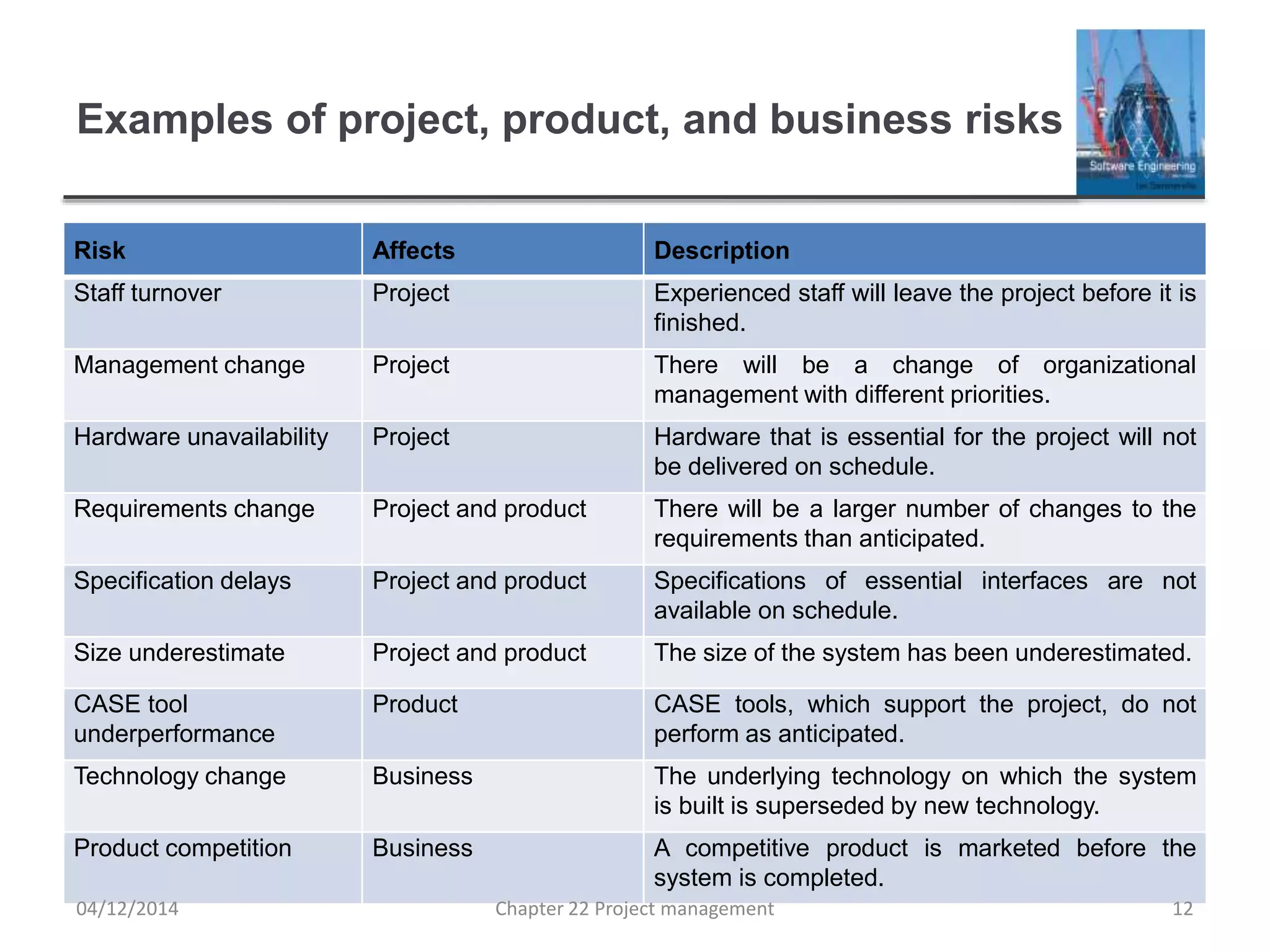
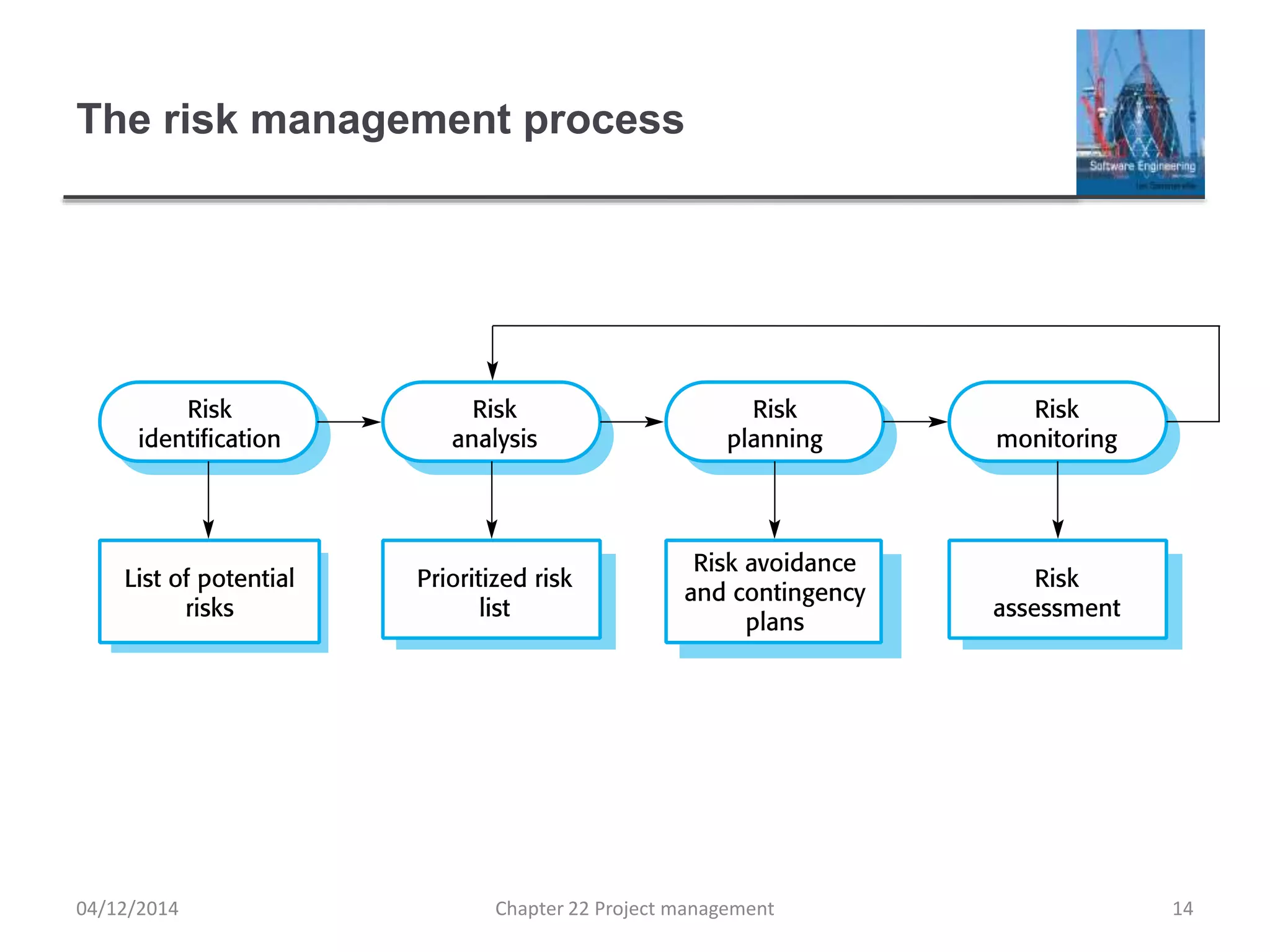
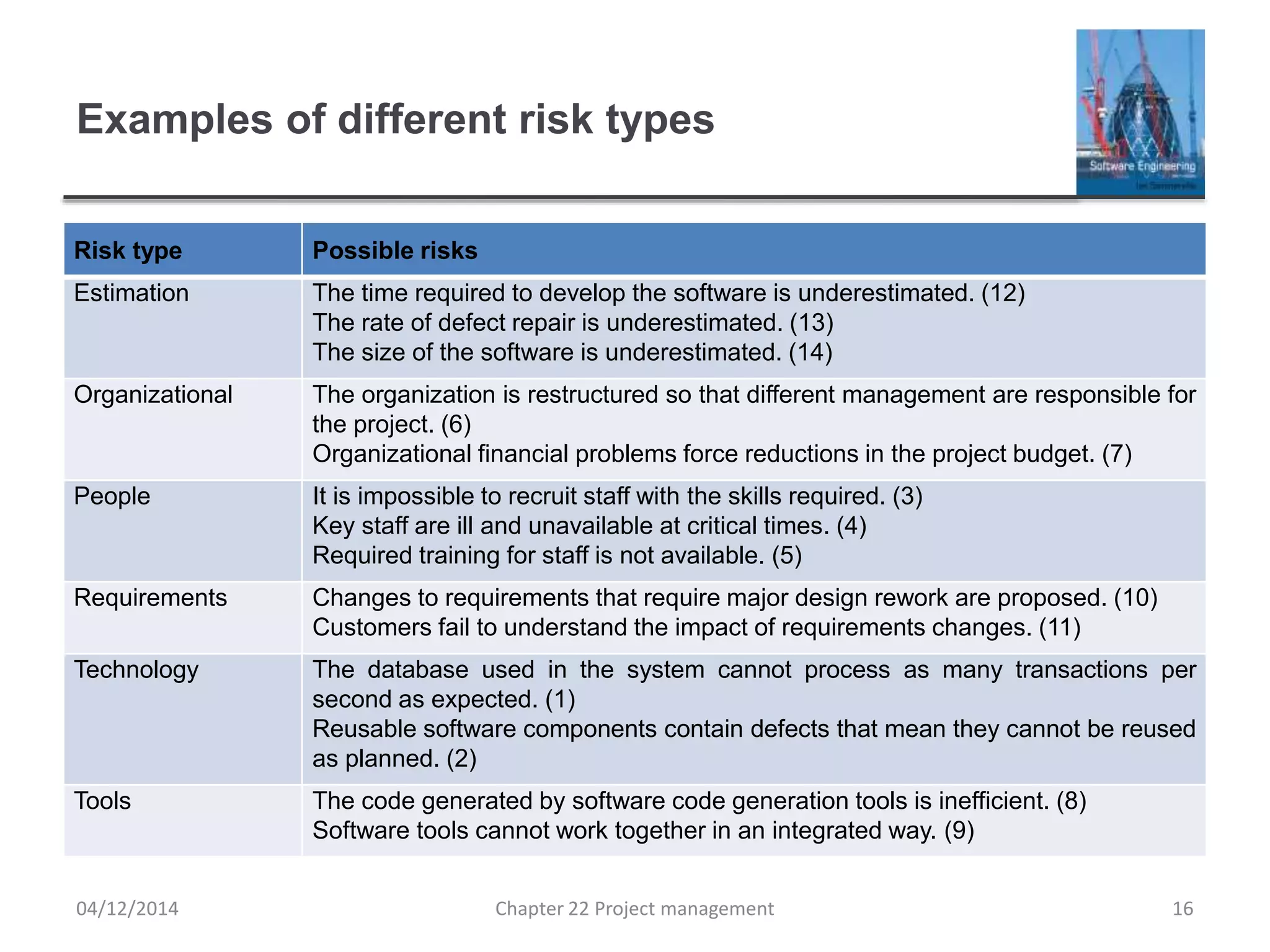
