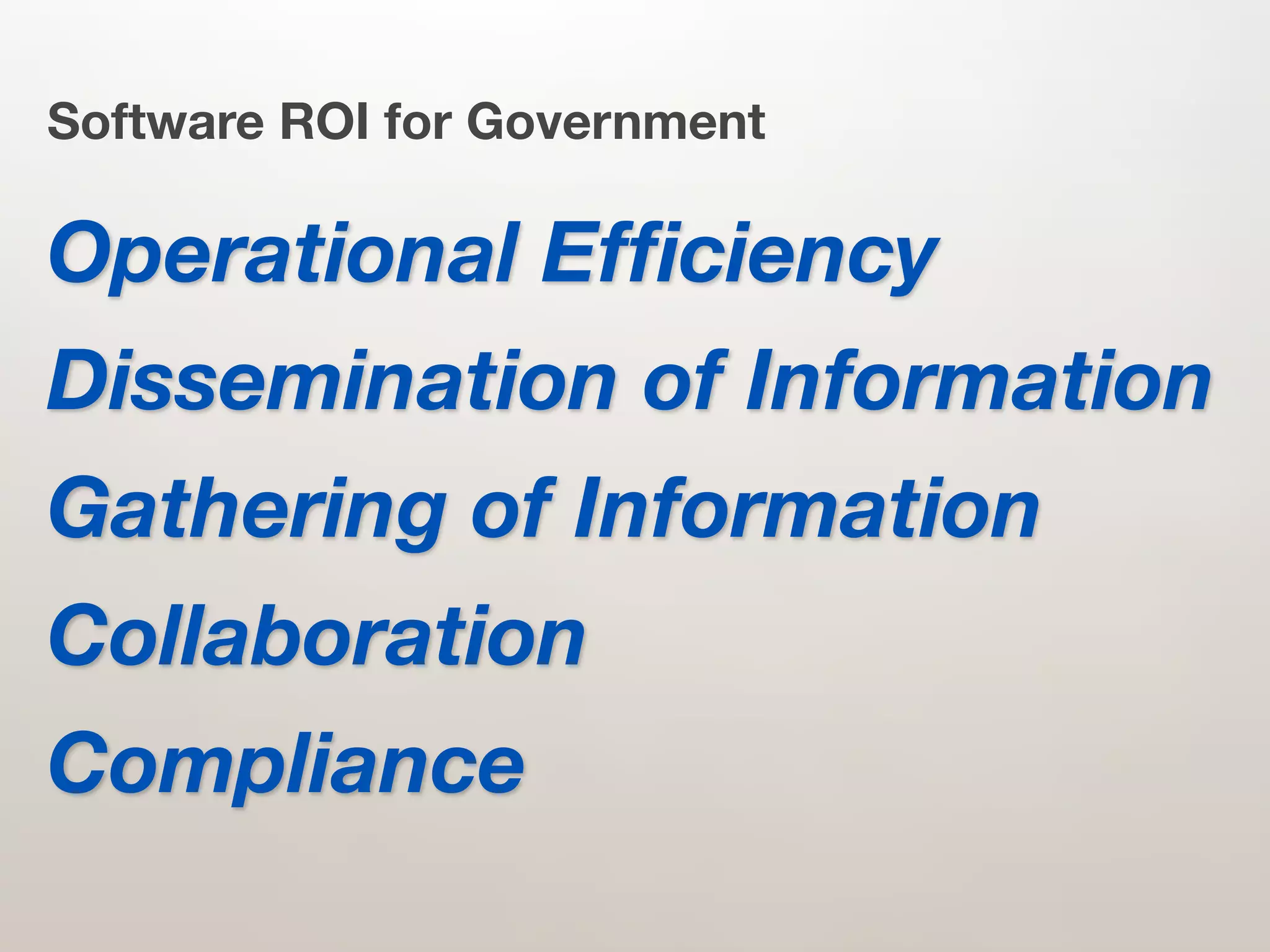
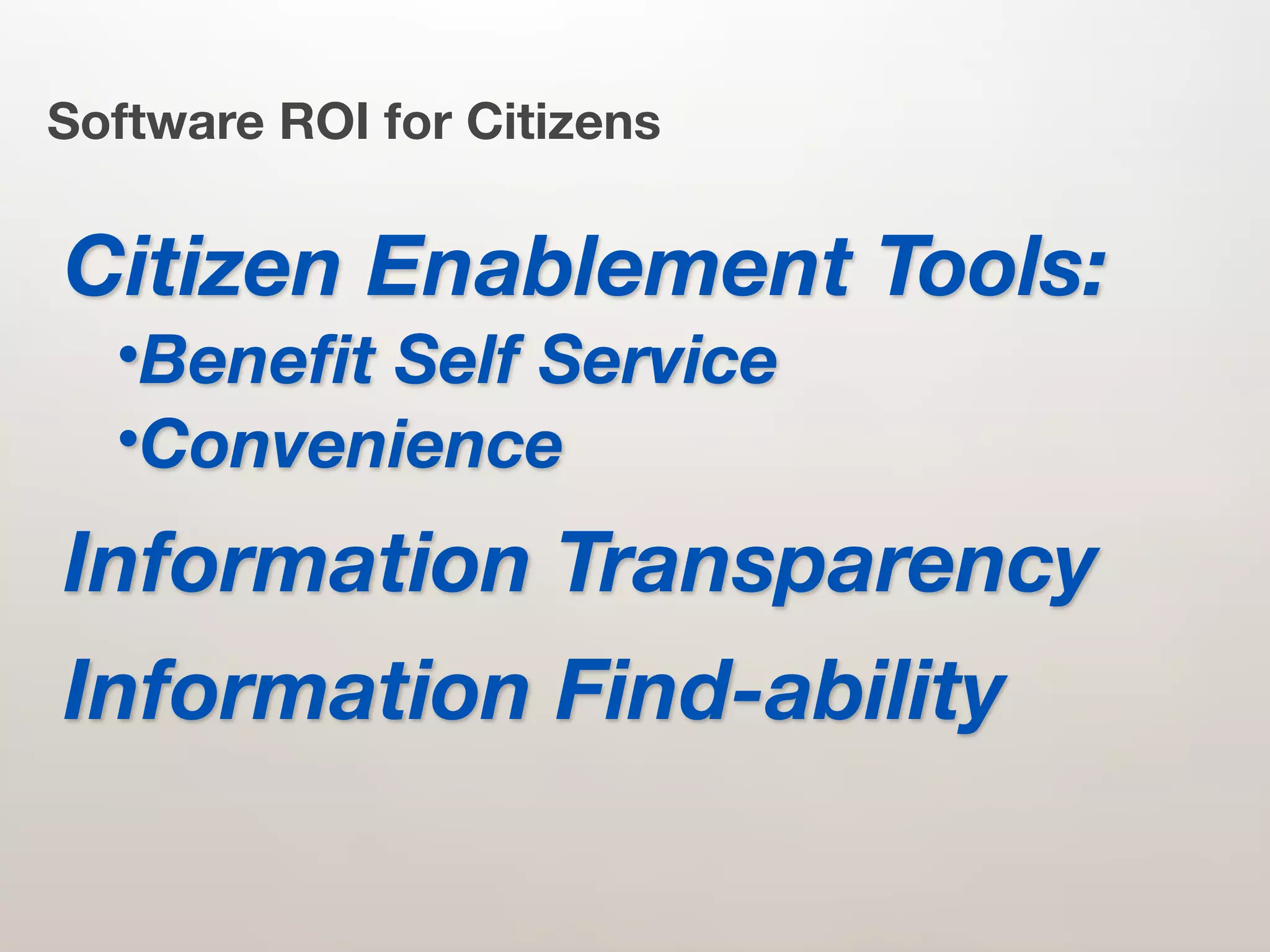
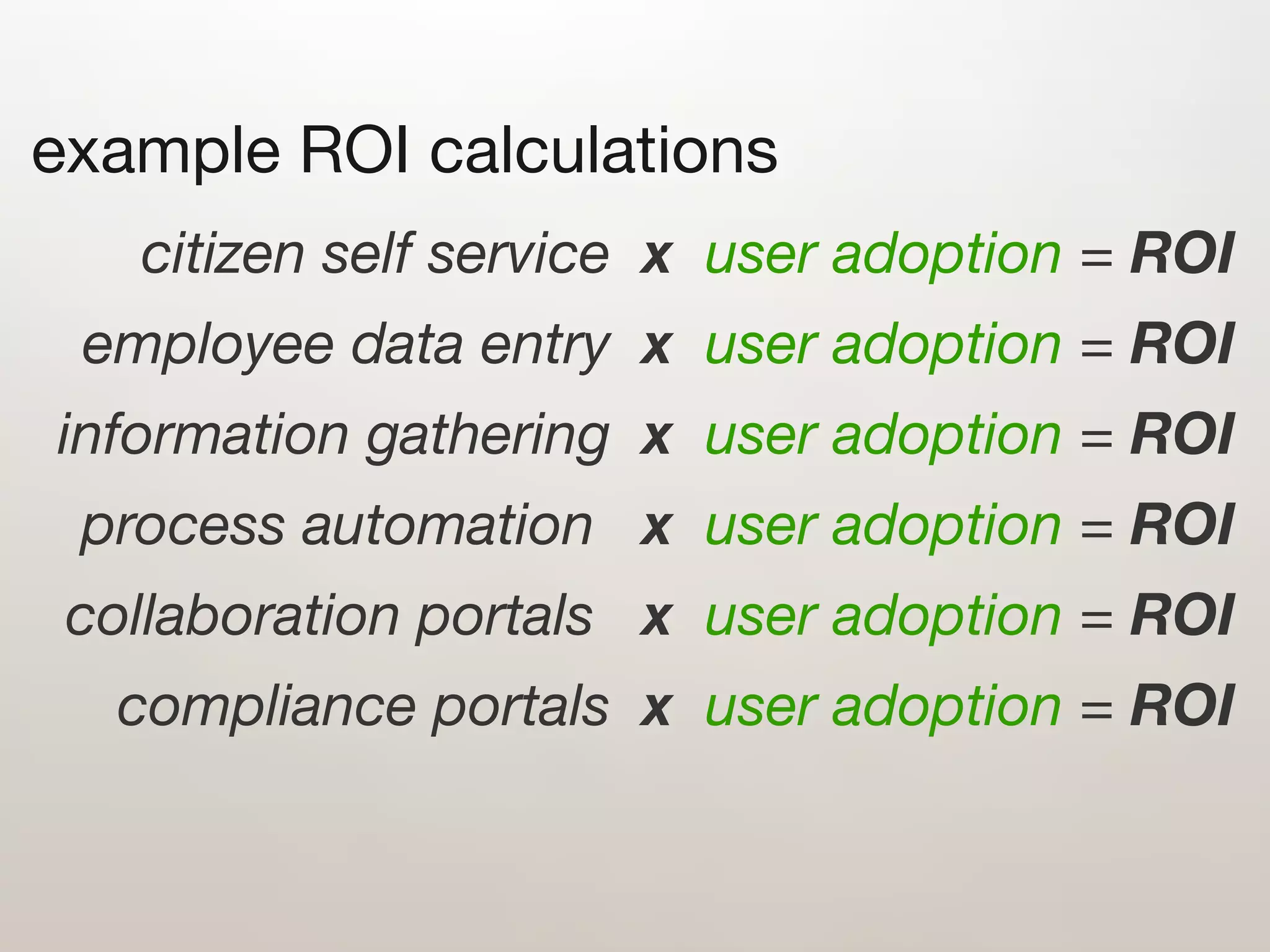
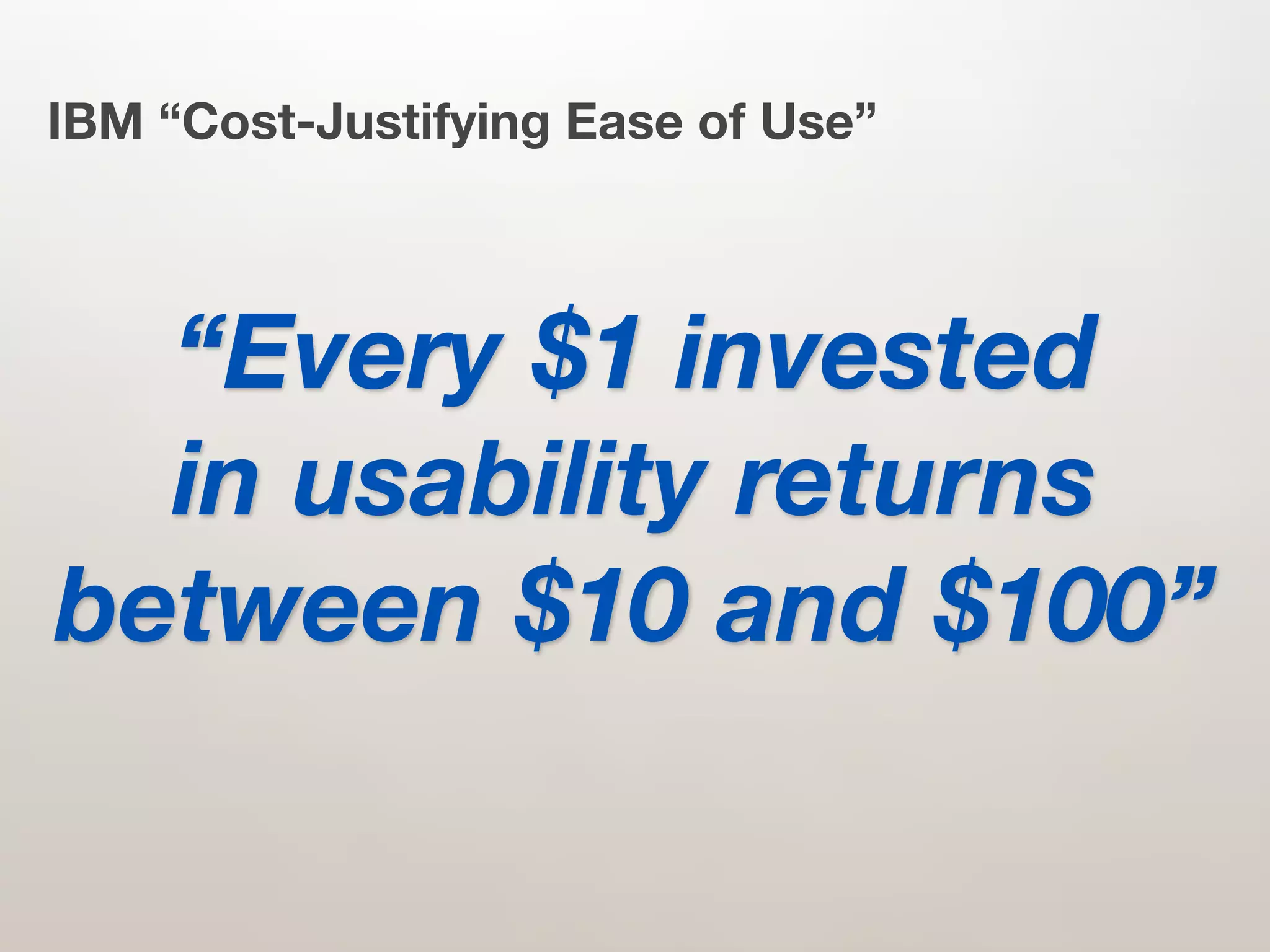
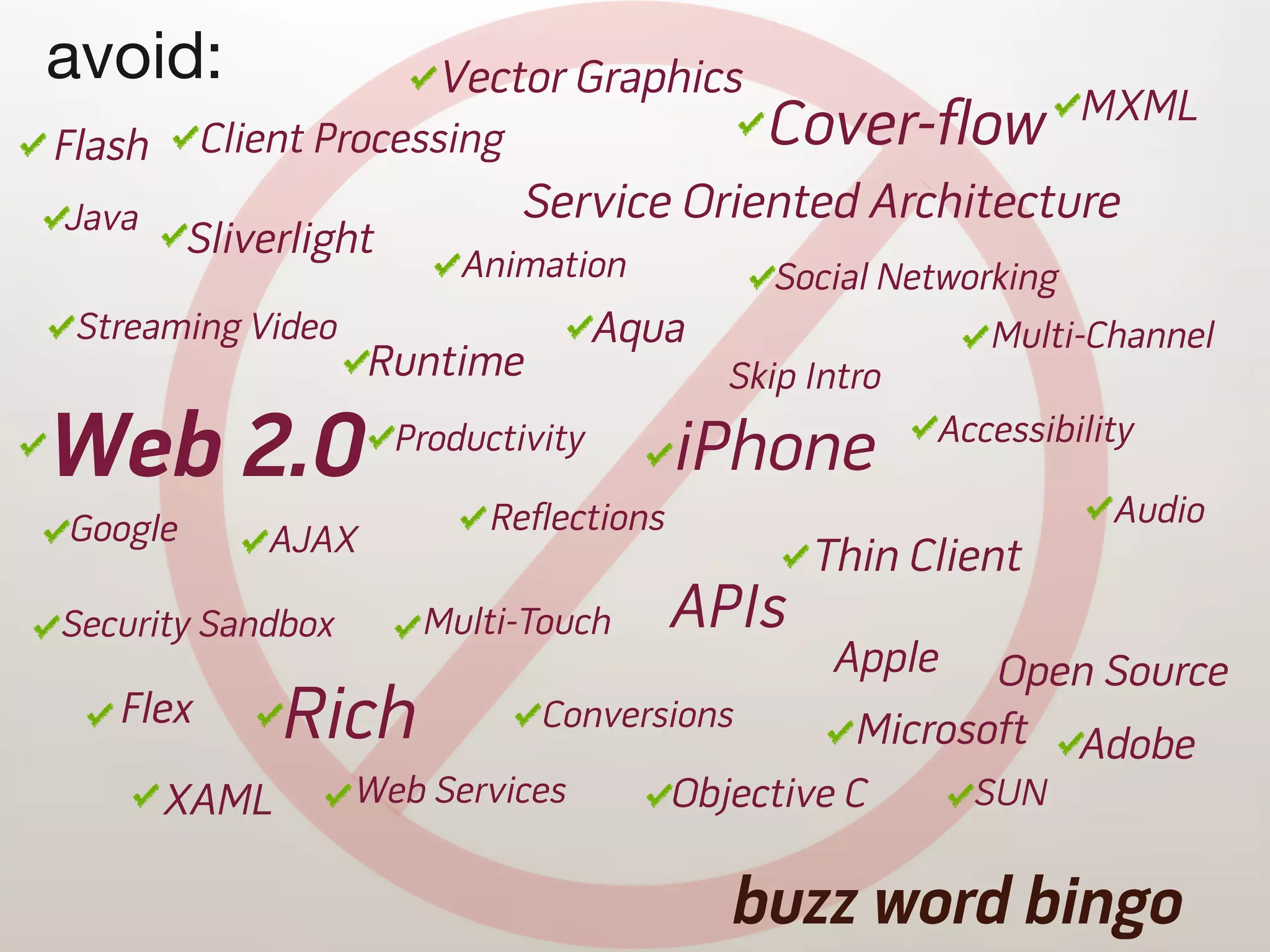
