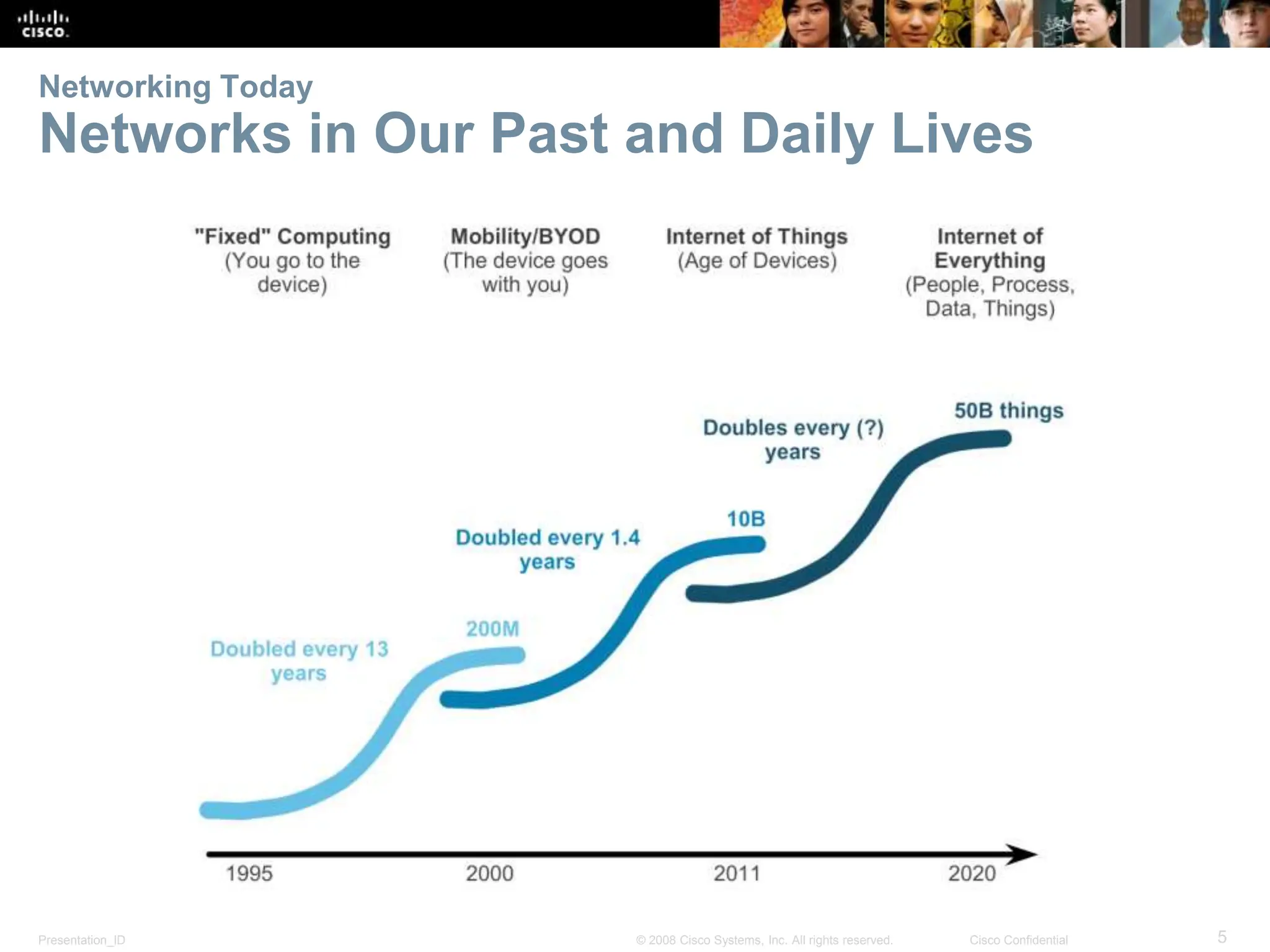
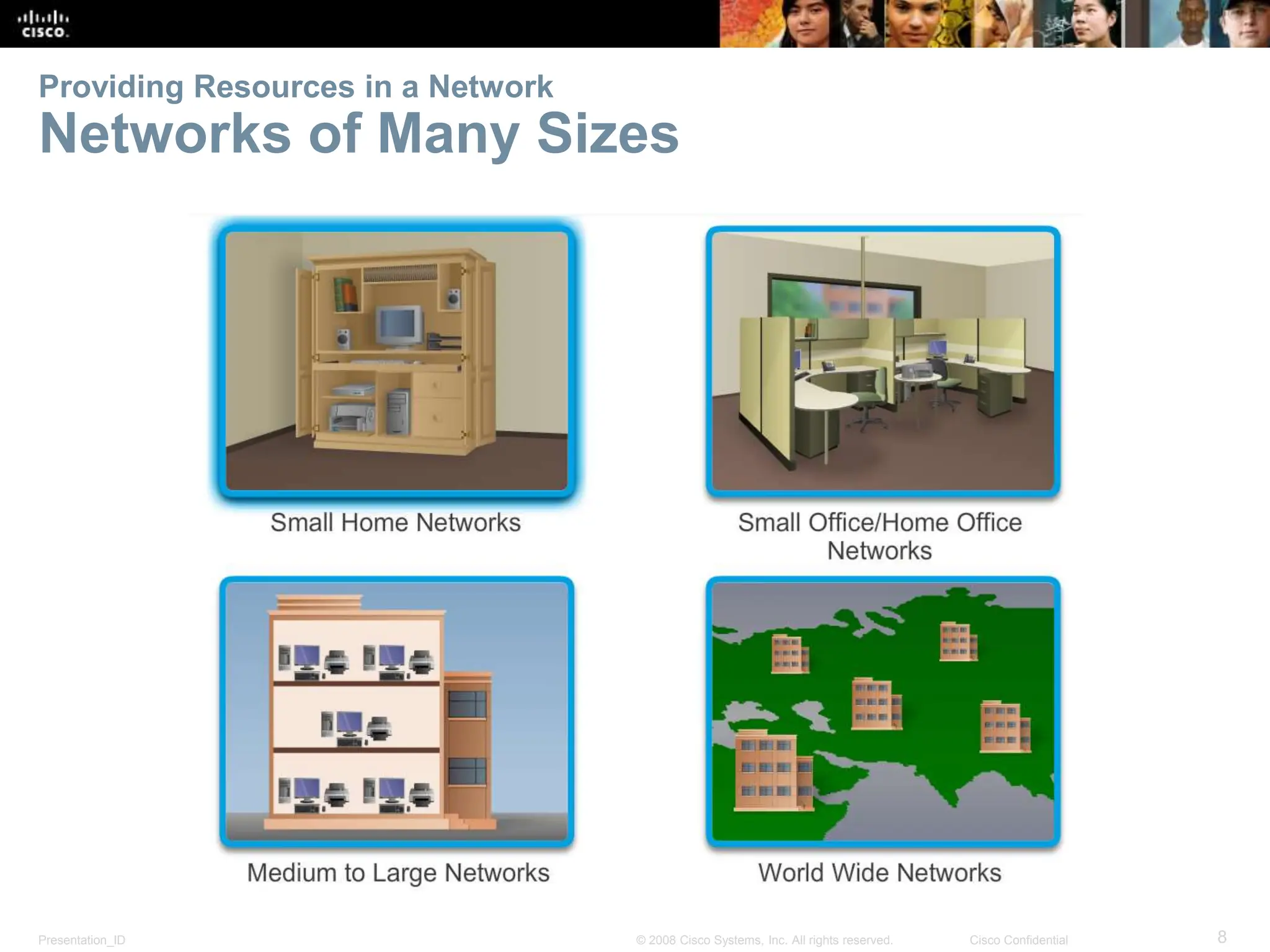
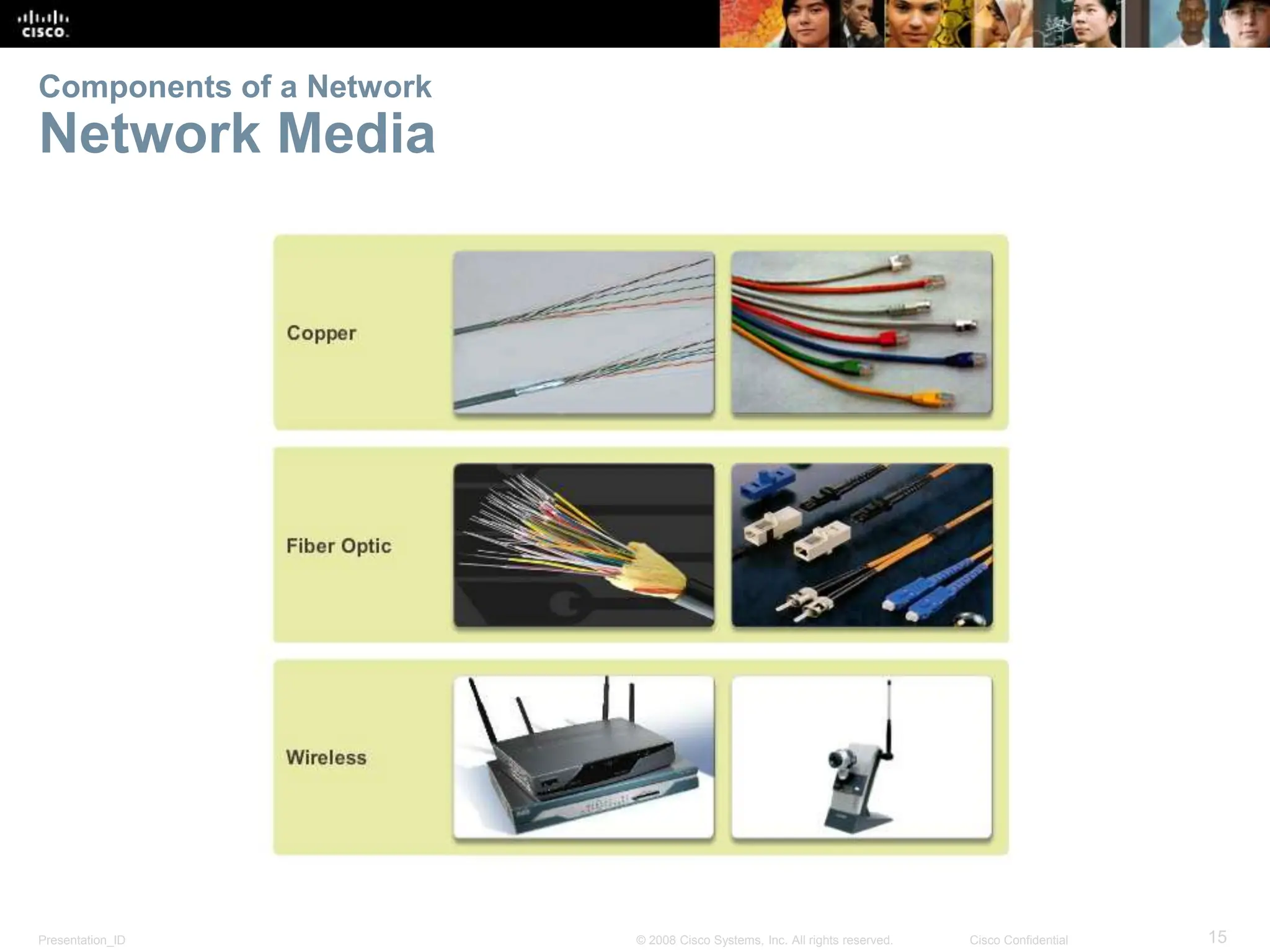
