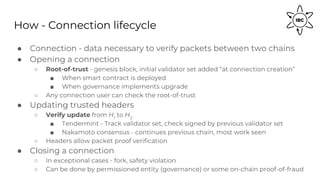
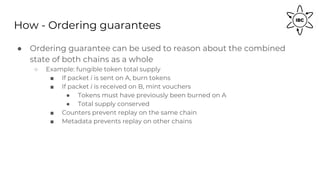
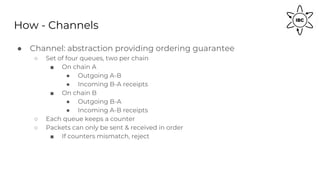
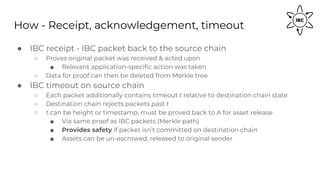
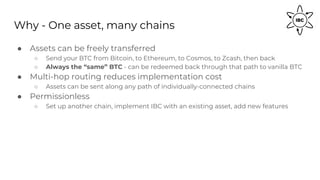
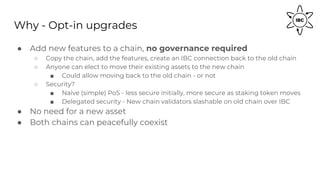
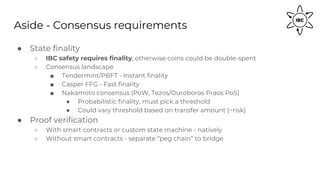
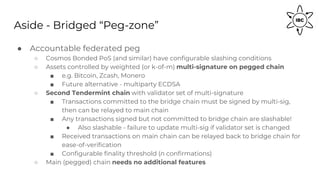
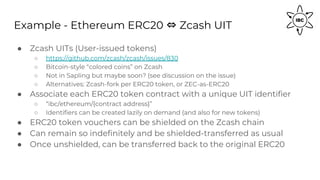
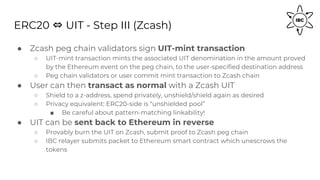
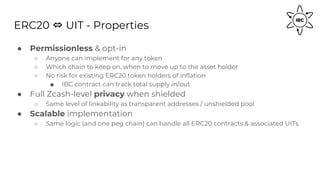
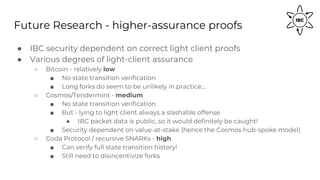
The document provides an in-depth explanation of the Inter-Blockchain Communication (IBC) protocol, detailing its design goals, implementation methods, and various use cases for enabling seamless data and asset transfers across different blockchain networks. It covers the security models, connection lifecycle, and the mechanisms for ensuring message ordering and packet verification between heterogeneous chains. Furthermore, it discusses practical examples such as connecting Ethereum and Zcash, allowing for features like token transfers and privacy-preserving transactions.