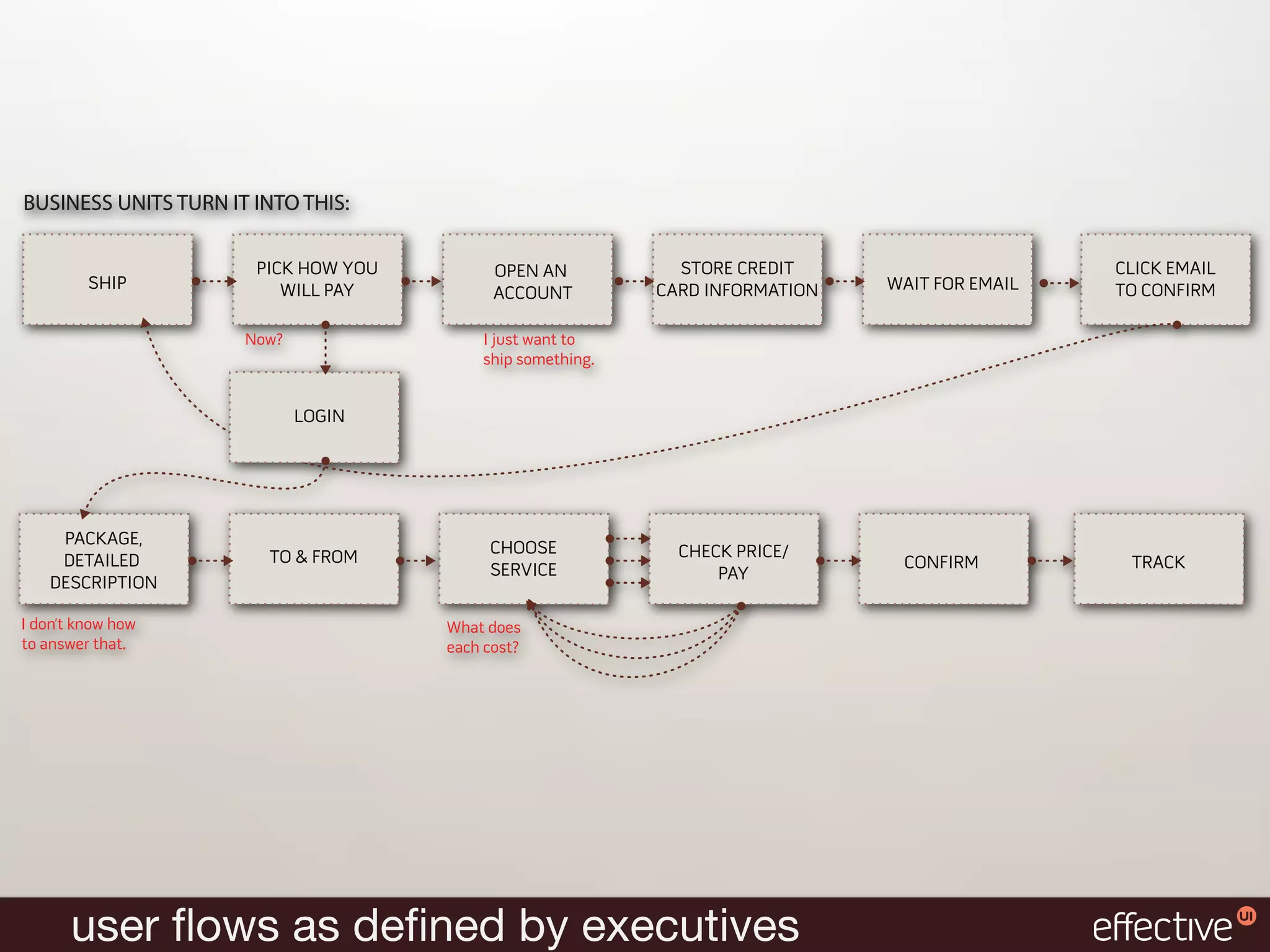
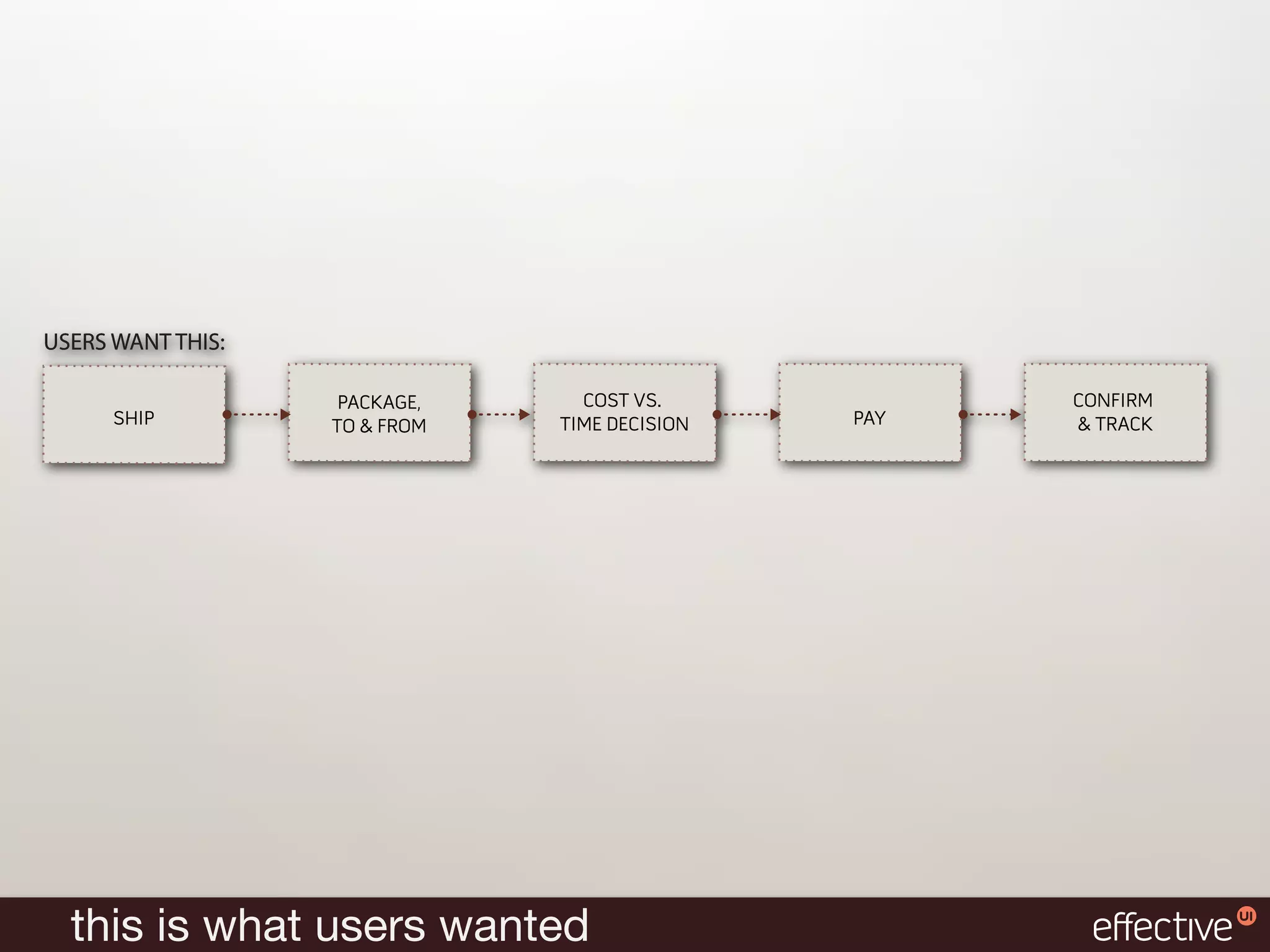
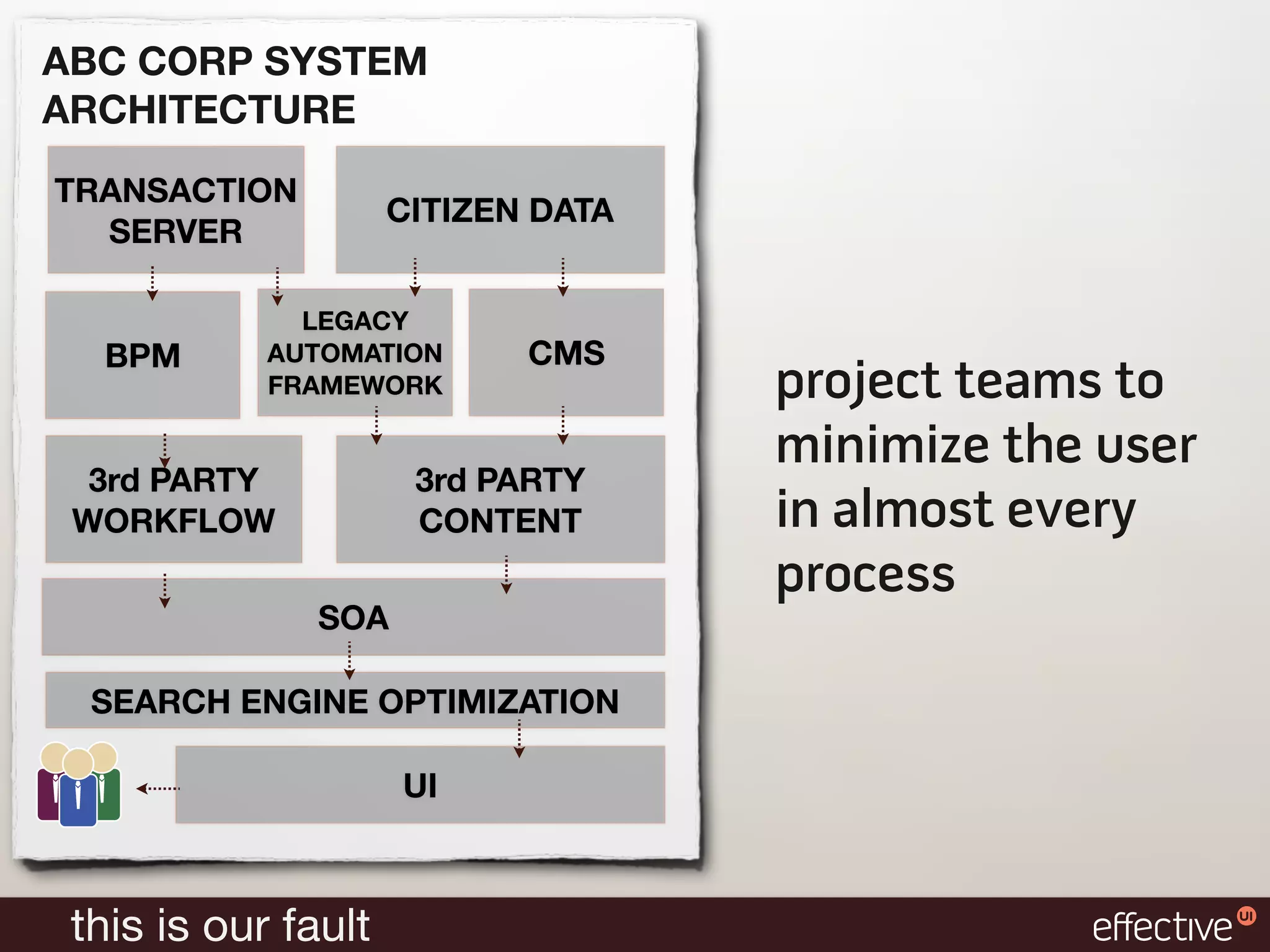
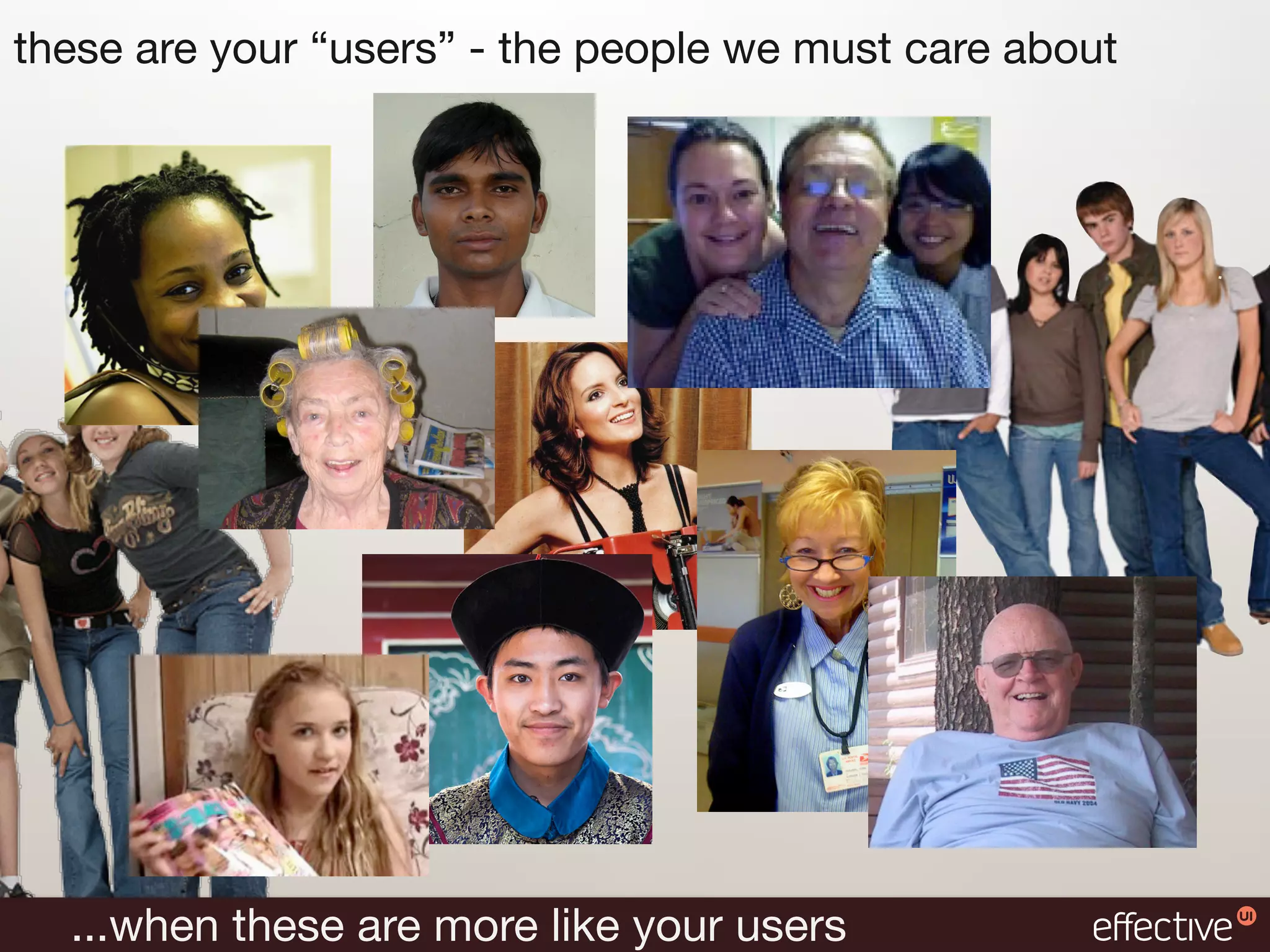
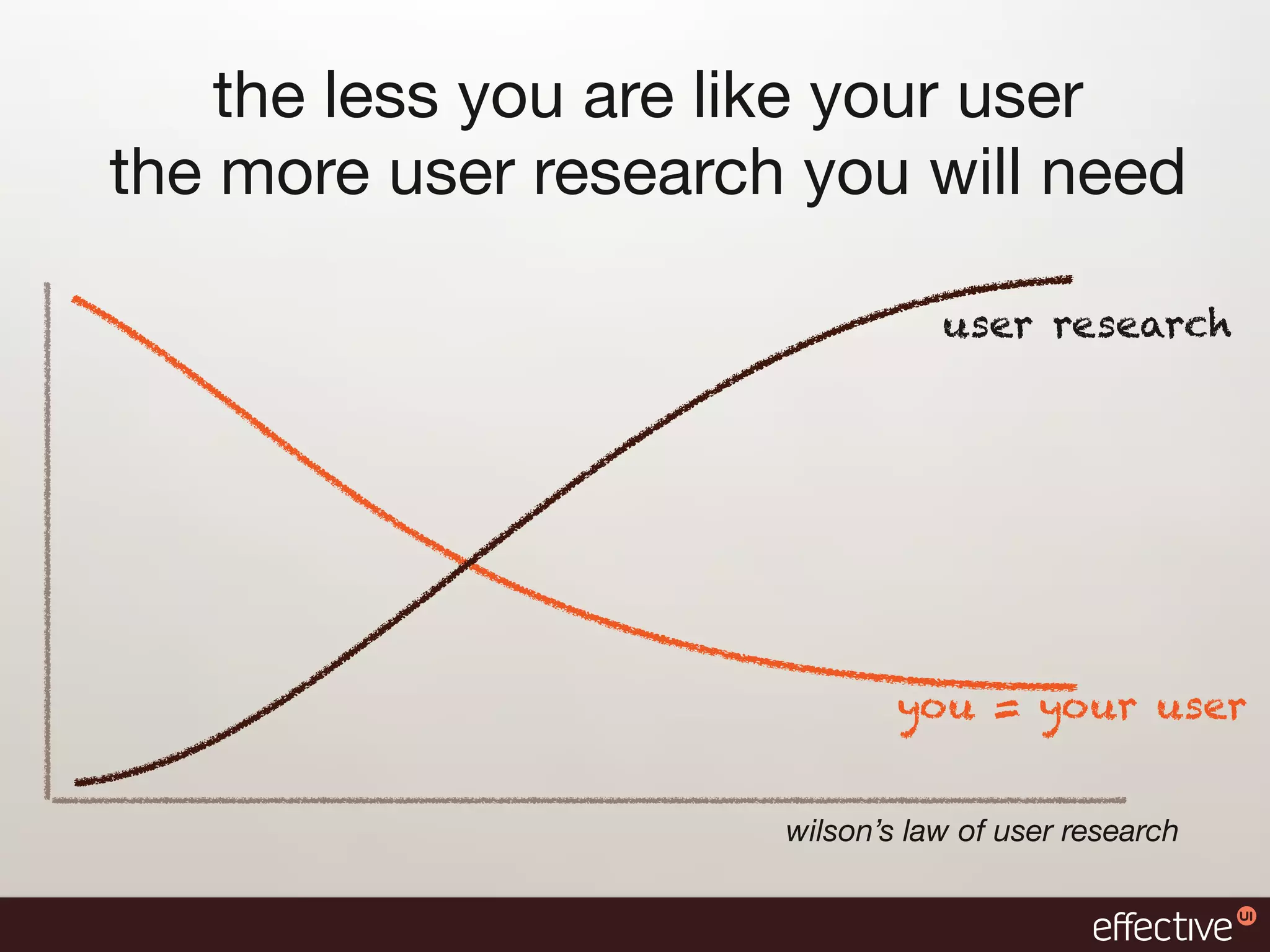
