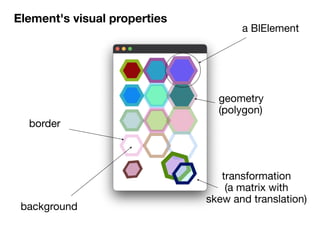
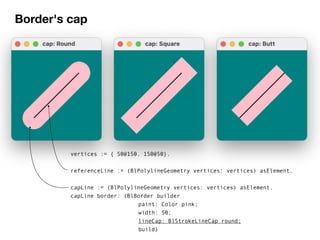
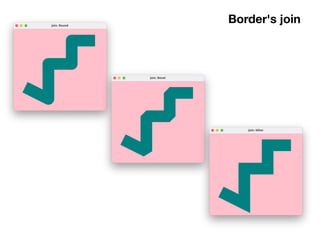
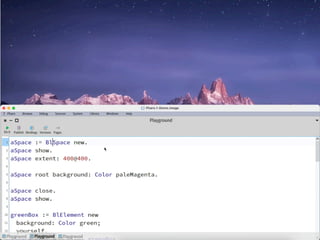
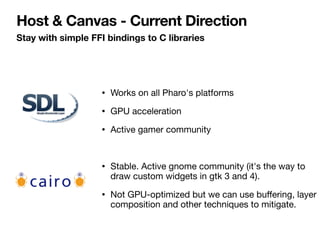
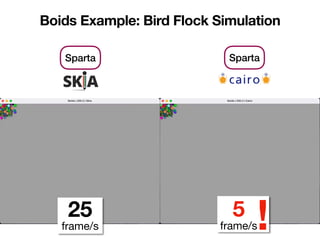
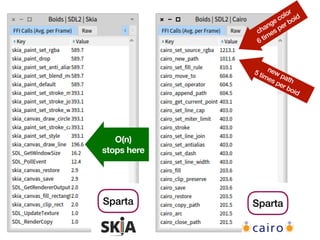
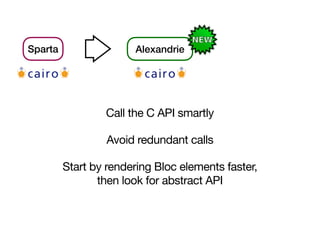
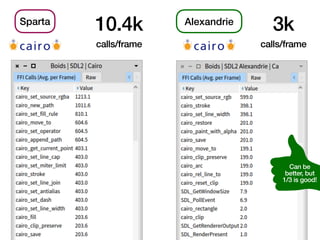
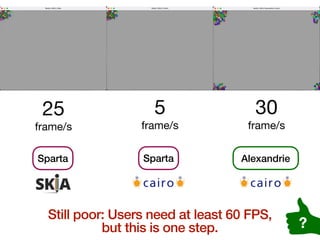
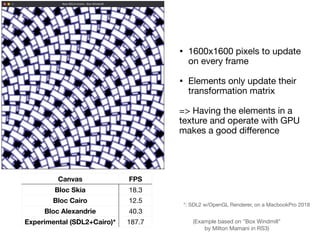
The document outlines the 'Bloc' framework for creating low-level UI infrastructure in Pharo, focusing on geometry and visual properties of elements. It discusses optimization methods, performance metrics, and future objectives, including GPU acceleration and efficient rendering techniques. Additionally, it provides links to resources, community channels, and GitHub repositories related to Bloc and its development ecosystem.