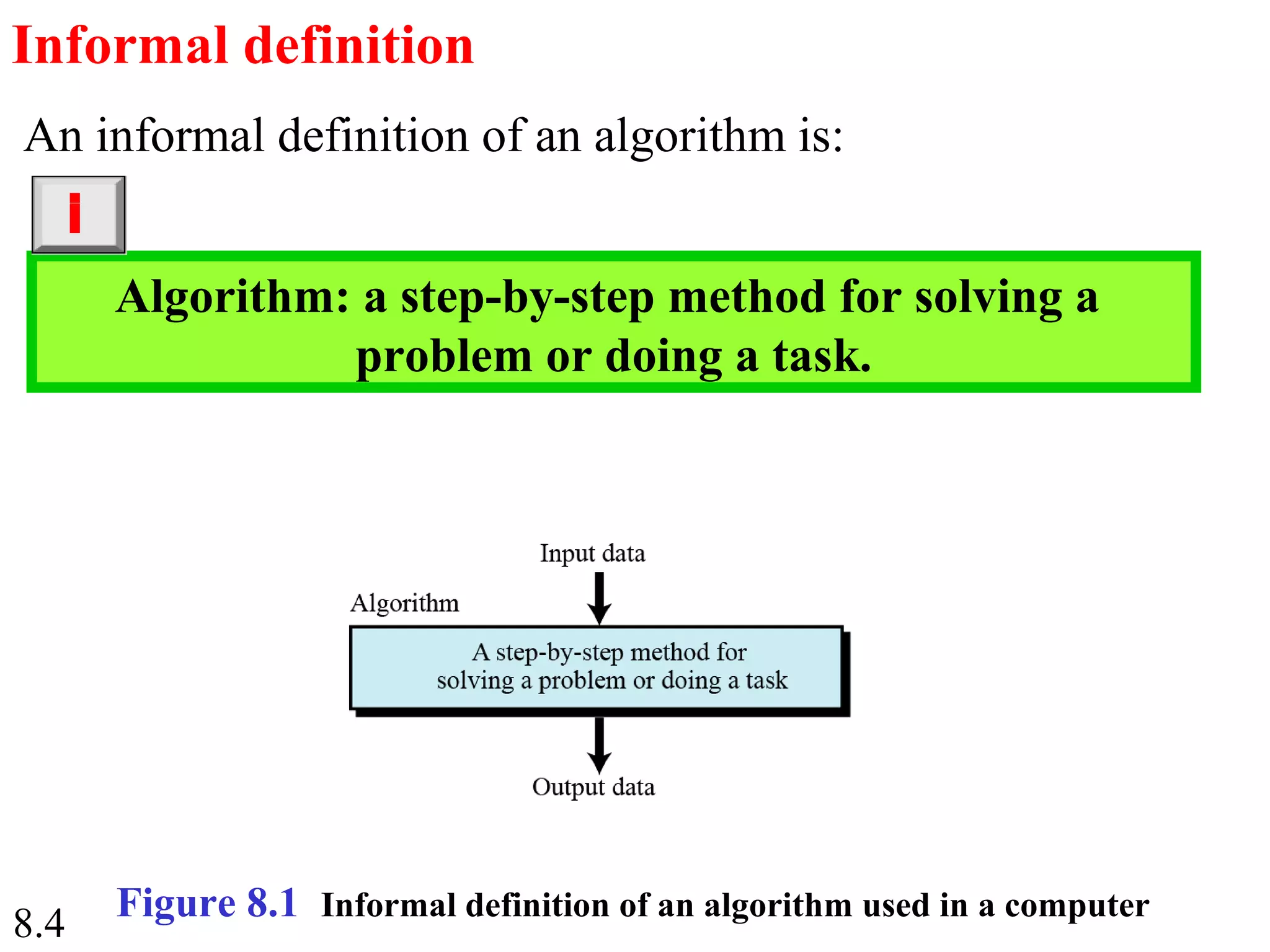
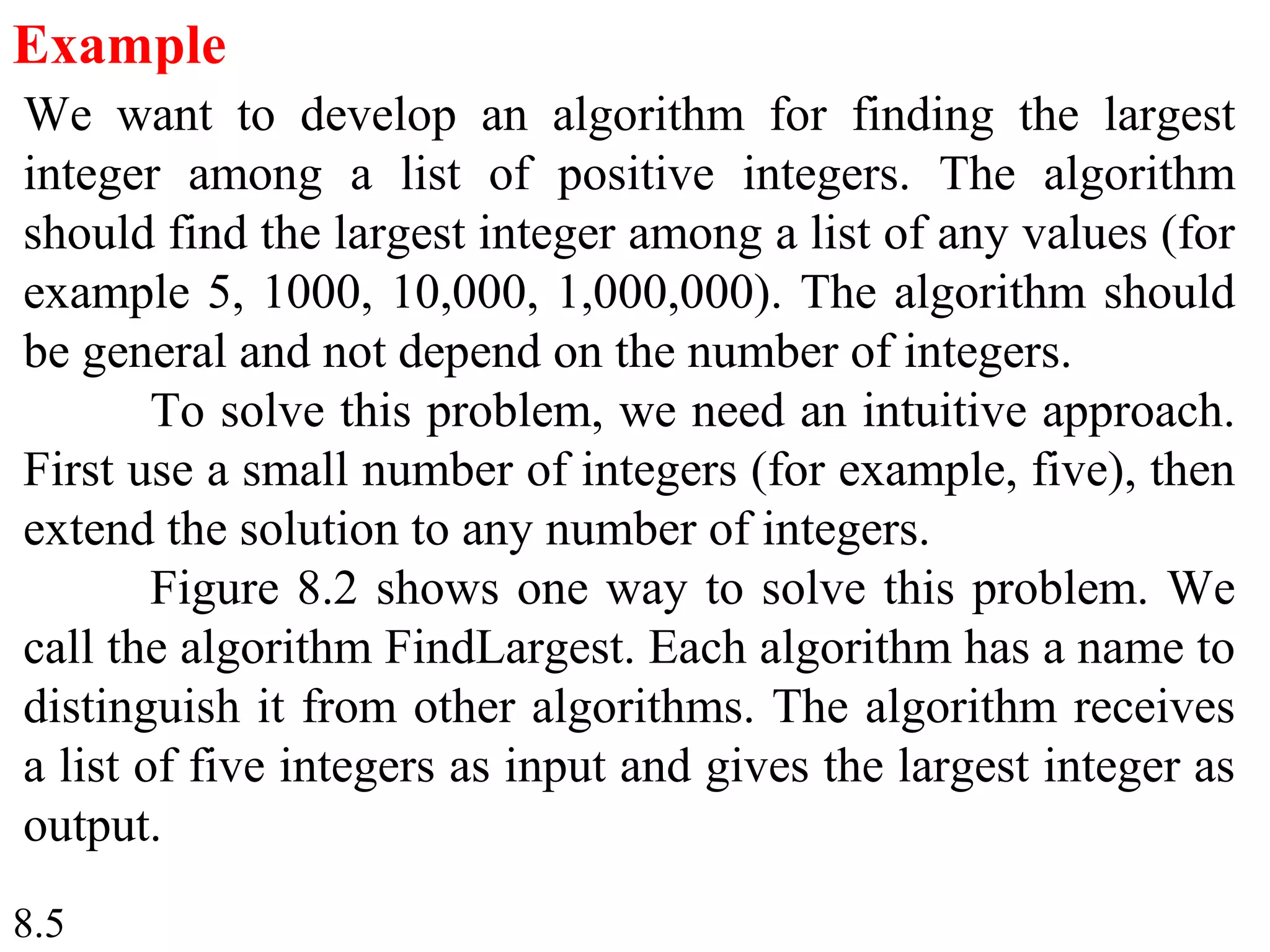
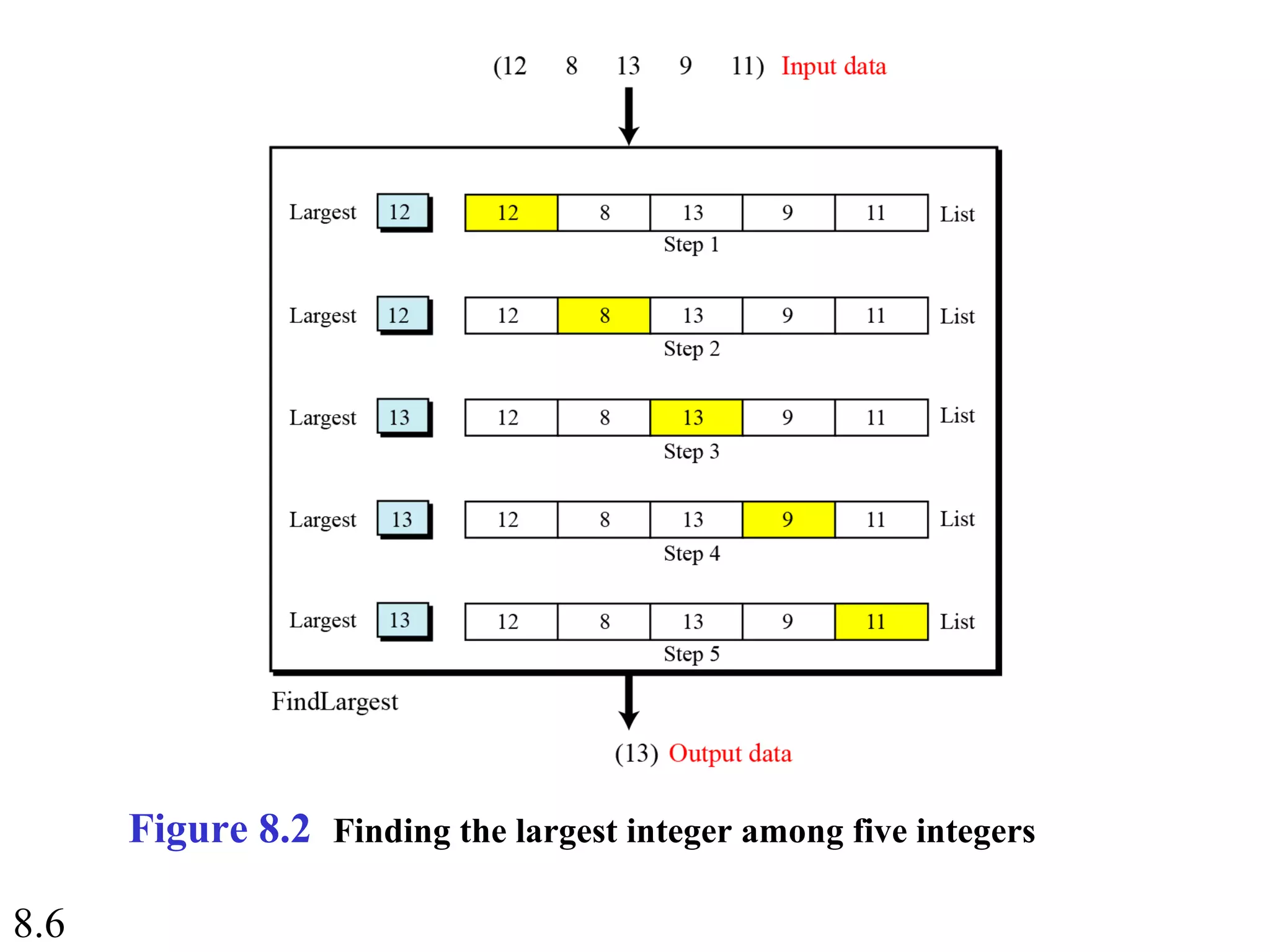
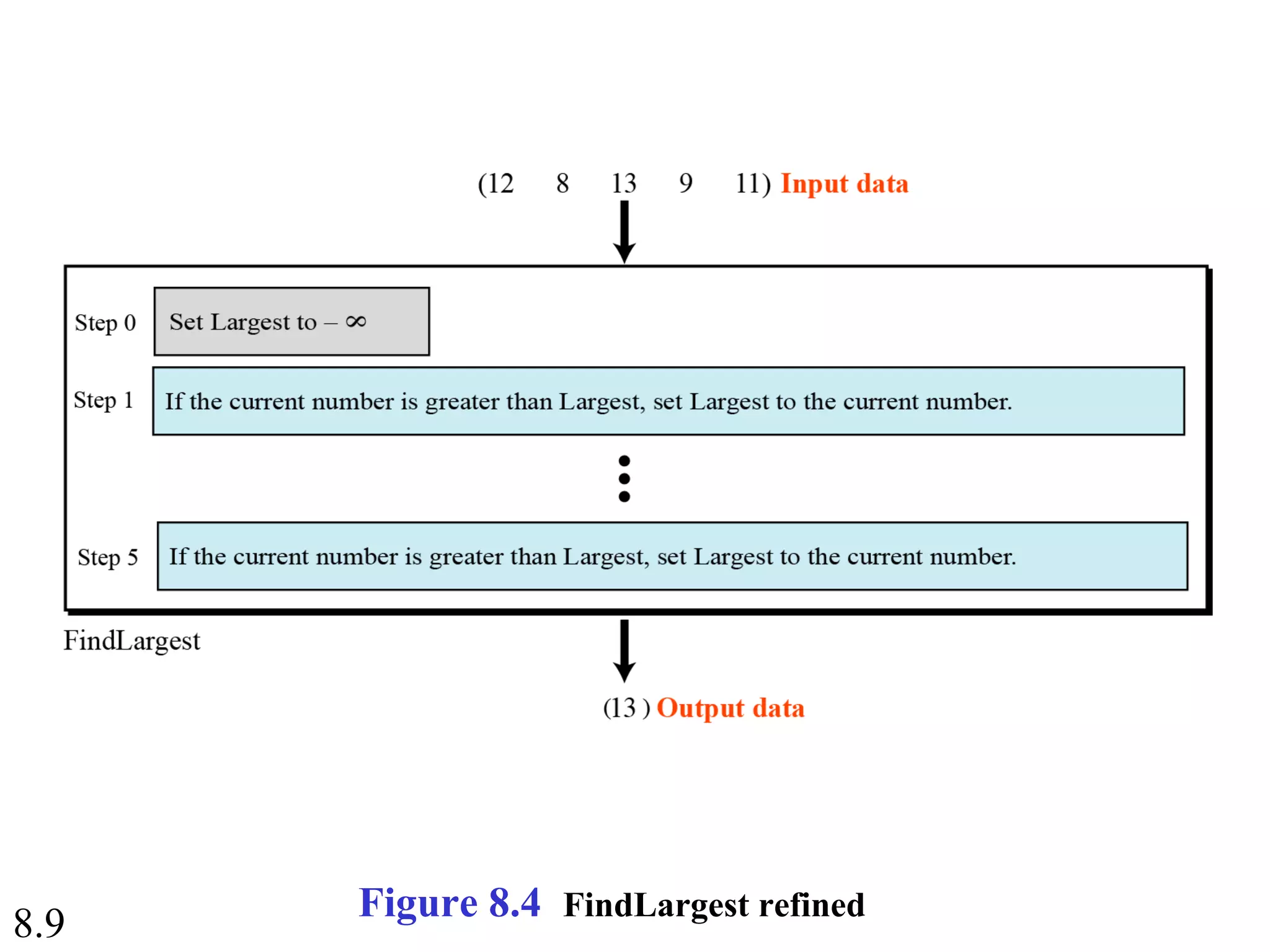
