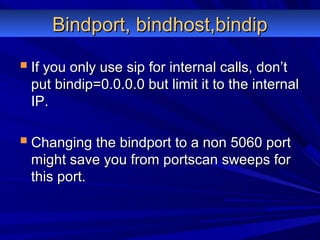
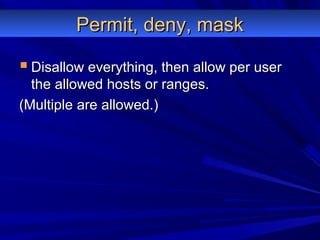
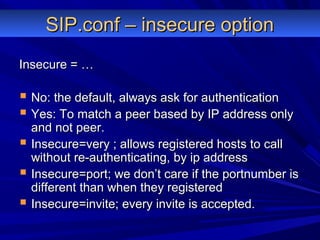
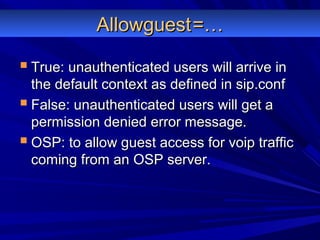
Asterisk security involves properly configuring files like SIP.conf and dial plans to prevent extension hopping and restrict access. It is also important to limit the default context, monitor the system, and use secure protocols to protect privacy. Hardening the system through practices like restricting ports and disallowing everything by default improves security.





![Extension hoppingExtension hopping
User can reach ANY extension in the currentUser can reach ANY extension in the current
context:context:
[internal][internal]
exten => intro,1,Background(question);exten => intro,1,Background(question);
exten => 1,spanish,Goto(Spanish)exten => 1,spanish,Goto(Spanish)
exten => 2,english,Goto(English)exten => 2,english,Goto(English)
exten => _XX.,1,Dial(ZAP/g1/${EXTEN});exten => _XX.,1,Dial(ZAP/g1/${EXTEN});](https://image.slidesharecdn.com/asterisksecuritykingasterisk-130723131448-phpapp01/85/Asterisk-security-with-kingasterisk-30-320.jpg)
![Default contextDefault context
Example:Example:
[default][default]
Include outgoing;Include outgoing;
Include internal;Include internal;
OH OH OH, guest calls will go to the defaultOH OH OH, guest calls will go to the default
context!!!!!context!!!!!](https://image.slidesharecdn.com/asterisksecuritykingasterisk-130723131448-phpapp01/85/Asterisk-security-with-kingasterisk-36-320.jpg)
![Sip.confSip.conf
Default contextDefault context
Bindport, bindhost, bindipBindport, bindhost, bindip
[username] vs username=[username] vs username=
Permit, deny, maskPermit, deny, mask
Insecure=yes, very, noInsecure=yes, very, no
User vs peer vs friendUser vs peer vs friend
AllowguestAllowguest
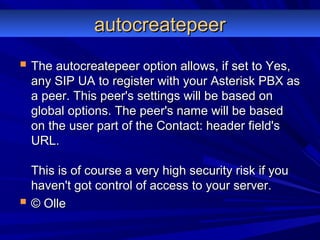
AutocreatepeerAutocreatepeer
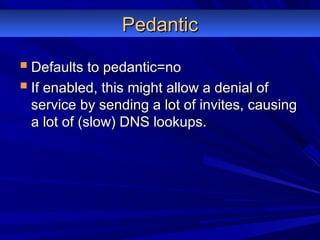
PedanticPedantic
Ospauth
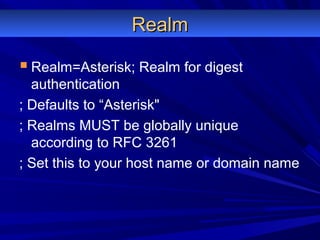
Realm
Md5secretMd5secret
User authentication logicUser authentication logic
Username= vs [username]Username= vs [username]](https://image.slidesharecdn.com/asterisksecuritykingasterisk-130723131448-phpapp01/85/Asterisk-security-with-kingasterisk-40-320.jpg)
![User vs Peer vs Friend in SIPUser vs Peer vs Friend in SIP
USER: never registers only makes callsUSER: never registers only makes calls
PEER: can register + can make calls.PEER: can register + can make calls.
