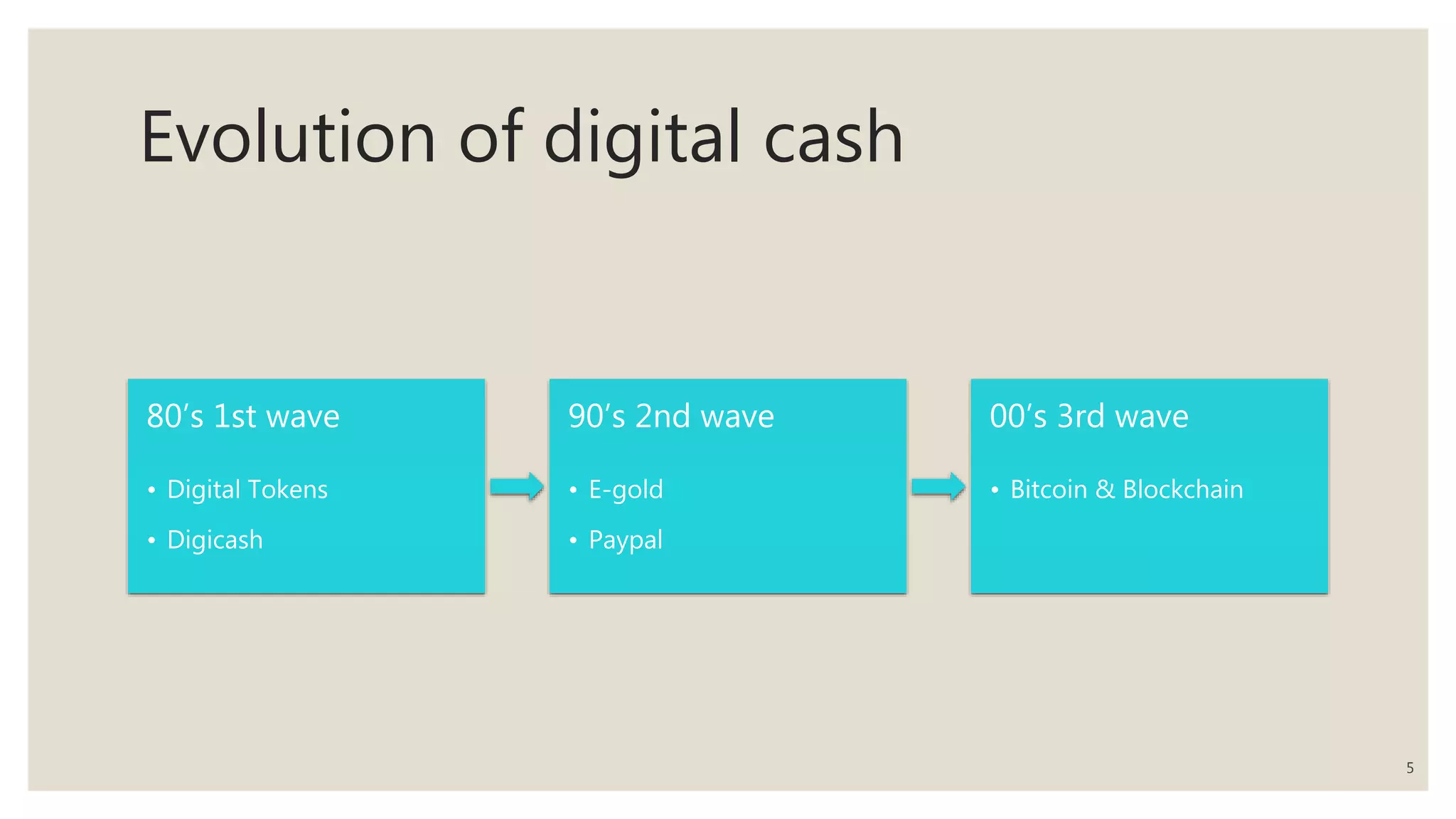
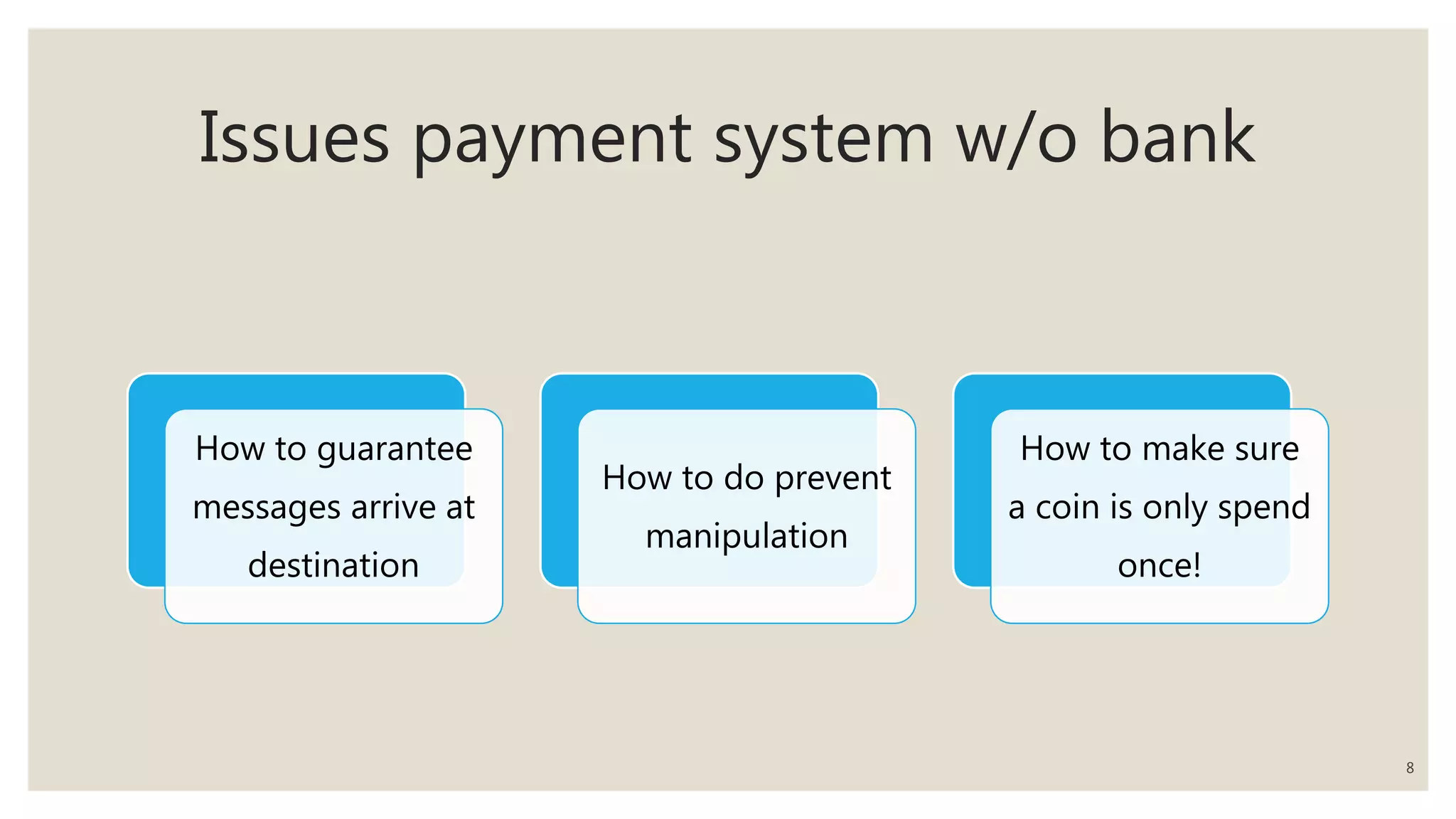
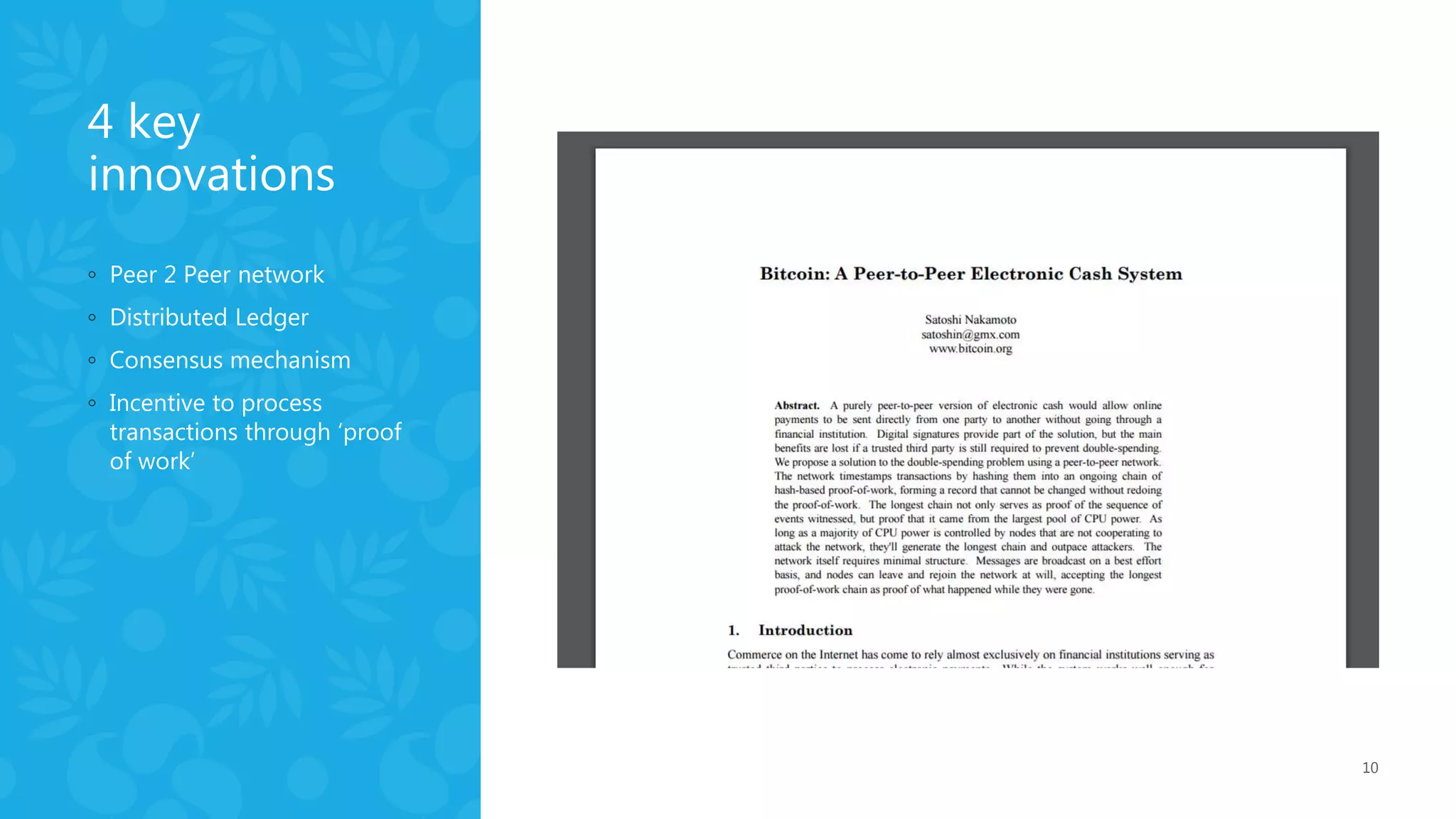