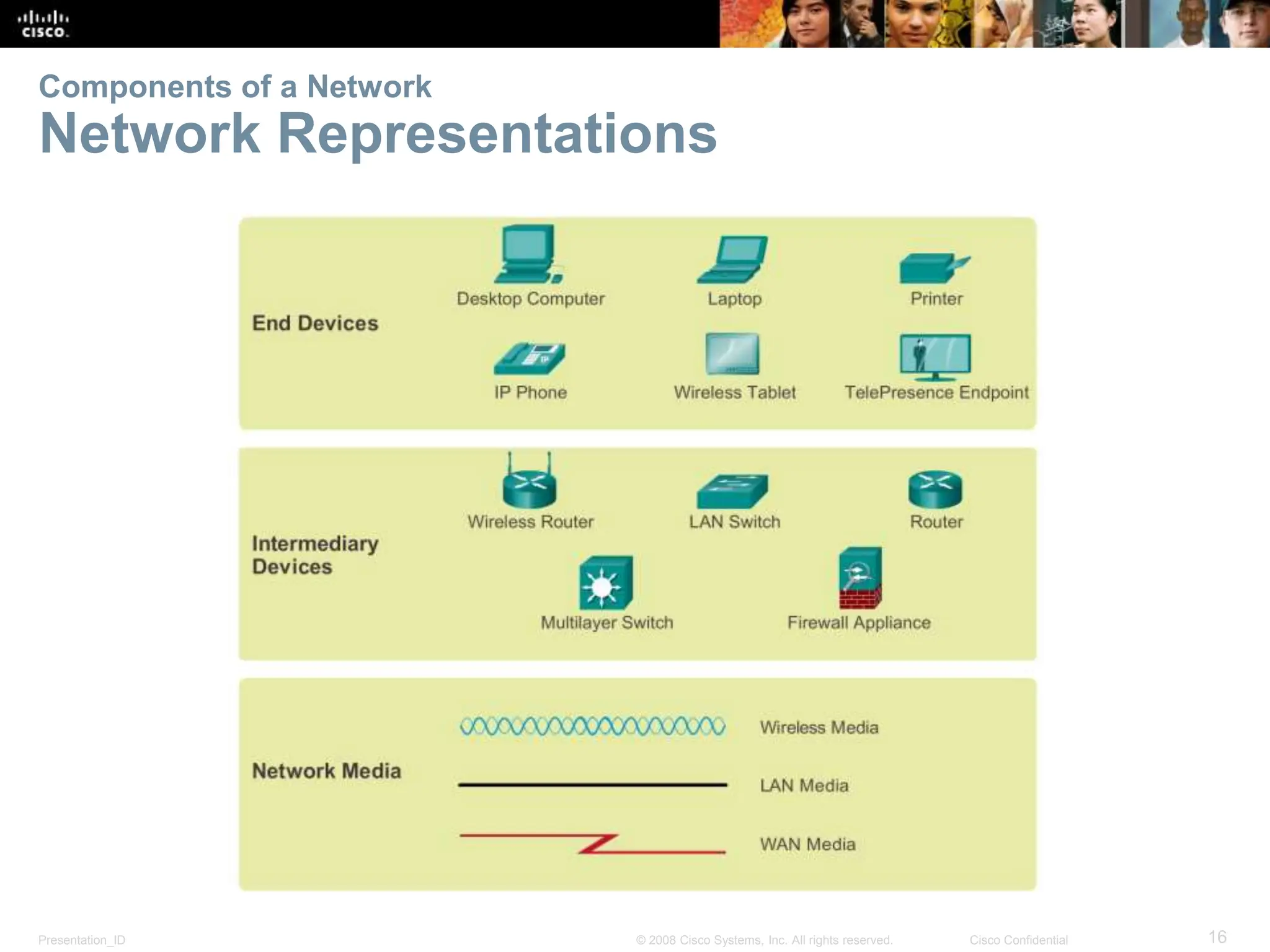
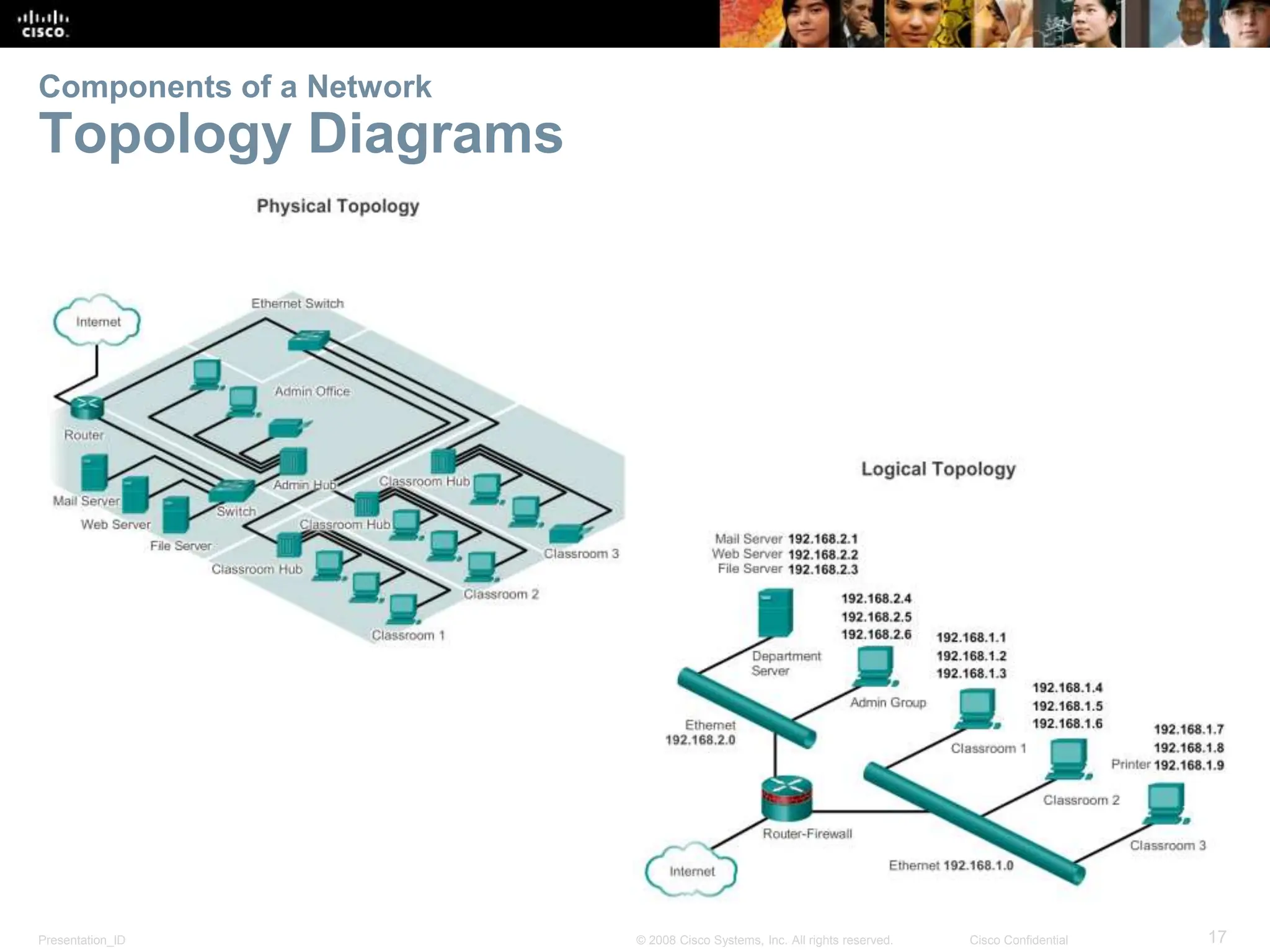