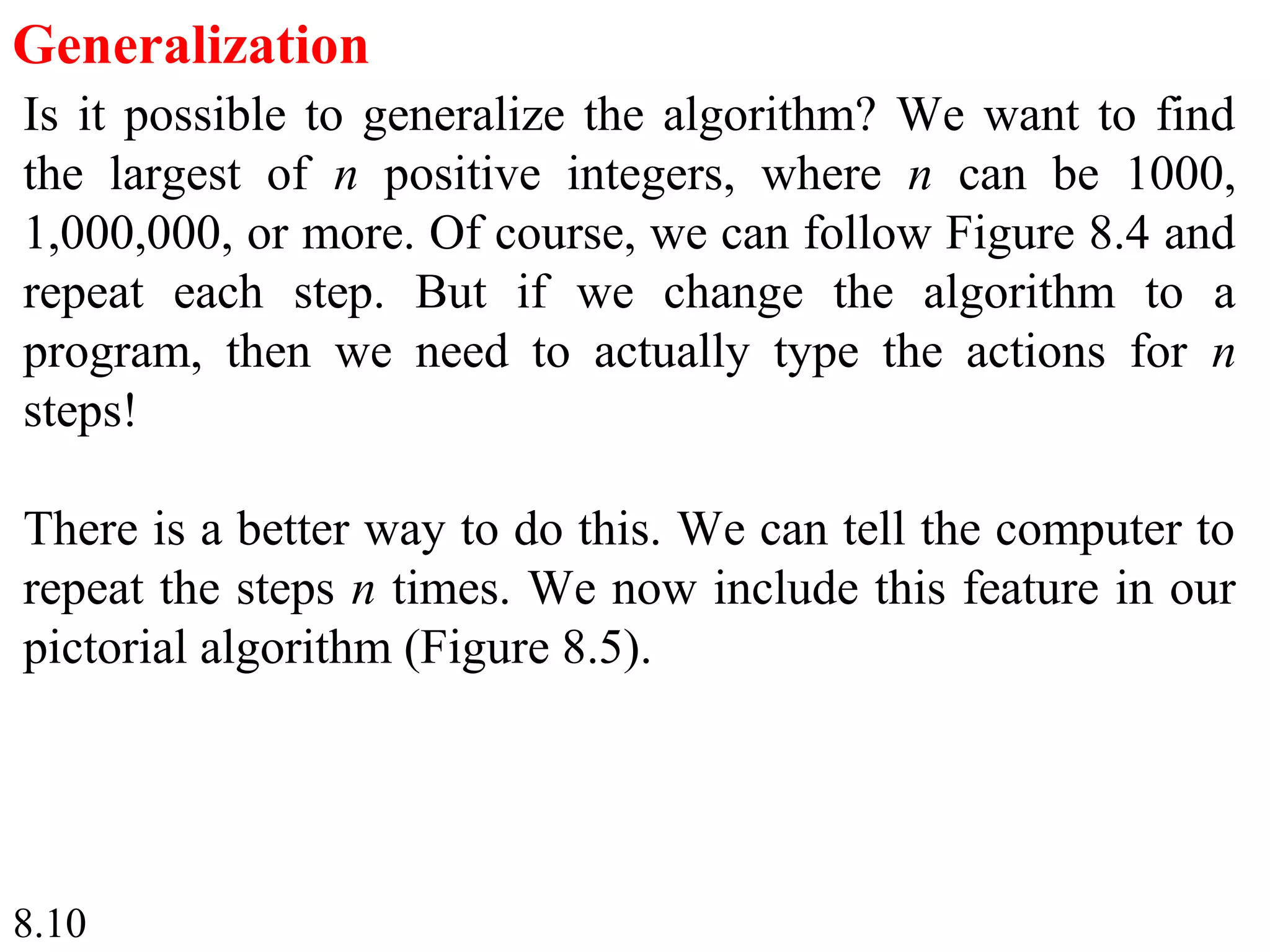
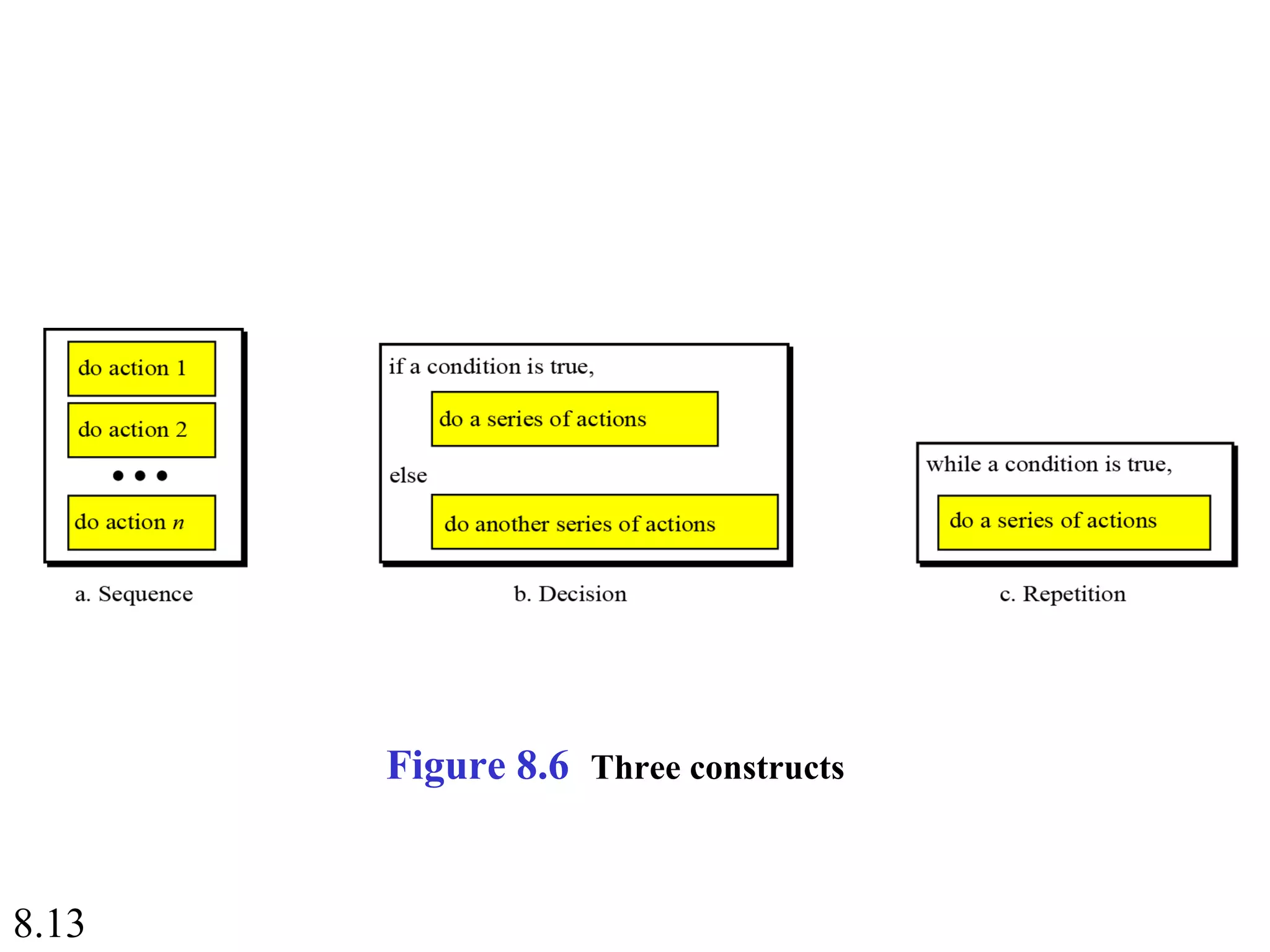
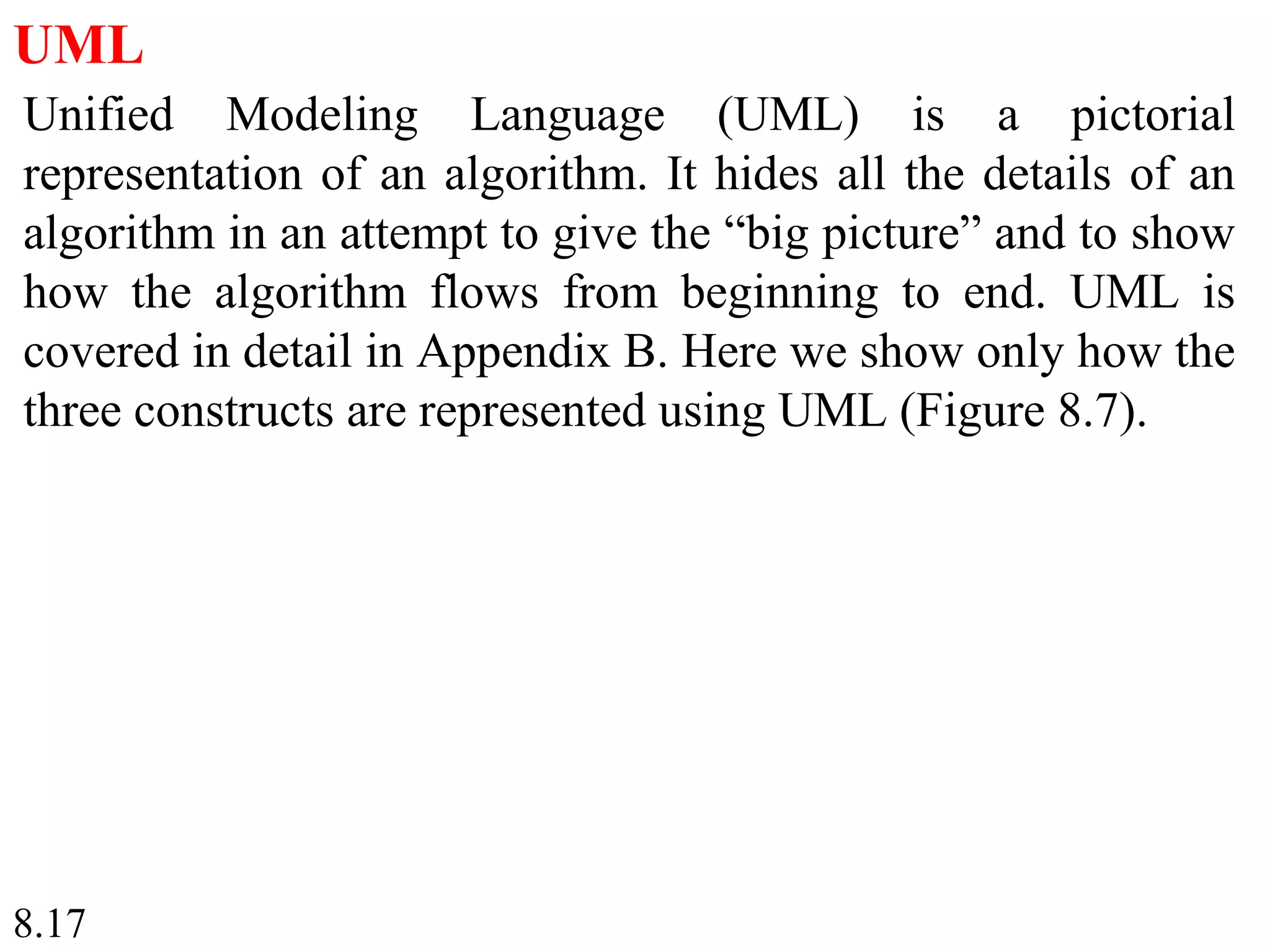
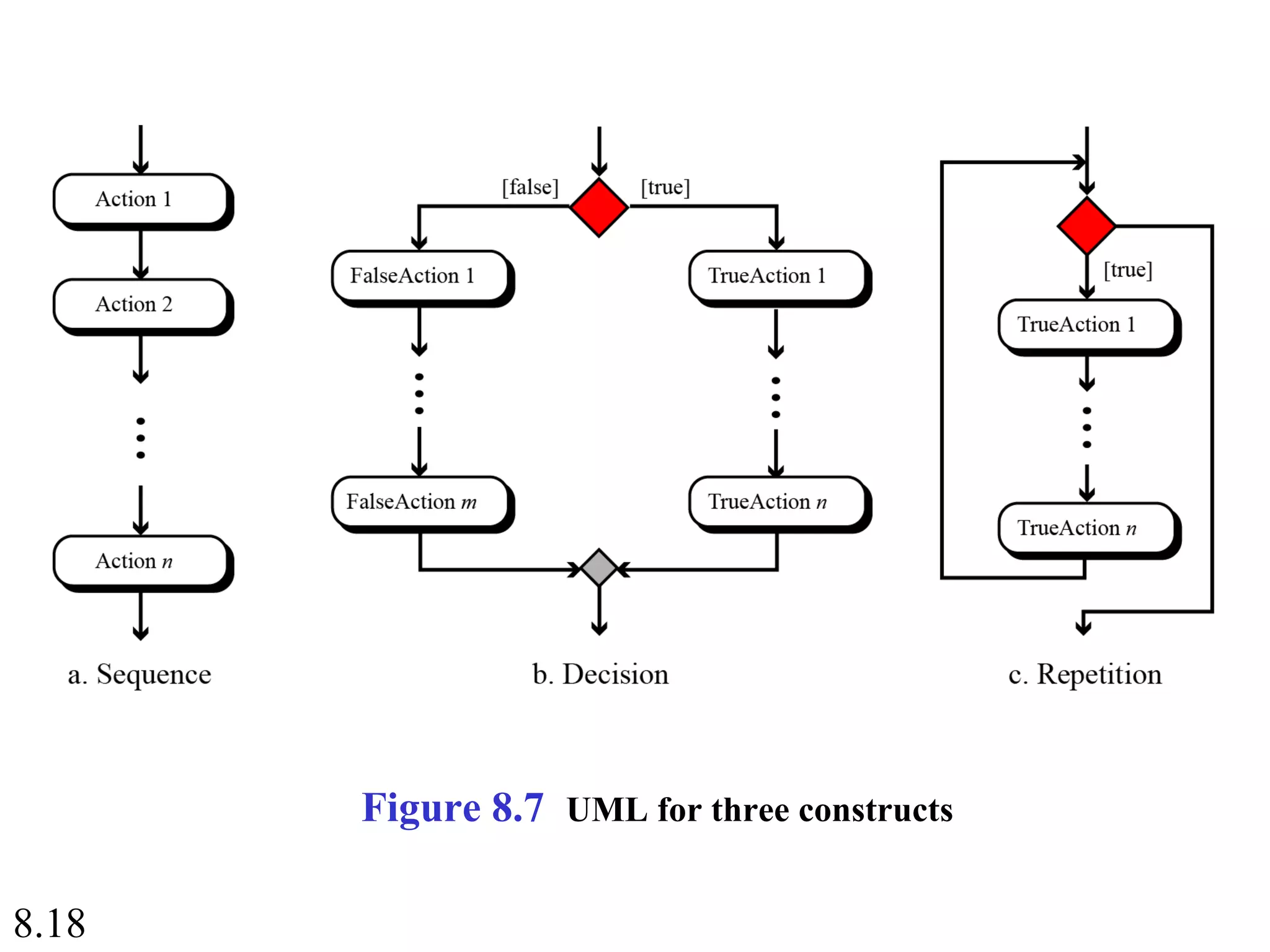
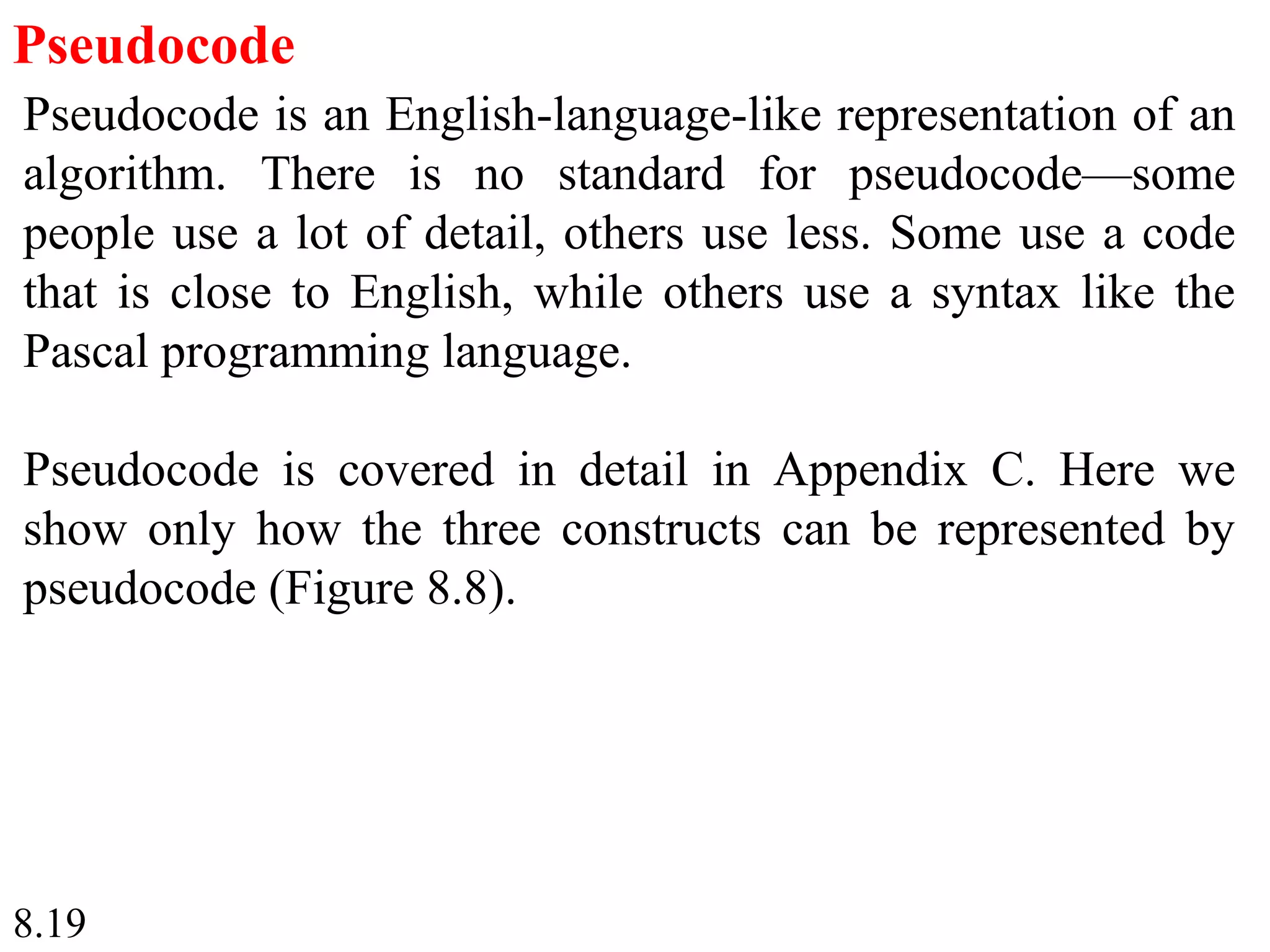