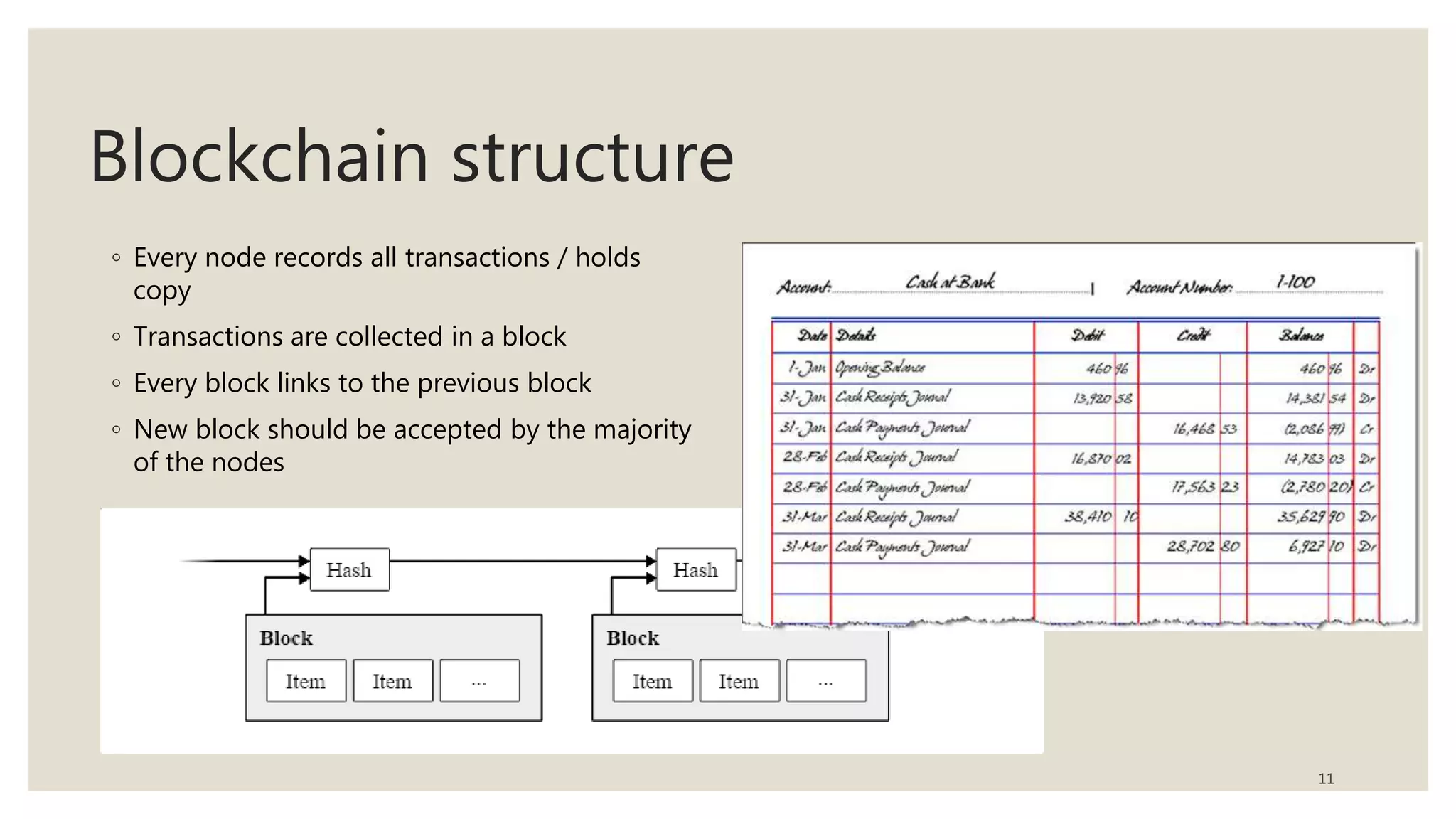
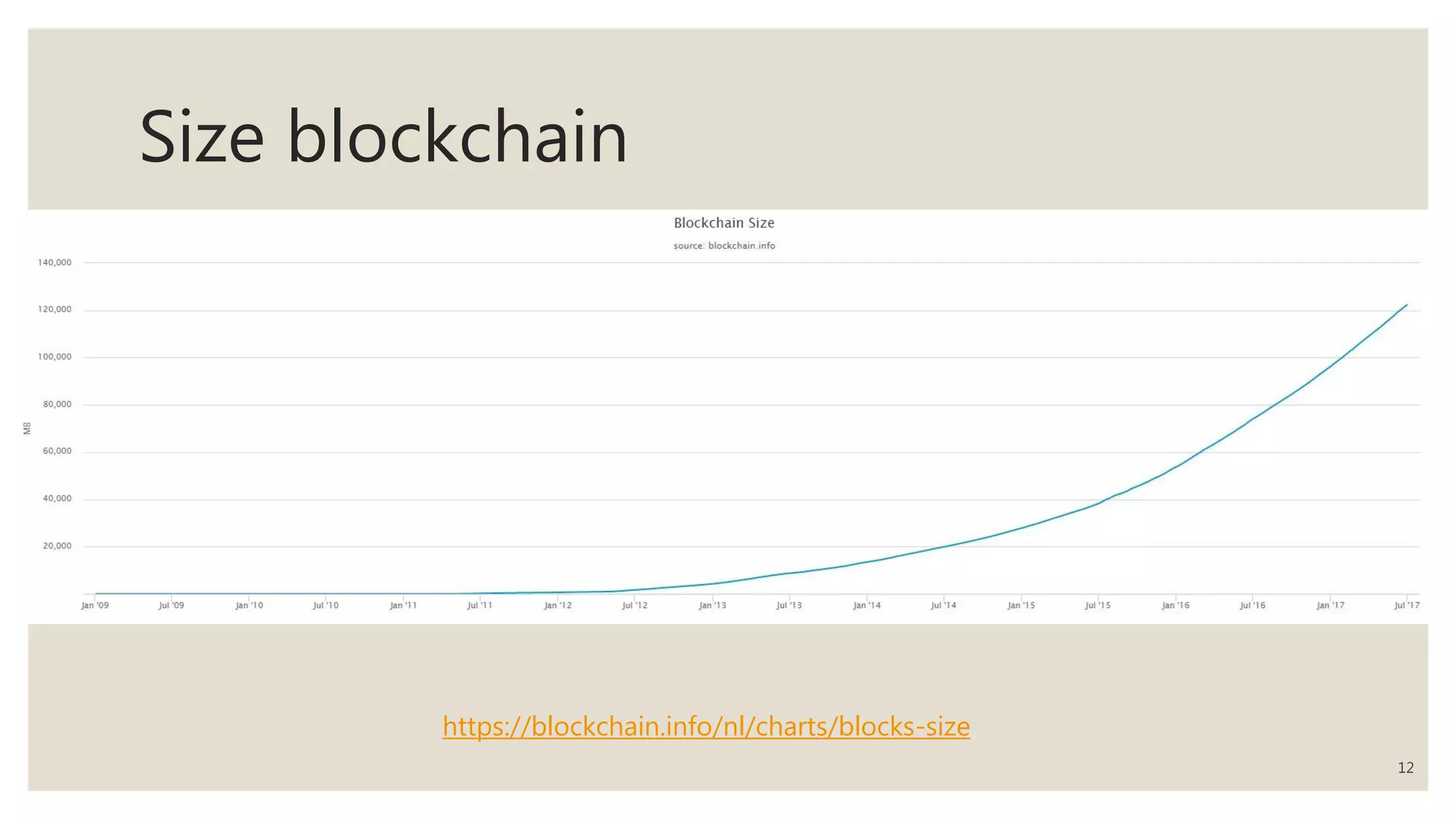
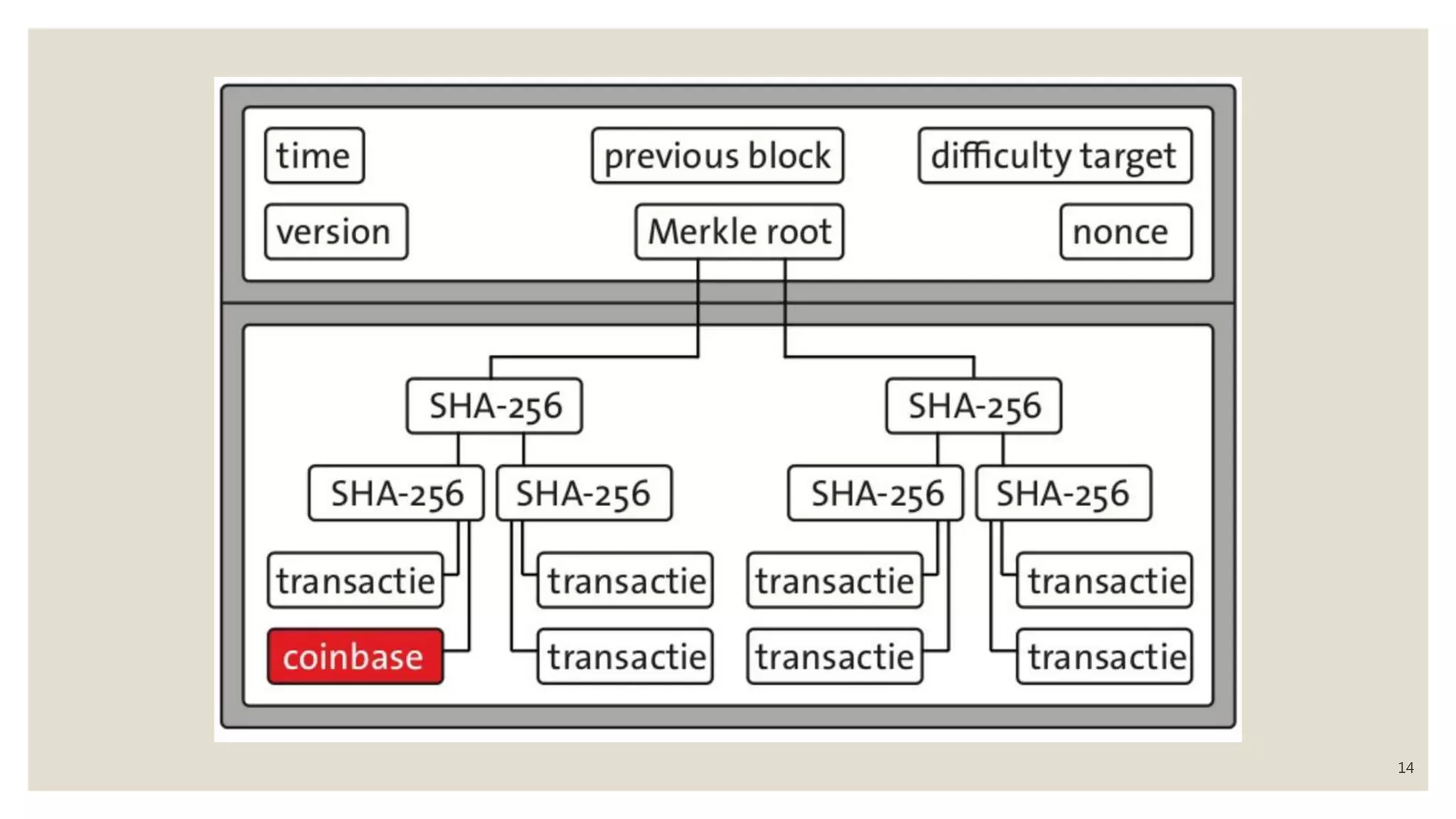
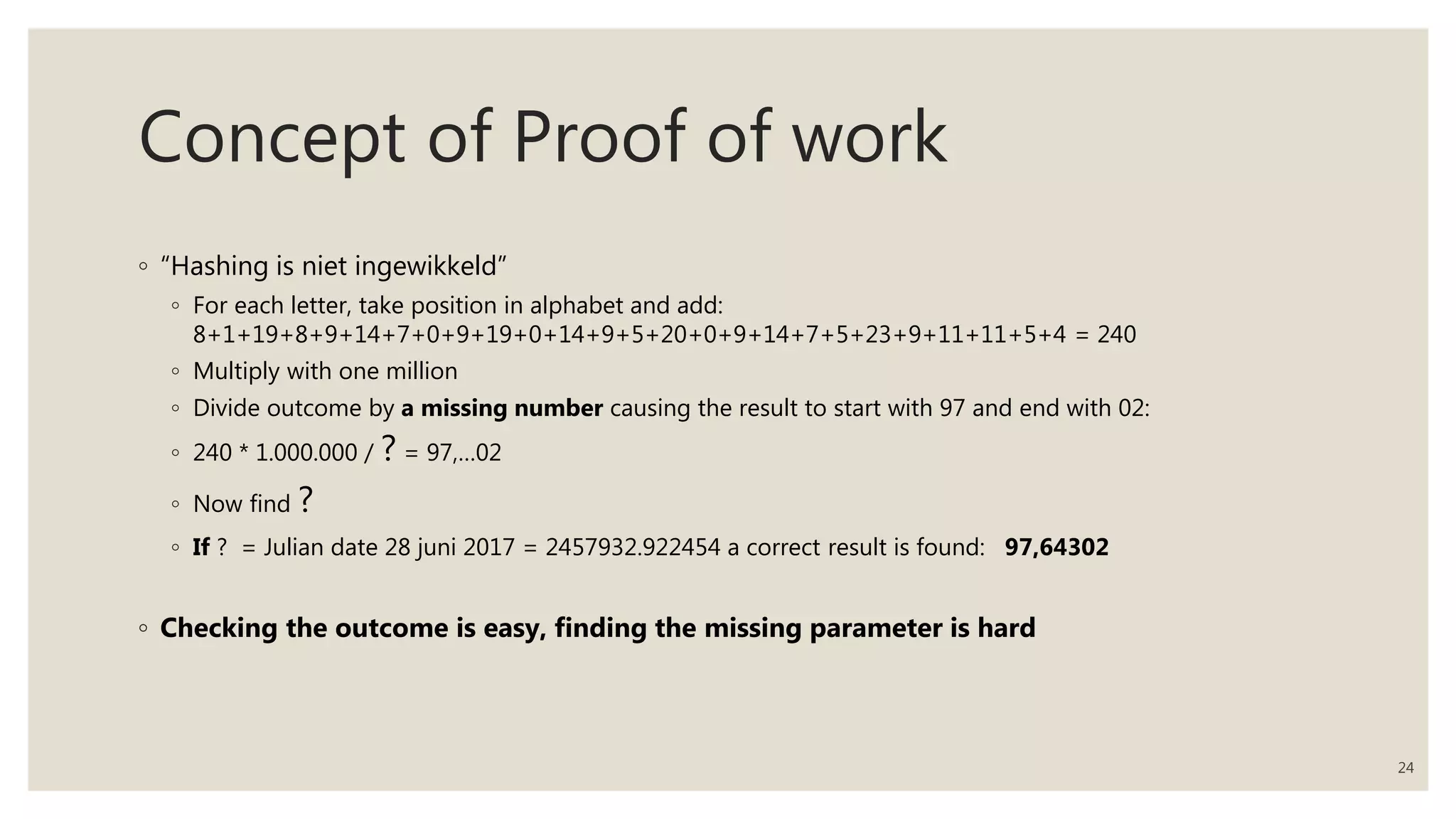