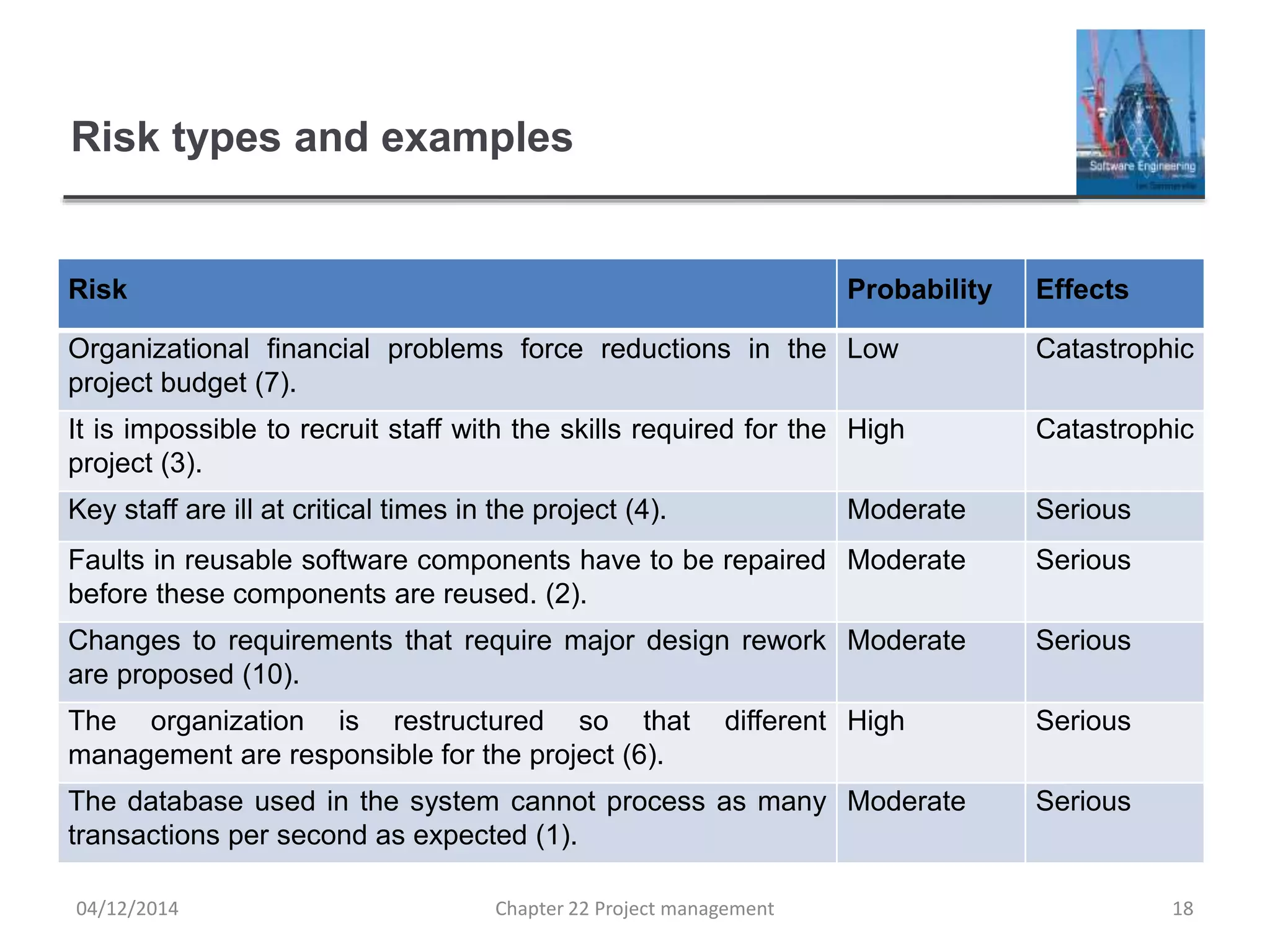
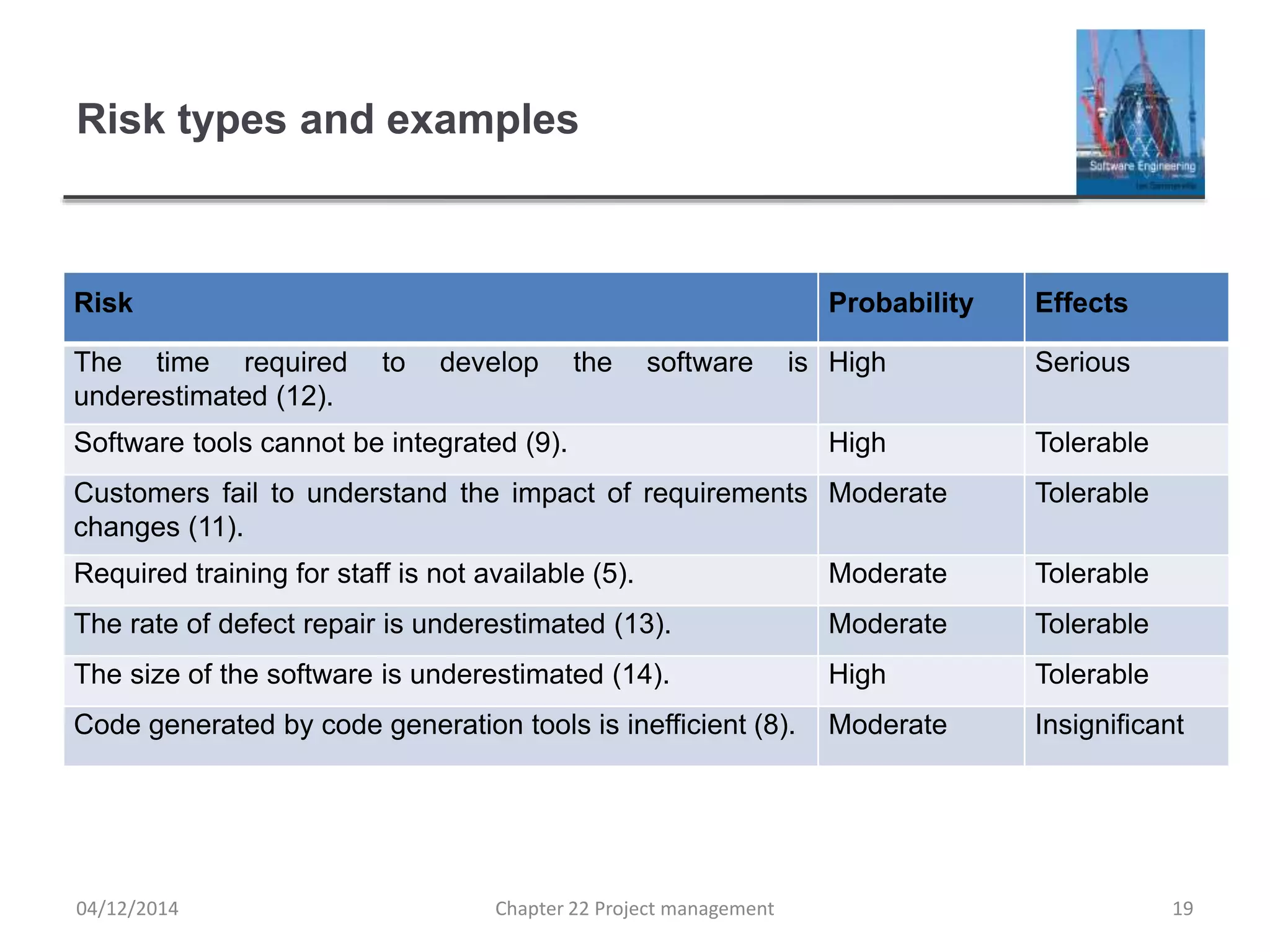
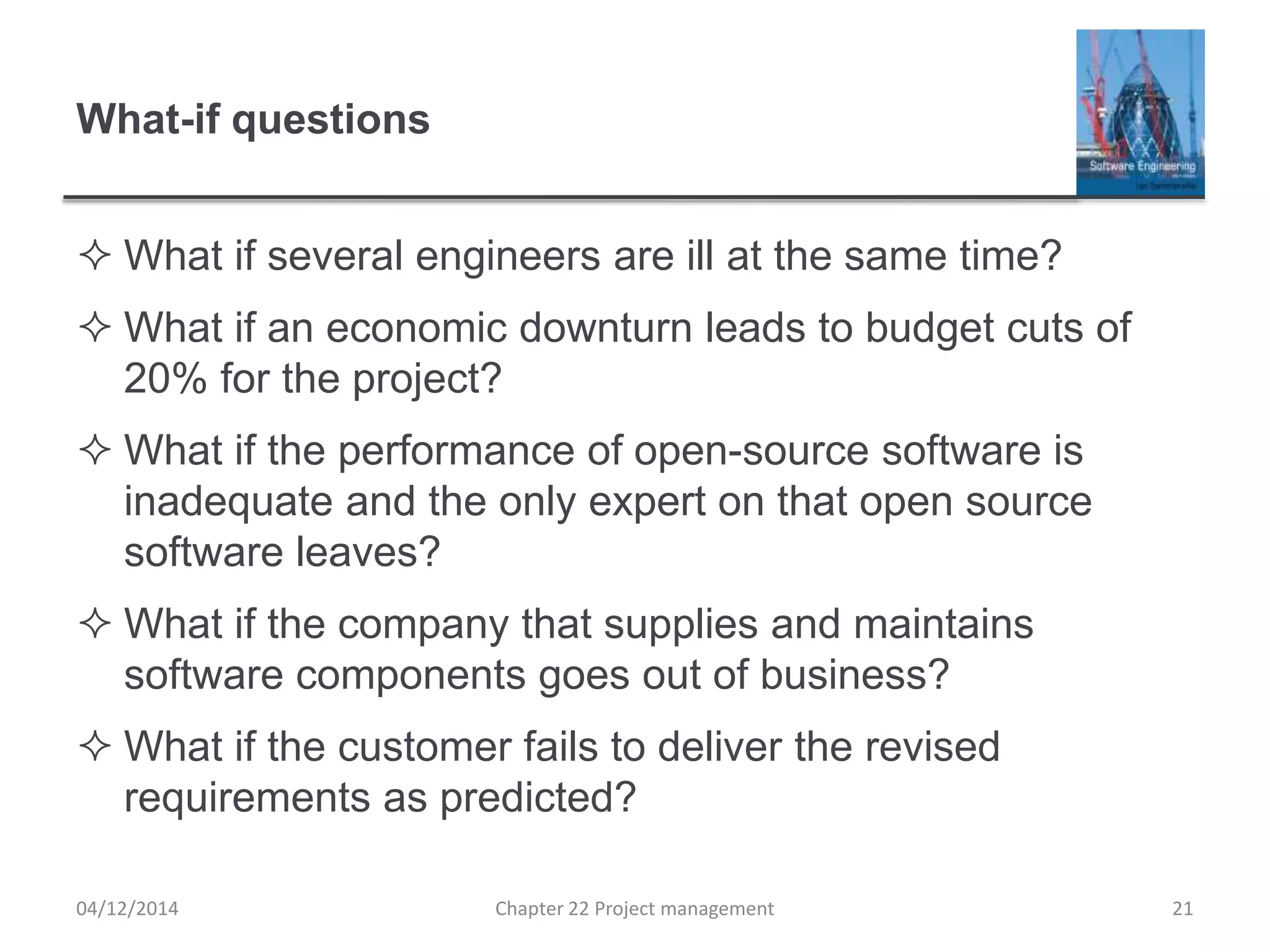