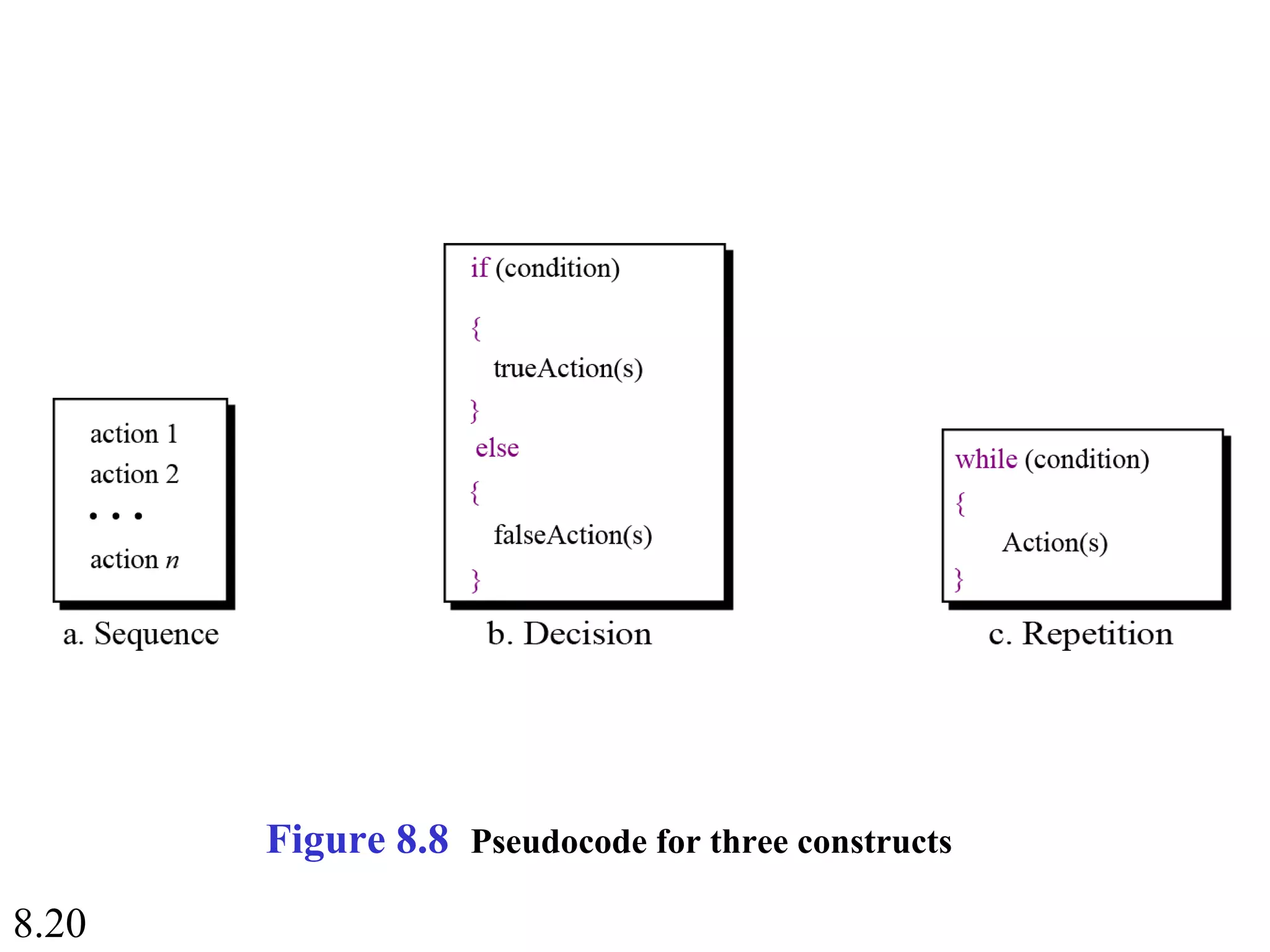
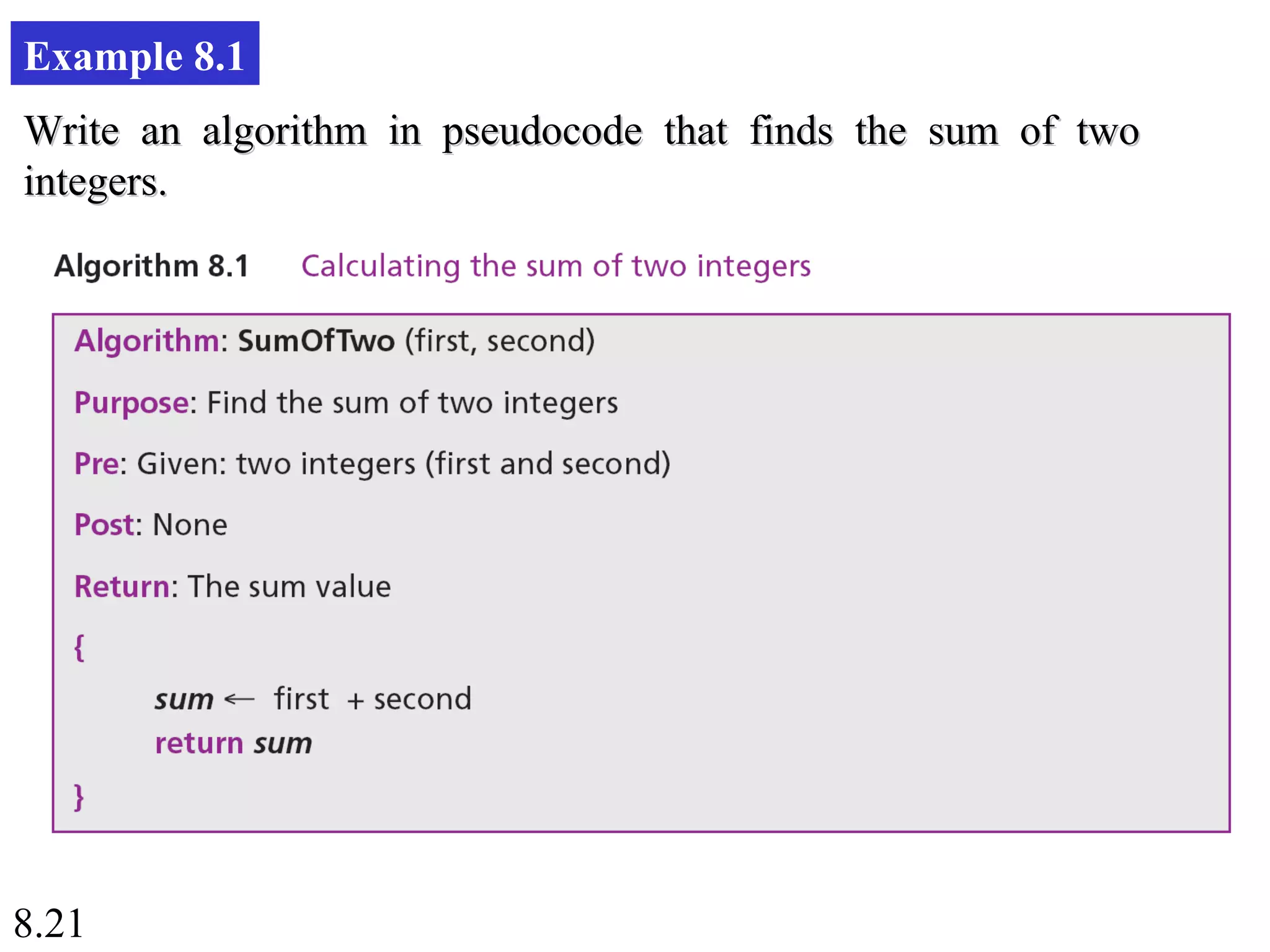
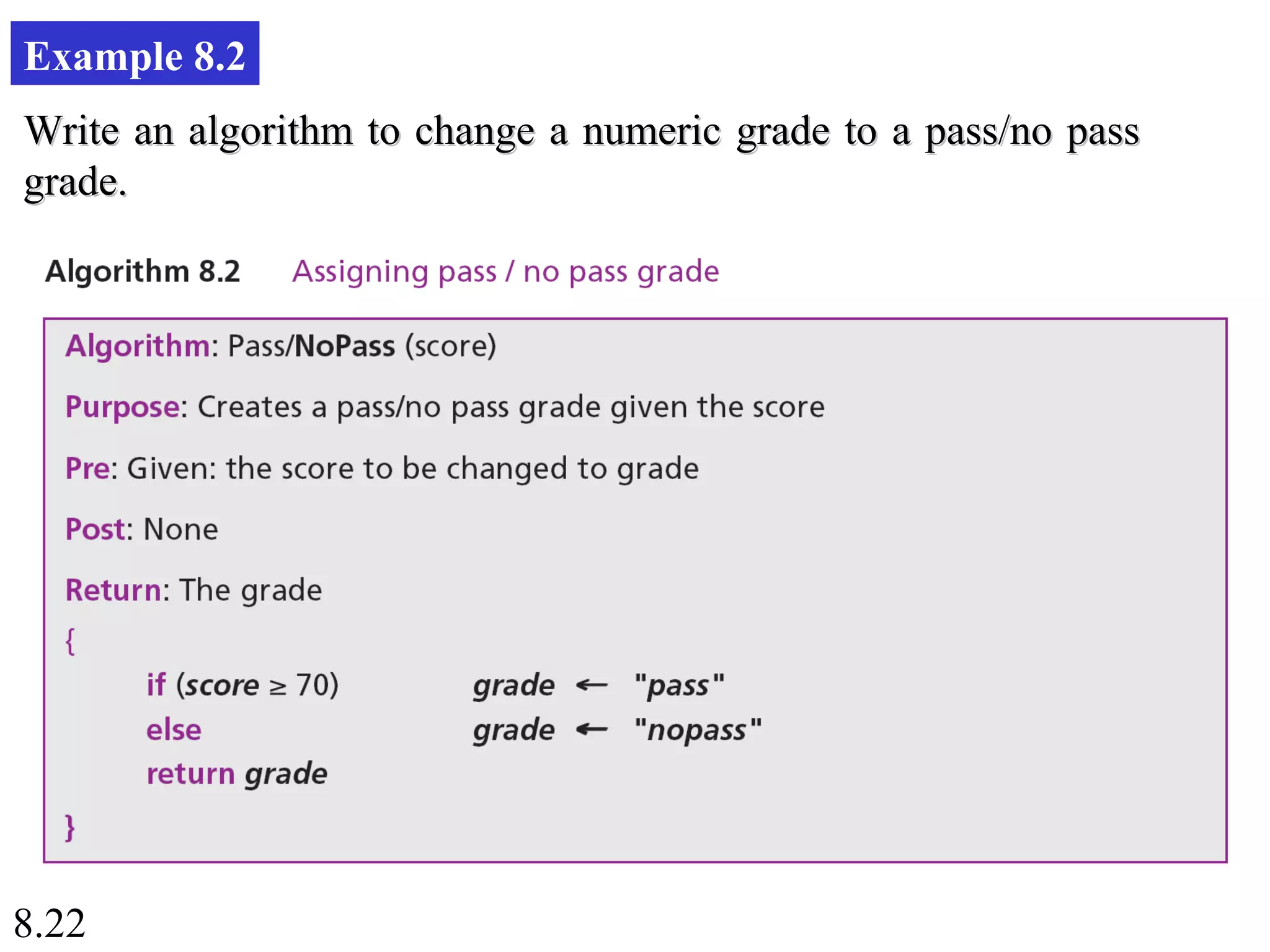
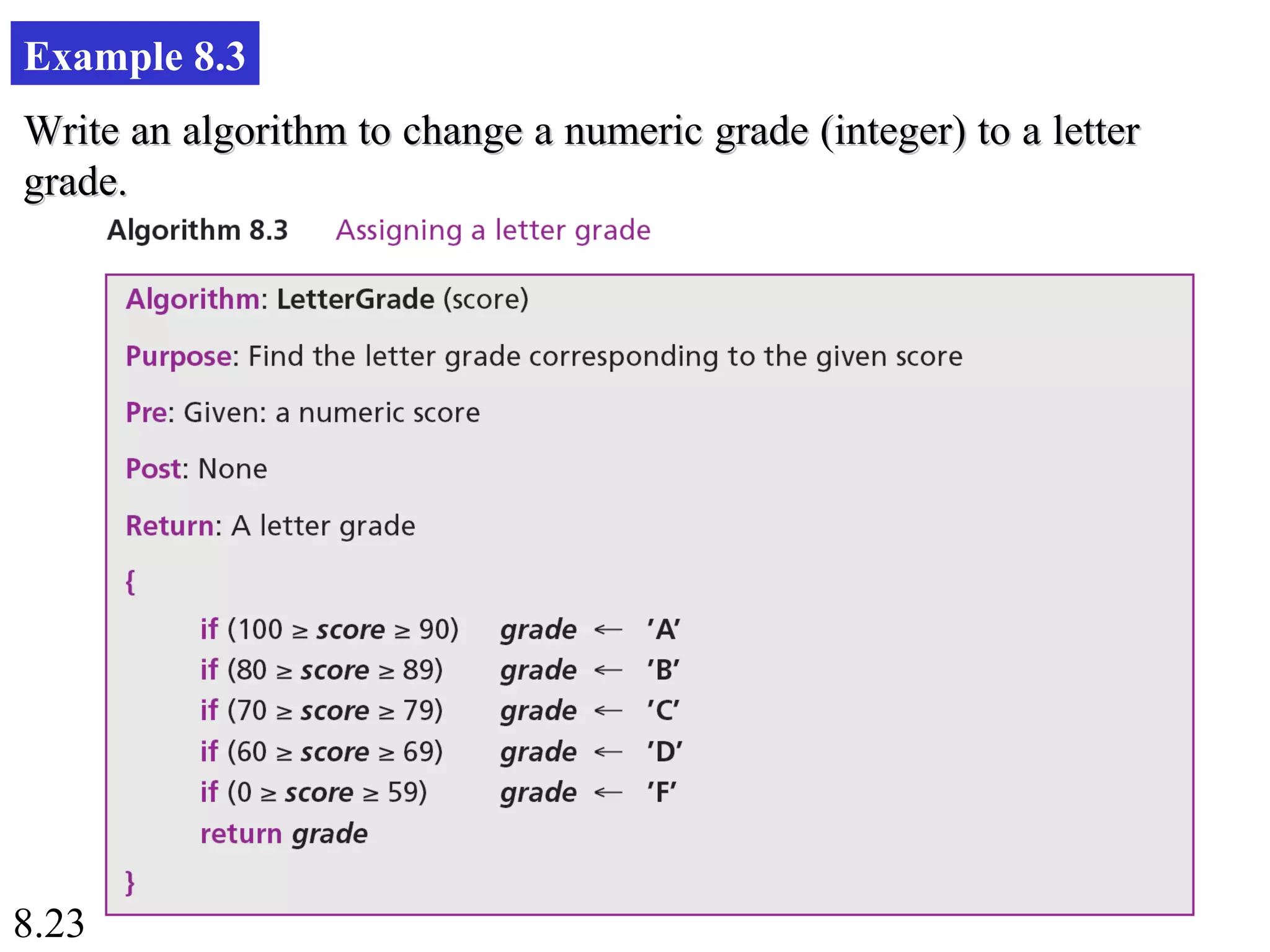
