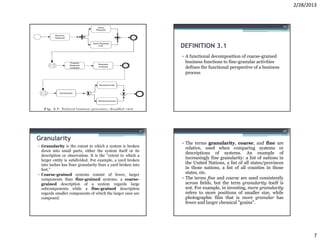
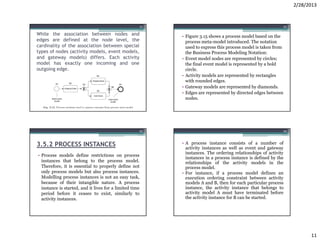
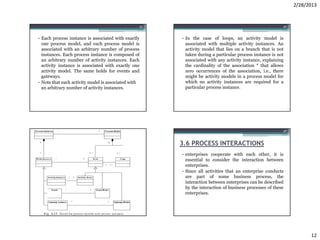
2) It explains the relationship between instances, models, and meta-models, with instances reflecting real-world entities and models representing classifications of similar instances.
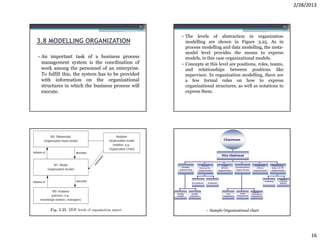
3) It introduces horizontal and vertical abstraction, with horizontal abstraction referring to modeling at the instance, model, and meta-model levels, and vertical abstraction separating distinct modeling sub-domains like processes, data, and organization.