The document discusses the security issues and challenges related to Bitcoin key management, focusing on how private keys serve as digital identities and their vulnerabilities. It outlines various key management approaches, their limitations, and the potential risks of attacks, such as side-channel and invalid-curve attacks. The study emphasizes the need for rethinking key management strategies to enhance security for end users in the context of decentralized systems like blockchain.
![Problem Statement
3
Private Key Security[6]
With BC, a private key is regarded as user identity and security credential
Generated and maintained by the user instead of 3rd party agencies
Hartwig et al.[1] discover a vulnerability in ECDSA* scheme
Side-channel attack and invalid-curve attack might be possible
Does not generate enough randomness during the signature process
Attacker can be able to recover the user’s private key
* Elliptic Curve Digital Signature Algorithm](https://image.slidesharecdn.com/20171212blockchainsecurityissuesandchallengesdec2017-181018034119/75/Blockchain-Security-Issues-and-Challenges-3-2048.jpg)
![Problem Statement
5
Private Key Security[6]
Once a user’s private key is lost, it will not be able to recovered
User’s BCT account will face the risks of being tampered by others
If a private key is stolen by criminals
BCT doesn’t dependent on any centralized 3rd party trusted infrastructure
Difficult to track the criminal’s behaviors and recover modified BC information
Decentralized aspect of BC makes the key management task very challenging](https://image.slidesharecdn.com/20171212blockchainsecurityissuesandchallengesdec2017-181018034119/75/Blockchain-Security-Issues-and-Challenges-5-2048.jpg)