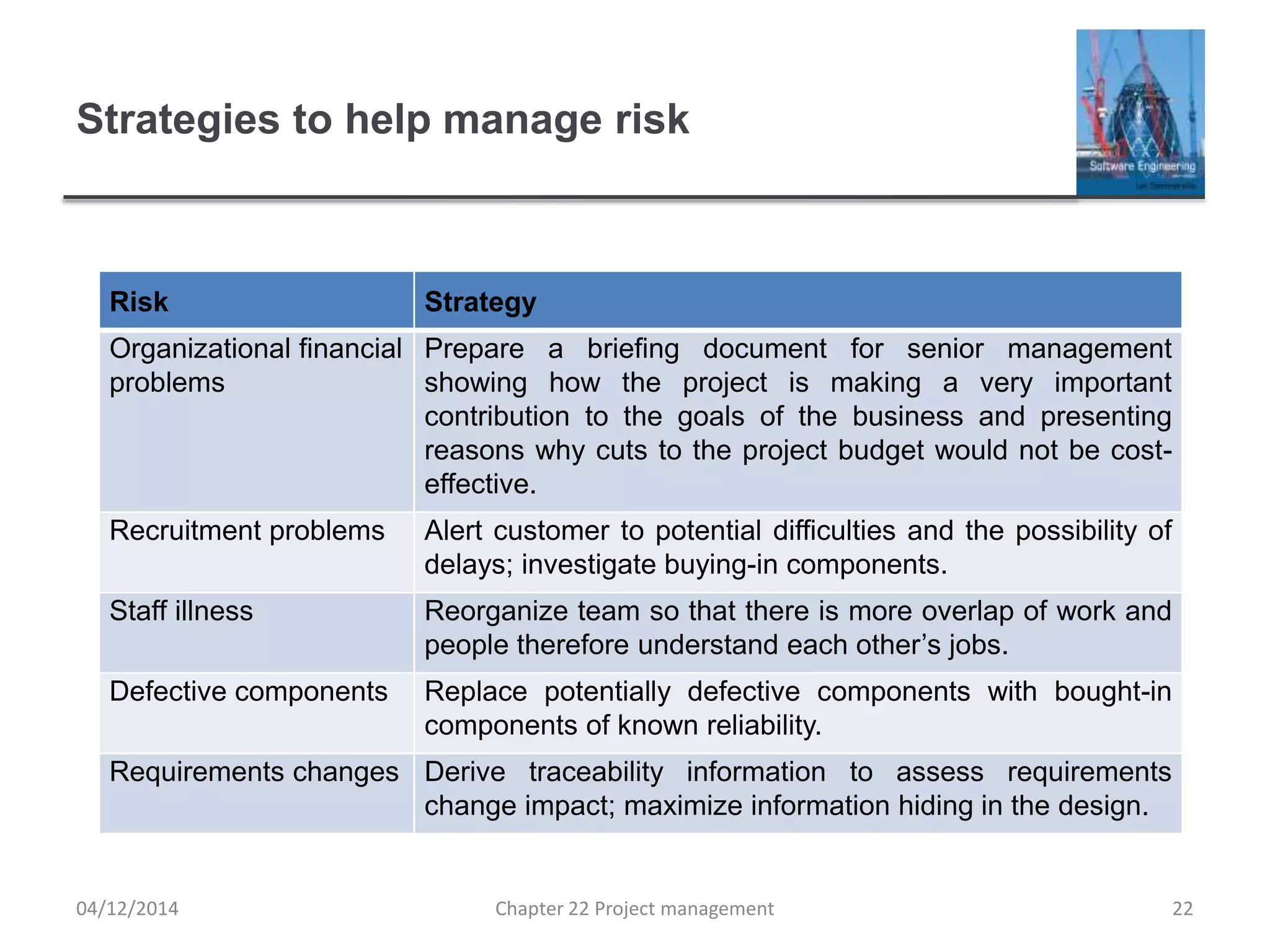
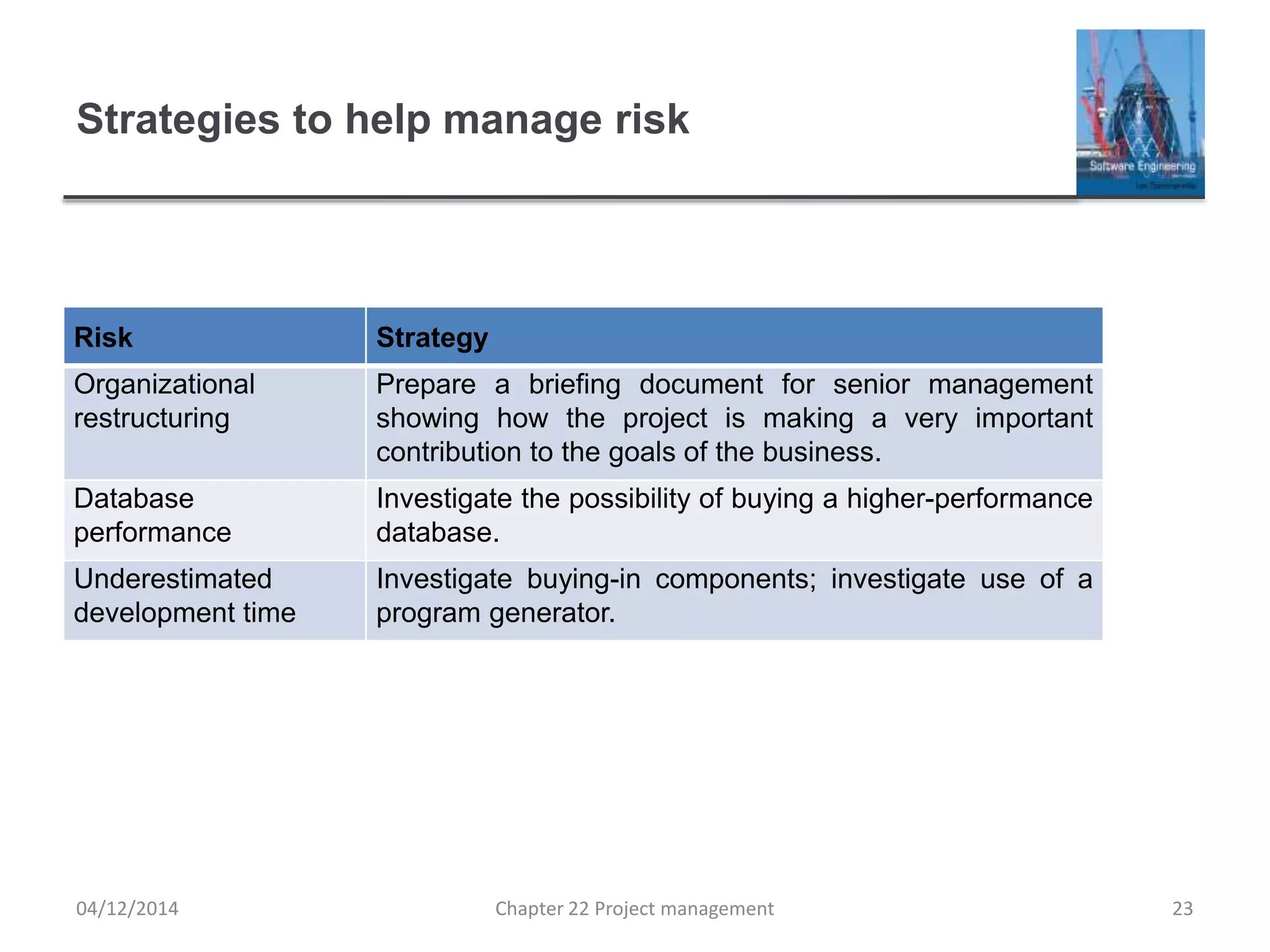
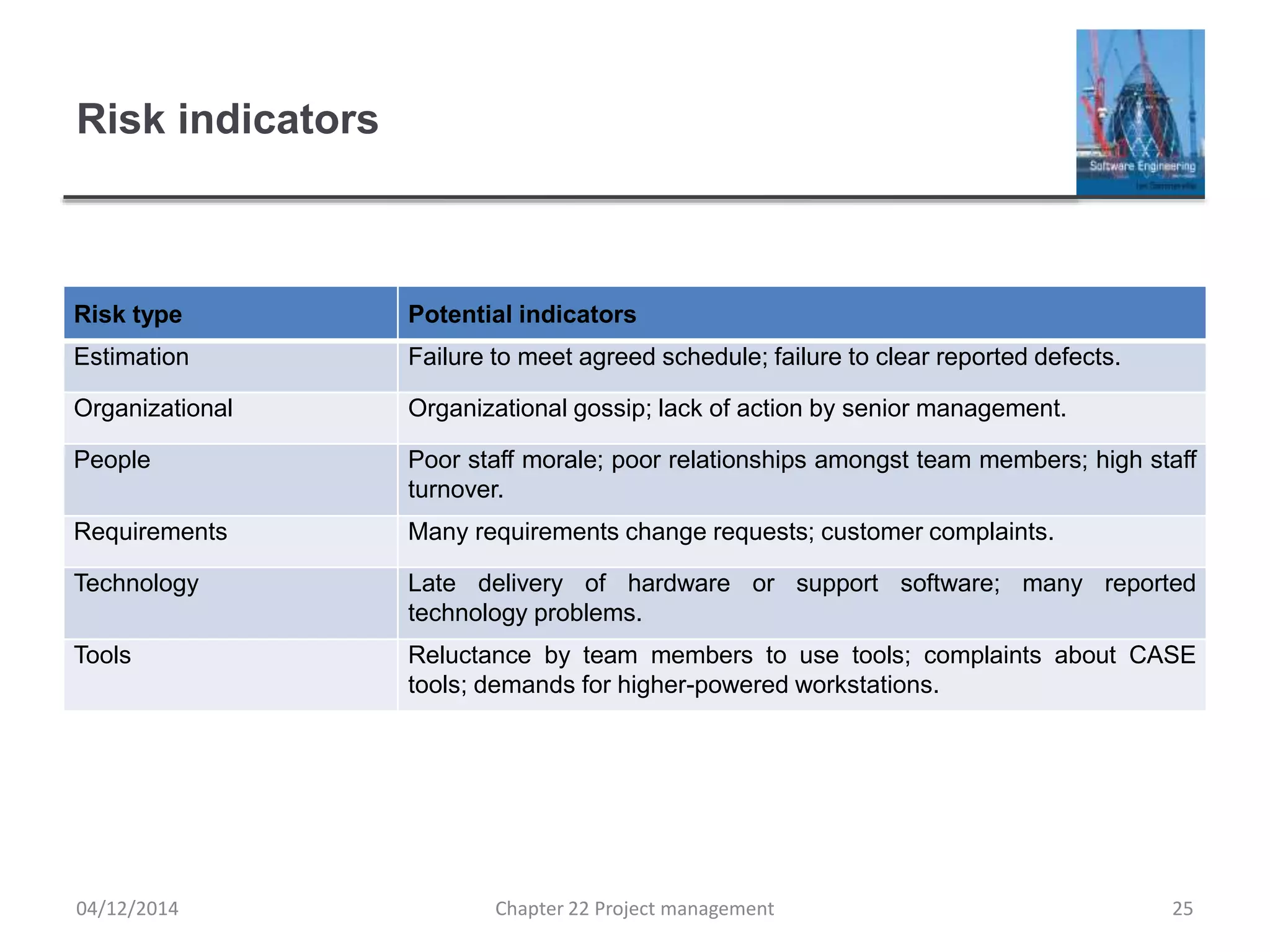