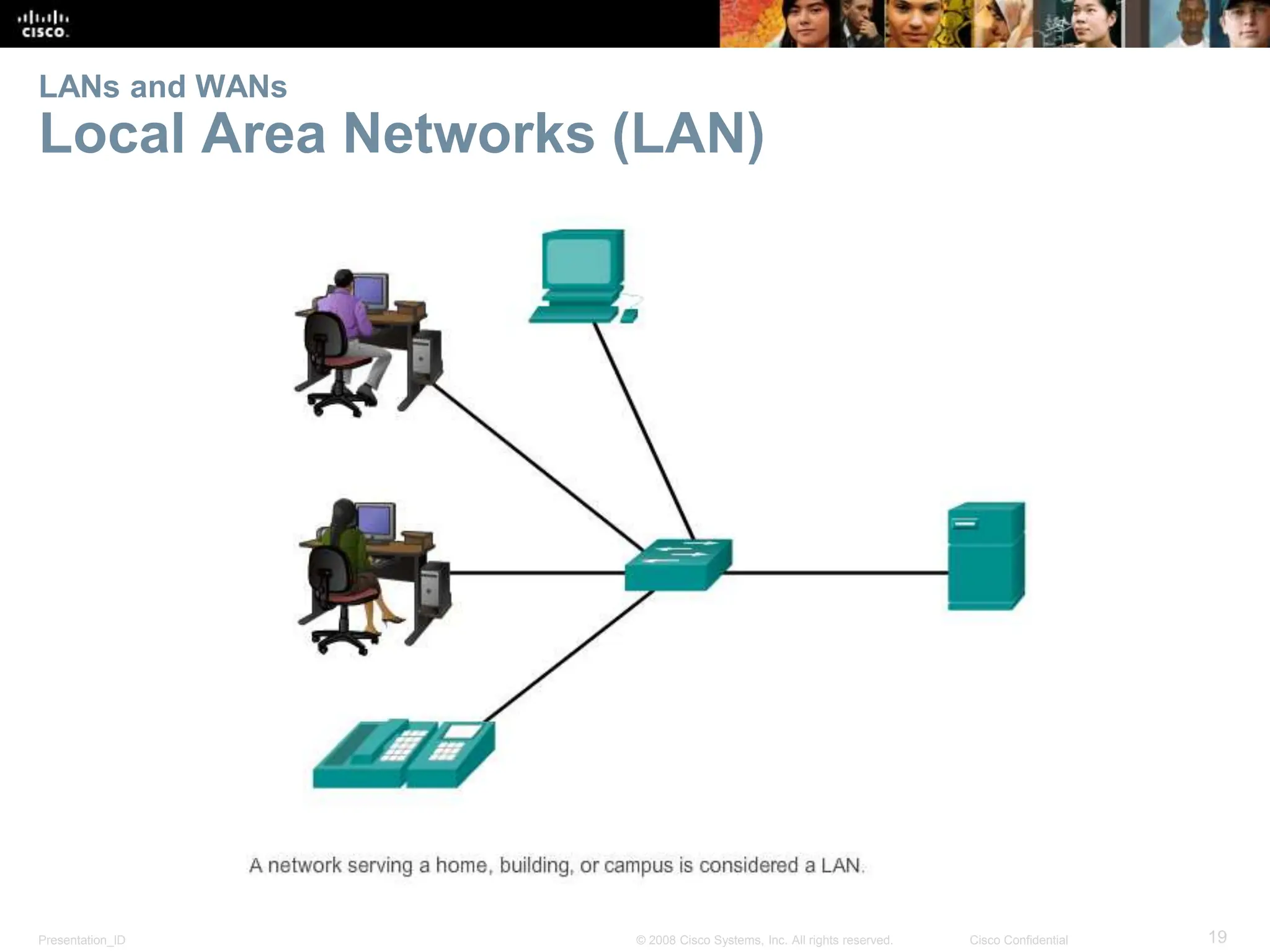
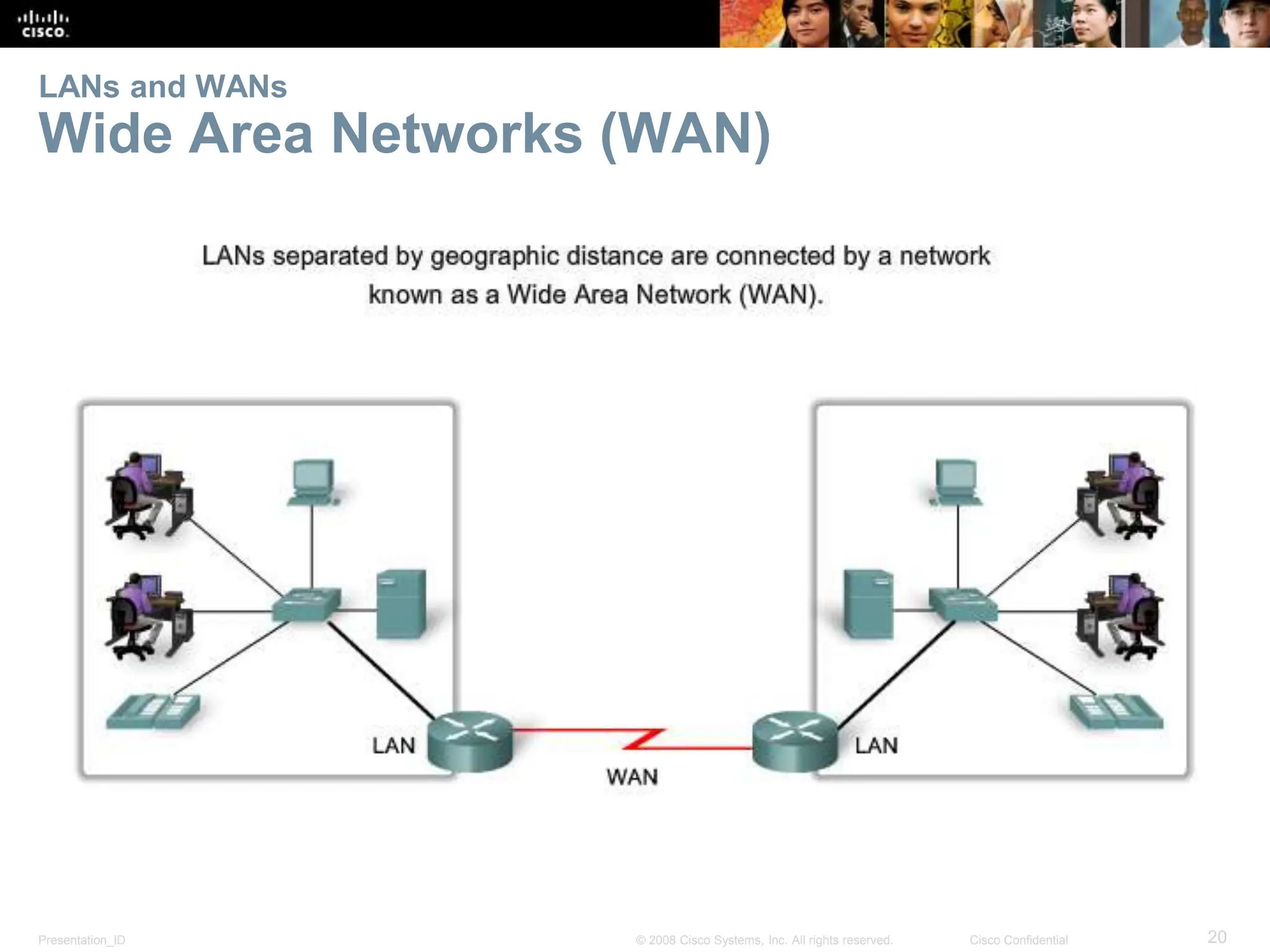
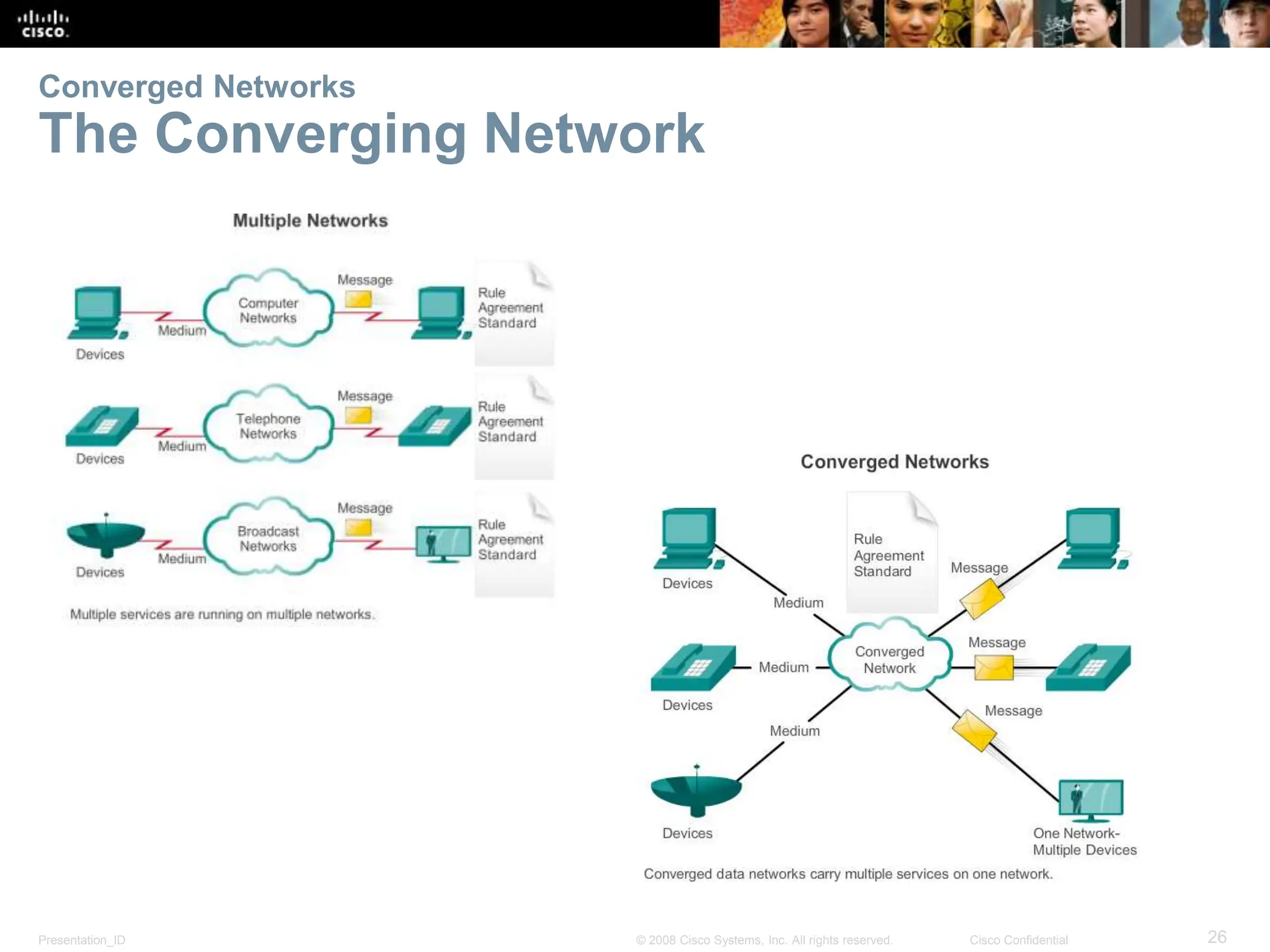