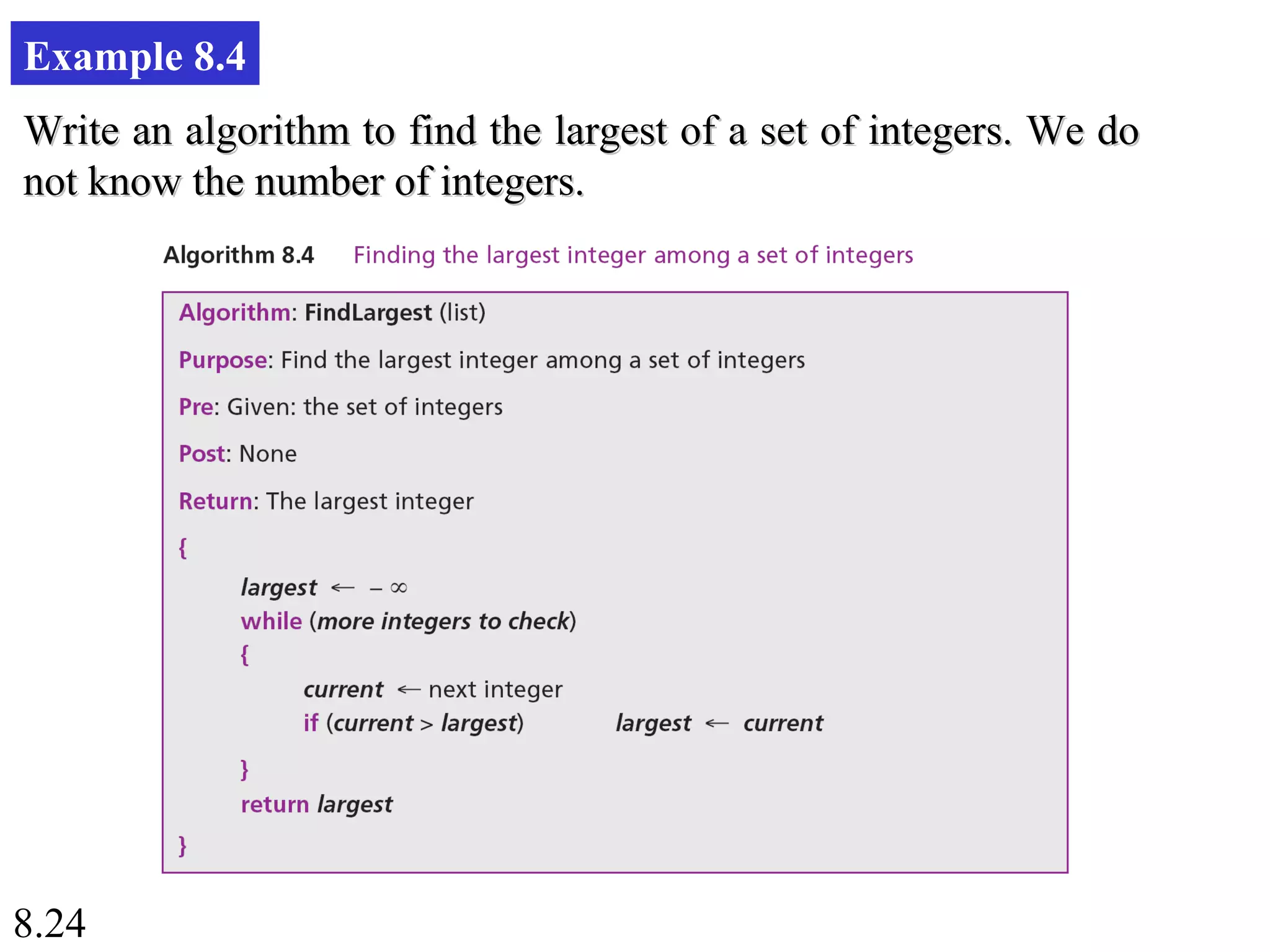
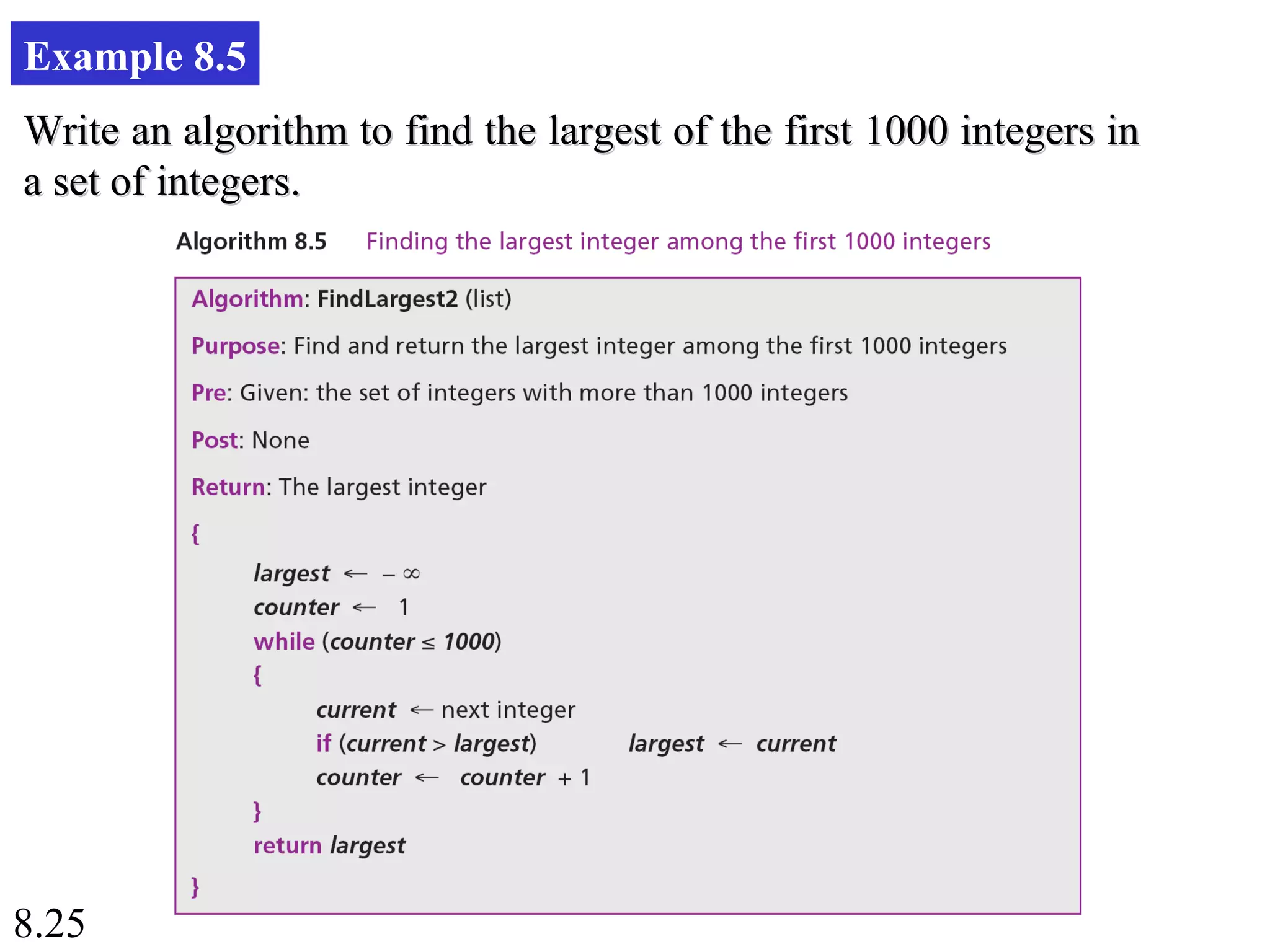
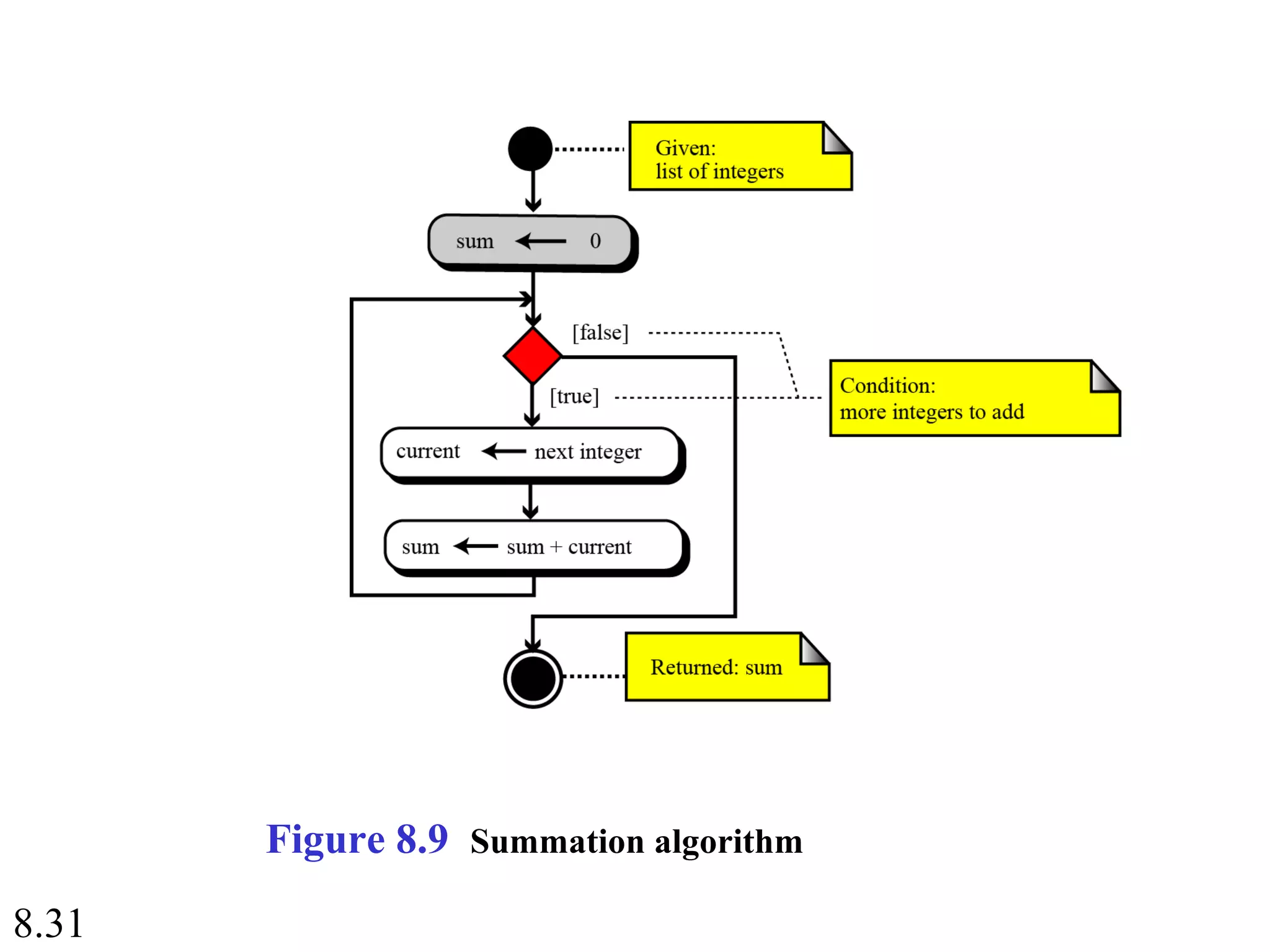
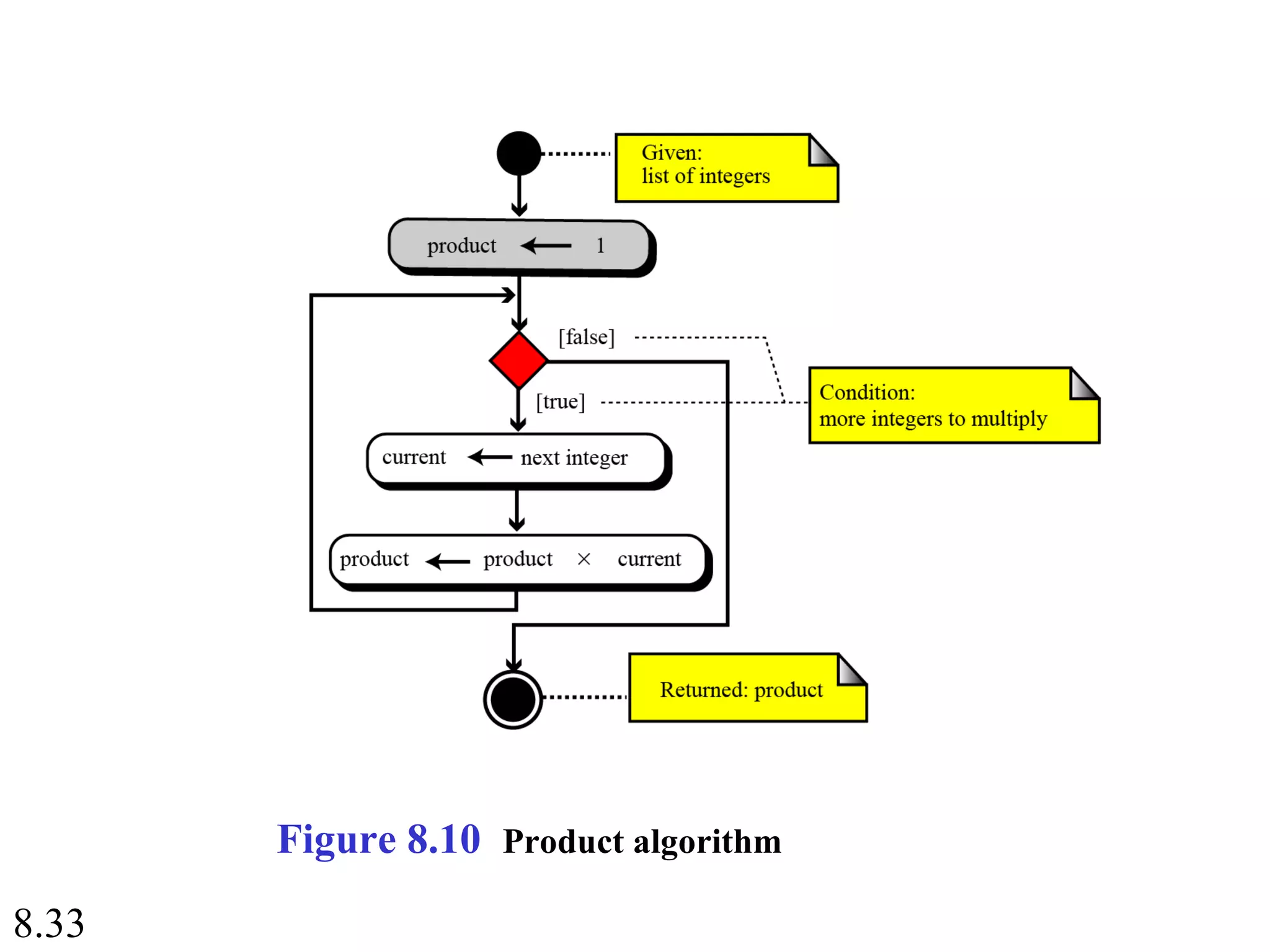