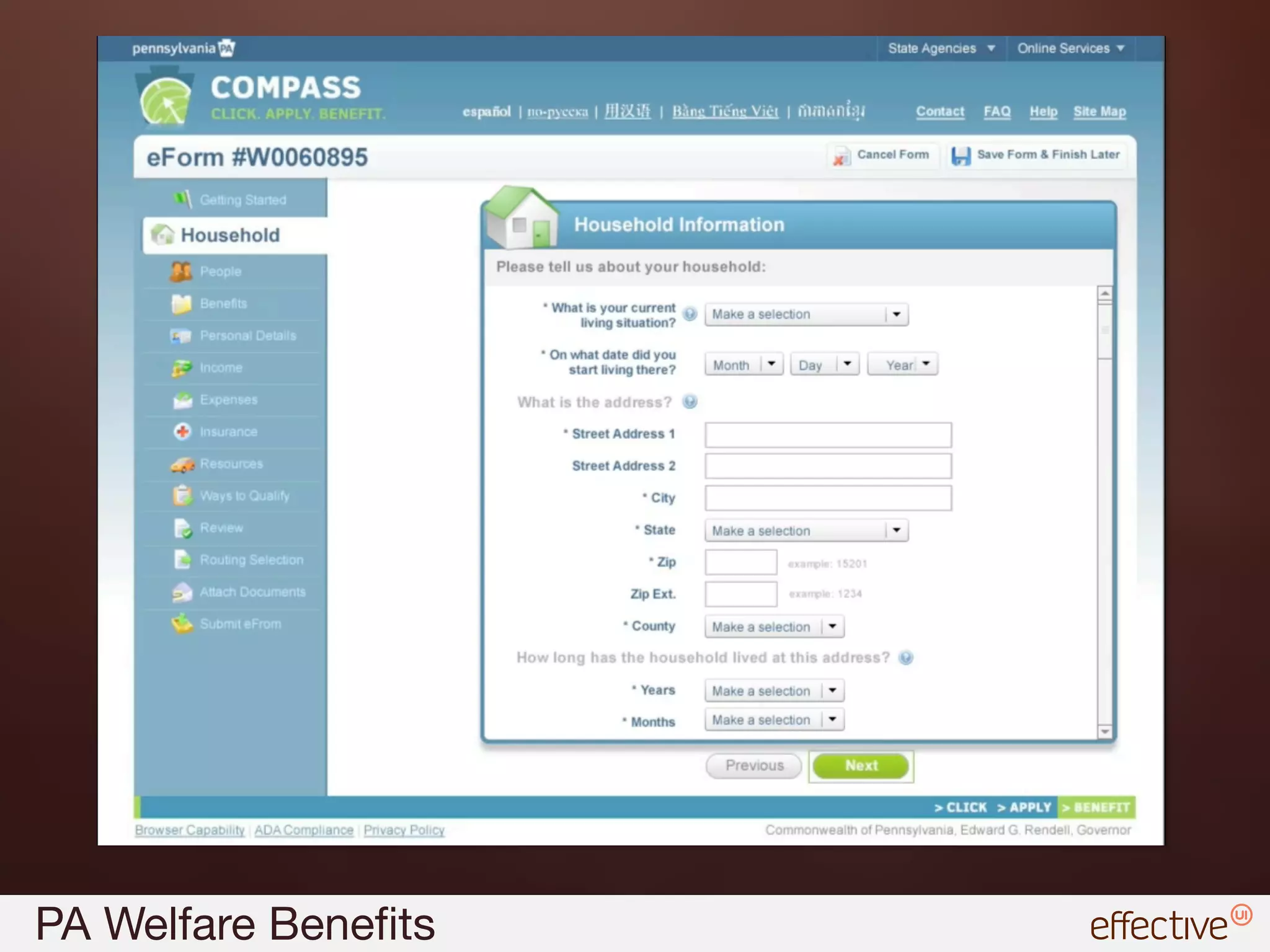
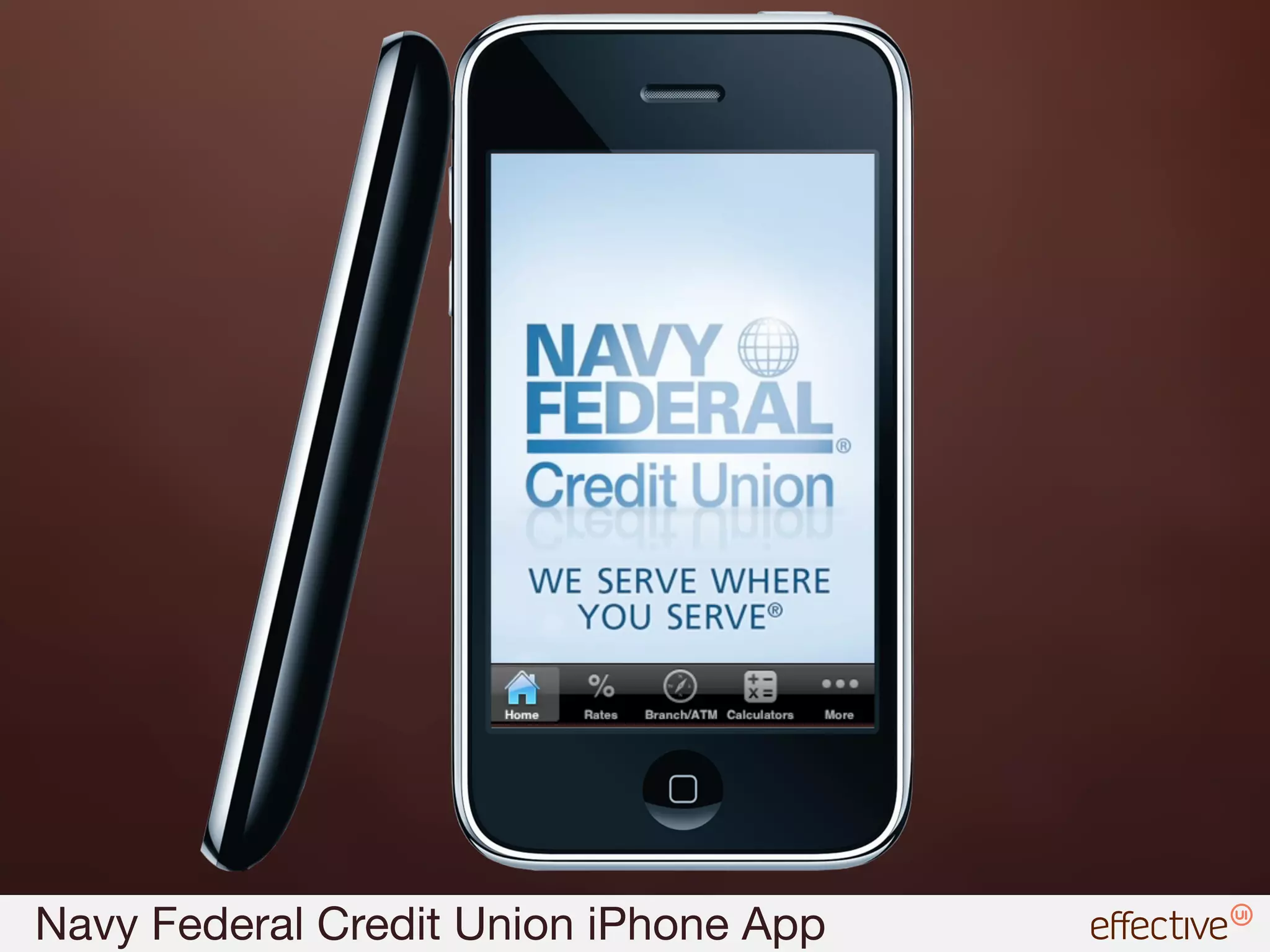
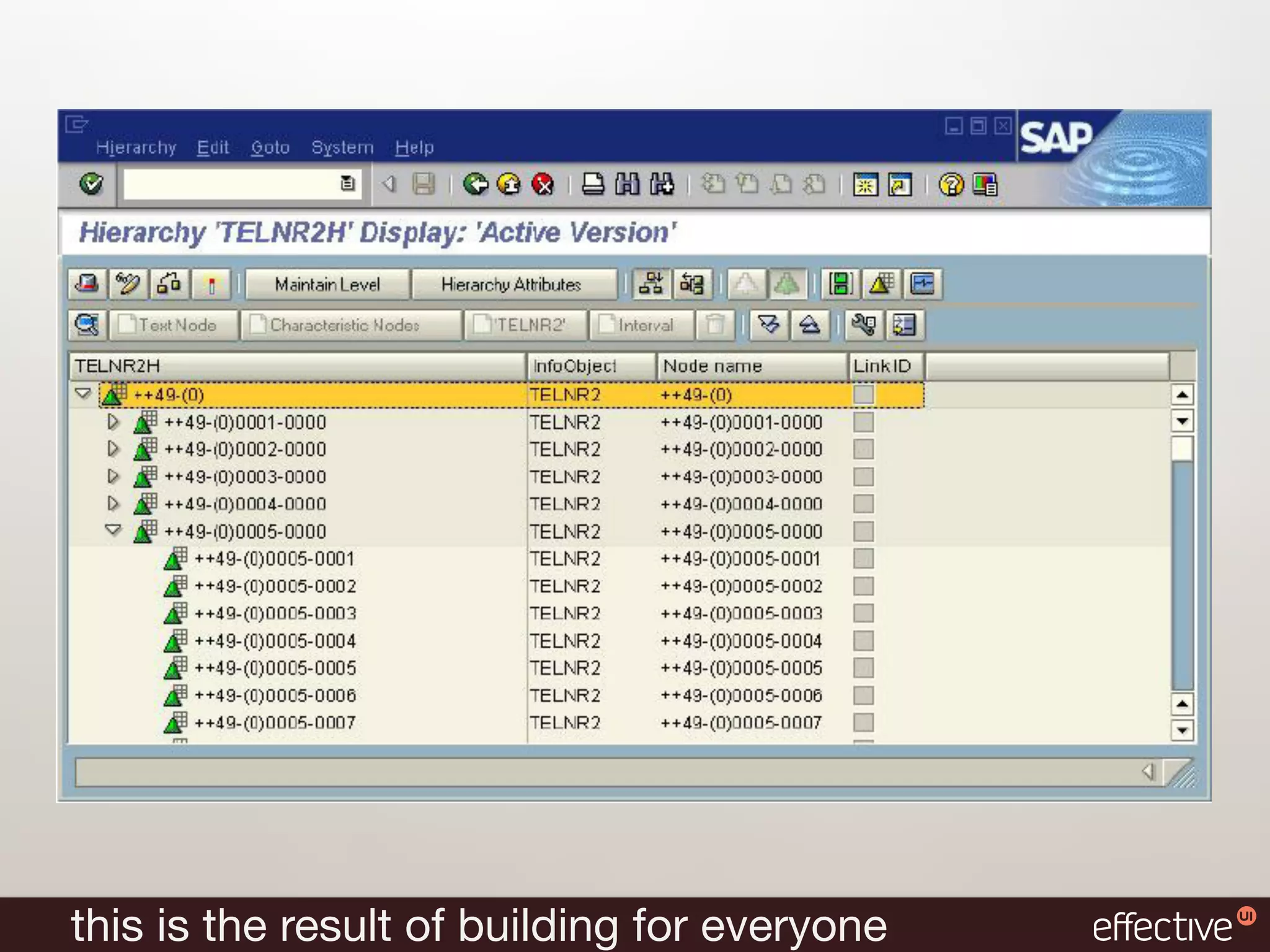
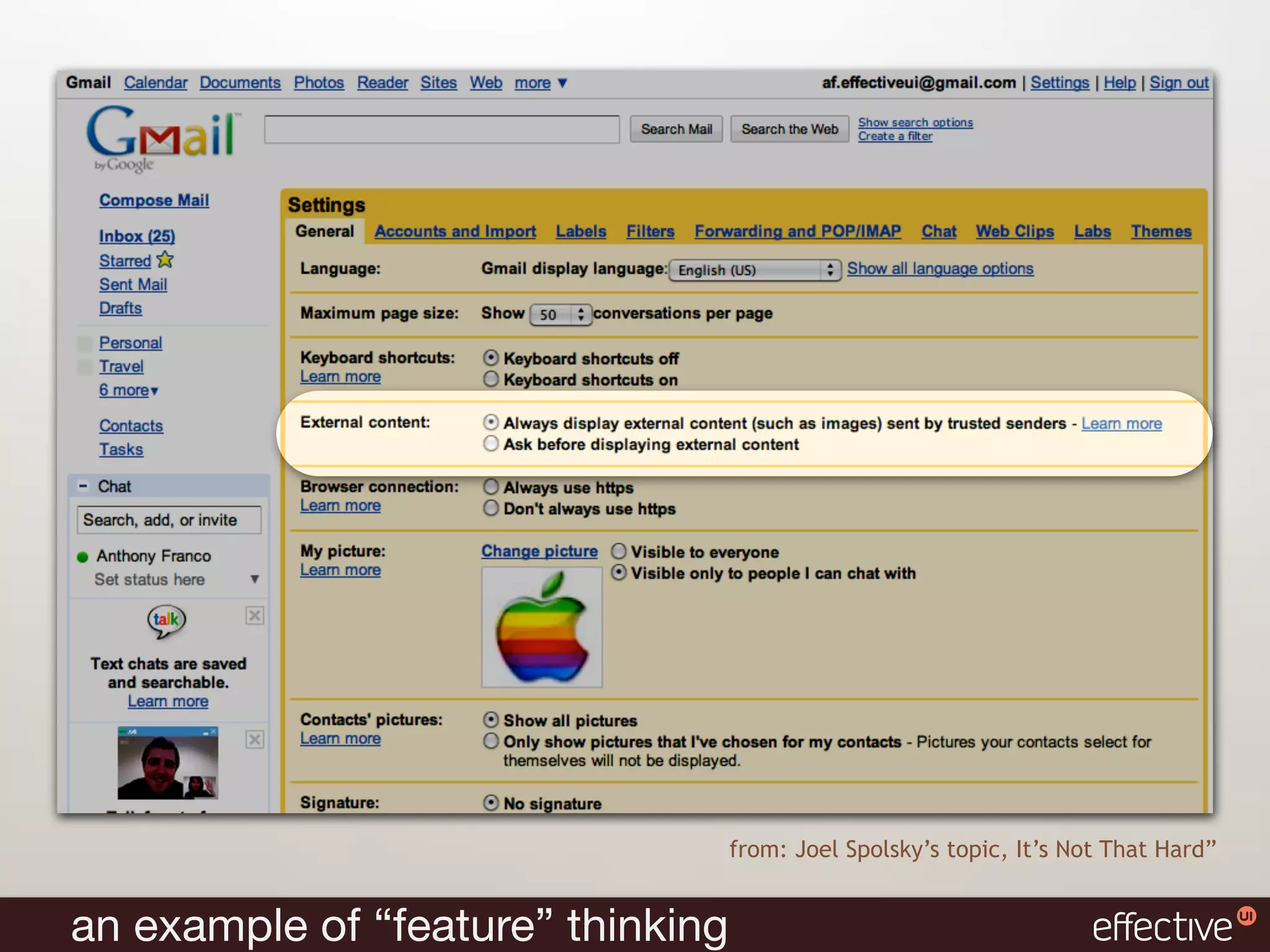