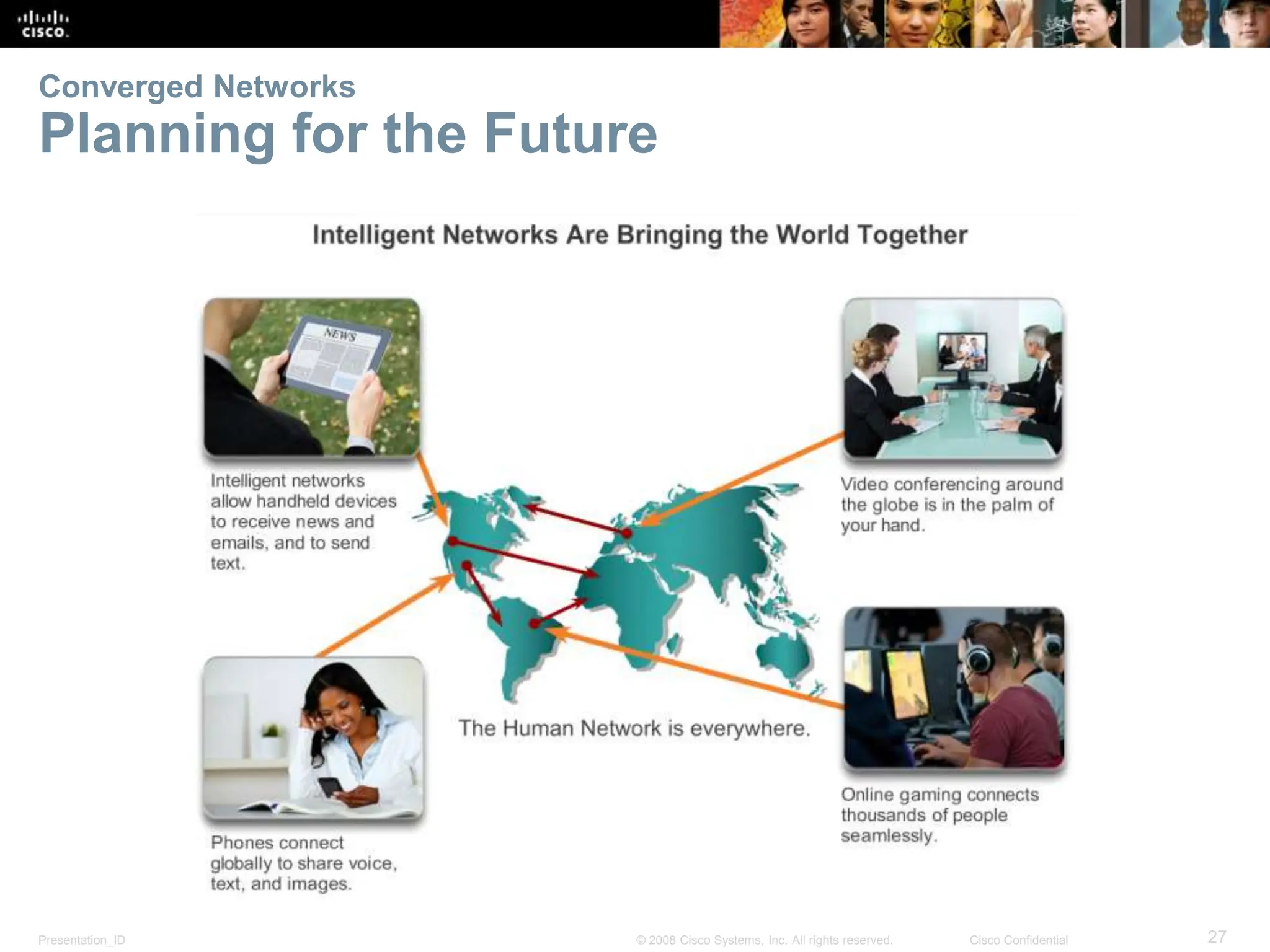
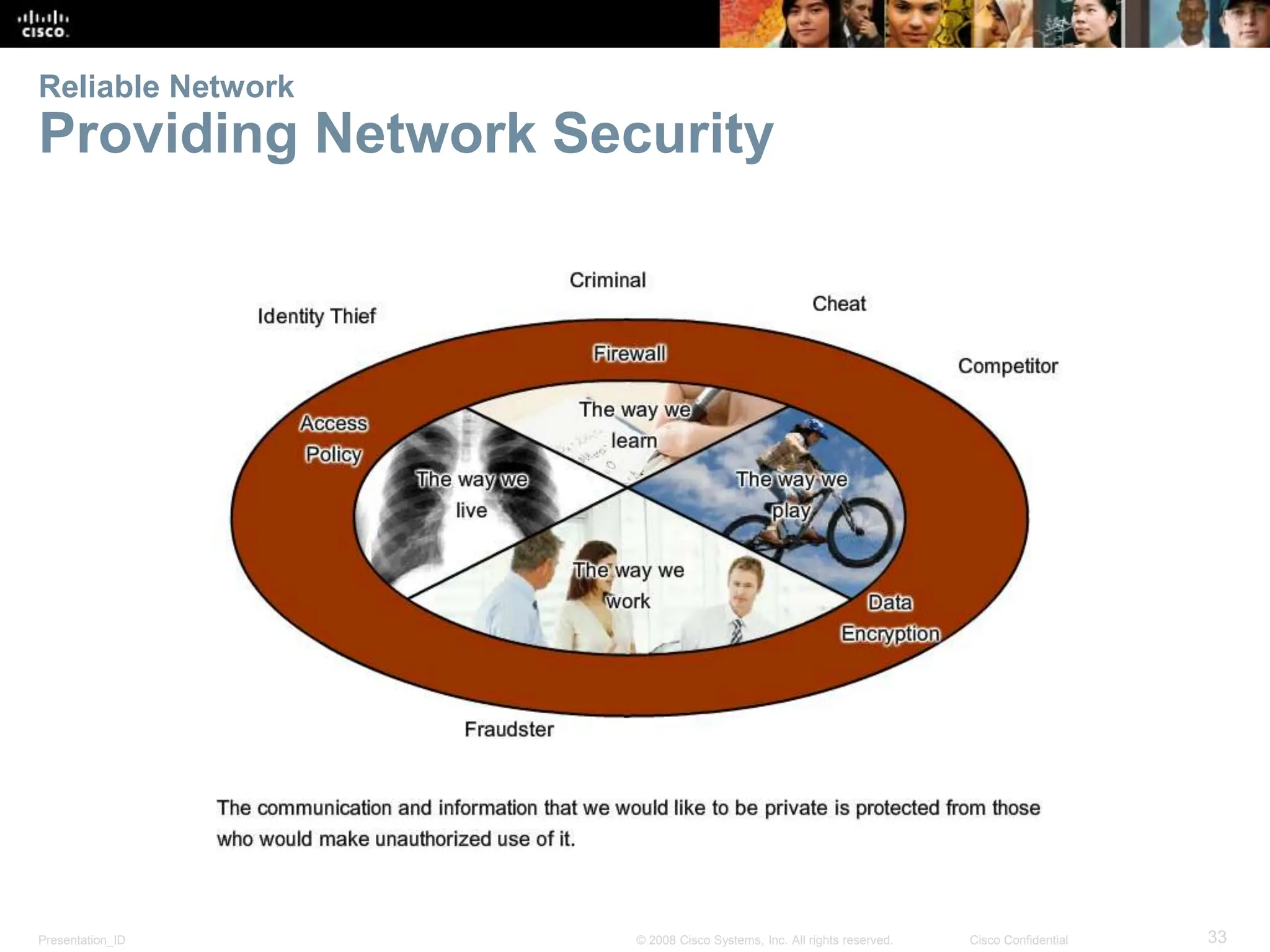
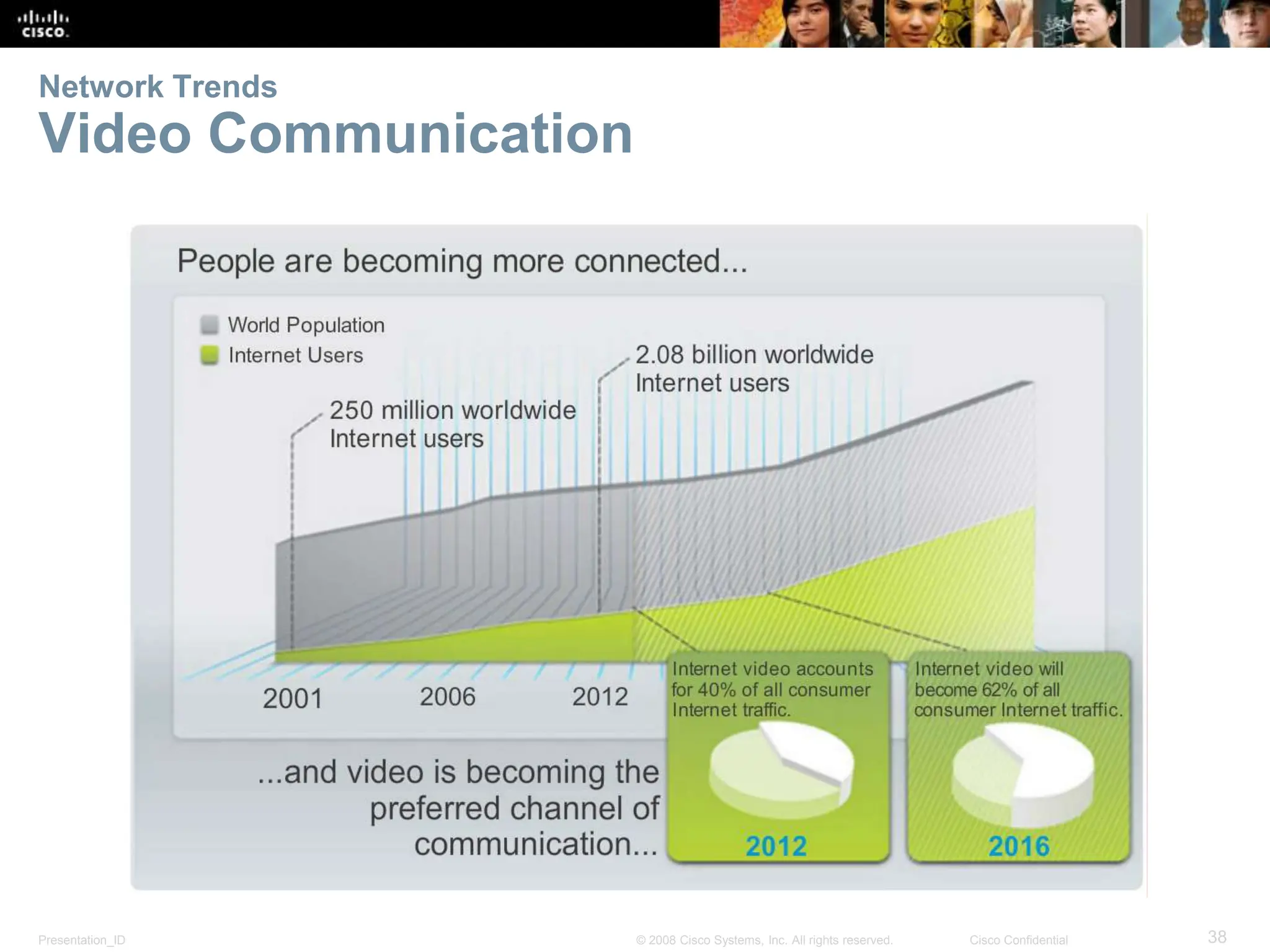