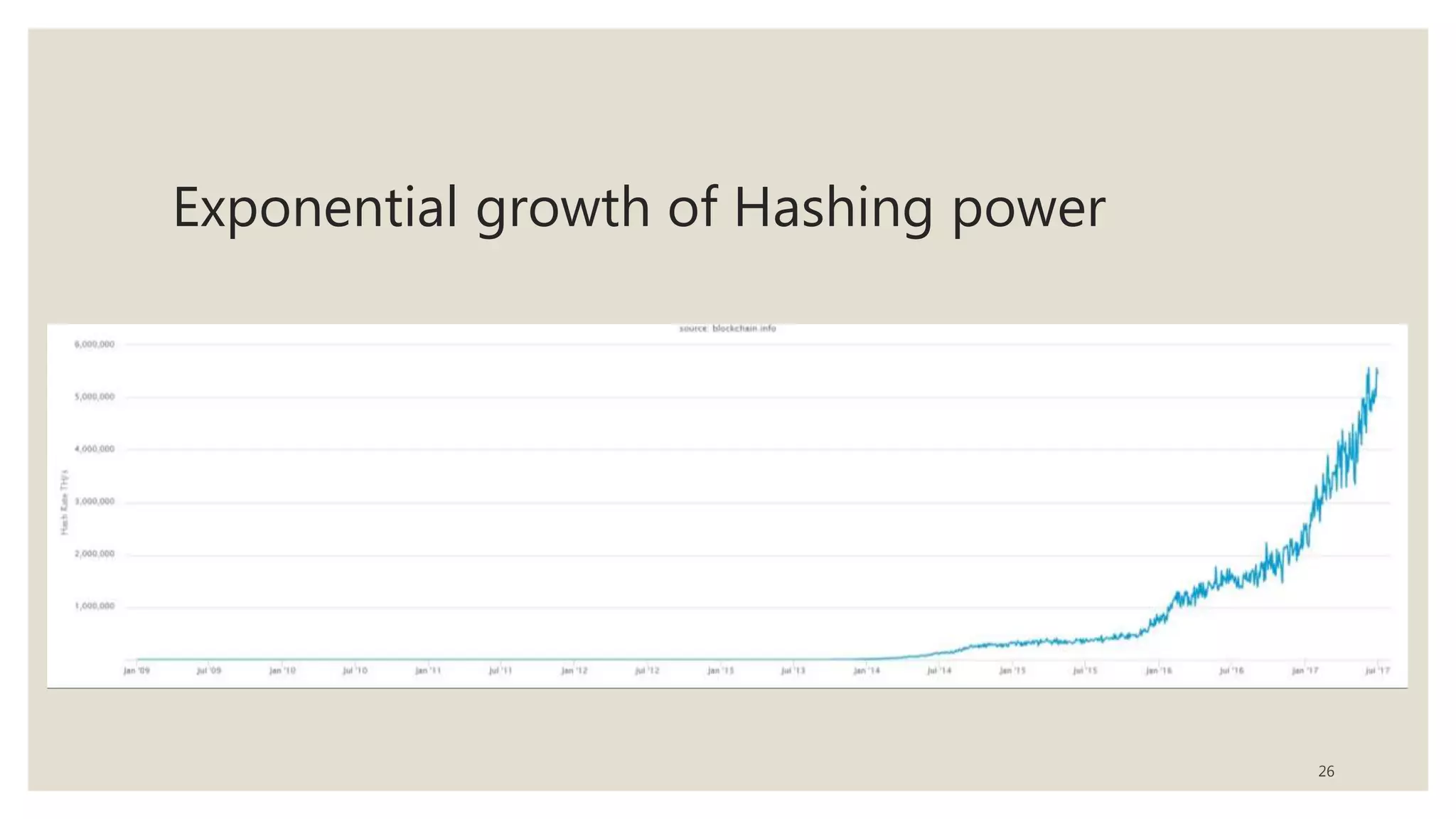
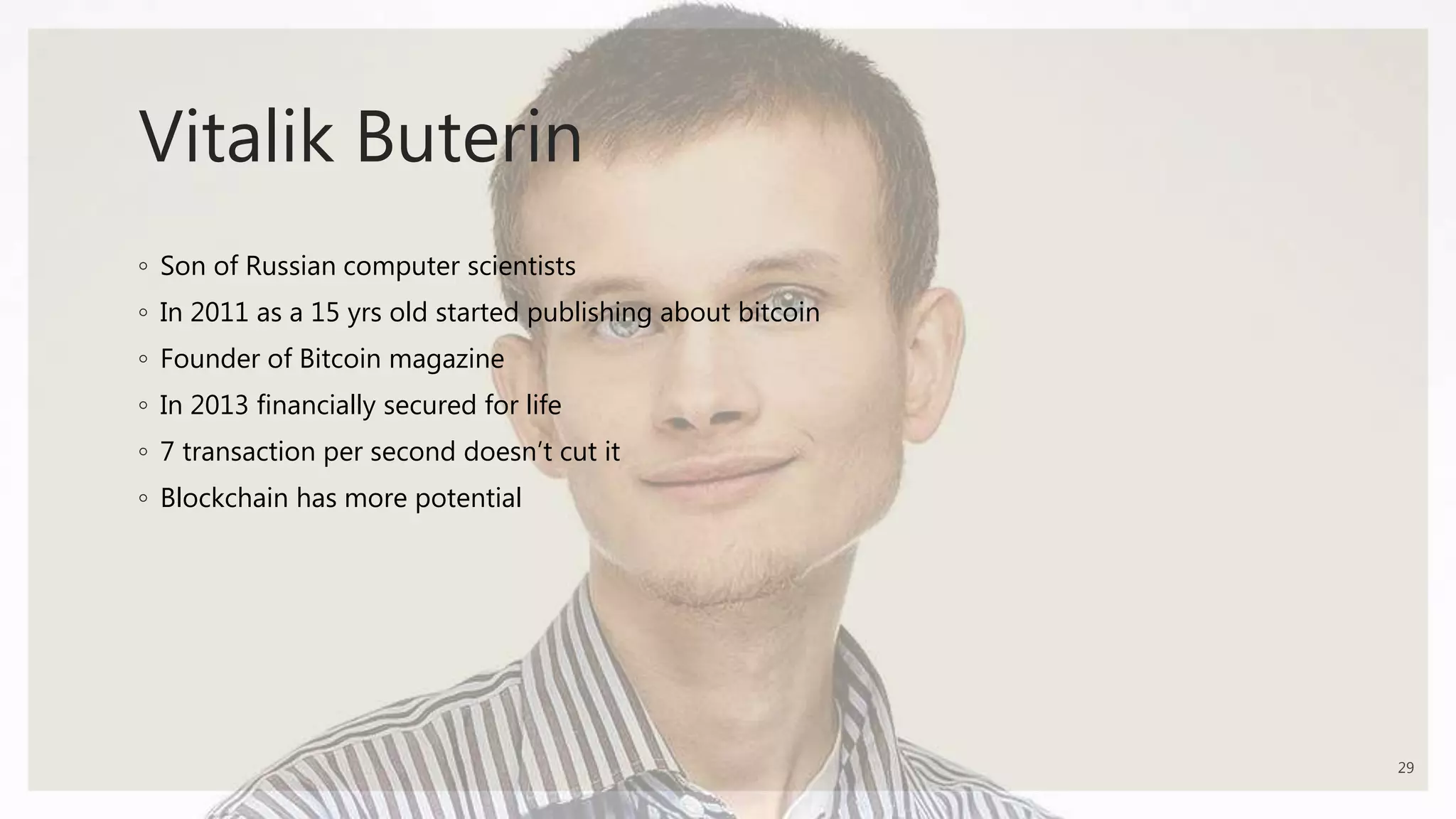
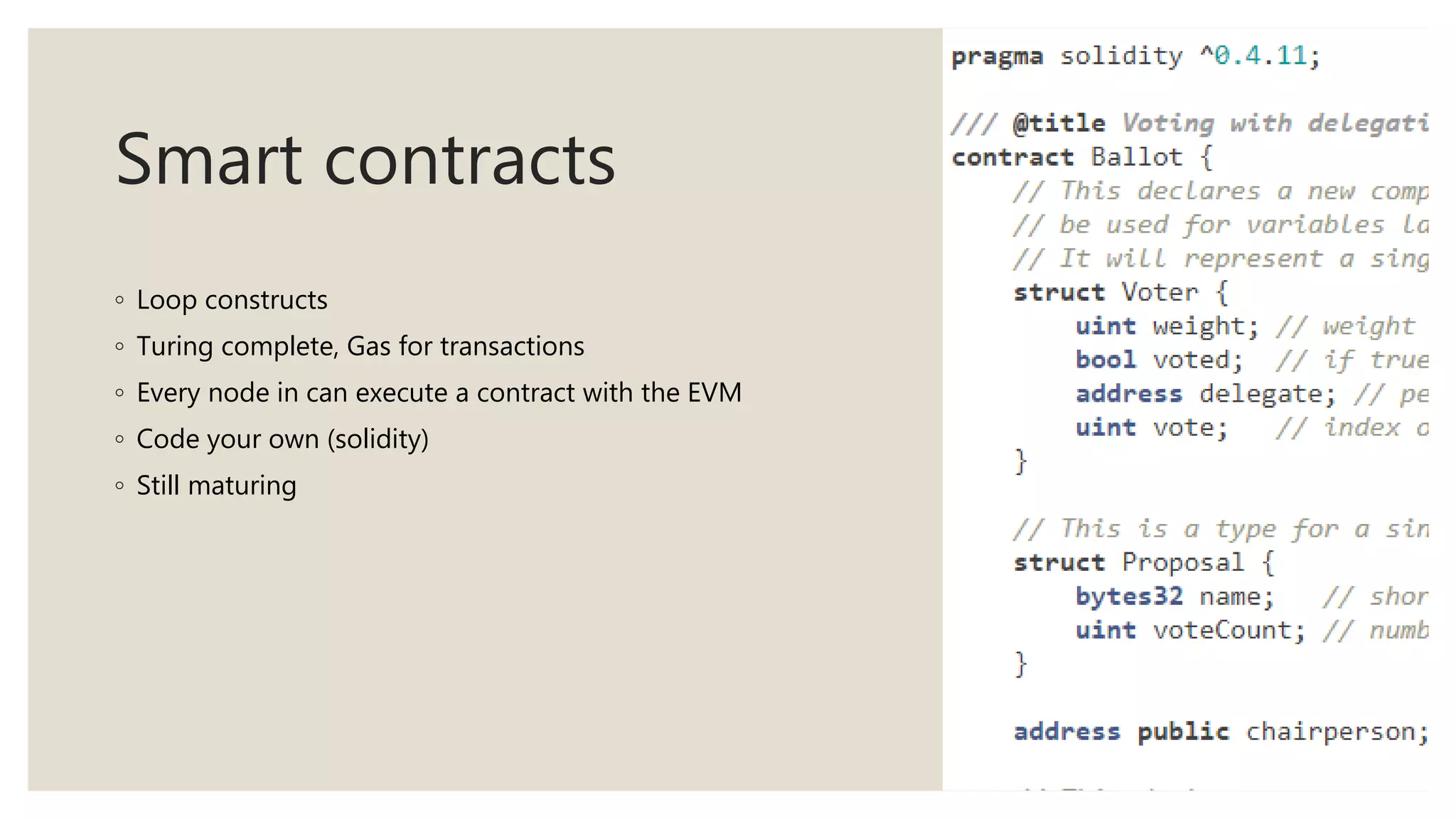
