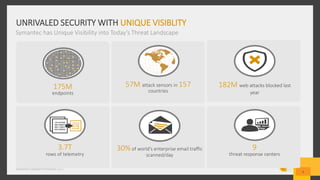
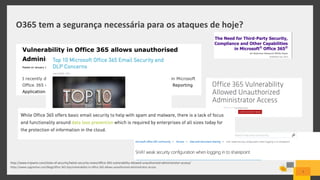
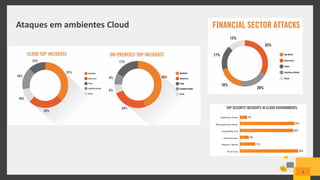
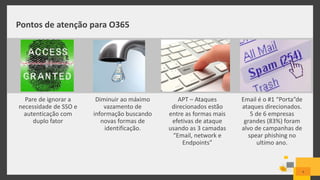
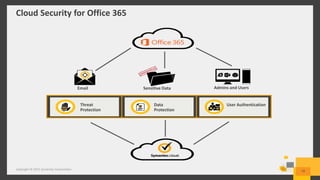
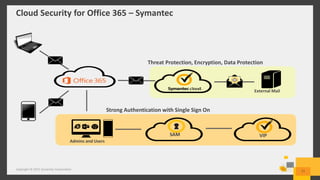
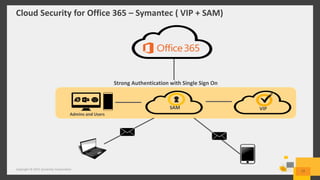
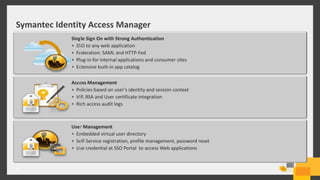
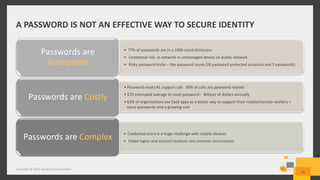
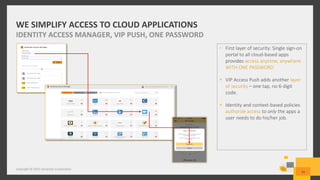
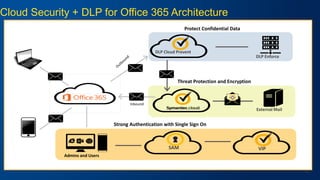
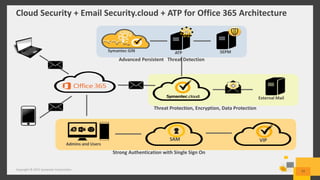
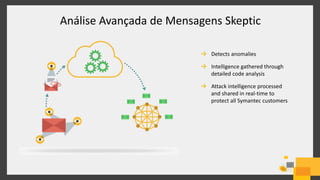
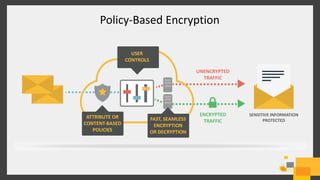
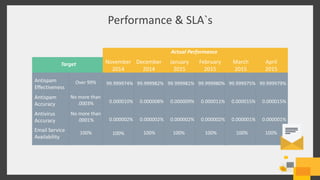
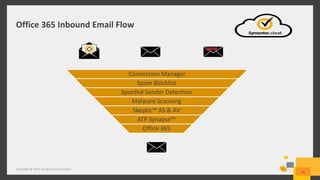
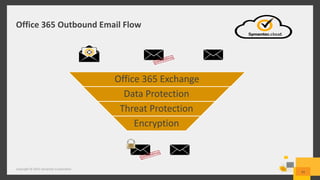
The document discusses cybersecurity measures for Office 365, emphasizing the importance of strong authentication, data loss prevention (DLP), and threat protection against targeted attacks like spear phishing. It highlights Symantec's advanced security solutions, including unified management and integrated analytics for data protection and incident response. The content includes insights from experienced presenters in the field of IT security, detailing the risks posed by cloud environments and the need for robust identity management.