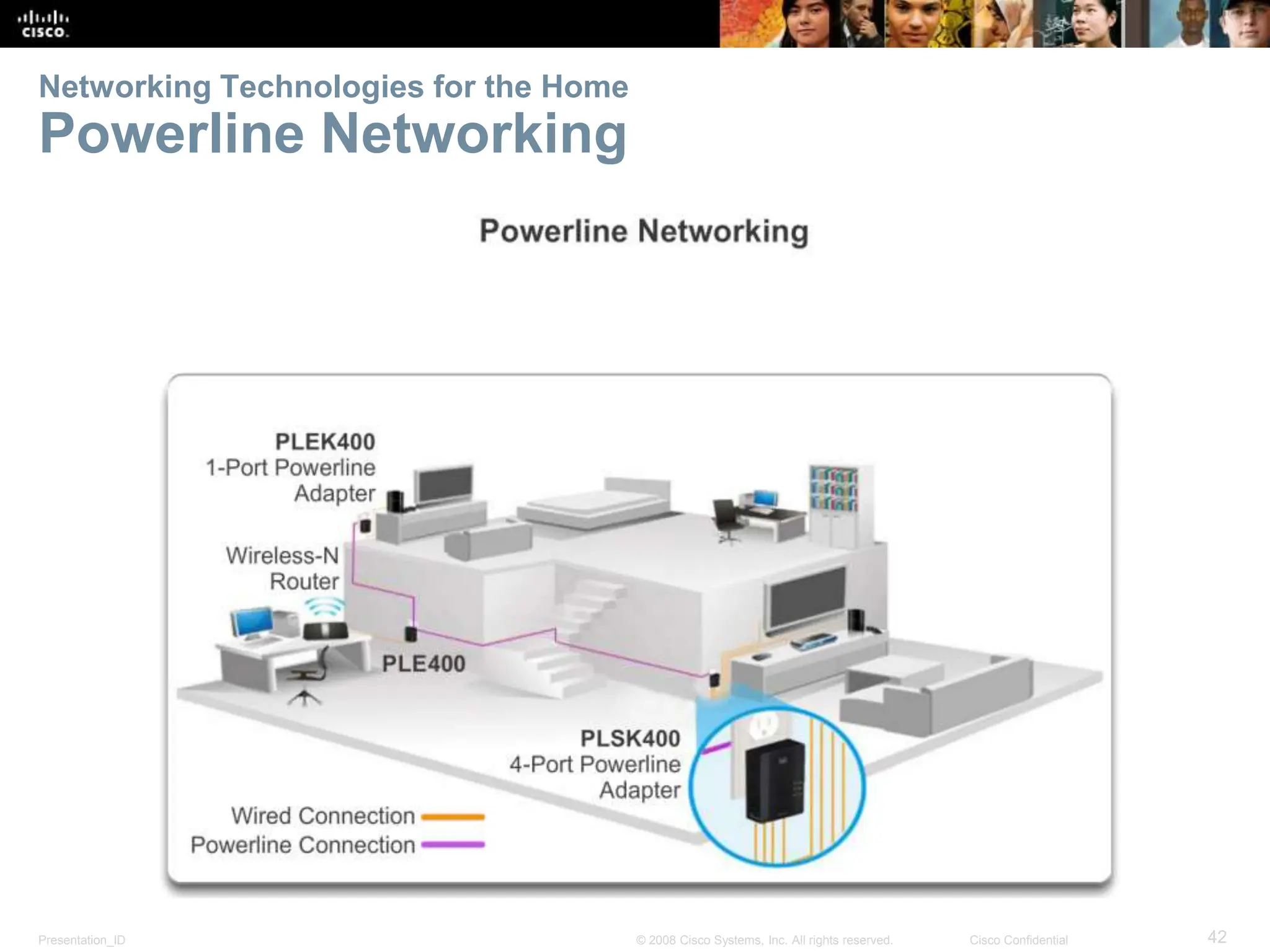
The document is a chapter from a Cisco networking textbook. It covers topics like how networks are used in everyday life, common network topologies for businesses, and trends that will impact future networks like BYOD, video communication, and cloud computing. The chapter objectives are to explain network fundamentals and explore how networks are evolving to meet new needs.