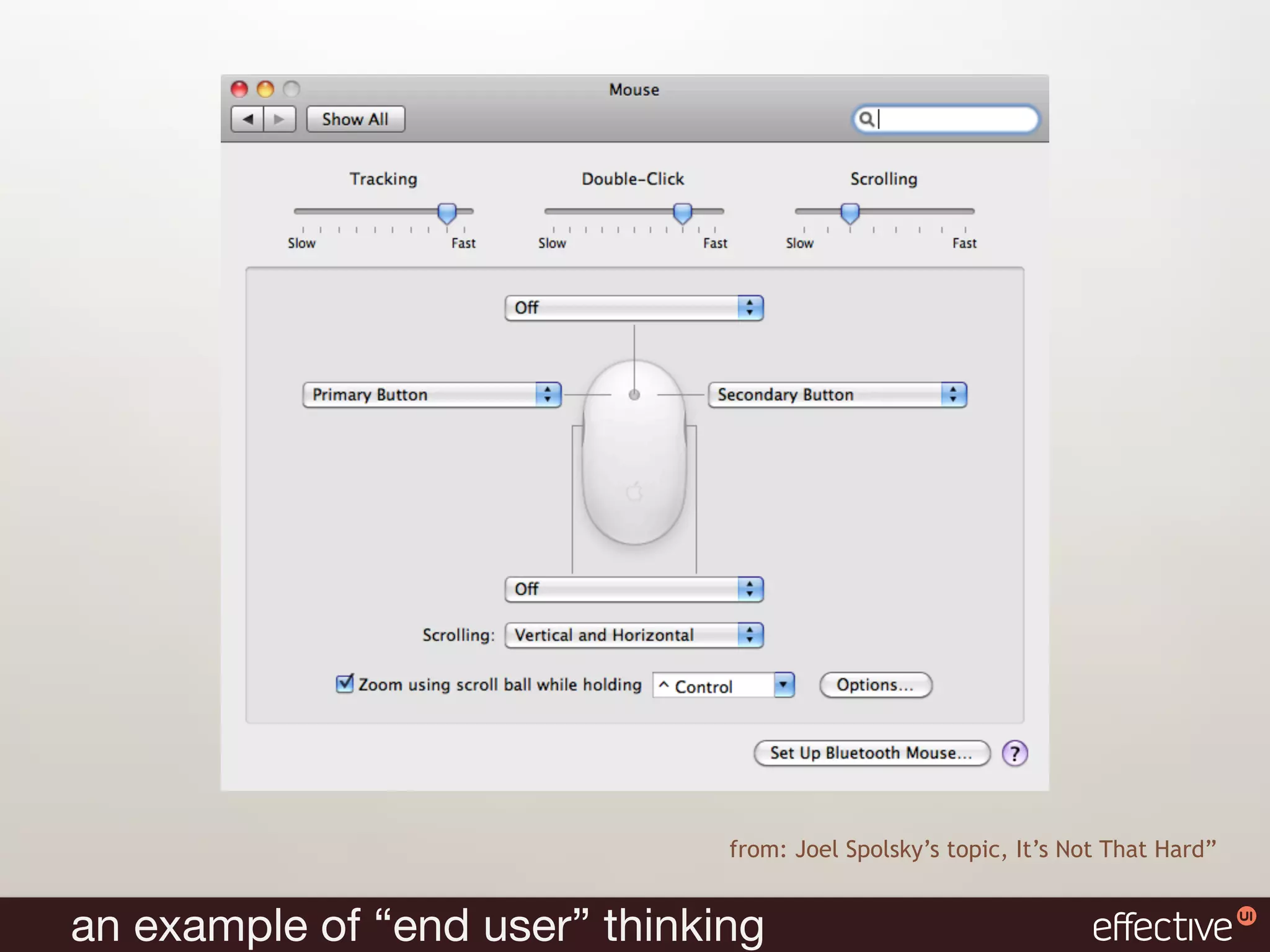
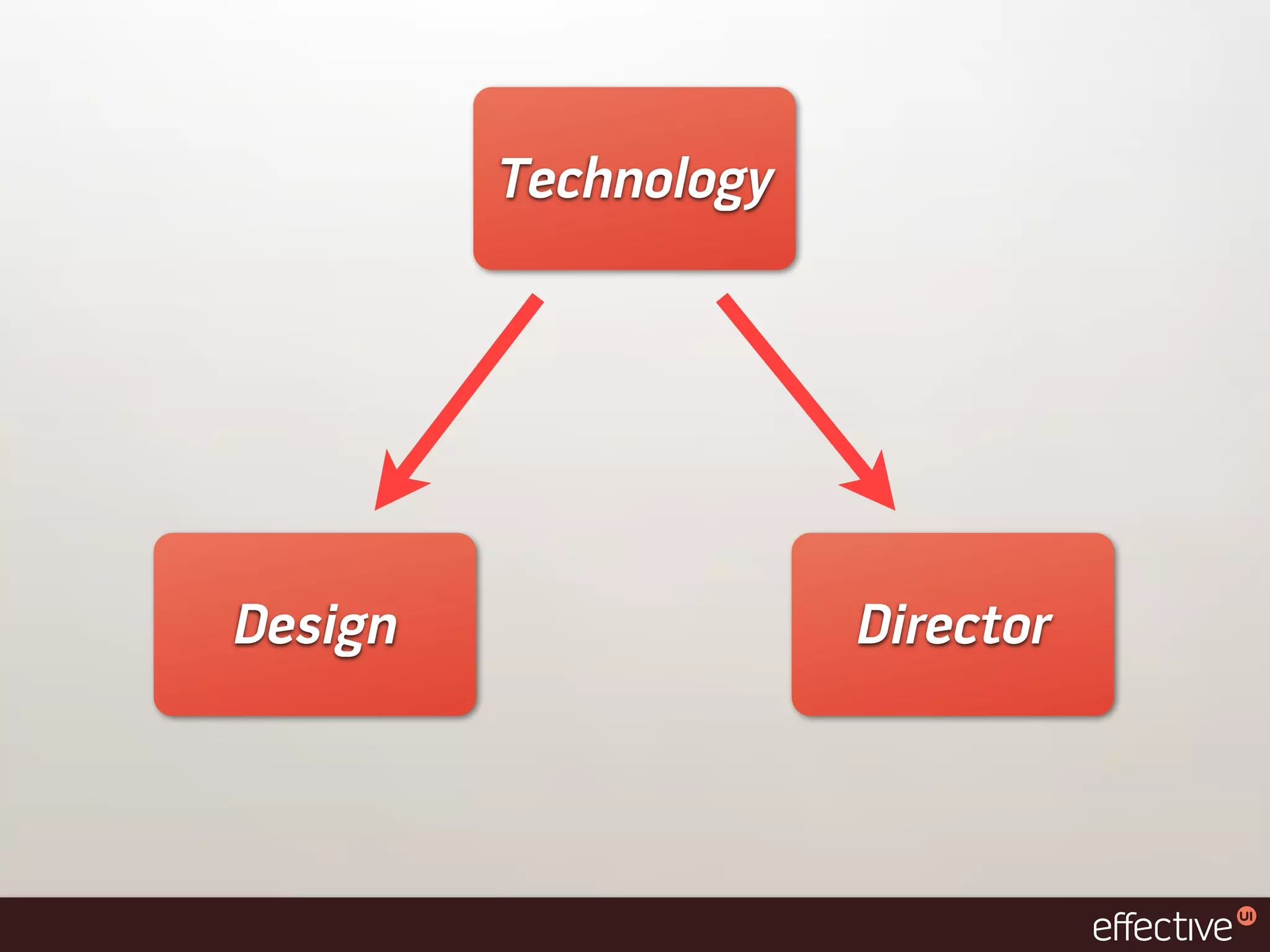
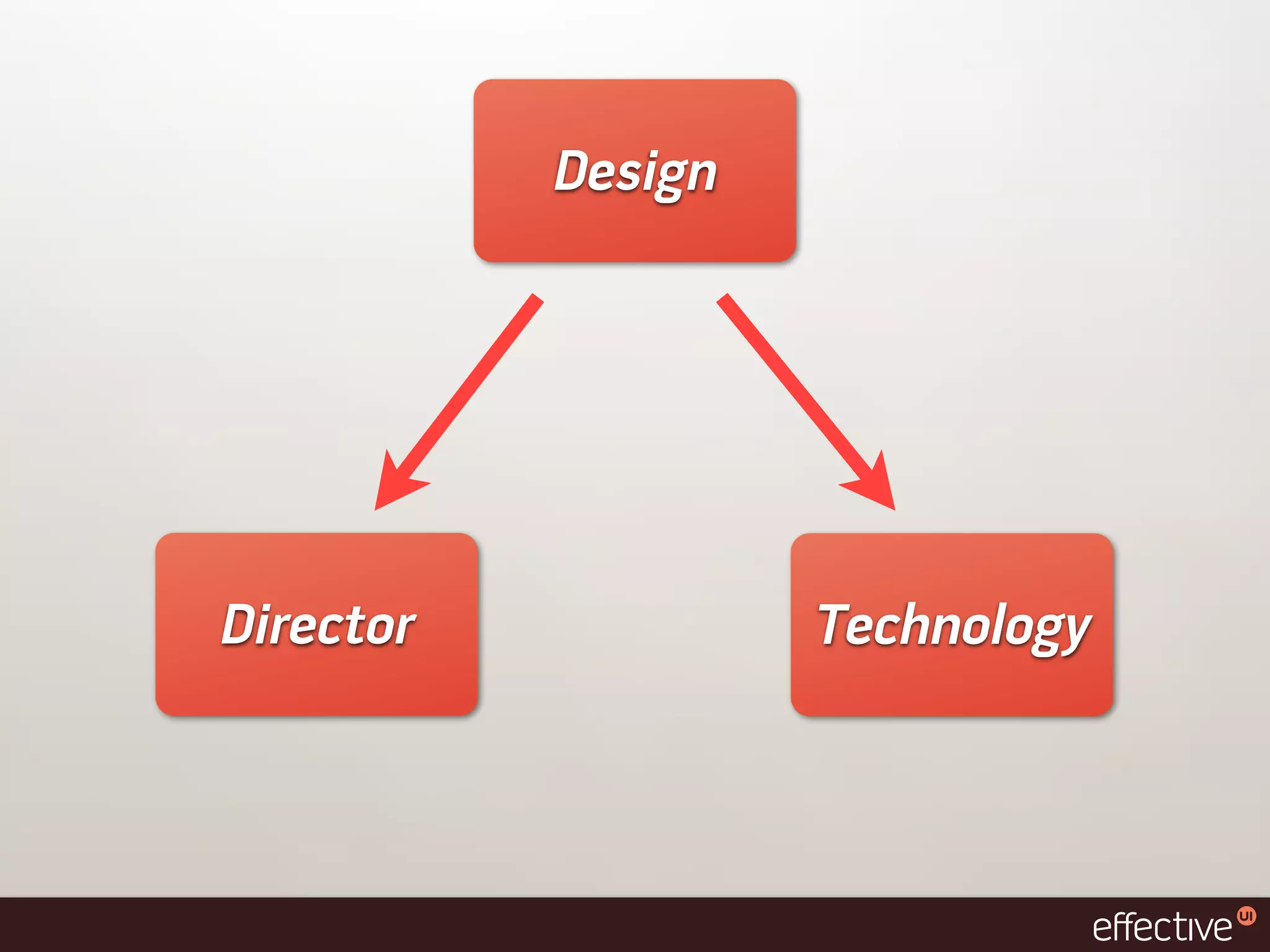
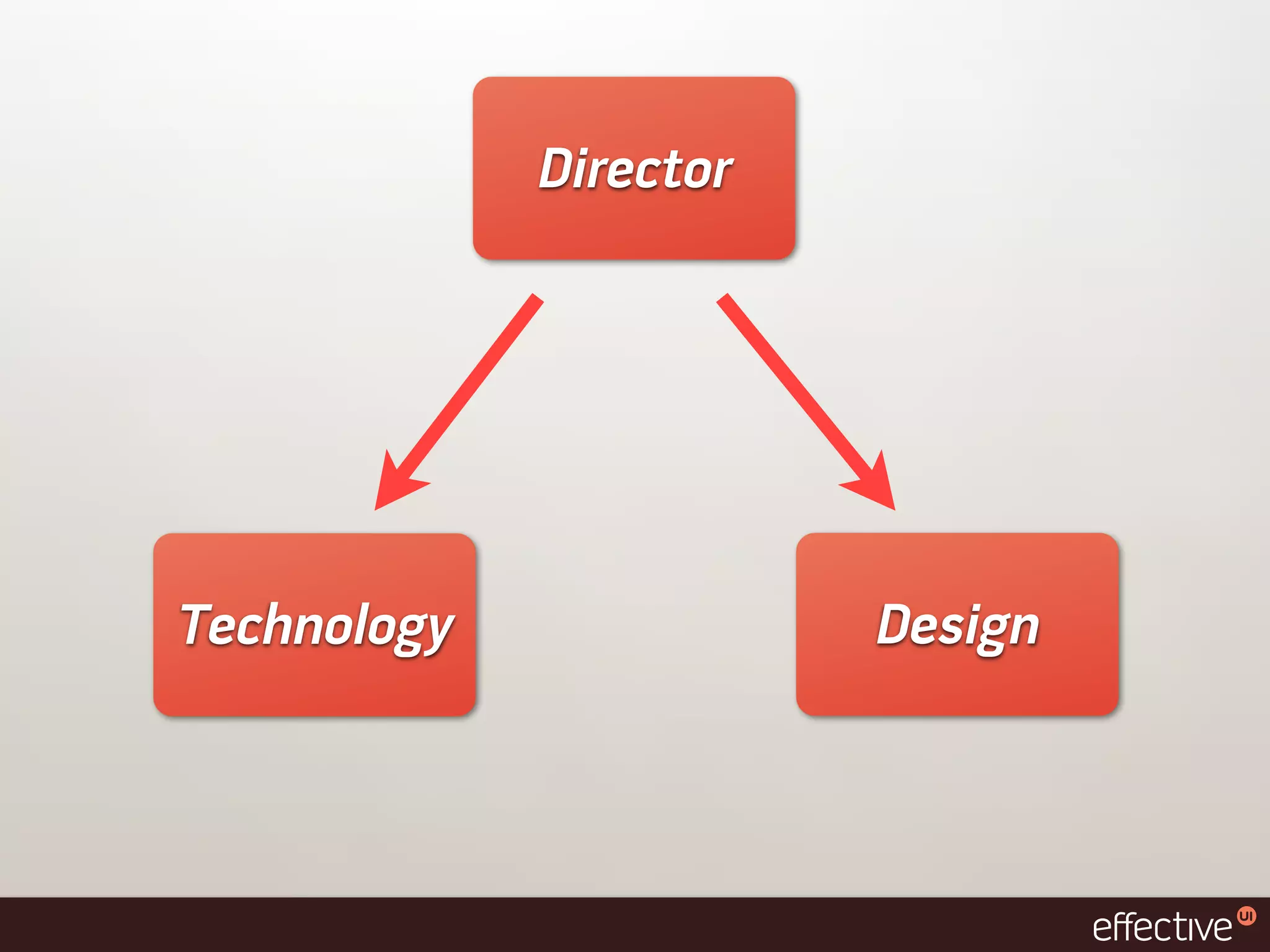
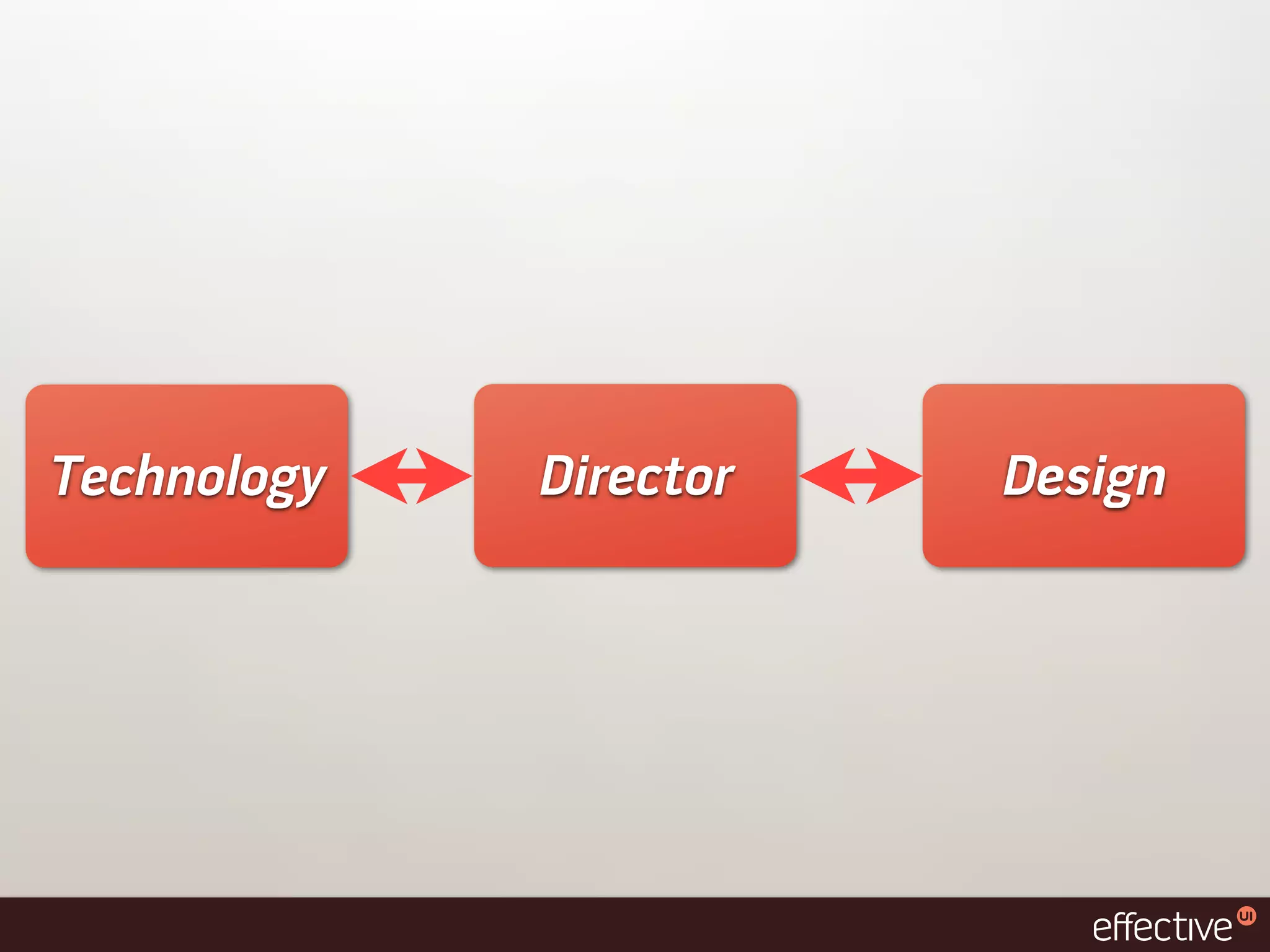