![Bitcoin Keys and Addresses
6
With bitcoin, keys come in pairs:
Private (secret) key = secret PIN or signature on a check
Provides a control over the account and sign TXs
Public key = bank account number
Unique and derived from private key
Bitcoin address = K recipient, represented by its digital fingerprint
Similar to a beneficiary name on a check (i.e. “Pay to the order of”)
Bitcoin address is generated form and corresponds to a public key
Conversion of a public key into a bitcoin
address [2]
A = RIPEMD160(SHA256(K ))K = k * G
G : is the generator point](https://image.slidesharecdn.com/20171212blockchainsecurityissuesandchallengesdec2017-181018034119/75/Blockchain-Security-Issues-and-Challenges-6-2048.jpg)
![Bitcoin Wallet (BW)
7
Type-2 deterministic (seeded) wallet [2]:
a tree of keys generated from a single seed
Type-0 nondeterministic (random) wallet [2]:
a collection of randomly generated keys
Contains and manages a collection of key pairs
Mostly, k and K are stored together as a Key pair for convenience
Randomly generated number
combined with other data
(i.e. index or chain code)](https://image.slidesharecdn.com/20171212blockchainsecurityissuesandchallengesdec2017-181018034119/75/Blockchain-Security-Issues-and-Challenges-7-2048.jpg)
![Master Keys Creation & PK extension
8http://chimera.labs.oreilly.com/books/1234000001802/ch04.html#hd_wallets
Creating master keys and chain code from a
root seed [2]
Extending a parent private key to create a
child private key [2]
HMAC : Hash Message Authentication Code
Chain code is used to introduce entropy in the
function that creates child keys from parent keys.](https://image.slidesharecdn.com/20171212blockchainsecurityissuesandchallengesdec2017-181018034119/75/Blockchain-Security-Issues-and-Challenges-8-2048.jpg)