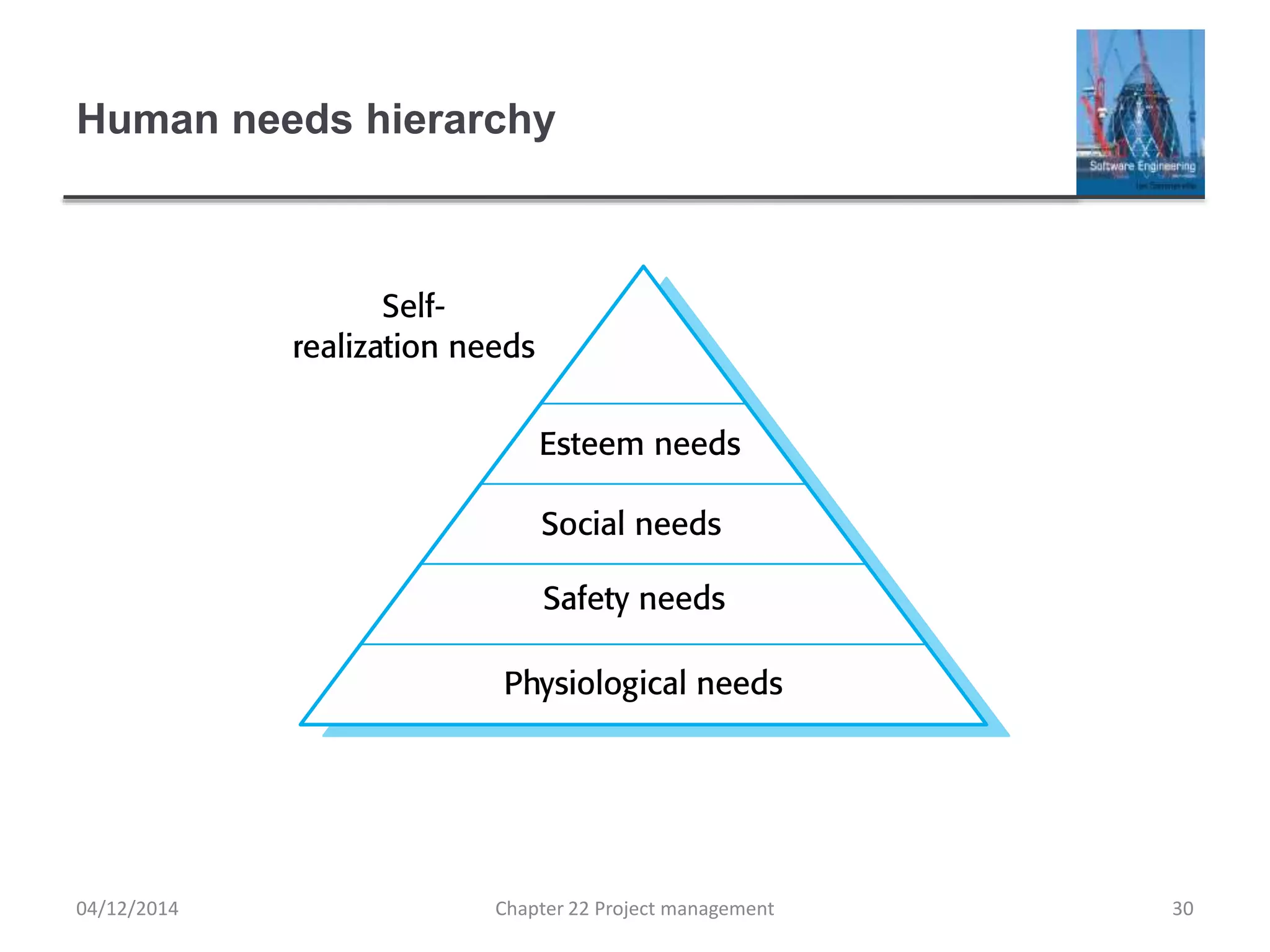
The document discusses several aspects of software project management including risk management, managing people, and teamwork. It describes the risk management process of identifying, analyzing, planning for, and monitoring risks. Examples of different types of project, product, and business risks are provided. The document also discusses the importance of people management in projects and different personality types and motivations that managers should consider. Motivation factors like an individual's needs hierarchy and creating a balanced environment are addressed.