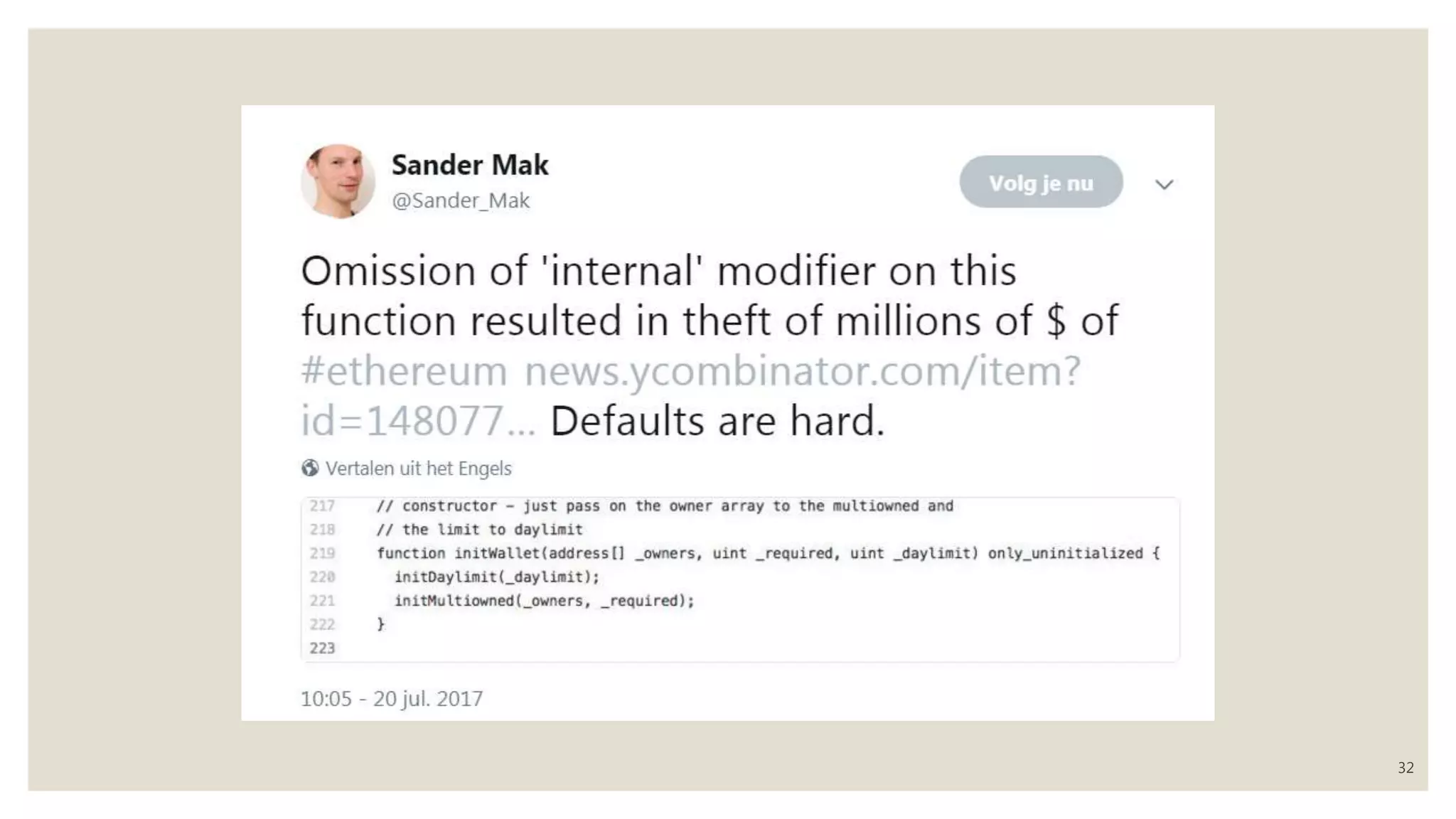
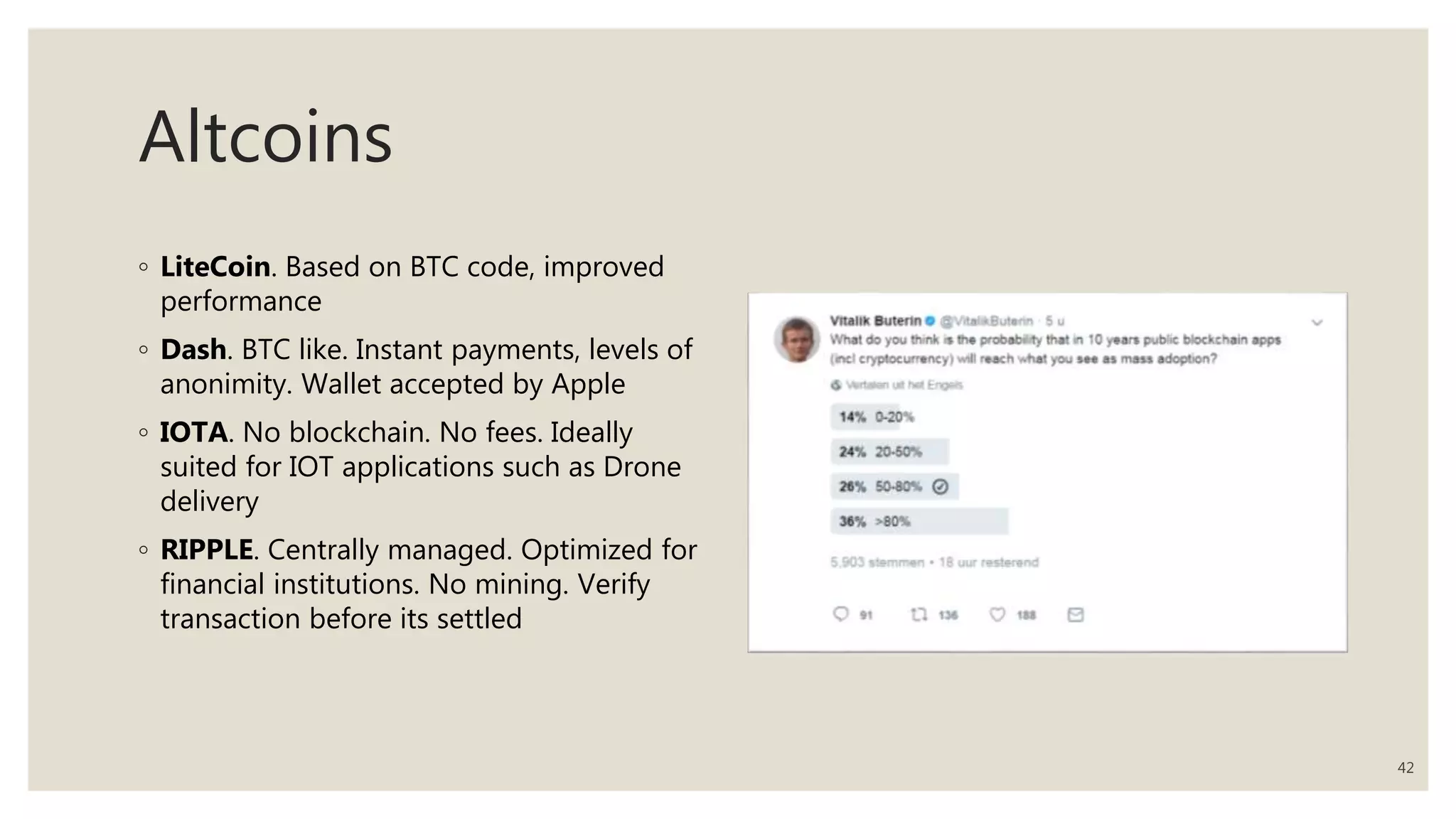
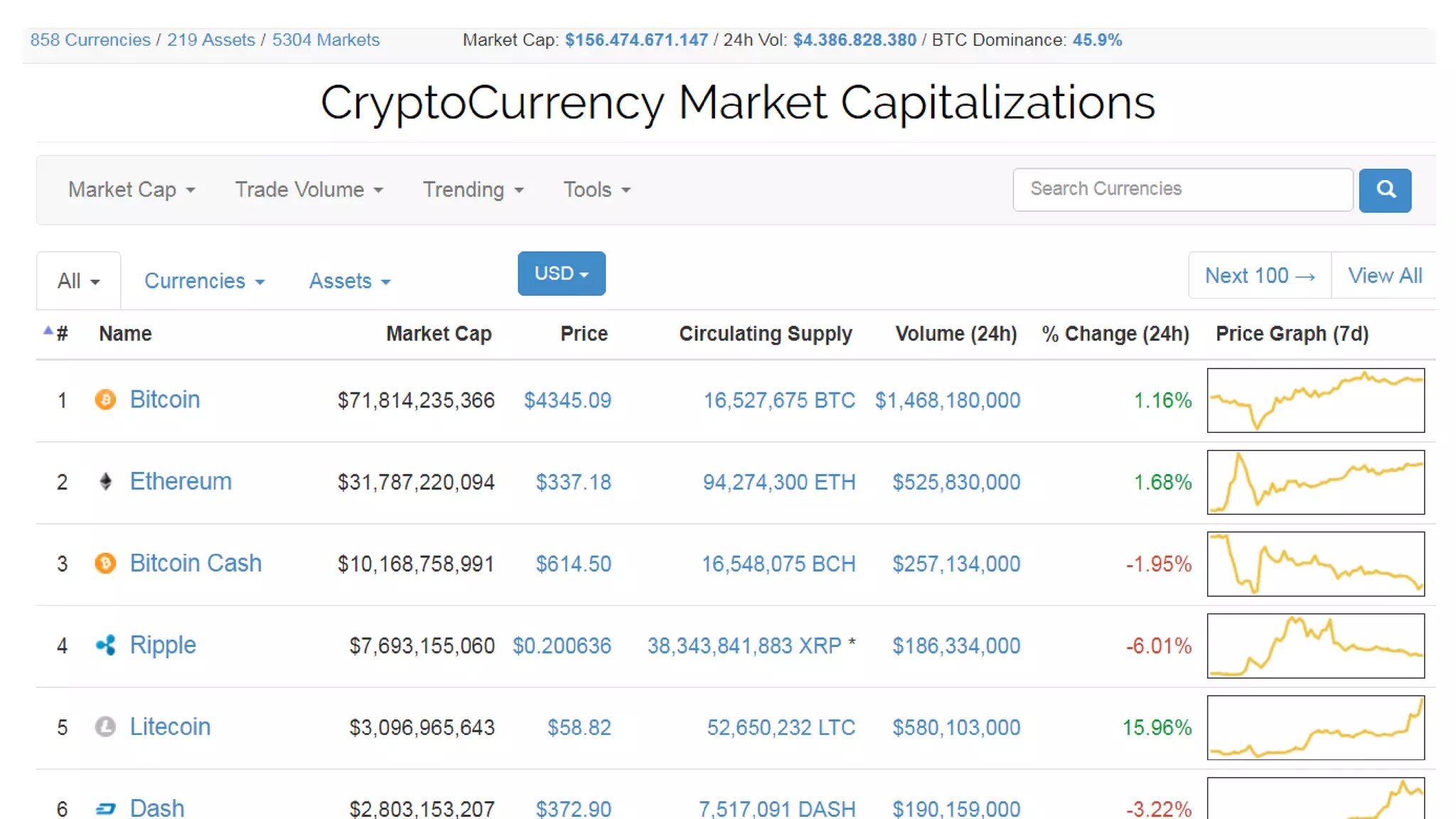