[user1][user1]
type=usertype=user
[user1][user1]
type=peertype=peer
Is allowed and the same as type=friend if the otherIs allowed and the same as type=friend if the other
parameters are identical!!!parameters are identical!!!](https://image.slidesharecdn.com/asterisksecuritykingasterisk-130723131448-phpapp01/85/Asterisk-security-with-kingasterisk-44-320.jpg)
![Secret vs md5secretSecret vs md5secret
With SIP all passwords are md5 encryptedWith SIP all passwords are md5 encrypted
when sending the packets, but are storedwhen sending the packets, but are stored
in plaintext in sip.confin plaintext in sip.conf
[user][user]
Secret=blablaSecret=blabla](https://image.slidesharecdn.com/asterisksecuritykingasterisk-130723131448-phpapp01/85/Asterisk-security-with-kingasterisk-51-320.jpg)
![Secret vs md5secretSecret vs md5secret
echo - n "<user>:<realm>:<secret>" | md5sumecho - n "<user>:<realm>:<secret>" | md5sum
E.g.:E.g.:
echo -n "user:asterisk:blabla" | md5sumecho -n "user:asterisk:blabla" | md5sum
e1b588233e4bc8645cc0da24d8cb848de1b588233e4bc8645cc0da24d8cb848d
[user][user]
md5secret=e1b588233e4bc8645cc0da24d8cb848dmd5secret=e1b588233e4bc8645cc0da24d8cb848d](https://image.slidesharecdn.com/asterisksecuritykingasterisk-130723131448-phpapp01/85/Asterisk-security-with-kingasterisk-52-320.jpg)
![Username= vs [username]Username= vs [username]
[username] is for authentication a client[username] is for authentication a client
connecting to asterisk.connecting to asterisk.
Username=… is to have your asteriskUsername=… is to have your asterisk
server authenticate to another SIP server.server authenticate to another SIP server.](https://image.slidesharecdn.com/asterisksecuritykingasterisk-130723131448-phpapp01/85/Asterisk-security-with-kingasterisk-53-320.jpg)
![Iax.confIax.conf
auth=plaintext,md5,rsaauth=plaintext,md5,rsa
User authentication logicUser authentication logic
Default contextDefault context
[username] vs username=[username] vs username=
Permit, deny, maskPermit, deny, mask
Bindport, bindhost, bindipBindport, bindhost, bindip
User vs peer vs friendUser vs peer vs friend](https://image.slidesharecdn.com/asterisksecuritykingasterisk-130723131448-phpapp01/85/Asterisk-security-with-kingasterisk-54-320.jpg)
![User vs Peer vs friendUser vs Peer vs friend
USER: can only accept callsUSER: can only accept calls
PEER: can only make callsPEER: can only make calls
FRIEND: can do bothFRIEND: can do both
[user1][user1]
type=usertype=user
[user1][user1]
type=peertype=peer
Is allowed!!!Is allowed!!!](https://image.slidesharecdn.com/asterisksecuritykingasterisk-130723131448-phpapp01/85/Asterisk-security-with-kingasterisk-56-320.jpg)

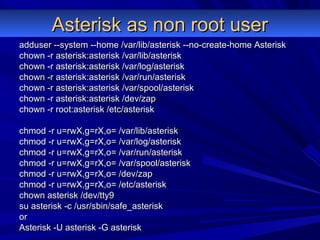
![Manager.confManager.conf
[general][general]
enabled = yesenabled = yes
port = 5038port = 5038
bindaddr = 0.0.0.0bindaddr = 0.0.0.0
[zoa][zoa]
secret = blablasecret = blabla
deny=0.0.0.0/0.0.0.deny=0.0.0.0/0.0.0.
permit=221.17.246.77/255.255.255.0permit=221.17.246.77/255.255.255.0
permit=127.0.0.1/255.255.255.0permit=127.0.0.1/255.255.255.0
read = system,call,log,verbose,command,agent,userread = system,call,log,verbose,command,agent,user
write = system,call,log,verbose,command,agent,userwrite = system,call,log,verbose,command,agent,user](https://image.slidesharecdn.com/asterisksecuritykingasterisk-130723131448-phpapp01/85/Asterisk-security-with-kingasterisk-60-320.jpg)