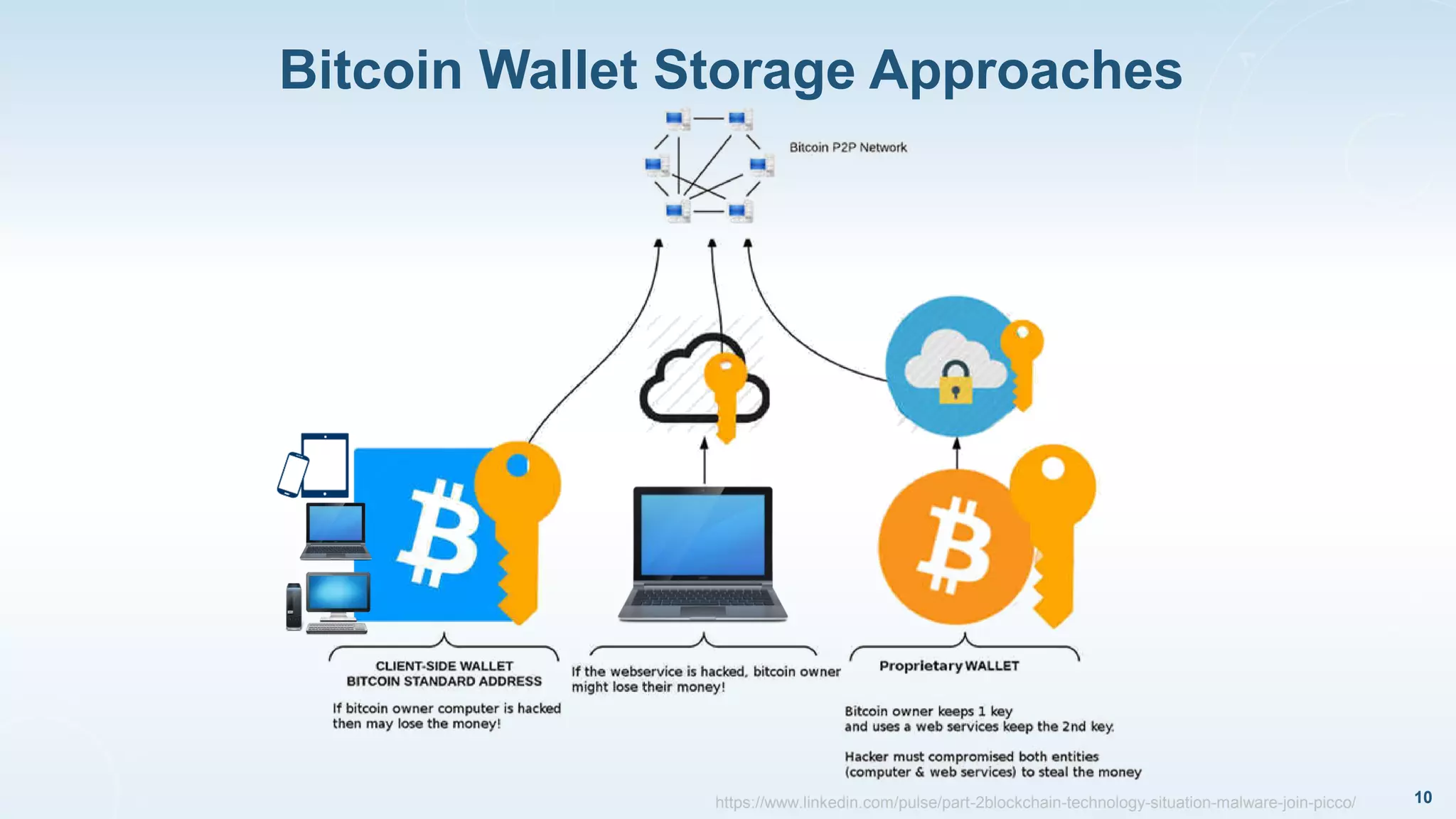
![BTC Key Management Approaches
11
Works in [3-5] surveyed on the BTC Key management approaches
Found that BTC has several fundamental issues and challenges
It offers opportunities to rethink the key management for end users
First investigation [3] on the usability issues of BTC’s key management
Survey and categorize most known BTC key management proposals
Propose a set of evaluation criteria for BTC key management](https://image.slidesharecdn.com/20171212blockchainsecurityissuesandchallengesdec2017-181018034119/75/Blockchain-Security-Issues-and-Challenges-11-2048.jpg)
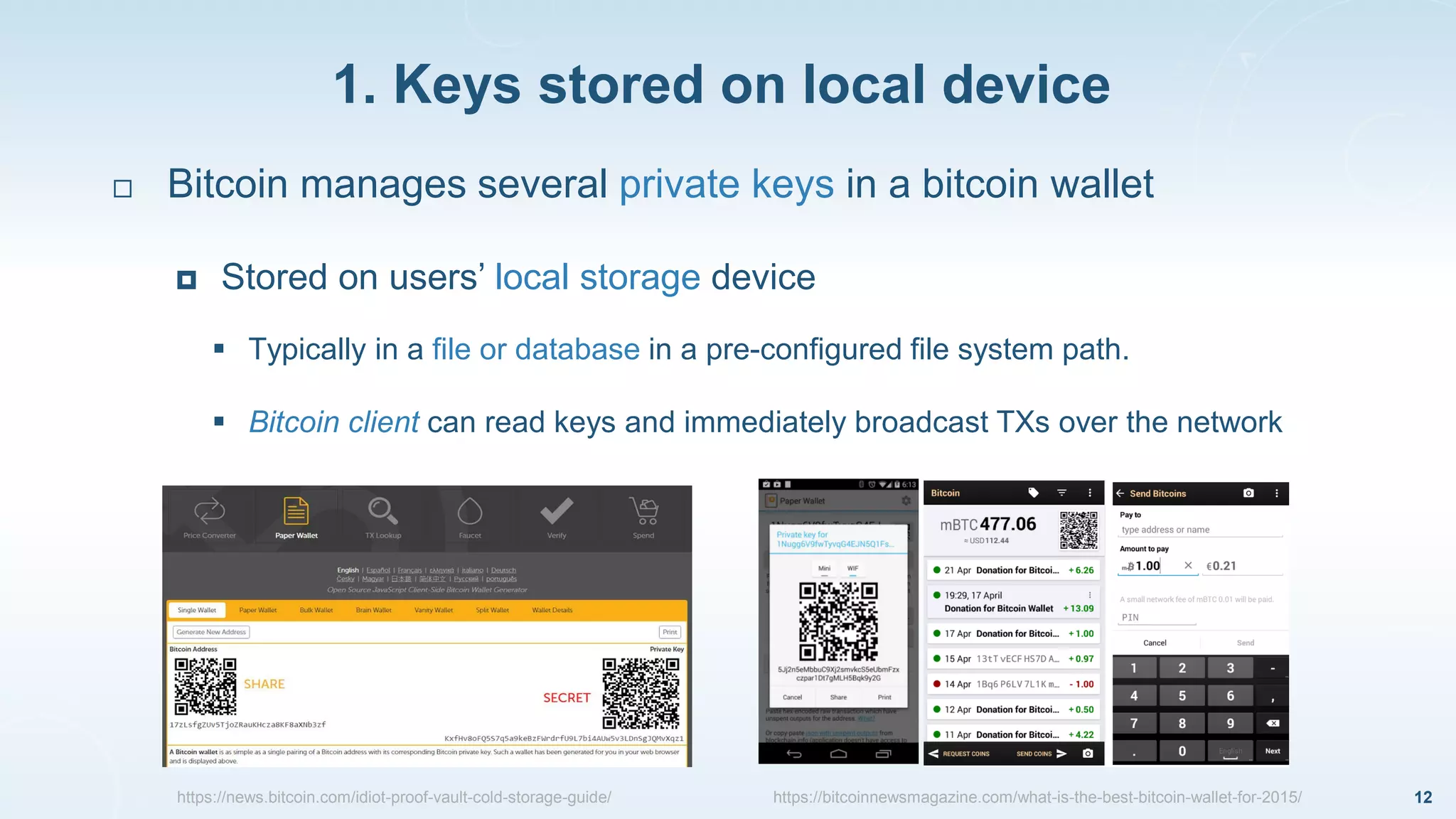
![1. Keys stored on local device
13
Several threats to store keys in local devices [3]:
Files storing private keys can be read by any app.
with access to the user’s application folder
Malware may exploit this key management approach
Access to local files results in the adversary gaining access to the victim’s funds
Users must be aware to not mistakenly share their app. folders
P2P file sharing networks, off-site backups or a shared network drive
https://www.secureworks.com/research/cryptocurrency-stealing-malware-landscapehttps://www.secureworks.com/research/cryptocurrency-stealing-malware-landscape](https://image.slidesharecdn.com/20171212blockchainsecurityissuesandchallengesdec2017-181018034119/75/Blockchain-Security-Issues-and-Challenges-13-2048.jpg)
![1. Keys stored on local device
14
Several threats to store keys in a locally[3] :
Physical storage device theft
Especially in case of mobile devices (i.e. laptops or smart phones)
Equipment failure
Due to natural disasters and electrical failures
Undetected storage failure, etc.