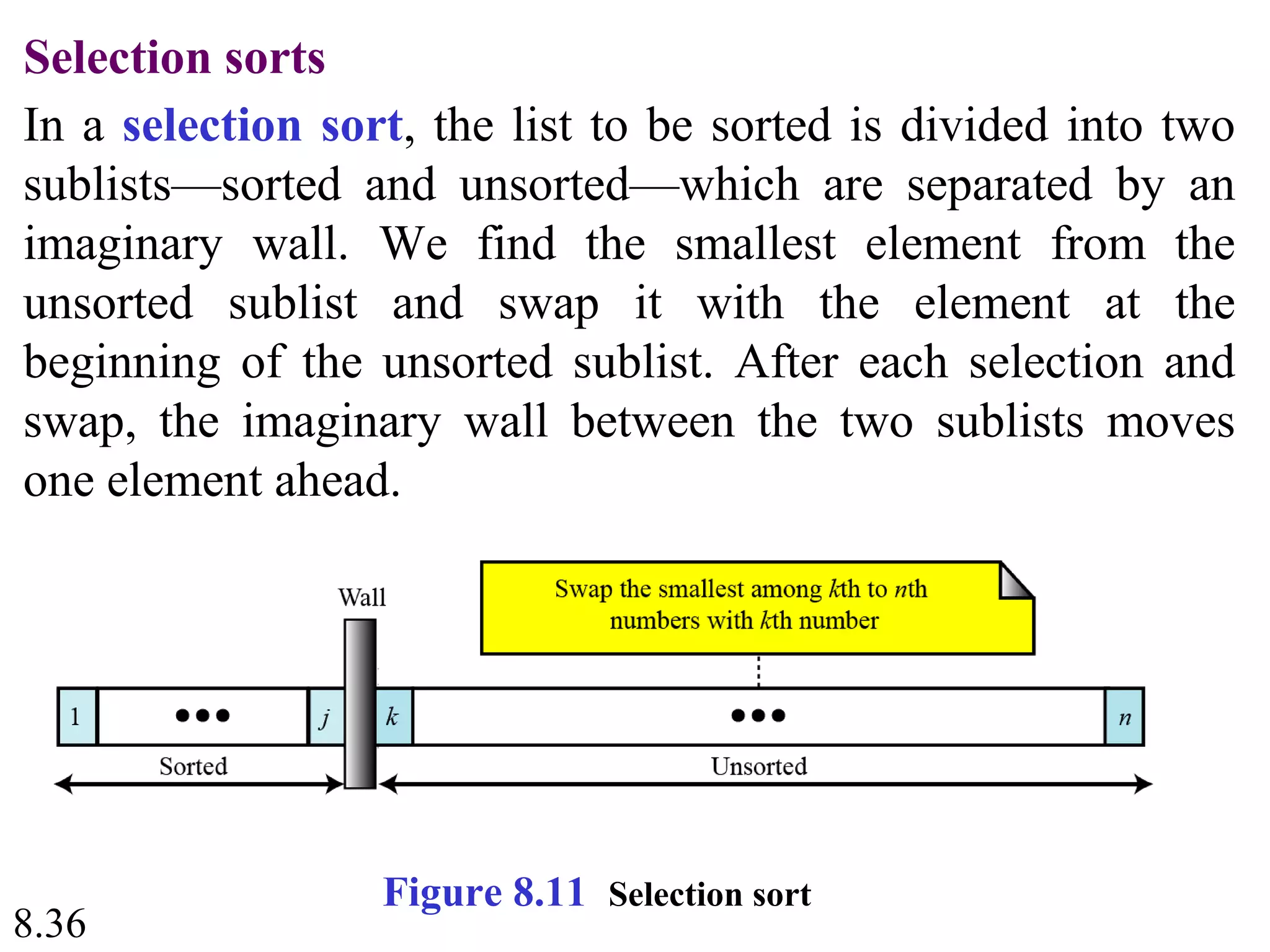
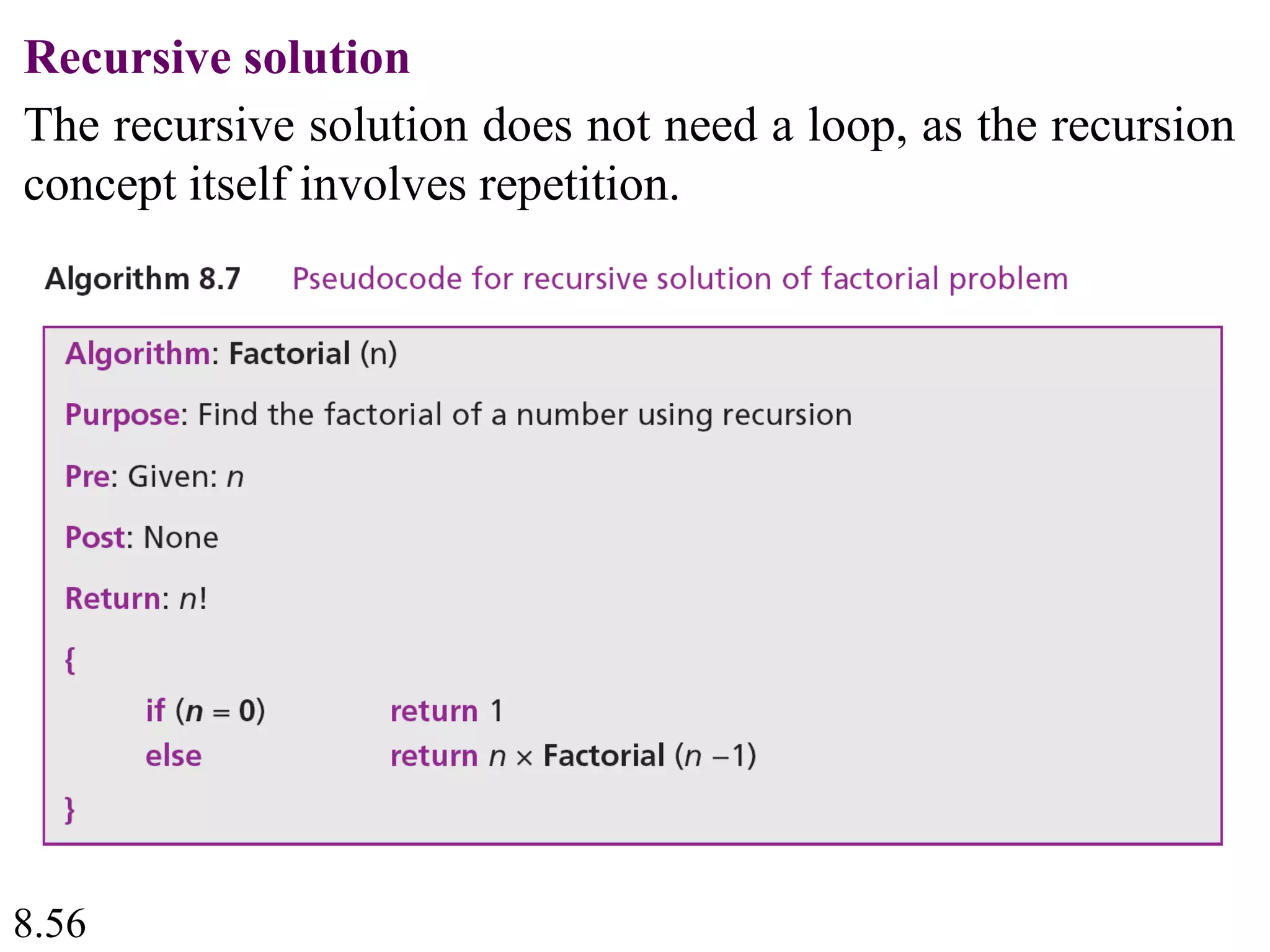
This document discusses algorithms and some basic algorithms used in computer science. It begins by defining an algorithm as a step-by-step method for solving a problem or completing a task. It then describes three common constructs used in algorithms: sequence, decision, and repetition. The document also discusses representations of algorithms using UML diagrams and pseudocode. Finally, it provides examples of basic algorithms like summation, product, and finding the smallest/largest values; and describes the general logic and structure of algorithms for addition, multiplication, and minimum/maximum calculations.