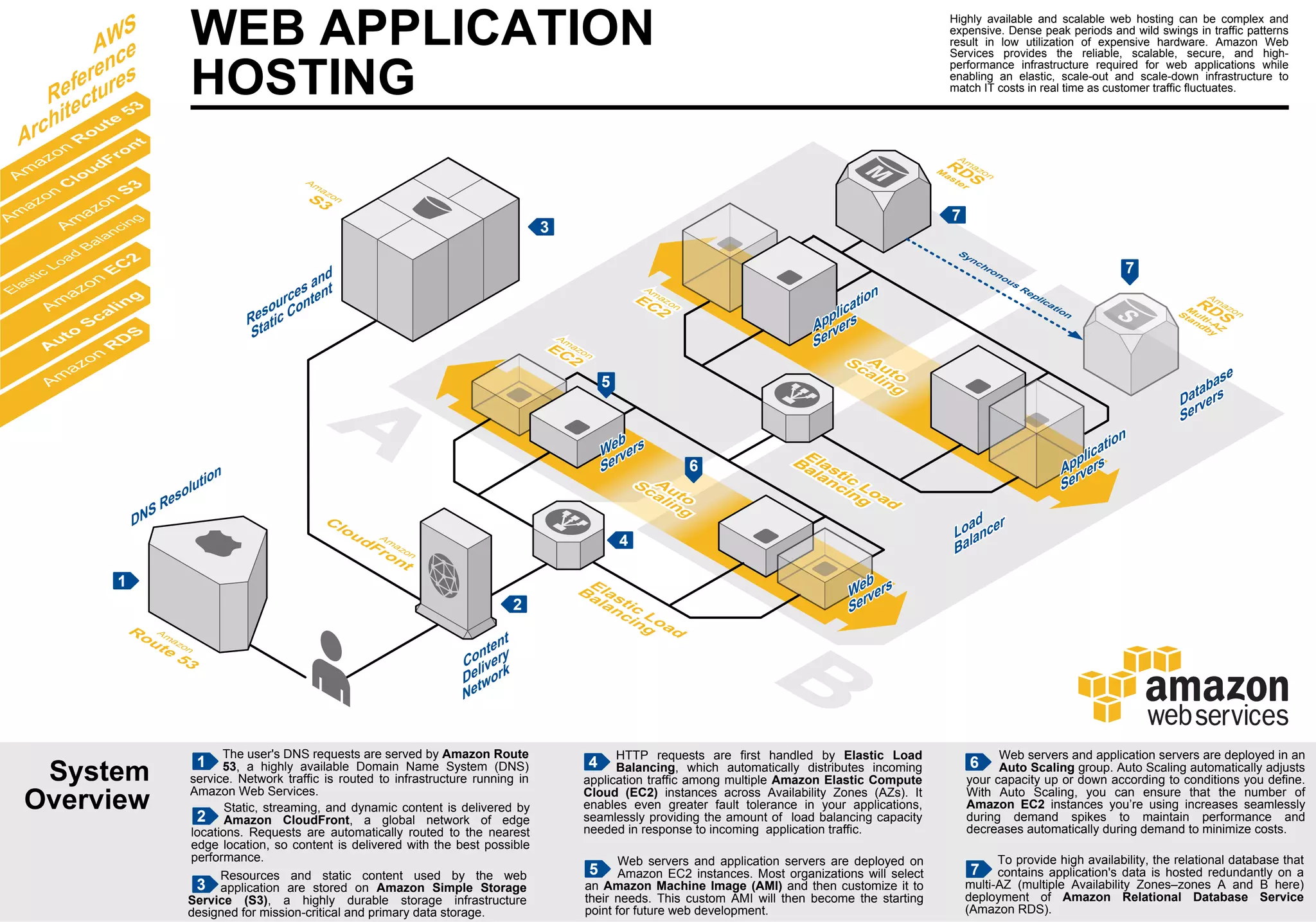
This document provides an overview of Amazon Web Services for highly available and scalable web hosting. It describes how AWS components like Elastic Load Balancing, Auto Scaling, Amazon EC2 instances, Amazon RDS, and Amazon CloudFront can be used together to create a reliable and cost-effective architecture. Traffic is routed through AWS services and automatically distributed across Availability Zones for redundancy and scalability to match fluctuations in customer demand.