Private key files format long-term readability
A trust fund/long-term saving requires PKs to be stored for a long period of time
Users must ensure that keys’ file format can continue to be read](https://image.slidesharecdn.com/20171212blockchainsecurityissuesandchallengesdec2017-181018034119/75/Blockchain-Security-Issues-and-Challenges-14-2048.jpg)
![5. Password-derived Keys
19
HD wallets [2] deterministically derive a set of private keys
form a master secret key (a user randomly chosen passphrase)
pw holder can view the balance and funds of any sub-account derived from the pw
If one sub-key k is compromised, only the funds of that sub-key
(or sub-keys derived from it) may be stolen
Weak passwords can be found easily through brute-force search
Fingerprint of associated public keys will be in the public ledger
if the account holds any amount of bitcoin
Hierarchical Deterministic
(HD) wallet
https://brainwallet.io/
https://brainwalletx.github.io/](https://image.slidesharecdn.com/20171212blockchainsecurityissuesandchallengesdec2017-181018034119/75/Blockchain-Security-Issues-and-Challenges-19-2048.jpg)
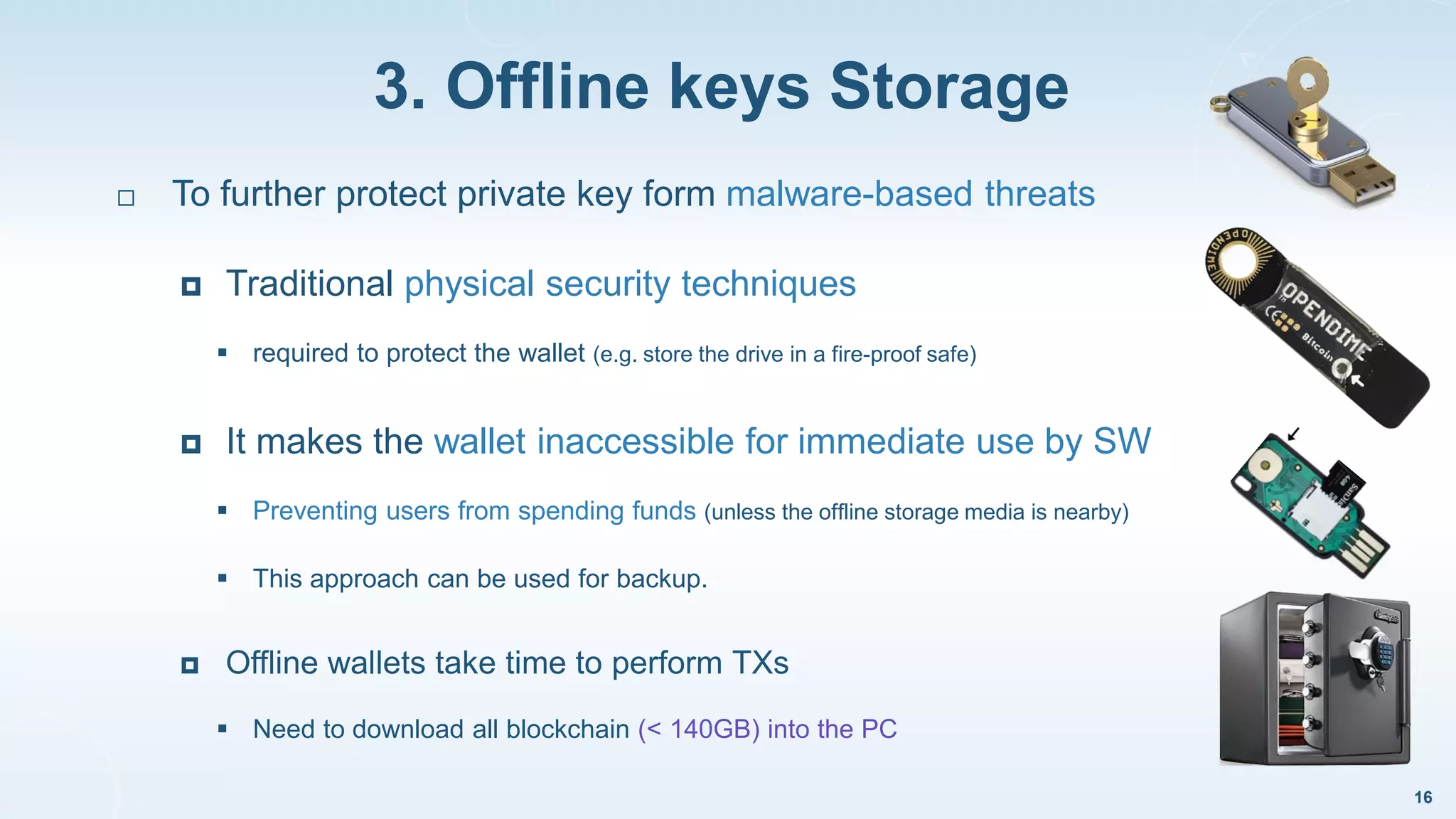
![Super-Wallet [9] : Multi Tiered Storage Scheme
21
https://bitcoinsecurityproject.org/SecureStorage/MultiTieredColdStorageScheme/
As a counter measure to theft, hosted
wallet providers often keep :
Small float of holdings online in hot storage
Majority of holdings offline in cold storage
Causes delays in TXs for users if the
hot storage amount is exhausted.
Implementation complexity](https://image.slidesharecdn.com/20171212blockchainsecurityissuesandchallengesdec2017-181018034119/75/Blockchain-Security-Issues-and-Challenges-21-2048.jpg)