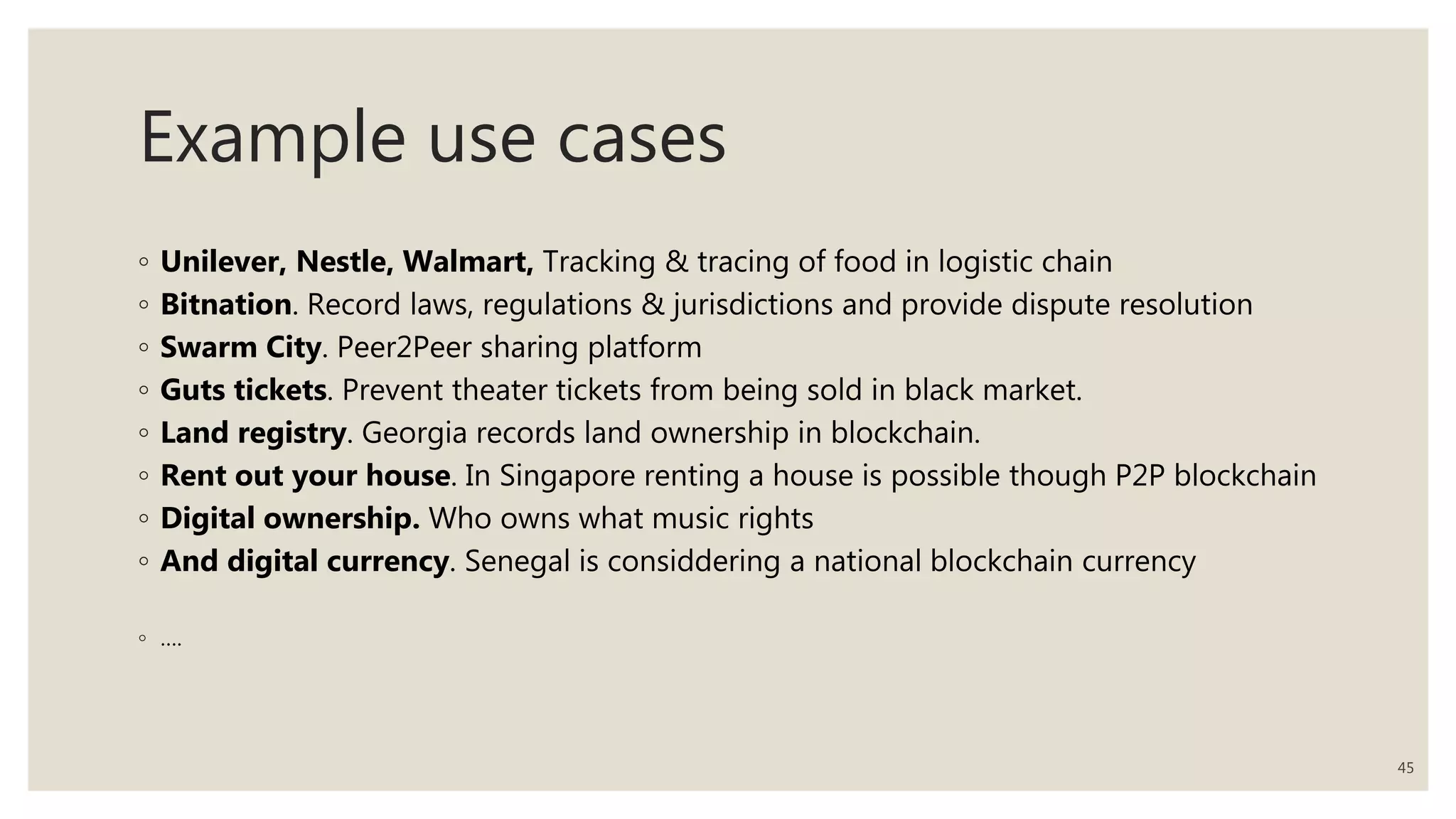
The document discusses the evolution of blockchain and cryptocurrency, highlighting key innovations such as peer-to-peer networks, distributed ledgers, and consensus mechanisms. It compares Bitcoin and Ethereum, emphasizing the advantages of smart contracts and the use of blockchain in various applications, including supply chain management and decentralized autonomous organizations. Additionally, it addresses when to use and not to use blockchain technology based on specific needs and conditions.