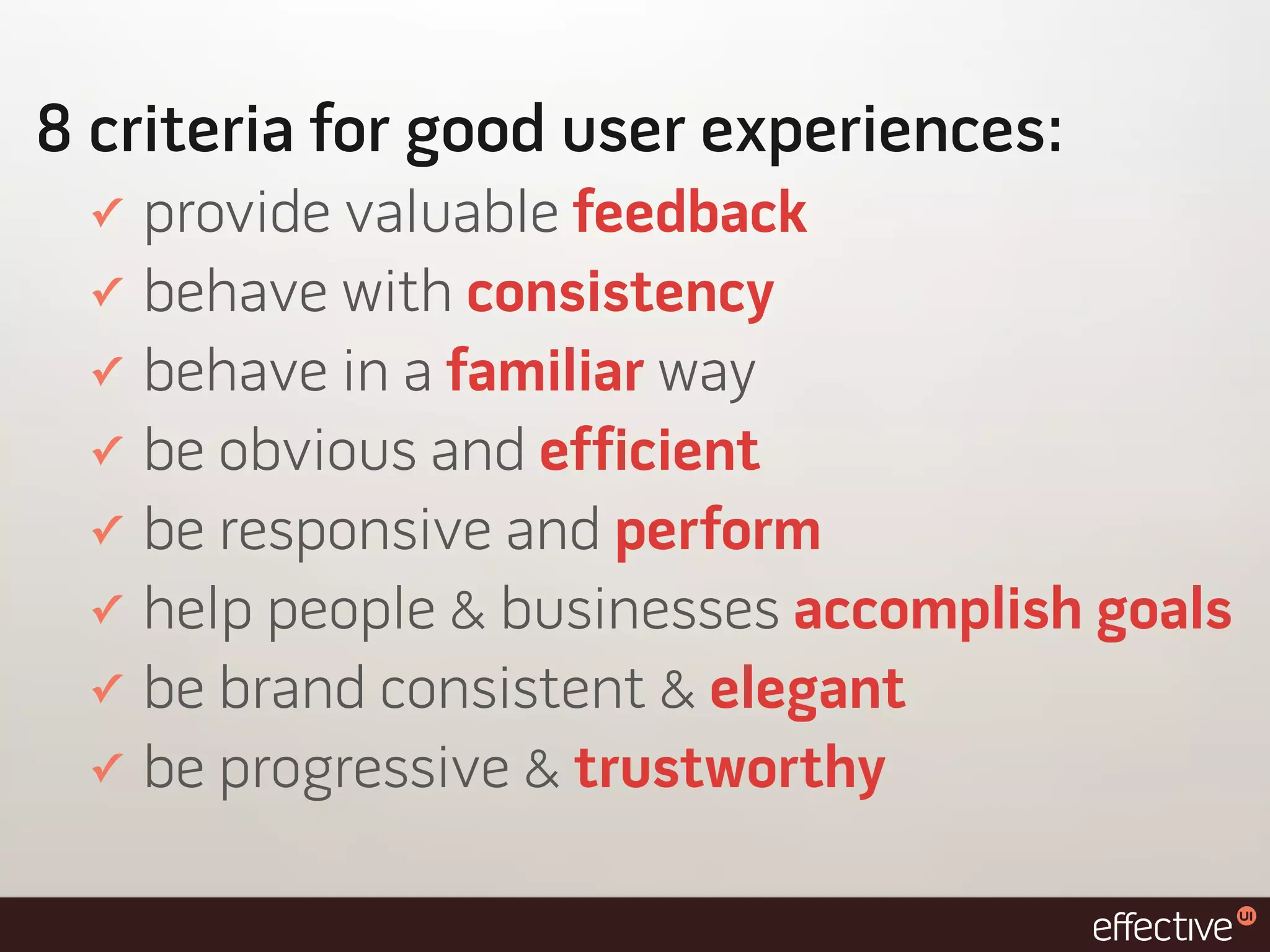
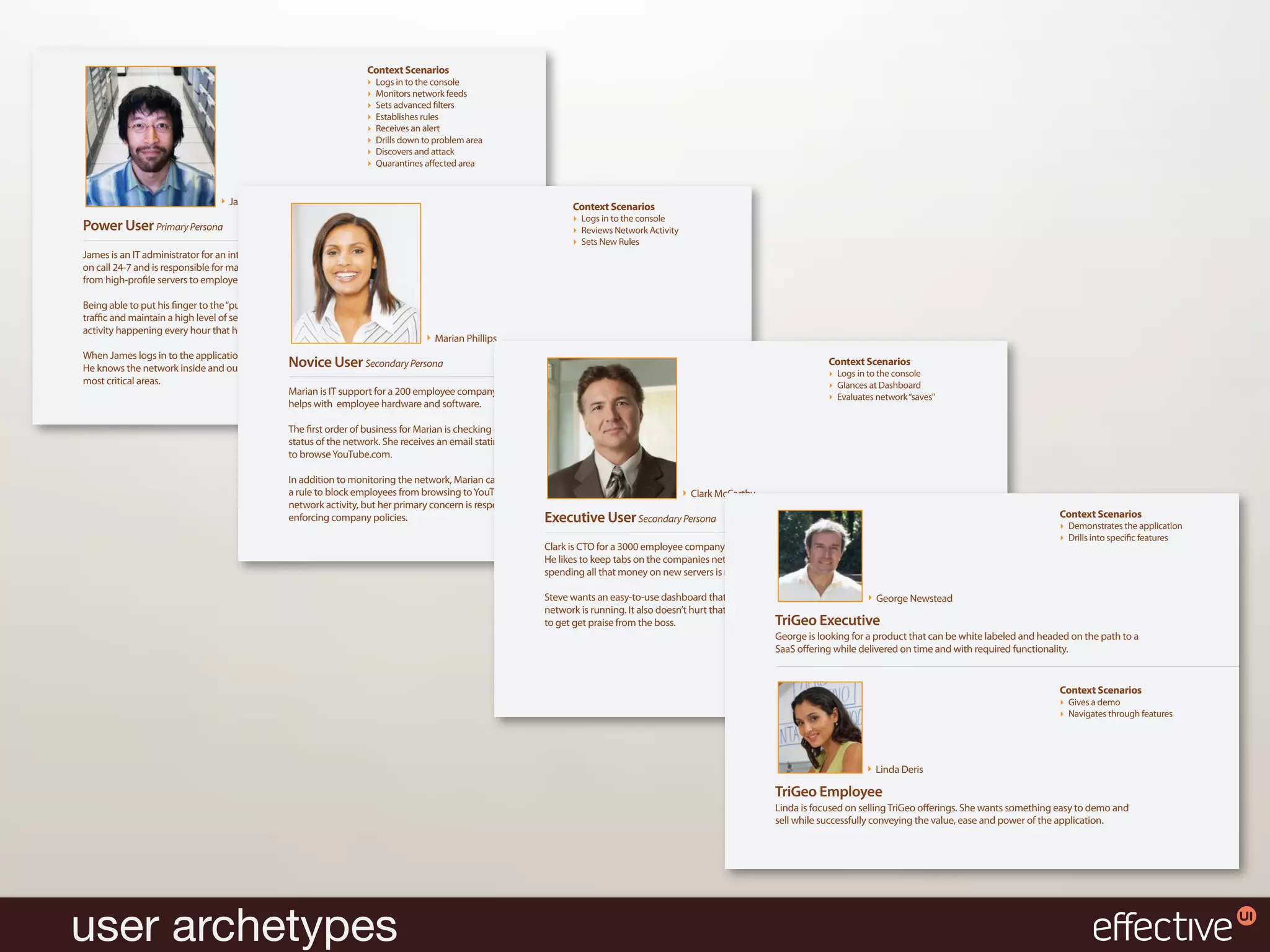
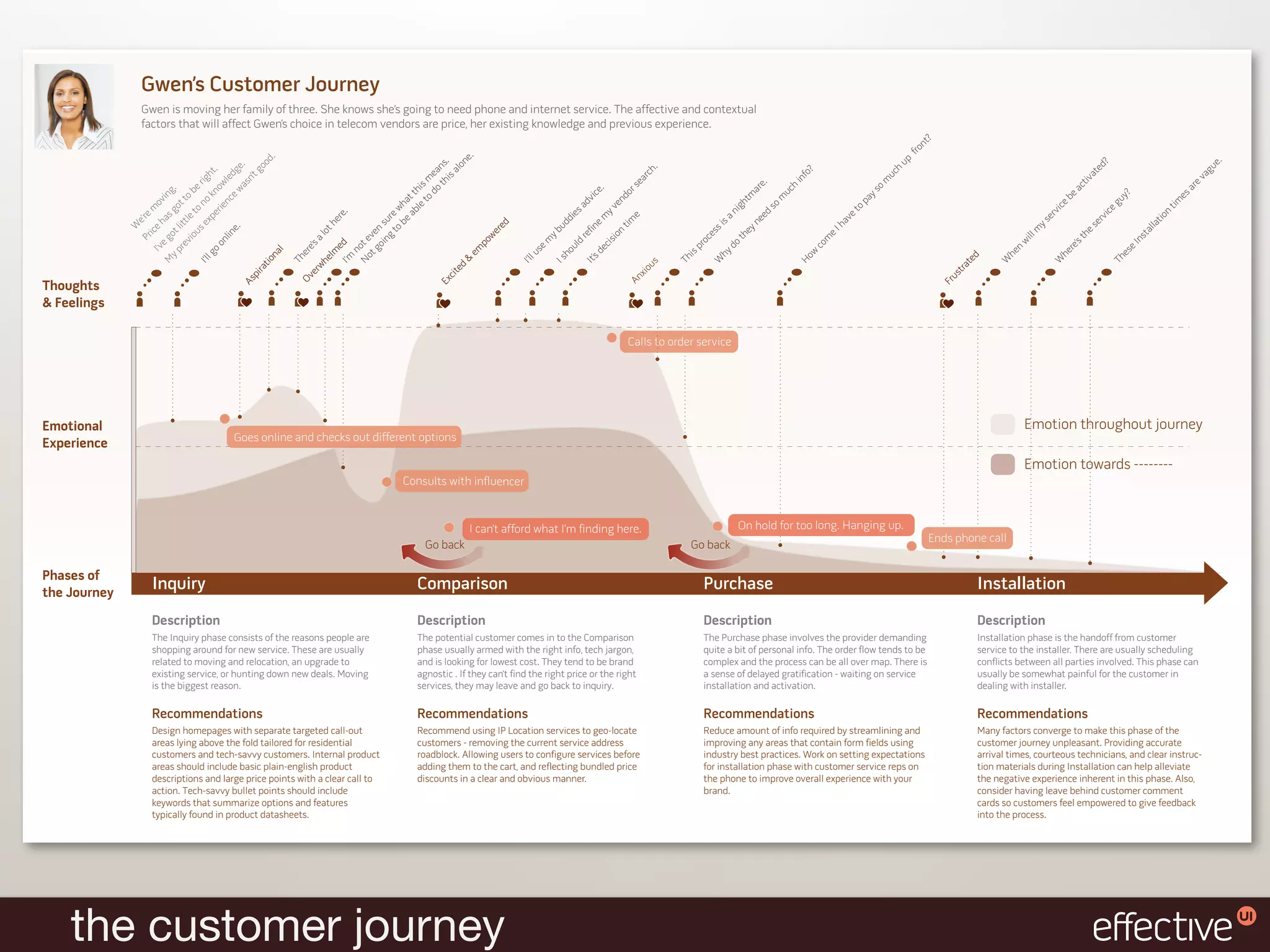
This document discusses user experiences with software and how they can impact government and citizens. It provides nine laws of effective user experiences based on common successes, including focusing on the user first, empathizing with users, delivering software where users want it, gathering feedback through conversation, interpreting rather than directly taking user requirements, valuing good design, not trying to build for everyone, collaborating across teams, and allowing for flexibility rather than rigid plans. The document advocates applying these laws to optimize user adoption and achieve the benefits of software ROI for both government operations and citizens.