![Comparison of Key Management Approaches for Bitcoin
Vs Traditional Online Banking Service [3]
22
Client partially awards the benefit
Client is awarded the benefit](https://image.slidesharecdn.com/20171212blockchainsecurityissuesandchallengesdec2017-181018034119/75/Blockchain-Security-Issues-and-Challenges-22-2048.jpg)
![[1] Mayer, Hartwig. "ECDSA Security in Bitcoin and Ethereum: a Research Survey." (2016).
[2] Antonopoulos, Andreas M. "Mastering Bitcoin: unlocking digital cryptocurrencies. " O'Reilly Media, Inc., 2014.
[3] Eskandari, Shayan, et al. "A first look at the usability of bitcoin key management." Workshop on Usable Security
(USEC), 2015.
[4] Goldfeder, Steven, et al. "Securing Bitcoin wallets via a new DSA/ECDSA threshold signature scheme." (2015).
[5] Bonneau, Joseph, et al. "Sok: Research perspectives and challenges for bitcoin and cryptocurrencies." Security
and Privacy (SP), 2015 IEEE Symposium on. IEEE, 2015
[6] Li, Xiaoqi, et al. "A survey on the security of blockchain systems." Future Generation Computer Systems (2017).
[7] RSA Laboratories, “PBKDF2 (Password-Based Key Derivation Function 2),” http://tools.ietf.org/html/rfc2898.
[9] Barber, Simon, et al. "Bitter to better—how to make bitcoin a better currency." International Conference on
Financial Cryptography and Data Security. Springer, Berlin, Heidelberg, 2012.
[10] Top 10 Security Concerns for Bitcoin Wallets and Exchanges - https://bitcoinsecurityproject.org/topten/
REFERENCES
24](https://image.slidesharecdn.com/20171212blockchainsecurityissuesandchallengesdec2017-181018034119/75/Blockchain-Security-Issues-and-Challenges-24-2048.jpg)
